Privileged Access Management: Will We Never Learn?
Publication Date: 12 July 2021
Abstract
We continue to get hacked. Instead of reaching a place where cyber security can consistently prevent hackers from inserting ransomware, injecting malicious code, stealing sensitive data, etc., we only find ourselves falling further behind. With the democratization of traditional IT into an Agile-centric rapid development and deployment model intended to help many businesses stay afloat and meet their customers’ ever-increasing demands, the necessary cyber security protections are often ignored or saved for later.
This unfortunate phenomenon is becoming all too real to many citizens around the globe as our Operational Technology (OT) infrastructure like electric grids, fuel and gas pipelines and water systems are being severely and successfully attacked. The combination of massive, relatively unbridled IT and OT infrastructure being spread out over multiple ‘platforms’ – both on premise and in-cloud in our race against “revenue time” is a very sobering predicament to find ourselves in, no matter what industry you happen to be in.
So why and how do hackers succeed? Broken record: by hijacking privileged access rights in order to drop their malicious code in your environment. For more than two decades, the TechVision Research team has been (strongly) advising its customers to invest money and personnel resources in Privileged Access Management deployment. That said, the overall footprint for PAM deployments across many enterprises remains patchy. Beating the same drum in support of PAM is not fun, but we are here to keep you apprised of the maturation and deploy-ability of several PAM solutions.
This report starts by looking at what PAM is, then evaluates the various types of approaches currently being deployed, the challenges associated with deployment, and provides a review of our short-list of vendors and solutions you should consider. We then conclude with a set of pragmatic recommendations and an enterprise action plan for PAM deployment.
Author:
| Doug Simmons Principal Consulting Analyst [email protected] |
Executive Summary
We’re all tired of hearing about security breaches, ransomware and sensitive data theft. But the hackers and thieves are more sophisticated than ever – and it is hard to tell who’s the cat and who’s the mouse in this never-ending battle. The shifting of our IT infrastructures to Software as a Service (SaaS), Platform as a Service (PaaS) and Infrastructure as a Service (IaaS) commences rapidly, and these cloud-level topologies we deploy create more security risks than many of us can contemplate.
In reviewing most of the high-profile breaches over the past decade or so, it is apparent that the ultimate targets for most hackers are the administrative accounts used by systems administrators and administration-centric applications. Systems administration accounts for Operating Systems like Windows and Linux, network and security devices, cloud platforms, database servers, and web servers – as well as those embedded within applications to perform administrative functions in application-to-application communications are the top prize for hackers and thieves. These administrative accounts are privileged accounts, in that they enable the human or system to configure environments and access the data contained therein. Once a hacker has administrative access to a single server or device, the path often opens to move laterally within the infrastructure to hack deeper and deeper within the enterprise – or beyond.
And the risk associated with privileged access is even greater in that many administrative and service accounts are shared. The fact that privileged access and the resultant actions taken during this access cannot be traced to a specific individual or application service should be very alarming.
To dramatically reduce the attack surface that enables administrative account hijacking, solutions residing under the banner of Privileged Access Management (PAM) have been available for quite a while. Such solutions have been on the market for nearly two decades now and have gradually improved to the point where most enterprises will find them compelling. That said, the overall footprint for PAM deployments across many enterprises remains patchy.
PAM solutions typically address four primary types of privileged access activities:
- System Administrator Privileged Management (SAPM), which is focused on system administration (SysAdmin), such as Windows Server or Azure Service administration, database administration, etc. The privileges associated with SAPM are usually restricted to administration and configuration services related only to the server, application, database, network device or platform to which the administrative account is associated. In other words, a Windows SysAdmin should only be able to run with administrative privileges on the associated Windows environment – he or she should not be able to use Windows SysAdmin credentials to configure other hosts or environments.
- Privileged session management (PSM) involves establishing and monitoring sessions to multiple systems. Authenticating users (e.g., using two-factor authentication) and then providing the users access to shared accounts from which all actions will be monitored.
- Application-to-Application Privileged Management (AAPM) is focused on what are often referred to as ‘service accounts’ associated with application identities and credentials used for system-to-system communications, such as a web application that interacts directly with a backend database. Service accounts typically have a username and password that is programmatically sent on the network when connecting to the target system (e.g., the backend database). The passwords associated with service accounts are often not managed in accordance with the Enterprise Password Policy that is focused on end users (i.e., people, including SysAdmins) and are all too often simple or factory default passwords, such as “password” that are not even rotated periodically in line with the Policy.
- Super User Privileged Management (SUPM) is focused on “root” accounts (e.g., root is the superuser on Linux systems). Root / superuser accounts are most often used to make system configuration changes and can override user file protection. These are very powerful, often-human-associated privileged accounts that provide the basis for configuring almost everything deployed in the enterprise IT infrastructure, including in the cloud.
Privileged Access Management is sometimes viewed as a subset of the Identity and Access Management (IAM) market but is often deployed as a separate project or program from IAM-centric provisioning, access management, access governance and authentication services. As we discuss in more detail further in this report, the deployment of PAM in typical high-risk IT environments can and should be removed from the critical path of general IAM implementations. In other words, enterprises should not delay PAM deployments while waiting for user provisioning lifecycle processes to be designed/re-designed, codified and implemented. However, the deployment of PAM should not be done in a vacuum.
While PAM and IAM deployments may proceed in parallel, there needs to be an intersection at some point in the not-to-distant future to establish more comprehensive and auditable capabilities reflecting all identities and access rights – whether end users, system or application administrators or application entities. The key intersection should occur with Identity Governance and Administration (IGA). IGA and PAM are two inter-related technologies because together, they provide one of the most important risk reduction services and enterprise can have. This level of management and audit is what IGA enables, in that IGA policies and processes institute a keen level of awareness and monitoring of ‘who has access to what, for what purposes, for how long and under whose authority?’
So, while we dive deeper into the world of PAM – especially as the unparalleled levels of migration to cloud-based environments continue to escalate (i.e., cloud-shift: SaaS, PaaS, IaaS), we will retain some focus on approaches that engender tighter PAM/IGA integration. At the end of the day, this level of visibility (i.e., monitoring, auditing, etc.) will be necessary to ‘see’ what is happening and react accordingly in the ever-expanding cloud-universe.
Introduction
Simply put, most current-day PAM solutions take privileged account credentials, such as systems administrator and application service accounts, and put them inside a secure repository typically called a ‘vault’. Once inside the vault, system administrators and application service accounts need to go through the PAM system to access the credentials in the vault, at which point they may authenticate to the target system and their access is monitored and logged. When the credential is checked back into the vault, it is reset to ensure administrators must go through the PAM system next time they want to use a credential from the vault. This method of vaulting credentials (or ‘secrets’) and checking credentials in and out on a real-time, as-needed basis accounts for the majority of PAM approaches today. (There are more capabilities and approaches, and we’ll get to them later.)
Recognize that the first word in the term Privileged Access Management is the word ‘privileged’. A privileged account is one that can perform various types of configuration and operational activities – and these activities can vary quite a bit and can yield devastating consequences to enterprise systems, applications and networks if not tightly controlled. For instance, some privileged accounts, such as Windows Administrator, have more system rights than a ‘standard user’, as defined by Microsoft Windows. The Administrator type allows complete control, which means that the administrator can change settings globally, install applications, run elevated tasks, and do pretty much anything else on the server or workstation he or she is authenticated to. This is precisely how ransomware is installed.
On the other hand, the ‘standard user’ account type is more restrictive. Users with this type of account can work with applications, but they’re not allowed to install new applications. They can change settings, but only settings that won’t affect other accounts. If an application requires elevation of privileges, they’ll need administrative credentials to complete the task. This simple scenario highlights the ‘principle of least privilege’, which means “give the administrator or user only the capabilities needed to perform their job”. In the case of an end (standard) user as just described, the principle can be somewhat easy to apply – give them next to nothing in terms of admin privileges.
However, when looking at the multiple types of systems administrators – or, sysadmins, that an enterprise typically has, the granularity required to appropriately affect the principle of least privilege can be quite daunting. What typically occurs, unfortunately, is that sysadmins of all types are granted or acquire over time much more administrative capabilities than they need to perform their day-to-day administrative duties. Call it ‘privilege accumulation’, which, much like “sensitive data sprawl” can spiral out of control over the years and becomes increasingly difficult to properly rein in without breaking something.
As a result, when it comes to effectively managing access to important resources and infrastructure, it is critically important to pay special attention to the accounts that have the most privileges, what can be done with those privileges, and who has access to those accounts.
A consistent set of well-thought-out privileged access management (PAM) controls that are aligned to a comprehensive cybersecurity framework is an imperative, enabling the automation and enforcement of controls over privileged credentials in any system, platform, or environment. PAM also identifies all known exceptions that require special control implementation. This is particularly important considering the large number and dynamic nature of resources typically deployed in the cloud. Most of these cloud environments (e.g., AWS, Google, Azure) have powerful management consoles and APIs that can expand the available attack surface requiring protection and defense. Therefore, PAM solutions that provide comprehensive automated PAM capabilities are becoming an absolute necessity.
Functional Types of PAM
PAM isn’t one monolithic ‘thing’. It is a set of capabilities that are focused on the type of administrative functionality being acted upon. There are typically four functional types of PAM capabilities that constitute complete offerings. They are:
- System Administrator Privileged Management
- Privileged Session Management,
- Application-to-Application Privileged Management
- Super User Privileged Management.
Each functional category is briefly described below.
System Administrator Privileged Management
System Administrator Privileged Management (SAPM) is centered on managing and rotating passwords and access to them. This is the original PAM formula, which was established nearly two decades ago with CyberArk’s vault model. Many products also manage SSL/TLS keys, encryption keys, SSH keys, and/or other confidential data in their vaults. Some products also save password history to handle restoring from backups and continuously monitor the environment for password changes made outside the solution (reconciliation). Access to shared accounts often involves a request and approval workflow. An incontestable audit trail is typically kept of any access to passwords. Sometimes access may be configured to only be possible when there is an outstanding ticket in an IT Service Management (ITSM) system that explicitly requires access. Additional authentication may also be required before access is granted. Some highly critical systems may require an additional person to monitor the session. Break-glass or fire-call functionality may also be supported for emergency access.
