Microsoft Entra as a Complete IAM Platform
Published 1 November 2022
Abstract
Microsoft has been a dominant force in enterprise Identity and Access Management (IAM) since the introduction of Active Directory (AD) in 1994. While Active Directory is a primary enterprise directory in over 90% of large organizations, the limited traditional breadth of AD capabilities has opened the door for complementary (or competing) IAM related cyber security capabilities such as Single Sign On (SSO), Multi-Factor Authentication (MFA), Identity Governance and Administration (IGA), IAM Lifecycle Management, and Privileged Access Management (PAM). These key capabilities have been delivered by vendors such as Okta, SailPoint, Saviynt, CyberArk, BeyondTrust, Thycotic/Delinea, Ping Identity, Radiant Logic, and others.
Microsoft Entra represents a significant upgrade to Microsoft’s traditional IAM program as they plan to offer capabilities that address many of IAM security gaps within Microsoft’s portfolio and to provide a more comprehensive enterprise Identity, Security and Governance ecosystem. There are five main products supporting the initial Microsoft Entra program: Microsoft Azure Active Directory, Microsoft Entra Permissions Management, Microsoft Entra Workload Identities, Microsoft Entra Identity Governance, and Microsoft Entra Verified ID, and each element will be explained and assessed in detail. We’ll do this by referencing a set of typical enterprise requirements as well as assessing how Microsoft’s current and expected future Entra offerings fits within our Reference Architecture for IAM.
Authors:
| Doug Simmons
Principal Consulting Analyst |
Gary Rowe
CEO/ Principal Consulting Analyst |
Executive Summary
Microsoft has been a dominant force in the IT world for as long as many readers of this report have been alive. When Local Area Networks (LANs) stormed the IT landscape more than a few decades ago, Microsoft introduced Active Directory (AD) as a both a means to administer and manage a rapidly growing user base of desktop personal computers, and in response to the growing dominance of Novell Network Directory Services (NDS).
Microsoft Entra is the product family name for Microsoft’s identity and access products. It is not just a renaming/rebranding of Azure AD, which remains a significant centerpiece of the Entra strategy, but adds several key Identity and Security elements. There are five main products supporting the initial Microsoft Entra program: Microsoft Azure Active Directory, Microsoft Entra Permissions Management, Microsoft Entra Workload Identities, Microsoft Entra Identity Governance, and Microsoft Entra Verified ID, and each element will be explained and assessed in detail. Microsoft Entra’s high-level capabilities are intended to achieve (per Microsoft) the following results:
- Protect access to any application or resource for every identity.
- Secure and verify every identity, including employees, contractors, customers, partners, devices, applications, and workloads.
- Provide only necessary access by managing identity lifecycles and ensuring least privilege for any identity – including people and resources (i.e., apps and service accounts).
- Simplify the user experience by simplifying the authentication process utilizing intelligent security and unified administration.
With Entra, Microsoft emphasizes the need for a “trust fabric driving zero trust”, which to most readers is something that resonates quite well. We feel zero trust is a journey more than a destination and its basic philosophy of identity centric authentication and authorization is a fundamental approach to cyber security we have been advocating for many years.
It should be clear that Microsoft is not only staying in the IAM market but looking to expand to such a degree as to render other IAM solutions irrelevant. That is an extremely aggressive goal. However, there are merits to such a goal. For instance, Microsoft Active Directory and the Windows server and desktop network operating system practically dominate the global enterprise market. With the advent of cloud computing a couple of decades ago, Microsoft rolled out Azure to compete head-to-head with Amazon and Google. Over that same timeframe the company invested in bringing their enterprise computing solution into Azure and then flipping the legacy enterprise model on its head by making Azure and Azure Active Directory the center of the Microsoft IAM universe.
While this was happening, enterprise customers needed solutions at various points in time that enabled key IAM related cyber security capabilities such as SSO, MFA, IGA and PAM. Vendors like Okta, SailPoint, Saviynt, CyberArk, BeyondTrust, Thycotic/Delinea, Radiant Logic and many others filled this void and have become entrenched in many enterprises with varying degrees of success. But there has always been an important question lurking in the backs of minds of IAM architects as to why Microsoft hasn’t been able to meet the demands associated with mature IAM capabilities across the board.
This could be changing with Entra. For the first time it appears as though Microsoft has struck paydirt in the broader IAM market. Entra has brought to bear the capabilities direly needed in a compelling way. Most large enterprises have, in fact, already invested heavily in Microsoft. We have worked with thousands of organizations over many years and are hard-pressed to recall even one that does not have a major Windows/Active Directory/Azure footprint.
