Strata.io Stratifies the Identity Orchestration Landscape
Publication Date: 01 October 2025
Abstract
This is the third of a series of reports on specific vendor offerings that enterprises should consider as they modernize their Identity and Access Management (IAM) foundation. In this report, we’ll review Strata.io, a company founded in 2019 that is focused on “identity orchestration” in multi-cloud environments.
With a particular focus on decoupling identities from specific Identity Providers (IDPs), the company’s approach to facilitating application modernization efforts can be quite appealing. Within multi-cloud environments, identity management table stakes such as user/subject authentication and authorization can be challenging because identities and their entitlements don’t typically translate cleanly across various cloud vendors’ security capabilities. What’s worse, previous attempts to homogenize multiple cloud security requirements into a common identity denominator have often left architects and implementers with undesirable limitations that in effect weaken security.
In this report, we explore in detail the Stata.io Maverics Identity Orchestration platform and its corresponding set of tools that help its customers achieve higher levels of cross-cloud security. We’ll then conclude with a set of pragmatic recommendations and an enterprise action plan for improving enterprise access control capabilities via Strata.io deployment.
Authors:
| Doug Simmons Principal Consulting Analyst [email protected] |
Gary Rowe CEO / Principal Consulting Analyst [email protected] |
Executive Summary
This is the third of a series of reports on specific vendor offerings that enterprises should consider as they modernize their Identity and Access Management (IAM) foundation. In this report, we’ll review Strata.io, a company founded in 2019 that is focused on “identity orchestration” in multi-cloud environments.
With a particular focus on decoupling identities from specific Identity Providers (IDPs), the company’s approach to facilitating application modernization efforts can be quite appealing. Within multi-cloud environments, identity management table stakes such as authentication and authorization can be challenging because identities and their entitlements don’t typically translate cleanly across various cloud vendors’ security capabilities. What’s worse, previous attempts to homogenize multiple cloud security requirements into a common identity denominator have often left architects and implementers with undesirable limitations that can weaken security.
Strata was founded in 2019 by three long-time presences in the IAM universe: Eric Olden, Eric Leach and Topher Marie. As the founder and CEO of Symplified, the first IDaaS (identity as a service) SSO (single sign-on) company (acquired by RSA), and founder and CTO of Securant/ClearTrust (acquired by RSA), Eric Olden has a distinguished history of starting companies that can be seen running in many of today’s enterprise IAM ecosystems. Similarly, Eric Leach has held the role of Chief Product Officer and Product Management positions at influential companies such as SalesForce and Oracle. Topher Marie also has deep IAM experience coming from Oracle, Auth0 and JumpCloud. Lastly Eve Maeler, a friend of our team at TechVision Research, former CTO at ForgeRock and a brilliant IAM thought leader just joined Strata as their Agentic Identity Program Ambassador. Strata has established several key partnerships since its founding, including:
· Amazon Web Services (AWS) – positions Strata as its orchestration and gateway partner for the Amazon Verified Permissions service launch.
· CyberArk – positions Maverics as the IDP broker to legacy IDPs such as SiteMinder, Oracle Access Manager and Tivoli Access Manager.
· HYPR – partners with Strata to offer passwordless multi-factor authentication (MFA) to any application without modifying its source code or writing custom code.
Some of Strata Identity’s key customers include Verizon, Kroger, McKesson, CIBC, Navy Federal Credit Union and many more. TechVision Research recently had the opportunity to speak at length with Gerry Gebel, Strata’s VP of Product and Standards (recently retired). The purpose of this meeting was to understand Strata’s (strata.io) solution to multi-cloud identity orchestration and how it differs from many of the existing approaches in this area.
Principle to Strata’s product line strategy is the concept of identity orchestration. In their words, identity orchestration software uses an abstraction layer that allows consistent authentication and authorization to web applications, regardless of where they run or what identity services they use. They refer to this abstraction layer as the identity fabric and a Strata-provided illustration of their concept is shown below.

Figure 1: Strata’s Identity Fabric (Source: Strata.io)
A key intention of this model is to be “developer friendly” in that it can reduce (if not eliminate) application code re-write to fit into the overall identity orchestration ecosystem. Directly related to this benefit is that “vendor lock-in” through proprietary authentication and authorization schemes can be reduced, allowing the environment to become more vendor agnostic.