Privileged Session Management
Privileged session management (PSM) involves establishing and monitoring sessions for multiple systems. It functions by authenticating users (e.g., using multi-factor authentication) and then providing user access to shared accounts. Shared accounts are potentially very dangerous and PSM attaches an individual user account, such as the user’s Active Directory account to a shared administrative account, monitors every action during the subsequent administrative session and removes the association between the user account and the shared account upon completion of the administrative task.
Application-to-Application Privileged Management
Application-to-Application Privileged management (AAPM) functionality refers to providing applications and scripts access to passwords stored in a password vault. This is basically used to eliminate hard-coded passwords stored in each application. Hard-coded passwords are generally very easy to guess due to minimal password complexity and the fact that they are likely never updated.
Super User Privileged Management
Super User Privileged Management (SUPM) is focused on “root” accounts (e.g., root is the superuser on Linux systems). Root / superuser accounts are most often used to make system configuration changes and can override user file protection. These are very powerful, often-human-associated privileged accounts that provide the basis for configuring almost everything deployed in the enterprise IT infrastructure, including in the cloud.
PAM from a Historical Perspective
Privileged access management tools became de rigueur in the early 2000’s, precipitated in large part by the advancement of regulations such as Sarbanes-Oxley (SOX), the Payment Card Industry Data Security Standard (PCI/DSS), the Health Information Portability and Accountability Act (HIPAA) and similar regulations in light of the ‘dawn of the information age’. Regulations such as these armed auditors with specific guidelines for protecting information from theft or misuse. To be sure, the regulatory environment has since exploded over the past several years, most recently with the General Data Protection Regulation (GDPR) and California’s Consumer Protection Act (CCPA). These regulations are necessary to protect businesses and consumers from significant cyber threats, and policies and tooling to assist enterprises in marshaling information and network access rights with the level of granularity necessary to succeed is of extreme importance.
A startup company (at the time) named CyberArk Software was one of the first vendors to develop and sell a commercially available PAM solution back in 2003. It may be worth mentioning here that many PAM vendors have come and gone since that time frame, but CyberArk is still in business and going strong. Note that both IBM and Computer Associates (CA) were quick to follow suit in the early 2000s, and they, too remain viable vendors for PAM solutions depending on the enterprise’s requirements. In fact, CyberArk’s PAM server/Enterprise Password Vault (EPV) ran on IBM WebSphere application servers in the early days.
In those ‘early days’, Lightweight Directory Access Protocol (LDAP) directories were seen as the logical place to ‘vault’ credentials. For example, at runtime, the privileged account management system would query the LDAP system to determine the existence of the system administrator, the administrator password and his or her LDAP group membership. The privileged account management system’s policy would then bind system administrators to privileged accounts byLDAP group membership. This was seen as beneficial because provisioning solutions could (and still can) provision accounts to an LDAP directory without requiring any explicit knowledge about the privileged account management system.
In this way, CyberArk’s EPV PAM solution would make authorization calls to the LDAP server for all system administrator activity. If the system administrator’s LDAP group membership changed during his or her employment, his access rights immediately changed. Similarly, if the system administrator’s user object is removed from the directory, the system administrator’s next attempt to access privileged systems would be denied.
But LDAP directories could only be secured to a point, and other forms of vaulting were desired. This led to the emergence of new technology vendors such as HashiCorp. In 2015, the company released its first version of HashiCorp Vault as a tool for securely accessing ‘secrets’, which it defined as anything that you want to tightly control access to, such as API keys, passwords, or certificates. The HashiCorp Vault provided a unified interface to any secret, while providing tight access control and recording a detailed audit log. In March of 2018, CyberArk acquired Vaultive, in an effort to bring their own vaulting technology into the cloud-first, DevOps mindset. In essence, LDAP directories are being replaced by more tightly coupled, highly secured ‘special-purpose’ database vaults.
It’s Getting Cloudy
This advancement of special-purpose, cloud-ready vault technology is better suited to enable automation and Agile-method continuous integration/continuous development (CI/CD) use cases while enabling policy to codify, protect, and govern access to secrets. The vault can leverage many trusted identity providers, such as cloud IAM platforms, Active Directory, cloud automation platforms such as Kubernetes, and so forth to authenticate into the vault. Identity is abstracted and is scale independent, unlike IP addresses, which require complex firewall rules and frequent updates. Vaulting allows a service to request secrets for any system through a consistent, audited, and secured workflow.
With this evolution of the vault model, HashiCorp Vault became the credential vaulting solution behind Amazon’s AWS/EC2 IaaS environment, as well as the chosen vaulting solution for emerging PAM vendors such as Saviynt.
Secondly, the early PAM solutions were focusing primarily on human administrators and left a lot of room for further development of application-to-application PAM. This began to change with CyberArk’s 2017 acquisition of Conjur, a solution developed to better secure DevOps environments. With Conjur, CyberArk’s PAM environment can reach deeper into the DevOps lifecycle to protect secrets and manage machine identities.
For instance, Conjur’s Kubernetes integration consists of TLS-connected ‘client and server’ plug-ins that adds Kubernetes authentication capabilities. Conjur (with this plugin installed) is on the server-side. The second piece of the integration is a sidecar container that is deployed alongside a user’s application. This sidecar container handles the authentication with Conjur on behalf of the application. This sidecar container is the client. Using this type of methodology for cloud service automation extends application-based PAM functionality across enterprise IaaS infrastructures, which is a major step forward to bringing ‘service account’-type authentication into the highly monitored world of PAM.
Future State of PAM
For good reason, vendors are increasingly describing their offerings in terms of Just in Time (JIT) PAM. JIT PAM means that system administrators – whether human or application functions, can be assigned privileges in near real time using their existing, or creating temporary, end-user accounts. JIT PAM limits the duration for which an account possesses elevated privileges and access rights in that the creation and deletion of an appropriate privileged account is assigned only to meet that specific period’s mission objectives. The “good reason” is to eliminate the risk surface of having privileged accounts that are “always on”.
To make this work, users typically request the access they need via a workflow process – such as ServiceNow or via an existing IAM/IGA workflow process and are quickly granted access or an access privilege level to an application or system. Privileged access may be granted for just a few minutes or several months, depending on the sensitivity level of the application or the organization’s governance requirements. In some cases, like developers who compile code, JIT PAM may be available all the time but use other methods for privileged elevation in order to avoid the risks of “always on” accounts. In addition, special approvals and logic checks can be added when access to sensitive applications or systems is requested.
When JIT PAM is combined with role-based or attribute-based access control policies (RBAC and ABAC, respectively), organizations can better ensure control and insight over every user’s systems access at any point in time. Coupling Multi-factor Authentication (MFA) with JIT PAM processes also adds a significant element of trust that the individuals requesting elevated privileged access are who they say they are, and with added contextual information such as device, geo-location, previous requests/approvals and so forth, an organization can provide better guard against multiple threat vectors.
This is where vendors and the industry are moving. It is a significant departure from the password vault model in place for the past two decades and affords a more IAM and workflow-integrated approach that may make PAM much easier to deploy at an enterprise-wide level that is increasingly cloud-centric.
PAM Deployment Best Practices
With this general background of PAM’s evolution, current approaches, and emerging trends, we’ll now focus on typical features that your enterprise should be considering as you embark on your PAM journey for the first time – or look to improve your current security posture by making some marked PAM improvements. These features are critical to the deployment of your PAM solutions and can also be factored into your PAM vendor evaluations. To this end, TechVision Research provides the following list of features and functions we feel are necessary for a successful PAM deployment.
Key Requirements for PAM Deployment
- Tools to discover, map and visualize privileged accounts in multiple systems, applications, and devices, whether on-premises or cloud-based SaaS or IaaS.
- Auto-discovery of new hosts, VMs and apps in the enterprise cloud
- Management of cloud-based administration accounts on:
- Hypervisor/cloud management platform (CMP)/IaaS
- Guest OSs
- Cloud-resident applications
- Restricting access to the hypervisor/CMP/IaaS management console
- A secured, hardened and universally available vault for storing credentials and secrets. The vault should encompass tools that automatically randomize, rotate, and manage credentials for system, administrative, service, database, device, and application accounts – both on-prem and in the cloud.
- AAPM integration tools that dynamically bind credentials to applications to eliminate static clear-text credentials in configuration files or scripts.
- User interfaces and underlying workflows to manage the end-to-end process of requesting access and receiving privileged credentials.
- Support for role-based administration, including centralized policy management for controlling access to credentials and privileged actions.
- Command filtering to instantiate the policy of least privilege by restricting administrative functions to only those that are required for a specific task.
- Restrict operations that allow the instantiation, deletion, starting, stopping, and copying of VM images and other cloud-delivered services.
- Capability to allow a privileged session to be automatically established using protocols like SSH, RDP or HTTPS without revealing credentials to the user.
- Capability to fully record and review sessions and manage active sessions by allowing them to be monitored or terminated.
- Analytics and reporting on privileged accounts and their use.
- Session recording
- Audit reports.
- Multifactor authentication (MFA), including biometrics support.
Discovering Privileged Accounts
As we have discussed, privileged accounts exist in four areas, principally:
- System Administrator Privileged Management (SAPM)
- Privileged session management (PSM)
- Application-to-Application Privileged Management (AAPM)
- Super User Privileged Management (SUPM)
With these types of privileged accounts often used across the entire enterprise IT ecosystem, it becomes exceedingly important to identify where these accounts exist, for what purposes they are used and to whom (or to what) each privileged account is assigned. An important facet of PAM deployment, therefore, is to first “discover” existing privileged accounts in use across the enterprise. This can be a daunting task, as privileged account proliferation over the many years of deployment can render a complete accounting of all service accounts – in all four categories, quite formidable.
A great place to start this process of privileged account identification is through Privileged Account Discovery tools. Discovery tools are intended to assist the PAM deployment team in locating privileged accounts across the enterprise by automating their discovery. A good discovery tool can eliminate – or greatly reduce, the time and effort needed to manually audit every system, device and application in the organization and then determine what rights each administrative account has, and what services and/or tasks the account is associated with. Automating the discovery of privileged accounts avoids digging through every system administrator’s personal spreadsheet or text file containing the usernames and passwords for his or her often multiple administrative accounts.
Using an automated tool that can scan the systems and directories on the enterprise network and identify all of the privileged accounts can provide substantial savings in time and effort – not to mention providing a much higher level of accuracy by eliminating the need to manually query individuals and rely on their historical documentation. Additionally, the discovery tool can and should become a mainstay in the PAM topology, to better ensure ongoing discovery and proper handling of new privileged accounts that may continue to crop up.
For example, a free automated discovery tool within Thycotic’s Secret Server PAM solution allows an administrator to funnel newly discovered accounts into workflows that will also automatically assign roles and permissions to the teams that should have access, as well as applying necessary policies and configuration requirements to these Windows and Unix administrative accounts (https://thycotic.com/solutions/free-it-tools/).
Similarly, CyberArk’s Discover and Audit download is a free assessment tool intended to help discover privileged accounts, privileged passwords, SSH keys and Pass-the-Hash vulnerabilities on the enterprise network (https://cyberark.wistia.com/medias/pvboagjjtp). Another leading vendor, BeyondTrust, provides a free scanning tool centered on Windows privileged accounts, such as AD accounts, local accounts and service accounts within an enterprise’s Windows environment (https://www.beyondtrust.com/tools/discovery).
Saviynt, a market leader in Identity Governance and Administration (IGA) has greatly expanded its focus on enterprises’ cloud environments – namely Amazon Web Services (AWS), Microsoft Azure and Google Cloud. The Saviynt Security Manager solution is a cloud-based SaaS solution itself (running on AWS) and provides discovery capabilities for both cloud-centric and on-premise privileged accounts as a foundation for its IGA functionality.
In addition to PAM discovery and IGA tools, enterprises can leverage information garnered from other security solutions that may already be in place, such as Data Loss Prevention (DLP). For instance, Symantec’s Cloud Detection Service provides the capability for enterprise security teams to discover instances of sensitive data on the cloud and on-premise. While not a PAM discovery in and of itself, this information can be used to triage information regarding owners of sensitive information in the cloud or on-prem with the administrative privileges required to manage this information. The more information an enterprise has about where its data ‘lives’ and who put it there/manages it, the more educated and refined the process of PAM deployment can become.
Don’t Skimp on Authentication
With the rapid adoption of more convenient mobile phone-based multi factor authentication (MFA) technologies that include biometrics, PAM solutions for human administrators (SAPM and SUPM) generally support (if not require) MFA out-of-the-box – a very good practice, to be sure!
Architectural Principles
Now that we’ve described PAM, key trends, major vendor directions and key requirements, we can focus on major architectural principles enterprises should be considering as the develop their PAM programs. PAM tools typically offer one or more of these important features:
- Providing secured, centralized, and automated management of passwords and secrets for administrative, service and application accounts, as well as enforcement of password policies.
- Abstracting actual service/system passwords and secrets using time-limited/one-time use and role-constrained tokens.
- Controlling and auditing access to shared accounts.
- Managing and monitoring privileged sessions, commands, and actions in real-time through over-the-shoulder surveillance, recording them and allowing them to be audited.
- Controlling and filtering commands or actions an administrator can execute.
- Providing capabilities to govern and administrate administrative access, whether systems and applications are on-premises or in-cloud.
- Maintaining a comprehensive view of privileged accounts and their usage in the IT environment through dashboards and reporting.
- Integrating with enterprise IAM and IGA systems to foster a comprehensive understanding of exactly who (or what) has access to what.
- Integrating with existing IT service management (ITSM) systems and change management workflows for tighter control of administrative access.
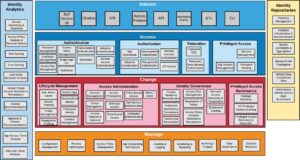
With these principles as a backdrop, let’s view the TechVision IAM Reference Architecture with our MFA glasses on. The TechVision Research Reference Architecture for IAM is this starting point; a master template, shown in Figure 1, below, identifies the IAM capabilities (rather than technologies) that can be improved or enabled, allowing business stakeholders and technical architects to achieve a common language for IAM functions, which can then be refined over time.
It is important that your PAM program fits within this overarching architectural context. This high-level template starts the journey:
Figure 1: IAM/MFA Master Template
The capabilities illustrated above are described at the highest level as:
Interact – how end-users and application developers interact with the IAM platform. In the case of PAM, this will involve a variety of diverse people and technology interactions.
Access – the rules that define the roles, rights, and obligations of any actor wishing to access enterprise or connected external assets.
Change – the capability to define and manage the relationships between the user/ application developer and the enterprise assets.
Manage – the capabilities required to manage and upgrade the IAM solution itself.
Measure – the capabilities required to audit and improve IAM activities.
Store – the capabilities required to share identity information and relationships between the components of the IAM solution.
The next level of the architecture outlines the functional capabilities that are the foundation for a best-in-class IAM Reference Architecture. Each category is broken up into multiple capabilities at a level of greater detail. For example, interfaces can be for applications / developers (APIs, messaging services), Lines of Business, self-service, or even robotic processes. This applies to each category and, based on stakeholder input, use cases and priorities can be further developed into Reference Architecture patterns or templates for specific services.
It is important to understand that these functional capabilities consider all type of objects and use cases within the IAM foundation. For example, identifying, securing, and collecting data pertaining to IoT devices is expected to be accommodated within the IAM Reference Architecture.
As ultimately implemented, different enterprises use different IAM capabilities in different ways to meet different protection needs. And they do so differently for different content and business functions because of the different risks and potential consequences associated with failures and costs associated with protection. One size does not fit all.
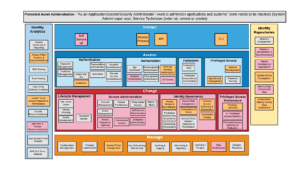
Once the required business capabilities are identified, the next layer of the TechVision Research Reference Architecture for IAM allows us to explore each of the specific technology or process elements comprising each capability in the form of a combined portfolio architecture. This is illustrated in Figure 2, below.
Figure 2: Combined Portfolio Architecture
In the template below, we’ve now illustrated the IAM capabilities required for a typical organization’s Privileged Access Management, removing all other IAM capabilities that are not directly supporting the PAM service. Note that this representation includes a typical ‘user story’ in the form of “As an Application Administrator, I want to…”. User stories help keep the focus on the capabilities necessary to support it and we highly recommend you work through your key user stories.
Figure 3: Typical PAM Capabilities Map
Note that this is intended to give you a sense for how to apply the reference architecture to PAM specific capabilities and to give you a sense for typical relative timing. In our example, we have determined that the IAM-related capabilities necessary to support the PAM Service for a large organization can be color-coded as follows:
- Rose – requires significant investment over next 2 years. This typical organization does not currently support these IAM capabilities. An example is JIT PAM (Just In Time access).
- Orange – requires investment over next 2 years. The organization either currently does not support these IAM capabilities or they may require additional investment and deployment in order to achieve a requisite level of functionality. For example, most organizations currently support some form of MFA, but additional investments will generally be required.
- Grey – indicates capabilities that the organization IAM has in place in some capacity, although it could be likely that some augmentation may be required to improve functionality and ubiquity to fully meet the organization’s requirements. An example here is Federation/SSO which may be relatively mature in many organizations – but could be enhanced over the next few years.
Please recognize that your Capabilities Map is likely going to be different than the one shown in Figure 3. The important point is to start with the complete list of capabilities building blocks as shown in Figure 2, and pare that down to represent what PAM requires, color-coding to show where you will likely need additional investment or attention. TechVision can – via dialogues or full consulting engagements, work through this process with your team. The PAM Service IAM capabilities are used as input to the development of the Reference Architecture pattern illustrated and described in the next section.
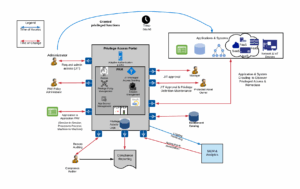
Develop PAM Reference Architecture Patterns
As we described above, PAM looks to provide an additional layer of security in support of administrative and other high-risk access. The policies maintained in the PAM control service dynamically evaluate the risk of a given operation based on a variety of environmental and risk factors and filter access if risk exceeds a defined threshold. This extends from the internal network to external connections. As the example PAM Reference Architecture pattern illustrates below, the intent is to draw ‘what good looks like’ for your organization. This pattern should be indicative of what you want. It is completely vendor-agnostic in this instantiation so that you have the vision ready to query multiple vendors about how they can support this pattern via Request for Proposal (RFP) or Request for Information (RFI).
Figure 4: Example PAM Reference Architecture Pattern
This pattern supports the use case in which an application programmatically ‘checks out’ the service account credentials from the PAM service, eliminating the need for setting up hard coded credentials for the service account and guaranteeing that the service account credentials are continuously recycled. The overall PAM environment should be viewed as the gatekeeper to privileged operations. Also, even though not static, PAM still need to Authorize as to who can access and make requests via JIT PAM. Thus far we have discussed the nature of privileged access management, its various approaches and anticipated market trends. We’ll now look at how these patterns and approaches are being supporting today by the leading PAM vendors.
Leading PAM Solution Overview
As we have written, a great deal of investment and time has gone into developing many of the PAM solutions available on the market today. These investments reflect the increasing enterprise focus on protecting those environments that are of the greatest risk and can do the most damage if compromised. While technical approaches to PAM vary and vendors often focus certain approaches – like agent-based PAM, proxy-based solutions or the use of a special-purpose vaults, there are many viable PAM solutions. As usual, what might be an excellent fit for one customer environment may be overly risky or complex for another. With that background, TechVision feels that the following vendors are good candidates to put on your PAM short-list:
- CyberArk
- Arcon
- BeyondTrust
- Thycotic
- Microsoft
- One Identity
- Hitachi ID Systems
- Centrify
- Okta
Given the increased use of cloud platforms within the enterprise, we’ll also briefly discuss the limited, but expanding privileged management capabilities enabled by Google Cloud Platform and Amazon Web Services. We’ll start with CyberArk since they have been the historic leader in the PAM space.