TechVision Research emphasizes that we have consistently advocated “loose coupling” of the various components of the IAM infrastructure using standards-based approaches that help eliminate vendor lock-in. Our experience of over 30 years designing and implementing IAM capabilities has led us to believe that the ability to rapidly “rip and replace” various components of the infrastructure – especially as burgeoning “as a service” (SaaS) models for authentication and authorization continue to emerge.
In fact, our Reference Architecture for IAM stresses the importance of identity abstraction layers as foundational to scalable, multipurpose-yet-secure authentication and authorization. For this reason alone, we are enthusiastic about Strata’s approach to identity data virtualization, abstraction and runtime consumption interoperability.
TechVision recommends a structured approach to identifying key access control risks across this spectrum and has developed a Reference Architecture that is very useful in evaluating the set of capabilities necessary for your future state access control foundation. With over 30 years of helping our customers identify and mitigate these identity-centric risks, TechVision can help with this process.
Introduction
TechVision has conducted a lot of research and written numerous reports concerning the challenges associated with multi-cloud identity and access management (IAM). As we describe in so many of our reports ranging from privileged access management of cloud platform and application administrators, code developers, knowledge workers, AI agents or “things” – all entities require identification, authentication and authorization to perform business tasks. When the applications and related information are running across multiple cloud platforms such as Amazon Web Services (AWS), Google Cloud Platform (GCP), Microsoft Azure or the range of others, being able to consistently define and apply appropriate authentication and authorization policies is difficult.
Principle to Strata’s product line strategy is the concept of identity orchestration. In their words, identity orchestration software uses an abstraction layer that allows consistent authentication and authorization to web applications, regardless of where they run or what identity services they use. They refer to this abstraction layer as the identity fabric and a Strata-provided illustration of their concept is shown below.

Figure 2: Strata’s Identity Fabric (Source: Strata.io)
A key intention of this model is to be “developer friendly” in that it can reduce (if not eliminate) application code re-write to fit into the overall identity orchestration ecosystem. Directly related to this benefit is that vendor lock-in through proprietary authentication and authorization schemes can be reduced, allowing the environment to become more vendor agnostic.
TechVision Research emphasizes that we have consistently advocated “loose coupling” of the various components of the IAM infrastructure using standards-based approaches that help eliminate vendor lock-in. Our experience of over 30 years designing and implementing IAM capabilities has led us to believe that the ability to rapidly “rip and replace” various components of the infrastructure – especially as burgeoning “as a service” (SaaS) models for authentication and authorization continue to emerge. In fact, our Reference Architecture for IAM stresses the importance of identity abstraction layers as foundational to scalable, multipurpose-yet-secure authentication and authorization. For this reason alone, we are enthusiastic about Strata’s approach to identity data virtualization, abstraction and runtime consumption interoperability.
Using this model to show the level of interaction between components of the runtime authentication and authorization process within TechVision Research’s Adaptive Identity Capability Pattern is shown below.

Figure 3: TechVision Research Adaptive Identity/SSO Capability Pattern
As can be seen, the Maverics Identity Orchestrator is positioned as the “broker” between the authenticating subject and the target application resources that can be resident on multiple cloud platforms or on-premises.Thisset of capabilities is explained in detail in TechVision’s report titled, “Architecting and Managing Hybrid and Cloud-based Identity Services”.
To be clear, TechVision Research has long been an advocate of “loose coupling” of the various components of the IAM infrastructure using standards-based approaches that help eliminate vendor lock-in. Our experience of over 30 years designing and implementing IAM capabilities has led us to believe that the ability to rapidly “rip and replace” various components of the infrastructure – especially as burgeoning “as a service” (SaaS) models for authentication and authorization continue to emerge. For this reason alone, we find Strata’s IDP-to-IDP brokering capabilities to be particularly interesting and promising.
TechVision Research recently had the opportunity to speak at length with Gerry Gebel, VP of Product and Standards. The purpose of this meeting was to understand Strata Identity’s (strata.io) Maverics Identity Orchestration platform and its corresponding set of tools that are intended to help its customers achieve higher levels of cross-cloud security and monitoring. We’ll then conclude with a set of pragmatic recommendations and an enterprise action plan for improving enterprise cross-cloud authentication and access control capabilities via Strata deployment.