CyberArk
CyberArk is a publicly traded information security company offering Privileged Account Security. CyberArk currently has over 5,000 customers, including more than 50 percent of the Fortune 500 and more than 30 percent of the Global 2000. CyberArk is headquartered in Israel, with U.S. headquarters located in Newton, Massachusetts. We provided some information about CyberArk earlier in this report given their history and traditional leadership position in this space. To recap, CyberArk was an early pioneer in the PAM market, with their Enterprise Password Vault (EPV) being first introduced in 2003. Since then, they have become the pre-eminent purveyor of PAM worldwide.
Their existing product suite is called the CyberArk Privileged Access Security Solution which can be deployed across on-premises, cloud, and hybrid infrastructure. The solution delivers risk-based credential protection and session management to detect and prevent attacks involving privileged access. The CyberArk PAM solution suite is comprised of the following individual products:
- Privileged Access Manager
- Vendor Privileged Access Manager
- Cloud Entitlements Manager
- Endpoint Privilege Manager
We look at each of these below.
CyberArk Privileged Access Manager
This is fundamental PAM technology CyberArk offers to provide the following capabilities:
- Privileged Credential Management: Automatically discovers and onboards privileged credentials and secrets used by human and non-human identities. Centralized policy management allows administrators to set policies for password complexity, frequency of password rotations, which users may access which safes, and more.
- Session Monitoring and Isolation: Maintains compliance with recorded key events and tamper-resistant audits. Establishes secure, isolated remote sessions and records all activity during sessions. Session recordings are securely and centrally stored.
- Threat Detection & Response: Automatically discovers and onboards unmanaged privileged accounts and credentials. Detects anomalous behavior and indicators of compromise with policy-driven remediation capabilities.
- Nomadic Device Management: Enforces security policies and rotates account credentials on endpoints that aren’t always connected to the enterprise network.
- Remote Access to PAM: Enables secure access for remote employees and external vendors to Privileged Access Manager. Supports VPN-less, agent-less, and password-less models.
- Adaptive MFA & SSO: Validates privileged users with context-aware Adaptive Multi-Factor Authentication and secure access to business resources with Single Sign-On.
Vendor Privileged Access Manager
This CyberArk PAM component is focused on better securing the ever-increasing third-party vendor (e.g., managed services) landscape. Key capabilities include:
- Biometric Multi-Factor Authentication: Helps to ensure that external vendors are confirming their identity each time they need to access critical assets.
- Just-in-Time Provisioning: Facilitates onboarding and off-boarding vendors to access specific resources on a temporal basis; and includes support for vendors to self-manage access requests (e.g., delegated administration).
- Recording and Monitoring: Provides visibility into vendor activities, with reporting, auditing and remediation capabilities.
- Native Direct Access: Directly and natively initiates privileged sessions from remote connection managers and web browsers.
Cloud Entitlements Manager
The Cloud Entitlements Manager component is an AI-powered detection to clean up misconfigured and unused cloud permissions. This is becoming a major issue for many organizations that have rapidly migrated to at least one cloud (more often, multi-cloud) environment. The component provides cloud-agnostic insight from a centralized dashboard to detect and control permissions to access resources across AWS, AWS Elastic Kubernetes Service, Azure, and GCP.
By being “AI powered”, the component can apply granular, code-level IAM policy recommendations for human and machine identities without impacting ongoing operations. This may also help organizations more proactively reduce risk and measure progress with dynamic, quantifiable exposure level scores for all identities and platforms.
Figure 5 – CyberArk Cloud Entitlements Manager
Endpoint Privilege Manager
Attacks such as ransomware and code injection most often enter the network through poorly secured endpoints. CyberArk has taken significant notice of this and developed their Endpoint Privilege Manager (EPM) to enable Dynamic Privilege Elevation that provides users with on-demand local admin access “whenever they need it”. This also includes credential protection that proactively blocks credential theft from the endpoint devices’ interface(s). These are both important features that, simple as they may sound on paper, can provide a great deal of protection from ransomware and code injection attacks.
The CyberArk Conjur Secrets Manager is an AAPM tool that can be used to provide and manage the credentials that commercial off-the-shelf (COTS) and internally developed applications, tools and solutions. Conjur Secrets Manager manages the required AAPM credentials in the CyberArk Vault. (CyberArk offers a sizeable eco-system of validated COTS integrations for securing privileged access.)
The CyberArk AAPM solution also manages secrets and credentials used by DevOps and PaaS tools, and containers. The solution integrates with a wide range of DevOps tools such as Ansible, Jenkins, Puppet; PaaS/Container orchestration platforms such as Red Hat OpenShift, Pivotal Cloud Foundry, and Kubernetes, whether running on-premises, hybrid or on multiple cloud platforms. The solution also integrates with CyberArk’s Enterprise Password Vault to provide a single enterprise-wide platform for securing privileged access. CyberArk offers an open-source version of Conjur Secrets Manager as Conjure Open Source (www.conjur.org). Conjur Secrets Manager also integrates with existing Active Directory, LDAP, and SIEM systems.
Lastly, the CyberArk Privilege Cloud is an as-a-service solution that provides a path to securely store, rotate and isolate credentials and monitor sessions. CyberArk offers this solution with subscription-based pricing that can scale as needed.
Figure 6 – CyberArk Privilege Cloud Architecture
The Privilege Cloud solution is intended to protect, control, and monitor privileged access across on-premises, cloud, and hybrid infrastructures. The features associated with the PAM solution outlined above are deployed in a secure public cloud environment for feature parity. The offering is hosted on AWS and comes pre-configured to be consistent with ‘best practice security recommendations’ that are intended to help its customers reduce the time to deploy successfully.
ARCON
ARCON is a Mumbai based company that provides enterprise-class risk mitigating solutions that they state have been deployed by 900+ global organizations that include financial institutions, government organizations, telecom, energy companies, utilities, and pharmaceutical companies among others. ARCON’s product portfolio includes four security and risk solutions:
- User Entity Behavior Analytics (UEBA): detects anomalous behavior with risk detection and analytics capabilities.
- Security Compliance Management: a system hardening tool that enables real-time assessment of baseline security configurations for critical technology platforms in concert with defined compliance levels.
- Privileged Access Management: discussed in more detail below.
- Endpoint Privileged Management: discussed in more detail below.
ARCON PAM enables fine-grained access control to restrict and control privileged users through a rule and role-based centralized governing policy. The functionality provides the IT risk managers with command restricting and filtering capabilities to control access to target systems. An illustration of ARCON’s PAM architecture is shown below.
Figure 7 – ARCON Privileged Access Management Solution Architecture
The PAM solution includes password vaulting that generates strong and dynamic passwords, with the ability to automatically change passwords for several devices or systems at once. The passwords are then stored in a secured electronic vault. The storage methodology is proprietary and is secured by several layers of protection that enables what ARCON calls a “virtual fortress”. The electronic vault integrated with ARCON’s PAM workflow provides authorized access to these passwords.
Other key features include:
- The PAM solution’s MFA functionality acts as an entry point to identity management systems and assists in managing system-based users. ARCON offers its own One-Time-Password (OTP) validation capability to begin a privileged session, and the tool also integrates with disparate third-party authentication solutions such as Gemalto, RSA, Vasco, 3M, Precision, SafeNet and Safran.
- Session monitoring provides basic auditing and monitoring of privileged activities across the enterprise IT network. Its Live Dashboard feature enables critical activities performed by administrators across the IT infrastructure to be viewed by security teams in real-time.
- Auto-discovery enables the risk management team to discover shared accounts, software and service accounts across the IT infrastructure. This important feature helps its customers identify privileged accounts that are ‘unaccounted for’ – often a critical piece of the organization’s PAM puzzle.
- Just-In-Time Privileges functionality forces all users to act as standard users, and not as privileged users – to implement the principle of least privilege. As implied, with JIT Privileges, an administrator can provide access to systems and applications only when the requirement arises. Privileges are therefore elevated for specific tasks on applications and systems. After any administrative access request is raised, administrators allow privileged rights to any user to perform a definite task at and for a specified time. The JIT PAM component removes standing privilege by limiting access to systems/ applications and the count of administrative/ operational staff. It can also limit access at a granular level and deny any “full-time access” to systems/ applications.
- JIT PAM also supports privileged interactive access to automatically generate rule and role-based temporary access rights to Amazon Web Services (AWS) Console or Command Line Interface (CLI) components that interacts with AWS Secure Token Service (STS) and allows administrators to customize accounts with unique AWS roles.
- App to App Password Management manages the passwords for an application through a single terminal in the IT infrastructure. This is an automated process where the password change is managed and monitored by giving the required details of the servers, the IP addresses, and the new passwords. It synchronizes the changes across the network to help mitigate service disruptions. All the changes are examined in the configuration file before and after the task.
- Knight Analytics is an AI-based threat detection system that is used to detect, predict and display anomalies in the logged data. It uses machine learning algorithms that learn each user’s behavior based on their historic data and predicts risk based on the activities.
- Application Gateway Server (AGW) is the single point of access to the target systems. The secure gateway creates an encrypted tunnel from endpoints to the target systems. Access to systems is based on identity along with other attributes and contextual information such as IP address, geo-location, device(s) used, time and date. This is available for an organization to add a layer of security for open communication channels.
- Virtual grouping provides a dynamic group setting to create functional groups of various systems. It is designed to facilitate relationships, responsibilities, accountabilities and caters to dynamically changing organizational structures, roles, and responsibilities. Virtual Grouping allows organizations to manage multiple subsidiaries and companies.
- The Workflow matrix enables configuration of approval processes for privileged users, user-groups, and service groups. A S\service and password request workflow mechanism facilitates the process of assigning target servers to privileged users.
- Privileged Elevation and Delegation Management (PEDM) supplements privileged user management by controlling and monitoring non-admin user activities that require temporary privileged access to the systems. Access to critical components such as applications, databases, cloud services is granted only after a valid automated approval process. Access rights assigned to critical systems are automatically terminated after the conclusion of “temporary privilege” activities.