Strata Identity Background
Strata Identity was founded in 2019 by three long-time presences in the IAM universe: Eric Olden, Eric Leach and Topher Marie. As the founder and CEO of Symplified, the first IDaaS (identity as a service) SSO (single sign-on) company (acquired by RSA), and founder and CTO of Securant/ClearTrust (acquired by RSA), Eric Olden has a distinguished history of starting companies that can be seen running in many of today’s enterprise IAM ecosystems. Similarly, Eric Leach has held the role of Chief Product Officer and Product Management positions at influential companies such as SalesForce and Oracle. Topher Marie also has deep IAM experience coming from Oracle, Auth0 and JumpCloud.
Two years after its founding, Strata also hired Gerry Gebel as its VP of Product and Standards. Our mutual lineage with Gerry goes back some 25 years to our days working together at Burton Group. The company currently employs approximately 80 people in North America and boasts several high-profile customers that have made the transition from many-to-many ID to IDP mappings to the Maverics platform.
Strata has established several key partnerships since its founding, including:
· Amazon Web Services (AWS) – positions Strata as its orchestration and gateway partner for the Amazon Verified Permissions service launch.
· CyberArk – positions Maverics as the IDP broker to legacy IDPs such as SiteMinder, Oracle Access Manager and Tivoli Access Manager.
· HYPR – partners with Strata to offer passwordless multi-factor authentication (MFA) to any application without modifying its source code or writing custom code.
We were fortunate to have an in-depth conversation with Gerry Gebel, Strata.io’s VP of Product and Standards recently. During this briefing, we were able to dive deep into the key capabilities of both the current product suite and the near-term roadmap. We share our findings in the next section.
Strata’s Maverics Platform
Typically, end users and administrators alike (not withstanding AI agents and things/devices, as well) log onto many different identity systems to perform their job functions throughout the workday. These identity systems are referred to as Identity Providers (IDPs) because they each maintain systems of record regarding the user, administrator, agent or thing. Within each record is an identifier of some sort, such as a user ID or login ID, along with the corresponding credential(s) for that ID, such as a password, PIN and/or biometric data. Strata illustrates this type of environment below:

Figure 4: Current State Multiple Identities and IDPs (Source: Strata.io)
This sort of situation results in the often heard “why do I have to remember so many IDs and passwords?” and “why are my access rights not consistent from application to application?” refrain from users and administrators. The results of this type of environment are well-documented:
· Authorization policies are unique to each IDP and the many-to-many connections between IDs and IDPs.
· Passwords written on sticky notes next to the computer and we shouldn’t have to explain why this is bad in 2025.
· Shared passwords by administrators, applications or other users that make auditing of specific user actions impossible. This is also a terrible “practice” still widely used today.
· A complex environment that is difficult to expand or change because of IDP lock-in.
These are just a few reasons why such one-to-one ID to IDP relationships are undesirable, but commonplace. In an age-old refrain, we can say “we need Single Sign-On!” (SSO). To the rescue comes Strata Identity, whose Maverics Identity Orchestration model is centered on helping their customers achieve an SSO-based authentication and authorization strategy that can support multiple (and in many cases, most if not all) applications and resources in their technology environment. Strata’s vision for this is illustrated below.

Figure 5: Strata Brokering Single IDs to Multiple IDPs (Source: Strata.io)
In the center of this illustration sits Strata’s Maverics platfom, which can:
- Modernize app IAM or IDPs: Switch clouds, swap IDPs, or deploy the emerging IAM technologies without touching the applications individually.
- Add MFA & passwordless to any app: Deploy strengthened authentication for multiple enterprise applications in a short period of time.
- Layer identity resilience into a customer’s multiple IDPs: Configure always-on protection against unexpected outages.
- Bridge identity and policy between clouds: Scale the IAM architecture and secure applications with multi-cloud and multi-identity options without refactoring individual applications.
- Build orchestrated user journeys: Create a more user-friendly secure identity experience for all types of users without writing special code.
- Act as a “protocol translation service” to allow non-standard applications to speak modern IAM protocols such as OIDC and SAML.
- Augment authentication tokens at runtime by providing multiple subject attributes from multiple identity stores, which can facilitate finer-grained authorization at the target application.
- Act as an App Proxy Gateway to replace single function app gateways by affording more flexibility between multiple target system IDPs.
To configure these capabilities within the enterprise, the architect, developer or administrator uses the Identity Orchestration modules within Maverics, described below.
Strata Maverics Identity Orchestration
The Identity Orchestration solution is a component of Maverics. It allows development organizations to connect any app to any service without refactoring and managing everything, in a single control plane. The Maverics Cloud Console’s Security Air Gap Architecture, shown below highlights this control plane architecture.
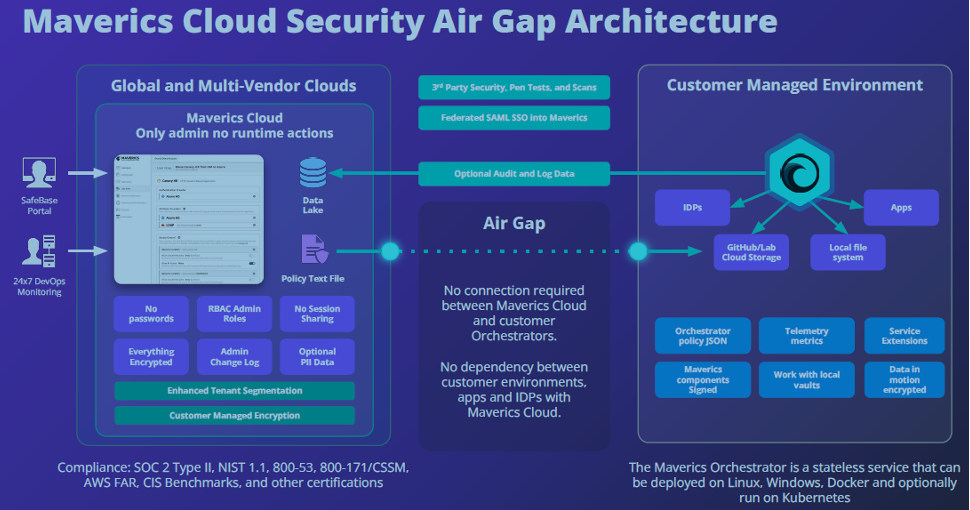
Figure 6: Strata Maverics Cloud Console Security Air Gap Architecture (Source: Strata.io)
As can be seen above, an “air gap” exists between the Maverics Cloud Console administrative interface and the enterprise’s “customer managed environment.” The Maverics Cloud Console is used to configure “environments”. Environments define storage buckets where the configurator can deploy user flow configuration and the orchestrators that will read that configuration for enterprise applications. Configurators then create environments (e.g., dev, test, staging, and production), configure cloud storage containers, and assign orchestrators to those environments in the Maverics interface or manually using environment variables.
Orchestrators are lightweight services that deploy in the cloud or on-premises. Each orchestrator runs as a service on Linux, Windows, or in a container runtime, and is configured through a YAML file or via the MavericsIdentity Orchestration Platform. YAML is a human-readable data serialization language that is often used for writing configuration files. Depending on whom you ask, YAML stands for yet another markup language. Strata also makes Mac OS X amd64 binaries also available for evaluation purposes.
Strata provides a series of “recipes” that identify the specific processes and functions afforded by the Identity Orchestrator to rapidly facilitate integration. Orchestration Recipes are no-code solutions for specific identity use cases.
These recipes automatically configure identity fabric and application integration variables to create complete user flows. Examples of Orchestration Recipes include protecting legacy apps with passwordless authentication, migrating off legacy IDPs, managing access across multiple clouds, and building identity resilience. For instance, if an enterprise intends to integrate one of their current IDPs (e.g., Okta) into their homegrown application ecosystem the following illustrates the integration model.