- Active Directory (AD) Bridging provides authentication to have a single-sign-on, for Linux/Unix users using Windows Active Directory credentials by bridging the machine and AD Server.
- The Spection tool leverages the solution’s analytics platform to generate dynamic reports with statistical as well as the graphical representation.
- Remote Assist helps system administrators to remotely access and troubleshoot end devices, wherever they may be. This is intended to resolve help-desk tickets, or desktop issues and enables PAM connectivity to specific users within or outside the enterprise network, in compliance with the organization’s security policy.
ARCON offers professional services for the deployment of the solution. Their PAM product supports integration with a variety of tools from SIEM, ITSM, RPA, DevOps CI/CD, IDAM, Automation Solutions, Containers and more. Some of the tools that can be integrated with ARCON are Symantec, RSA, Arcsight, Rapid7, BMC Remedy, Precision, ServiceNow, Nessus Manager, Tenable.io/Tenable.sc, Qualys, Ansible, Jenkins, Chef, Kubernetes, Red Hat OpenShift, AWS Elastic Container Service (ECS), Microsoft AD, Azure Ad, G-Suite, AWS IAM, Okta, Sailpoint, 1Kosmos and many more. This is just a small snapshot of the features included in ARCON’s PAM solution. From our viewpoint, ARCON PAM is a very feature-rich, ‘industrial strength’ PAM solution that warrants serious consideration.
Saviynt
Saviynt, based in El Segundo, CA is a strong player in the Identity Governance and Administration (IGA) space. From a historical perspective, it bears mentioning that Saviynt is a re-branded version of early IGA innovator Vaau, which was acquired by Sun Microsystems in 2007 – which was itself acquired by Oracle in 2009. The long-standing pedigree in the IGA space enabled Saviynt to gain leadership status in the IGA market. Regarding PAM, Saviynt has been embarking on a cloud-first strategy to offer effective privileged access management for cloud applications and services, whether SaaS or IaaS. Figure 8 below illustrates a summarization of their Cloud PAM solution.
Figure 8: Saviynt Cloud PAM
Though this report focuses on PAM, we start by looking at Saviynt’s IGA platform which is a FedRAMP Authority-to-Operate (ATO) approved IGA service and uses intelligent analytics to provide peer-group based insights giving context for how users access data. PAM and IGA have a lot of synergy and Saviynt is looking to better integrate these offerings. The use of analytics can help with the challenge of account provisioning and deprovisioning by providing more granularity around access control, supporting multi-level workflow approvals, identifying potential segregation of duties violations – and triggering preventive actions. This level of granular inspection helps with both with continuous monitoring, especially for higher risk system and data administration – and with discovery and remediation of privileged access.
Saviynt developed its credential vault on HashiCorp’s Vault, an open source and for fee commercial vault solution that controls access to secrets and encryption keys by authenticating against trusted sources of identity such as Active Directory, LDAP, Kubernetes, CloudFoundry, and cloud platforms. Integrated with Saviynt’s IGA and PAM solutions, Vault enables fine grained authorization of which users and applications are permitted access to secrets and keys.
By extending Saviynt’s IGA platform with its Cloud PAM solution, its customers can better mitigate risks associated with privileged access in the cloud. Saviynt’s Cloud PAM solution works inside the customer’s internal cloud to attach rights and privileges to identities so that it can streamline their governance. Rather than creating additional user accounts for privileged access that need to be monitored, Saviynt’s Cloud PAM solution enables administrators to assign timebound permissions to identities and then provides alerts to help remediate risks.
Saviynt’s Cloud Privileged Access Management (Cloud PAM) solution provides JIT access to managed privileged sessions of the Azure console, Azure workloads, tenant administration of Microsoft 365 applications, and other Azure services. Saviynt’s Cloud Security Analyzer solution protects data security and privacy by using automated tools to enforce the principle of least privilege access controls for users within Infrastructure-as-a-Service (IaaS), Platform-as-a-Service (PaaS), and Software-as-a-Service (SaaS) cloud ecosystems. As an example, Saviynt’s Identity Governance and Administration-as-a-Service (IGAaaS) platform enables organizations using Microsoft Azure a more integrated approach to identity governance and administration (IGA) when managing access to hybrid IT and managing/securing control over data and activities within Azure. Features include analytics, data access governance, SOD management, real-time threat detection, and compliance controls to secure critical Microsoft Azure assets.
Bearing this in mind, Saviynt’s Cloud PAM solution was the first to converge traditional PAM with IGA for certain business-critical hybrid-cloud enterprise applications such as Enterprise Resource Planning (ERP) systems (e.g., SAP/HANA, Oracle, Workday, Cerner, Epic) and Customer Relationship Management (CRM) systems such as SalesForce, SAP Business Suite and Oracle eBusiness Suite. Saviynt provides approximately 300 risk and governance policies for SaaS / IaaS and enterprise applications out-of-the-box, which can be further augmented with native integration with SIEM / UEBA providers. TechVision views this level of integration between PAM and IGA as a significant capability in terms of providing enterprises with a much more comprehensive view of ‘who has access to what’ – and why.
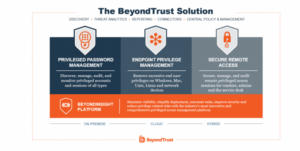
BeyondTrust
BeyondTrust is a U.S.-based company that develops, markets, and supports a family of privileged identity management (PAM), privileged remote access, and vulnerability management products for UNIX, Linux, Windows, and Mac OS operating systems.
BeyondTrust was founded in 2006 and provided Least Privilege Management software for the Microsoft Windows OS, before UNIX vendor Symark acquired the company in 2009. In 2018, the company was acquired by Bomgar, a developer of remote support and PAM software. In both cases, BeyondTrust was adopted/retained as the new company name. BeyondTrust claims over 20,000 customers of its PAM solutions. Given that the company has been providing these solutions for over 13 years, this level of adoption puts them on relatively stable customer footing.
BeyondTrusts PAM product line consists of four principal components:
- Privilege Password Management
- Endpoint Privilege Management
- Secure Remote Access
- Cloud Privilege Protection
Figure 9: BeyondTrust’s PAM Portfolio
BeyondTrust Privileged Password Management unifies privileged password and privileged session management, providing secure discovery, management, auditing, and monitoring for any privileged credential. Key features include:
- Enables removal of hard-coded passwords from applications and scripts
- Provides an extensible REST interface that supports many languages, including C/C++, Perl .NET, and Java
- Ensures that passwords can be automatically reset upon release
- Enforces e controls to lock down access to only authorized applications
- Enables the dynamic assignment of just-in-time privileges via the Advanced Workflow Control engine.
- Supports SSH key management:
- Stores private keys like any other privileged credential
- Automatically rotates SSH keys according to a defined schedule
- Allows designated ‘secondary’ accounts and SSH keys to be grouped to a ‘primary’ account to manage rotation interval, complexity and duration of SSH keys
- Enforces granular access control and workflow
- Alerts when a key is released
- Automatically logs users onto Unix or Linux systems through the proxy with no user exposure
- Records every privileged session with full playback and key usage auditing
- Offers failover to a managed password for complete redundancy
- Allows SSH sessions to be easily established via existing desktop tools without having to initiate with a web interface
- Leverages a distributed network discovery engine to scan, identify and profile all assets, including web, cloud, mobile or virtual. Dynamic categorization of all assets and accounts can enable auto-onboarding, and the ability for access policies to self-adjust according to environmental changes.
- Supports privileged session management using standard desktop tools such as PuTTY and Microsoft Terminal Services Client. Administrators can:
- Request RDP/SSH access to authorized systems only
- Start sessions instantly, or via workflow
- View any active privileged session, and if required, pause or terminate the session
- Use keystroke indexing and full text search to pinpoint data, and then log an acknowledgement of the review for audit purposes
- Avoid Java – Password Safe is a client-less solution with no agents required on the server
- Fully integrate with native tools (MSTSC, PuTTY, MobaXterm etc.)
- Gain full video recording with 100% accountability
- Supports threat analytics through audit and reporting, enabling customers to:
- Aggregate user and asset data to baseline and track behavior
- Correlate asset, user and threat activity to reveal critical risks
- Identify potential malware threats buried in asset activity data
- Generate reports to inform and align security decisions
BeyondTrust Endpoint Privilege Management enforces least privilege and eliminates local administrative rights on Windows, Mac, Unix, Linux, and network devices.
BeyondTrust Secure Remote Access provides visibility and control over third-party vendor access, as well as internal remote access, enabling organizations to extend access to important assets to vendors who typically provide systems support – but without compromising security. Privileged Remote Access provides a platform for enterprises to secure, manage, and audit vendor and internal remote privileged access without a VPN.
Thycotic
Washington, DC-based Thycotic has gained a solid reputation for itself over the past several years. Its flagship product, Secret Server, provides a web-based, encrypted repository for IT administrators to store sensitive system level passwords and actively enforce password security policies. Users can auto-generate complex passwords for privileged and shared accounts, as well as automatically rotate passwords over time. Discovery, service account management and session recording capabilities provide requisite accountability.
Organizations use Secret Server to securely store, distribute and manage privileged access data such as server passwords, router passwords and service accounts in a central, web-based password vault. In addition to Secret Server, the company also offers Password Reset Server, an end-user password reset tool, and Group Management Server, a self-service Active Directory (AD) management tool that enables IT administrators to delegate AD group membership to appropriate employees. Thycotic’s PAM architecture is illustrated below.
Figure 10: Thycotic’s PAM Architecture Overview
You can see that the centerpiece is the Thycotic Secret Server, which can run on-premises and in an IaaS cloud platform and has the following key features and functions:
- Vault – Sets granular permissions, users, and structure to map to your organization.
- Discovery – Identify all service, application, administrator, and root accounts to curb privilege sprawl.
- Secrets management – Provision, deprovision, ensure password complexity, and rotate credentials.
- Access delegation – Implement role-based access control, workflow for access requests, and approvals for third parties.
- Session management – Implement session launching, proxies, monitoring, and recording capabilities.
- DevOps security – Remove hardcoded passwords and secure privileged accounts within your software development lifecycle.
- Unix support – Implement Unix command whitelisting and SSH Key Management.