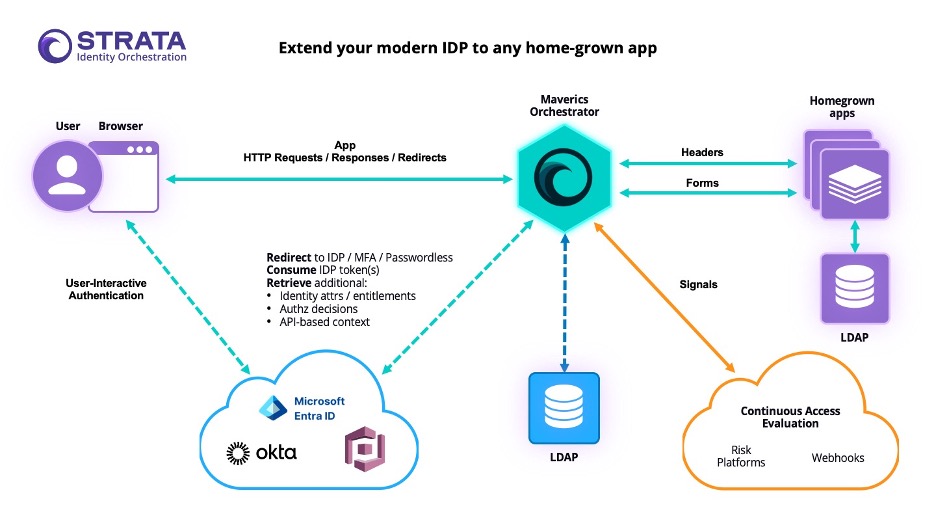
Figure 7: Strata Identity Orchestration Recipe Example (Source: Strata.io)
To reiterate, Strata’s Maverics Identity Orchestration Platform provides an abstraction layer that decouples applications from identity and natively integrates with cloud platforms, cloud identity systems, and on-premises identity and app infrastructures. The Maverics Orchestrator can also run as a standalone on-premises instance to manage identity for your identity and app infrastructures.
The identity fabric integrates on-premises identity systems such as CA SiteMinder or Oracle Access Manager; LDAP directories and SQL databases; cloud identity systems such as Microsoft Azure AD, Okta, Auth0, and HYPR; and threat intelligence providers. The Maverics Cloud Console walks configurators through the process of configuring the identity fabric with several types of authentication providers and attribute providers, or these can be configured manually as connectors and attribute providers.
Policy Definition
The aforementioned “user flows” have a 1-to-1 relationship with applications and are used to define policy details that are associated with an application. Within the Maverics Cloud Console interface, applications provide a declarative model for defining the relationships between users, applications, and identity systems, allowing the configurator to route users to any identity system for authentication, create and enforce policies, pass identities and attributes between identity systems, or pass that identity information to applications. Applications can also be configured manually as “App Gateways.”
Cookbooks
Strata also provides several “cookbooks” provide step-by-step instructions for using the Maverics Identity Orchestration platform and key “recipes” to solve common IAM challenges. The cookbooks cover a variety of topics, including authentication, authorization, provisioning, and more.
System Monitoring and Auditing
The Maverics platform supports comprehensive monitoring and auditing features, including identity service health monitoring, audit trails, and reporting capabilities to facilitate compliance and demonstrate consistent policy enforcement. It also allows for simulating outages to test continuity strategies and provides detailed reports for auditors. Here’s a more detailed breakdown:
Monitoring:
- Identity Service Health Monitoring – Continuous monitoring of IDP availability with configurable polling frequency, timeout, and failover/fallback thresholds, triggering alerts if an IDP cannot be reached.
- Orchestrator Health Monitoring – Built into Maverics, allowing for tracking of IDP performance and overall system health.
- Outage Simulations – Simulating IDP unavailability to test continuity strategies and ensure failover and failback processes work as intended.
Auditing:
- Audit Trails – Maintaining detailed audit trails of user and administrator activity, including changes to policies and access grants.
- Policy Analysis – Analyzing policies that grant access to applications and data to understand how user permissions align with actual activity, demonstrating compliance.
- Detailed Reports – Generating detailed compliance reports for auditors to demonstrate consistent policy enforcement and operational resilience.
- Failover Testing: – Performing regular failover tests to ensure that failover mechanisms function as expected and to prepare for potential outages.
Identity Continuity
Strata Identity defines Identity Continuity as an approach to keeping users connected to the applications even if an identity provider (IDP) or another identity service goes offline. It effectively enables automatic failover between IDPs without interrupting access. The graphic below shows how Maverics enables such continuity.

Figure 8: Strata Maverics Identity Continuity (Source: Strata.io)
By integrating multiple IDPs, whether cloud-based or on-premises, Maverics Identity Continuity can help organizations create a more resilient and flexible identity environment. When one IDP service outage occurs, another can step in instantly to temporarily replace the unavailable IDP. The intent is to reduce operational setbacks by eliminating reliance on manual authentication recovery processes during IDP outages.
Standards Supported
The Maverics platform supports several Identity and Access Management (IAM) standards to ensure interoperability and security across various systems and applications. These include:
· Security Assertion Markup Language (SAML)
· OpenID Connect (OIDC)
· System for Cross-domain Identity Management (SCIM)
· Identity Query Language (IDQL) – A new policy orchestration standard that Strata has invested in, promoting choice and breaking vendor lock-in.