The Thycotic Privilege Manager component enforces least privilege and application control designed to scale to thousands of endpoints. Key Privilege Manager functions:
- Agent deployment – Agents continuously discover endpoints, applications, and processes tied to privileges on domain and non-domain accounts.
- Implement Least Privilege Policy – Removes excess privileges and permanently controls which accounts are members of local groups, including administrators, and controls credentials of accounts in these groups.
- Define Policies – Create granular application control policies for whitelisting, blacklisting, and grey-listing applications based on advanced threat intelligence.
- Elevate Applications – Approve applications that require admin privileges to execute with policy-driven controls that consider endpoint, location, user, and process requested.
Thycotic’s Privileged Behavior Analytics component can generate automated alerts and enforce controls that discover and contain a privileged account breach. With Privileged Behavior Analytics, customer can better understand typical behavior patterns for privileged accounts in order to quickly detect anomalies. Privileged account actions can be viewed and monitored in custom dashboards, which can identify and confirm suspicious activity and alert incident response teams.
Thycotic’s Secret Server SDK for DevOps provides added PAM security in application development. Customers can protect code by removing hardcoded passwords and provide unique accounts and credentials to containers and services. The SDK is intended to help customers avoid using insecure repositories where secrets can be hijacked and exploited.
One Identity
In 2012, Dell Inc. bought Quest Software as part of its plan for fleshing out a software division for the hardware giant. However, this strategy changed following the bold move of acquiring EMC for $67 billion. Dell then sold the Quest and Sonicwall divisions to equity firms Francisco Partners and Elliot Management in 2016. In late 2016, the newly reformed Quest formed One Identity as a wholly owned subsidiary of Quest. Similar to Saviynt, One Identity has a rather strong background in IGA and IAM that helps enable a more well-rounded approach to identity governance and PAM. An illustration of One Identity’s PAM solution, called Safeguard, is shown below.
Figure 11: One Identity’s PAM Solution Overview
Key features of One Identity’s Safeguard PAM solution include:
- Automates and controls the process of granting privileged credentials with full session recording. Privileged access is granted based on established policies with appropriate approvals.
- Session data is captured, indexed, and stored in tamper-proof audit trails that can be viewed like a video and searched like a database.
- Safeguard for Privileged Analytics (an add-on) tracks and graphically represents user activity in real-time for a view of what is happening in the IT environment. This solution removes the need for pre-defined correlation rules, as it works with existing session data. Safeguard for Privileged Analytics creates a baseline of ‘normal’ behavior via data collected from your IT environment.
- Supports a least-privilege security approach with granular delegation of administrative access on UNIX and Windows servers and desktops.
- Removes the stand-alone authentication and authorization requirement of native UNIX in favor of a potentially more secure single-identity/point-of-management functionality available through AD for Microsoft Windows systems. Using the One Identity AD bridge solution (another add-on), enterprises can extend the unified authentication and authorization of Microsoft Active Directory (AD) to UNIX, Linux, and Mac systems.
- Extends the governance capabilities of unified policy, automated and business-driven attestation, enterprise provisioning, and access request and fulfillment to privileged accounts and administrator access. This can simplify privileged governance by enabling organizations to define roles and associated policies, access approval workflows and perform periodic attestation of privileged access.
- Integrates two-factor authentication for an added layer of security. One Identity offers both on-premises and SaaS-based two-factor authentication solutions.
Hitachi ID Systems
Based in Calgary, Alberta Canada, Hitachi ID Systems Originally founded in 1992 as M-Tech Information Technology, Inc. and acquired by Hitachi, Ltd. in 2008. The first product from Hitachi ID was Hitachi ID Bravura Pass, which originally shipped in 1995 as P-Synch. Today, Hitachi ID products are available either individually or as components of the Hitachi ID Bravura Security Fabric – their IAM solution.
Hitachi ID Bravura Privilege can integrate with many popular clients, servers, hypervisors, databases, and applications, whether on premise or in the cloud. It is part of the Hitachi ID Bravura Security Fabric, their IAM platform and framework that includes Hitachi ID Bravura Privilege, Identity, Pass, Group, and Discover. Working within a ‘singular security fabric’, their customers may be able to weave access and privilege patterns more easily by combining Hitachi ID Bravura services as the access management program evolves without having to install separate solutions. This is certainly an important aspect to consider, depending on whether your own IAM environment is more greenfield than legacy burdened.
As you would expect, the object of Hitachi ID’s Bravura Privilege is to replace shared and static passwords tied to privileged accounts with periodically new and random values based on defined password policy controls. As such, Bravura Privilege can enforce multiple scheduled or event-triggered password policies on fixed IT assets, laptops, and rapidly provisioned virtual machines. Some of the solution’s key capabilities include:
- A geographically distributed active-active architecture that replicates PAM functionality in real time across all instances for high-availability and disaster recovery scenarios. Data at rest and in transit is encrypted using a 256 AES encryption key unique to each customer.
- Access to shared accounts and elevated group memberships based on flexible-but-manageable access control policies. High frequency users can be pre-authorized based on group memberships or identity attributes without waiting for approvals. On the other hand, infrequent users can request to gain access when appropriate and for a defined time interval.
- By leveraging the Hitachi ID Bravura Security Fabric, Bravura Privilege customers can enable just-in-time (JIT) PAM, incorporating create, read, update, and delete (CRUD) operations and groups as part of their privileged access disclosure processes on both accounts. Bravura Privilege supports the creation, updating, and deleting of privileged accounts and groups to help customers achieve the principle of Zero Standing Privileges (ZSP) where and when it makes sense to do so.
- The solution randomizes administrator passwords frequently, so that each password is different, changes over time and is not known to anyone. It mediates logins to these accounts, requiring that users be personally identified, strongly authenticated, and specifically authorized for the access. Shared account usage with elevated privileges is linked to individual IT staff to create strong accountability for administrative changes.
- The solution can record keyboard input, take a picture with time and day stamp info, and collect other data key for forensic audits and internal knowledge sharing and training. Session recording, search and playback provide accountability. Recorded sessions are secured through a combination of access control policies and workflow approvals, designed to safeguard user privacy.
- Hitachi ID Bravura Privilege includes advanced infrastructure and auto discovery to collect system inventory data from multiple sources and apply rules to decide which systems to connect and what credentials to use. Systems can be probed to find all accounts, groups, and services. Organizations can apply further rules to decide which accounts and groups to manage and policies to attach to each one.
- Delegated administration provides the ability to designate trustees who can allocate responsibilities to other team members.
While Hitachi ID Systems is a relatively small company (approximately 160 employees), its M-Tech pedigree goes way back. Twenty years ago, M-Tech was a leader in the password management (P-Synch) market and deployed by many organizations, globally. This history and longevity are worth noting, and may be a reason for you to consider them.
Micro Focus/CyberRes
U.K.-based Micro Focus provides a core IAM suite with several optional add-ons, such as IGA and PAM. These solutions largely resulted from the Micro Focus acquisition of Attachmate/NetIQ in 2014 which is based on an offering initially developed by Novell and updated at an accelerated pace. In November 2020, Micro Focus announced the formation of CyberRes, a new business unit of the company that is aligning its cyber security products under a single banner. Now called the CyberRes NetIQ Privileged Account Manager, their solution supports the following PAM features:
- Password checkout for cloud services: secure and share administrative credentials for cloud service providers such as AWS and OpenStack.
- X11 Protocol support – records and monitors sessions carried out within an X Session.
- Secured password vaulting – the solution includes an Enterprise Credential Vault, or an encrypted password “vault,” that provides secure storage of system, application and database passwords.
- Database encryption – the credential vault is a secure embedded database with two levels of encryption. The passwords are encrypted with AES 256-bit keys, and the database is encrypted with a separate AES 256-bit key.
- LDAP Credential Vault – leverage existing LDAP directories, including Active Directory, as a secure credential vault.
- Advanced authentication for privileged accounts – enterprises can create a more layered defense for sensitive assets and resources with multi-factor authentication, step-up authentication, and smartcard support.
- Database privileged account monitoring.
- Securely delegate privileged account authority across database, application and cloud environments.
- Single sign-on to Linux and UNIX servers – authorized users can access servers without entering additional credentials or complex commands.
- Secure remote desktop proxy (RDP) – the solution creates a secure Remote Desktop Proxy (RDP) tunnel to the target Windows host, without exposing the administrative password to the user.
- AD and LDAP authentication – supports authentication against both Active Directory and LDAP identity stores—including NetIQ/Novell eDirectory—for accessing Windows servers.
- Secure remote privileged command execution – allows administrators to execute privileged commands on a UNIX host from a Windows desktop, without requiring users to start an SSH session from the Windows desktop.
- Single configurable port – all agent traffic is encrypted and directed through a single port for easy product configuration and deployment in multi-firewall environments.
- Auto discovery of privileged accounts – helps identify privileged accounts across Windows, Unix, Linux, and Active Directory.
- Simplified agent deployment and management – leverages third party software deployment solutions to deploy and manage agents where required.
- Web-based console – the solution is managed via a web-based console which can be accessed via intranet and extranet zones. The interface includes a command control console that enables the configuration of all privileged user management policies.
- Task-based wizards and drag-and-drop interface – the solution stores Windows administrative passwords in a credential vault that resides within Command Control.
- Windows group and policy enforcement – includes a GUI-based, drag-and-drop user interface to help simplify the rule-creation process and virtually eliminates the need for complex, manual scripting.
- Reusable script and command libraries – the solution includes sample libraries of policy objects that can be simply dragged and dropped to build security rules.
- Hierarchical rule structure – rules can be visually constructed without scripting then dragged and dropped to create rule hierarchies that determine the processing order.
- Failover and load balancing – host agents can be visually configured in hierarchical domain structures that automatically determine load-balancing and failover between components.
- Risk-based privileged session control – risk-analysis tools record and play back user activity—down to the keystroke level. Through the tool enterprises can define high-risk activity controls and enforce them with automatic session termination or access revocation.
- Privileged analytics – risk analysis engine examines user activity in real time and applies color-coded security risk ratings to help detect and address threats faster.
- Real-time keystroke logging – keystroke logs are updated in real time throughout the duration of a user’s session on any UNIX, Linux or Windows host.
- UNIX, Linux and Windows session playback – playback recorded user-session keystrokes in an intuitive interface that is indexed and highly searchable.
- Windows auditing service – the Windows audit service enables administrators to view real-time and historical user activity performed on local or remote Windows hosts. Audited activity includes all actions performed during a privileged session.
- Automatic data filtering for continuous compliance – enterprises can create pre-defined rules to pull events from audit log files using comprehensive filters and schedules.
- Automatic notifications – users can be automatically emailed a daily summary of events awaiting approval.
- Indelible audit record – all auditor activity is indelibly recorded on the event record, including the viewing of keystroke log activity, status changes and any notes recorded during the analysis.
- Workflows – for events that require further analysis, a workflow process escalates events to the appropriate reviewers—either by sending an email notification or flagging the event in the compliance auditor console.
- FTP auditing – enterprises can add an additional layer of security to FTP transactions by using the replacement daemon for fully audited and authenticated FTP transactions.
- Drop in UNIX/Linux shell replacement – privileged commands can be executed on-demand with a ‘usrun’ statement or the user shell replaced to provide command authentication and/or total session auditing.
- ACL restrictions – helps to determine which records individual auditors are allowed to view and prevent users from authorizing their own activity.
Centrify
Santa Clara, CA-based Centrify was founded in 2004. At the time, the company was the first to integrate UNIX and Linux into Active Directory, which was a major step forward in AD security supporting these two important platforms. In 2018, Centrify spun off its IDaaS business as a standalone company named Idaptive. Centrify is redefining the legacy approach to Privileged Access Management by delivering what it calls “cloud ready” Zero Trust Privilege. Centrify Zero Trust Privilege focuses on granting least privilege access based on verifying who is requesting access, the context of the request, and the risk of the access environment. Centrify’s PAM solution portfolio is illustrated below.
Figure 12: Centrify’s Cloud-Ready PAM Solution Portfolio
Acting as a SaaS instance, the Centrify Platform is the hub of this solution portfolio, providing shared services such as workflow-based access requests, MFA, and session recording. See below for an illustration.
Figure 13: The Centrify Platform SaaS Architecture
Key features of Centrify Platform include:
- Discovery tools to automatically discover systems and service accounts for subsequent management.
- Enforcement of centralized control over who can access credentials and audit administrator activity — including securing third-party access.
- Automation tools to support shared account password management for super user and service accounts.
- Single location for emergency access to super user passwords for all on-premises and cloud-based systems and network infrastructure.
- Step-up authentication and secure access to infrastructure without knowing privileged account passwords.
- DevSecOps support with secure storage of encrypted privileged account credentials in the Centrify Privileged Access Service or a key management appliance on-premises (or in the cloud).
- Password vaulting to enable authorized IT administrators, whether internal or outsourced, and third-party vendors to check out passwords for shared accounts, including service, application and database accounts for a limited duration. Password rotation is also supported.
- Authorized users can access resources using shared accounts without knowing the passwords and Centrify will not expose the passwords. IT admins can use shared accounts without encountering the risk of password sharing or unauthorized access.
- Users can initiate RDP and SSH sessions directly from their local Windows systems for privileged access that maintains the same level of security and control for privileged sessions with monitoring, session termination and multi-factor authentication (MFA).
- Anomalous behavior can be detected by enforcing risk-aware policies for users who are initiating a privileged session or checking out a password. Centrify combines information risk-level with role-based access controls (RBAC), user context and multi-factor authentication (MFA) to determine whether to grant privileged access or block it. Dynamically enforced access policies grant the user access, prompt for a second factor of authentication or block access completely.
- Emergency access to privileged account passwords may be obtained from mobile devices enrolled in the Centrify Zero Trust Privilege Services. Secured password checkout requires a PIN or fingerprint validation. Checkout automatically times out based on per-resource policy.
Centrify has been around awhile, with decent market share and experience running “as a Service”. The company was the first to invest and innovate in PAM-as-a-Service in 2015 with their cloud-native PAM platform and vault service. Organizations wanting to run more “as a Service” infrastructure should consider Centrify and the possibility that their cloud-native solution can get you up and running – and much more secure, more quickly than alternative vendors.
Okta
Founded in 2009 by a team of former Salesforce executives, Okta is a cloud-based identity and access management platform built on Amazon AWS. Okta was one of the first IAM solutions built ‘in the cloud’ from the ground up, rather than a cloud-instantiated on-premises solution suite. Their solution has gained a good deal of traction with enterprise customers over the past five years, as more and more companies look to migrate much of their IT infrastructure – including IAM, to the cloud. Okta’s Active Directory synchronization tool provides the primary mechanism for integrating on-premises identity information with Okta’s Universal Directory (cloud directory). The integration between customers’ AD infrastructure and Okta provides SSO to the enterprise applications ‘front-ended’ by Okta, including a broad range of SaaS applications like Workday, SalesForce, etc.
In April of 2019, Okta announced the launching of the Okta Advanced Server Access, which provides access management to help secure its customers’ multi-cloud infrastructure. Via the Okta Identity Cloud, its customers can manage privileged access to on-premises Windows and Linux servers as well as IaaS vendors including Amazon Web Services, Google Cloud Platform, and Microsoft Azure. This solution enables the centralization of privileged access controls to better mitigate the risk of credential theft, reuse, sprawl, and abandoned administrative accounts. Advanced Server Access utilizes an ephemeral client certificate architecture that replaces static keys.Figure 16: Okta’s Advanced Server Access
Figure 16: Okta Advanced Server Access
As show in Figure 16 above, Okta’s Advanced Server Access is geared toward administrator (human user) and service account (service user) integration. Advanced Server Access supports SSH and RDP integration with Windows and Linux servers – whether on-premise or in the cloud. The solution further offers:
- Okta as the single source of truth for local server user and group accounts.
- Automated provisioning & deprovisioning of local accounts.
- Single Sign-On for SSH & RDP workflows.
- Command filtering through the ability to inject contextual access controls in line with server authorization.
- Monitoring and auditing of all privileged logins, providing a record of who accessed what server from which device and when – exposed via Dashboard or exported to a SIEM.
Advanced Server Access uses a lightweight approach to PAM integration, with a Servers Agent that is installed on enterprise servers via bash or powershell commands integrated into the enterprise’s automation tool, such as Ansible, Chef, Puppet and Terraform.
Okta enables lifecycle management of local server group accounts via its Universal Directory, as shown below.
Figure 17: Okta Universal Directory Group Management
Using the Okta Universal Directory, Groups that assigned to Advanced Server Access are provisioned to the downstream application via SCIM (System for Cross-Domain Identity Management). Group membership is then reflected on the downstream applications, and local users are created when assigned to an Okta Project. Any change in groups or group membership is picked up automatically and reflected on the servers immediately.
For those organizations that have invested in Okta as their IDaaS provider, it certainly makes sense to investigate the Okta Advanced Server Access solution as a mechanism for improving multi-cloud access control and privileged administration. One caveat is to be sure to understand your requirements fully, because Okta is a new entrant to the PAM space and their PAM solution portfolio is more nascent than many of its competitors. Alas, there is no silver bullet.
Microsoft
Microsoft has not been a vendor in the PAM market in the past. In fact, the company doesn’t really call it PAM, but Privileged Identity Management (PIM) coupled with Just Enough Access (JEA). Azure Active Directory (Azure AD) PIM is a service that lets Windows-centric organizations manage, control, and monitor access to resources, such as Azure AD, Azure resources, and other Microsoft Online Services like Office 365 or Microsoft Intune. Some of the key features of PIM include:
- Provides just-in-time privileged access to Azure AD and Azure resources.
- Assigns time-bound access to resources using start and end dates.
- Requires approval to activate privileged roles.
- Enforces multi-factor authentication to activate any role.
- Uses justification to understand why users activate.
- Gets notifications when privileged roles are activated.
- Conducts access reviews to ensure users still need roles.
- Downloads audit history for internal or external audit.
- Supports Just-in-Time VM Access, which enables organizations to deny persistent access while providing controlled access to Azure VMs when needed.
For just-in-time access across Azure and Microsoft Online Services such as Azure AD and Office 365, PIM is implemented in the cloud service Azure AD PIM. For just-in-time access to resources in on-premises environments, PIM is implemented using Microsoft Identity Manager (MIM) and Active Directory. JEA can be used for finer-grained authorization for Windows and Windows Server applications.
JEA is a Windows PowerShell toolkit that defines a set of commands for performing privileged activities. In JEA, an administrator decides that users with a certain privilege can perform a certain task. Every time an eligible user needs to perform that task, the administrator enables that permission via MIM workflow. The permissions expire after a specified period, so that a malicious user can’t steal the access. For example, a MIM policy can specify that if a specific user requests administrative privileges and is authenticated by MFA, the request is approved and a separate account for the user will be added to the privileged group in a bastion AD forest.
Assuming the request is approved, the MIM workflow communicates directly with the bastion forest Active Directory to put a user in a group. For example, when Joe requests to administer the HR database, the administrative account for Joe is added to the privileged group in the bastion AD forest within seconds. His administrative account’s membership in that group will expire after a time limit.
For organizations that are mostly – if not completely deployed on Microsoft on-premise and Azure infrastructure, TechVision recommends consideration for PIM and JEA deployment. The mantra stays the same whether you are “all Microsoft” or the more common “mixed bag” – protect your information assets better by thoughtfully deploying PAM. For more complex or multi-cloud platform enterprise infrastructures, we recommend deployment of a leading PAM solution to not only augment PIM/JEA functionality if/where needed, but to extend PAM security across the entire cloud-based ecosystem.
Google’s Cloud Platform (GCP) offers a solution called Cloud Identity & Access Management (Cloud IAM) that lets administrators authorize who can act on specific GCP resources in order to maintain control and visibility of Google cloud resources centrally. Cloud IAM supports access to cloud resources at fine-grained levels, beyond project-level access. GCP Administrators can create more granular access control policies to resources based on attributes like device security status, IP address, resource type, and date/time. A full audit trail history of permissions authorization, removal, and delegation is captured and retained automatically.