· The Cloud Native Computing Foundation’s Hexa implementation. Authorization Interoperability and Development – An open-source software for multi-cloud identity orchestration developed by Strata.
· Strata Identity is also actively involved in the AuthZEN working group, further demonstrating its commitment to open standards for authorization.
OpenID AuthZEN is a two-year-old initiative bringing PDP vendors like PlainID, SGNL, Okta, Ping, Axiomatics and Strata together to establish a PEP/PDP interface standard. AuthZEN aims to improve interoperability and standardization in authorization, making it easier for organizations to deploy and operate authorization across their application estate. Their aim is to spearhead development of authorization agents that can lead the industry to something akin to “the OAuth moment of authorization.”
Gerry Gebel, Strata’s VP of Products and Standards at Strata Identity and who provided us with this briefing, is also a working group chair for AuthZEN, further highlighting Strata’s leadership in this area.
By supporting these standards, Strata Identity’s Maverics platform is better able to integrate with a wide variety of systems and applications and help ensure consistent and secure access management across diverse environments.
Embracing and Securing Artificial Intelligence
As we discussed in detail in the recent TechVision Research report titled, “Know Your Agent: IAM Support for AI”, AI offers game-changing benefits for individuals and enterprises but also exposes organizations to potentially devastating risks. One of the greatest AI-related risks is the management and security of AI agents (Agentic AI) that are designed to take proactive, autonomous actions on behalf of a wide range of stakeholders.
From a security perspective, any agent that takes autonomous action must be clearly identified, understood, managed, and governed and the right IAM foundation can play a major role in supporting this. Strata Identity unveiled a beta program called Maverics Identity for Agentic AI in early June 2025 to enable cross-system identity orchestration for Agents. While the specifics of how Maverics will support agent registration, authentication, access control procedures and workflows, auditing and monitoring are still being formulated, it is important to note here. TechVision is very focused on the rise of agentic AI and the very real risks it can bring into the enterprise if not managed with as much – if not more, precision as with workers. We applaud Strata Identity for getting out in front of this tsunami of efficiency so that it (agentic AI) will help us achieve the digital scalability it can bring. More information about the early beta can be seen at https://www.strata.io/blog/agentic-identity/identity-crisis-ai-agent-revolution-4a/.
Summary
With our four decades of experience helping our own customers design, source and implement large-scale enterprise and customer IAM architectures and strategies, we learned early on that “big vendor lock-in” can be both a blessing and a curse. A blessing when the organization is already standardized on a single vendor’s suite of software and as-a-service offerings. For example, there are some organizations that adopted a vendor, such as Microsoft, early on and built off that foundation for the many years that followed. Such companies might often do well to take what their primary vendor provides and make it work for them. Myriad reasons abound as to why this makes sense, from licensing costs to internal skills development and maintenance. Sometimes, however, the “big vendor” is not as nimble in responding to all of its customer requirements, because the behemoth platform has to be “all things to all people”. This can result in a set of capabilities that are good, but not necessarily best in class.
There are, however, very many enterprises that didn’t so much as standardize on a single platform vendor early on but instead grew organically with a best-of-breed approach. Over the course of 20 years or more, system and application sprawl can often result. We are not saying that this is an improper approach! There are “horses for courses” in all aspects of IT. For many organizations, market drivers indicate that individual “point solutions” are important ways to stay “ahead of the curve” as Moore’s Law drives them to address ever-changing business requirements.
For those enterprises that find themselves in a situation where multiple ID-IDP relationships via rapid technology sprawl in response to market requirements, a solution like Strata Identity’s Maverics platform makes perfect sense. By supporting important standards like OIDC, SCIM, SAML, and AuthZEN – to name a few, the spirit of interoperability reigns supreme.
We ask our customers to consider this: a tool such as Maverics, which is by its nature “developer friendly” and “IAM administrator friendly” can mean the difference between staying focused on key business objectives that directly relate to profit-and-loss statements or being mired in a slower moving large vendor ecosystem that constrains go-to-market demands.