While not a PAM solution by any stretch, Google Cloud IAM is the environment where administrators and end users of GCP resources are provisioned and granted access privileges. This is key to PAM deployments within enterprises that are GCP IaaS customers – PAM connectors and agents should integrate with GCP Cloud IAM so that GCP administrator functions can be securely managed whether using the SAPM, SUPM or AAPM methods. This is not a pureplay PAM solution, however, and customers should consider a more feature-rich solution for enabling PAM in both on-premises and multi-cloud environments. GCP Cloud IAM is likely to be sufficiently secure and useable for smaller organizations (e.g., less than 1,000).
Amazon
Amazon Web Services (AWS) promotes a “Shared Responsibility Model” for cloud security that AWS secures cloud access to the cloud from their multitenant customers, but the customer is responsible for securing access within AWS. Amazon introduced Lambda as its automation tool four years ago to facilitate logically centralized administration of AWS/EC2 resources. In AWS, Lambda runs customers’ code on a high-availability compute infrastructure and performs all of the administration of the compute resources, including server and operating system maintenance, capacity provisioning and automatic scaling, code monitoring and logging. Amazon’s Shared Responsibility Model is illustrated below.
Figure 18: Amazon AWS Shared Responsibility Model
Amazon states that when using AWS Lambda, you (the customer) are responsible only for your code. AWS Lambda manages the compute fleet that offers a balance of memory, CPU, network, and other resources. This is in exchange for flexibility, which means customer administrators cannot log in to compute instances or customize the operating system or language runtime. These constraints enable AWS Lambda to perform operational and administrative activities on the customer’s behalf, including provisioning capacity, monitoring fleet health, applying security patches, deploying code, and monitoring and logging Lambda functions.
AWS Lambda creates a unique access risk since services, not people, trigger its cloud activities. However, organizations often use Lambda to run administrative and operational processes, such as patch updates, that require privileged access to systems and networks.
Nevertheless, to help secure your AWS resources, Amazon only offers these recommendations for the AWS Identity and Access Management (IAM) service:
- Lock away your AWS account root user access keys
- Create individual IAM users
- Use user groups to assign permissions to IAM users
- Grant least privilege
- Get started using permissions with AWS managed policies
- Validate your policies
- Use customer managed policies instead of inline policies
- Use access levels to review IAM permissions
- Configure a strong password policy for your users
- Enable MFA
- Use roles for applications that run on Amazon EC2 instances
- Use roles to delegate permissions
- Do not share access keys
- Rotate credentials regularly
- Remove unnecessary credentials
- Use policy conditions for extra security
- Monitor activity in your AWS account
In summary, Lambda’s automation creates new privileged access management (PAM) risks as it connects to applications and infrastructures without human governance. That said, AWS is much like Google Cloud Platform – YOU are responsible for privileged access management. Most of the leading vendors in the PAM marketplace are cognizant of this and are focusing on continued extension and expansion of their PAM solutions to better secure infrastructures deployed on IaaS and SaaS cloud platforms.
Recommendations
This report covered several topics centered on Privileged Access Management. We looked at business drivers (why you need it), solution evolution and future trends, common approaches, and architectural patterns. We summarize our findings with the following key recommendations for PAM deployment consideration:
- Establish Governance for Privileged Accounts. For most of our customers, TechVision recommends an aggressive program to manage privileged accounts. Many of our customers have PAM programs underway and at various rates of efficacy, and we often recommend these existing programs continue to expand. In most customer scenarios, only SAPM has been deployed and only to a smaller number of higher risk systems – which is good, of course. But for a program to be effective, the risk lens needs to continue to expand – always in search of the ‘weakest link’. This means AAPM should rise in priority for many organizations, as service accounts tend to be widely unmanaged – and in many cases, unknown entities. The use of privileged access discovery tools, as we discussed in this document is a great way to keep the needle moving in terms of finding and fixing privileged access. With customers expanding rapidly into the cloud, this becomes more important than ever. Every day, things change.
- Deploy and Integrate with IGA. IGA tools are critical for governing, monitoring and auditing ‘who has access to what’. This question is of particular importance when focusing on key, high-risk systems or environments. A good IGA tool can help identify and isolate privileged accounts in all four categories (SAPM, SUPM, PSM, AAPM) and just as importantly – continuously monitor these accounts and privileges. Linking PAM with IGA is the best method for increasing your visibility and remediation ability across the wide spectrum of on-prem and in the cloud environments.
- Secure Cloud Environments. Enterprises should continue to develop clear policy and standards of good practice requiring controls on the granting and use administrative privilege for all in-house and cloud-based IT systems and applications. The policy guidelines should address IT privilege assignment, revocation, change, login credential management, session management by setting minimum requirements by low, medium or high-risk levels. These practices will require some degree of collaboration with outsourced service providers, particularly those responsible for managing the enterprise’s core IT infrastructure.
- Establish and Enforce Enterprise PAM Policies. It is generally recommended that all PAM-related policies be approved by the IAM governance body, the CISO, and the CIO to ensure top-down buy-in. Compliance with these policies should also be phased in globally, as appropriate, but never at the expense of significant risk exposure. As such, the planning process for phasing PAM in must be closely aligned with the affected IT systems or application road map and architecture strategy. Standard, policy-compliant operating procedures for PAM must be tightly aligned with the relevant IT and application administration operational teams, including strategic outsourced service providers.
- Raise Awareness. A critical success factor for the adoption of PAM will be centered on the vigilance of the PAM Program Manager with strong people skills and experience with complex project management. Be advised that the Program Manager role may need to be augmented by a subject matter expert with specific expertise in the selected solution(s). Enterprises should acknowledge that “marketing” PAM can be a challenge in the most collaborative environments; the necessary operational changes may cause some push back with outsourced service providers. Adequate training and awareness will be necessary to achieve the needed buy-in from administrators and stakeholders.
Other good practices include:
- Reduce the number of users with (permanent, full) superuser privileges to the minimum that is consistent with operational and business needs. Minimize the use of shared privileged accounts, too.
- Limit the scope across the infrastructure of any system administrator’s superuser privileges to what is consistent with business and operational needs.
- Restrict and time-limit the privileges for each privileged account. Set up discrete privileged and unprivileged accounts for each system administrator. If administrators’ accounts have permanent superuser privileges, it is recommended that they have alternate accounts for day-to-day use, while their superuser accounts should have severely restricted Internet access.
- Use risk-appropriate authentication methods, such as MFA for privileged accounts. Superuser privileges that are assigned to personal accounts (e.g., JIT PAM) should be protected with risk-appropriate authentication methods such as MFA, as well.
- Stop using shared passwords. Sharing passwords, even among approved users, severely limits the possibility of personal accountability that is a security best practice and demanded by regulatory compliance.
- Enable default administrator, root and similar accounts only in exception circumstances. The account should always be available when needed, but if it’s in use all the time, it’s not guaranteed that the password will be known or available to anyone who needs to use it in an emergency. Use a SUPM tool to manage this reliably and securely.
- Set up custom “fire call” or “break glass” accounts for emergency purposes.
- Monitor and reconcile all privileged account activity. As in other areas of IAM and information security, logging, monitoring, reporting and analysis of privileged account activity are essential detective and corrective controls.
It is worth noting that more than one PAM tool may be required for different aspects of the IT infrastructure. Generally, the leading PAM solutions tend to be relatively equal with respect to functionality for Windows and *NIX operating systems. However, fit-for-purpose solutions augmented by manual practices may be required for networking infrastructure, security infrastructure, and any other special-purpose components within the enterprise IT landscape. While a single PAM solution is ideal, enterprises should not hesitate to select multiple products should requirements, constraints, or dependencies dictate – especially when considering multiple-cloud environment integration.
We hope you have found this report useful. TechVision Research feels that PAM is one of the more critical elements of an enterprise security posture. Hackers and thieves want your privileged account access rights because that is the way to your data – whether in your data center or in the cloud. This is not fearmongering! We have seen a horrific rise in large-scale, nationwide ransomware attacks in 2020 and 2021. IT and OT environments are both at substantial risk. PAM is the most viable means to respond to these attacks.
So, no matter how far along you are (or aren’t) in PAM deployment, don’t delay moving the needle forward. If you’re a ways’ behind, don’t boil the ocean – start with the highest risk environments. If you’re pretty far along, keep it up by adding the right features that will improve your cloud security, DevOps and automation capabilities. There are very good tools on the market and now is the time to be proactive.
About TechVision
World-class research requires world-class consulting analysts, and our team is just that. Gaining value from research also means having access to research. All TechVision Research licenses are enterprise licenses; this means everyone that needs access to content can have access to content. We know major technology initiatives involve many different skillsets across an organization and limiting content to a few can compromise the effectiveness of the team and the success of the initiative. Our research leverages our team’s in-depth knowledge as well as their real-world consulting experience. We combine great analyst skills with real world client experiences to provide a deep and balanced perspective.
TechVision Consulting builds off our research with specific projects to help organizations better understand, architect, select, build, and deploy infrastructure technologies. Our well-rounded experience and strong analytical skills help us separate the “hype” from the reality. This provides organizations with a deeper understanding of the full scope of vendor capabilities, product life cycles, and a basis for making more informed decisions. We also support vendors in areas such as product and strategy reviews and assessments, requirement analysis, target market assessment, technology trend analysis, go-to-market plan assessment, and gap analysis.
TechVision Updates will provide regular updates on the latest developments with respect to the issues addressed in this report.
About the Author
 Doug Simmons brings more than 25 years of experience in IT security, risk management and identity and access management (IAM). He focuses on IT security, risk management and IAM. Doug holds a double major in Computer Science and Business Administration.
Doug Simmons brings more than 25 years of experience in IT security, risk management and identity and access management (IAM). He focuses on IT security, risk management and IAM. Doug holds a double major in Computer Science and Business Administration.
While leading consulting at Burton Group for 10 years and security, and identity management consulting at Gartner for 5 years, Doug has performed hundreds of engagements for large enterprise clients in multiple vertical industries including financial services, health care, higher education, federal and state government, manufacturing, aerospace, energy, utilities and critical infrastructure.