Put it this way, even an enterprise that has standardized on a single large vendor platform would likely benefit from a Maverics implementation that bridges the foundational platform with other, newer, faster-moving Line of Business requirements. For example, if a corporate division needs to roll out a set of vendor, partner or customer-facing capabilities on a different cloud platform simply to respond to time-to-market demands, dropping Maverics in the middle can help maintain a standardized policy framework for authentication and authorization while not hindering deployment speed. This is a huge benefit for many organizations. TechVision Research has often likened such a solution as Strata’s as a “Swiss Arny Knife” that enables fast, policy-compliant integration across multiple, disparate IDPs. This sort of capability is invaluable to most organizations today.
Recommendations
We hope you have found this report useful. TechVision Research feels that consistent enforcement of identity management capabilities is one of the more critical elements of an enterprise security posture. Zero Trust architecture cannot exist without solid access controls that genuinely reflect the risk tolerance of the organization – whether for enterprise users or customer users. As so many of our enterprise customers have strategically migrated from in-house data centers of 20-30 years ago to multi-cloud platform and SasS solutions, Zero Trust can be exceedingly tricky to implement.
A set of tools such as those made available via Strata Identity’s Maverics platform can be a critical element in the toolbox for all the reasons we have been discussing. Putting the “genie back in the bottle” with respect to going away from multi-cloud, multi-SaaS environments is mostly a pipe dream for many large organizations today. Ignore this truism at one’s own peril. Tools for securely integrating multi-platform environments that require cross-policy instantiations of identity and access controls are imperative in today’s IT ecosystems for most enterprises.
Action Plan
No matter how far along you are (or aren’t) in your deployment, don’t delay moving the needle forward. Business applications need to support better, faster, data-driven decisions and the stakes are higher than ever. Again, if you’re behind the IT modernization curve, don’t boil the ocean – start with the highest risk environments, solve the most pressing problems and keep moving forward. Strata Identity’s Maverics Platform can improve your multi-cloud cybersecurity, DevOps, automation capabilities and secure access to your IT assets.
Those organizations that strive to be prepared to protect their broad range of critical information assets in a secure-but-user-friendly ecosystem will be able to do this by developing a comprehensive IAM architecture and deployment strategy. TechVision recommends a structured approach to identifying key access control risks across this spectrum and has developed a Reference Architecture that is very useful in evaluating the set of capabilities necessary for your future state access control foundation. With over 30 years of helping our customers identify and mitigate these identity-centric risks, TechVision can help with this process.
About TechVision
World-class research requires world-class consulting analysts and our team is just that. Gaining value from research also means having access to research. All TechVision Research licenses are enterprise licenses; this means everyone that needs access to content can have access to content. We know major technology initiatives involve many different skillsets across an organization and limiting content to a few can compromise the effectiveness of the team and the success of the initiative. Our research leverages our team’s in-depth knowledge as well as their real-world consulting experience. We combine great analyst skills with real world client experiences to provide a deep and balanced perspective.
TechVision Consulting builds off our research with specific projects to help organizations better understand, architect, select, build, and deploy infrastructure technologies. Our well-rounded experience and strong analytical skills help us separate the “hype” from the reality. This provides organizations with a deeper understanding of the full scope of vendor capabilities, product life cycles, and a basis for making more informed decisions. We also support vendors in areas such as product and strategy reviews and assessments, requirement analysis, target market assessment, technology trend analysis, go-to-market plan assessment, and gap analysis.
TechVision Updates will provide regular updates on the latest developments with respect to the issues addressed in this report.
About the Authors
Doug Simmons brings more than 25 years of experience in IT security, risk management and identity and access management (IAM). He focuses on IT security, risk management and IAM. Doug holds a double major in Computer Science and Business Administration.
While leading consulting at Burton Group for 10 years and security, and identity management consulting at Gartner for 5 years, Doug has performed hundreds of engagements for large enterprise clients in multiple vertical industries including financial services, health care, higher education, federal and state government, manufacturing, aerospace, energy, utilities and critical infrastructure.
Gary Rowe is a seasoned technology analyst, consultant, advisor, executive and entrepreneur. Mr. Rowe helped architect, build and sell two companies and has been on the forefront the standardization and business application of core infrastructure technologies over the past 35 years. Core areas of focus include identity and access management, blockchain, Internet of Things, cloud computing, security/risk management, privacy, innovation, AI, new IT/business models and organizational strategies.
He was President of Burton Group from 1999 to 2010, the leading technology infrastructure research and consulting firm. Mr. Rowe grew Burton to over $30+ million in revenue on a self-funded basis, sold Burton to Gartner in 2010 and supported the acquisition as Burton President at Gartner.