Granted, there are often reasons why an organization does not want to “put all their eggs in one basket” and run the risk of vendor lock-in. But we’re talking about Microsoft here, not a new upstart vendor with a shiny new solution. Microsoft is going to be around for a long time – much longer than anyone who is nervous about a career-ending decision to select an inferior solution. We normally have been reluctant to push our customers to build out their infrastructure using a single vendor’s solution suite. In fact, we’ve almost as a rule been recommending “best of breed” solutioning to fit the various capabilities of the IAM Reference Architecture with the best of the best. The “best of breed” argument is becoming more difficult to make as Microsoft upgrades it’s IAM program.
For many large enterprises the cost effectiveness of leveraging an existing enterprise-wide licensing agreement for Microsoft Azure that includes Microsoft 365 and Azure AD will certainly factor into the business side of the IAM strategy. There may likely be other IAM solutions in place across the organization that are effectively no longer necessary as Microsoft introduces new capabilities via Entra. This may bring very significant cost saving to the organization in terms of end user licensing but also in terms of integration costs and user experience costs.
We also see many of our customers currently reliant upon Microsoft Identity Manager (MIM), which has recently extended its end-of-life to 2029. The replacement for MIM is Azure AD and Entra. Even though 2029 is six years away, the time to migrate is sooner rather than later. The migration path from MIM to Azure AD is much more straightforward than to any other 3rd party identity provisioning and governance solution. Yes, there will be somewhat of a learning curve, but for Microsoft shops, this is nothing extraordinary. Product evolution should be expected, and the enormous transformation from on-premises IT to in-cloud IT in general, spurs such evolution.
Our first in-depth look at Entra shows that there is a good reason for enterprise identity and security groups to increase the Microsoft capabilities that are ideally already at their disposal. This tectonic shift may need to take a “crawl, walk, run” strategy in order to bring measurable improvements on a regular cadence. However, as Lao Tzu once said, “every journey begins with a single step”. Taking small but increasingly larger steps down the Microsoft Entra path to IAM enlightenment may benefit many organizations that are already heavily invested in Microsoft products and solutions.
Introduction
Almost every large enterprise and certainly most of our customers reading this report have a large base of Microsoft Active Directory, Azure AD and hooks into various Microsoft applications and security services.
We’ll start with a look at Microsoft’s traditional portfolio of IAM and related products/services and expand to look at the new offering and expected future state IAM program under the Microsoft Entra umbrella. First, we’ll dive into Active Directory.
Active Directory
Active Directory (AD) is a directory service developed by Microsoft for Windows domain networks. It is included in most Windows Server operating systems as a set of processes and services. Initially, Active Directory was used only for centralized domain management. However, Active Directory eventually became the common term to represent a broad range of directory-based identity-related services, as will become more apparent throughout this report.
A server running the Active Directory Domain Service (AD DS) role is called a domain controller. It authenticates and authorizes all users and computers in a Windows network, assigning and enforcing security policies for all computers, and installing or updating Windows server software. AD also establishes the framework to deploy other related Microsoft services, such as:
- Certificate Services (MS CS) – establishes an on-premises public key infrastructure (PKI) that can create, validate, and revoke public key certificates for internal users and uses of an organization. For example, such certificates can be used to encrypt files, emails and network traffic.
- Active Directory Federation Services (ADFS) – enables a single sign-on (SSO) service that allows users to access network resources using only one set of credentials stored in AD. ADFS uses many popular open standards to pass token credentials such as SAML, OAuth or OpenID Connect.
- Lightweight Directory Services (LDS) – utilizes the Lightweight Directory Access Protocol (LDAP) v3, which has been the predominant Internet directory services protocol for nearly 30 years. LDS shares the code base with AD and provides the same functionality, including an identical API, but does not require the creation of domains or domain controllers.
- Rights Management Services – is server software for information rights management shipped with Windows Server that uses encryption and a form of selective functionality denial for limiting access to documents such as corporate e-mails, Microsoft Word documents, and web pages. Access limitations include viewing, editing, copying, saving as or printing for example.
- Azure Active Directory Connectivity – useful tools are provided, such as Azure AD Connect and Azure AD Sync, which help customers connect their on-prem AD to Azure AD for a unified IAM platform.
Additionally, Active Directory uses Microsoft’s version of Kerberos, and Domain Name Services (DNS).
This important underpinning of numerous organizations’ global workforce networks has become pretty much ubiquitous. While AD is exceedingly popular and widely deployed, in some ways it is only as good as the information it maintains. In other words, AD is an intelligent repository, but it needs to be populated with accurate information regarding users and computers. This reality leads to a conundrum regarding what information to store and how to get that information into AD (and LDS), as we discuss next.
Identity Data Integration
Microsoft was aware of the identity data integration challenge early on in the evolution of IAM. In 1999, Microsoft acquired a company called Zoomit, which at the time had a very advanced identity data integration toolset referred to as a meta-directory. It consisted of an advanced (at the time) scripting environment that enabled identity technicians to connect source identity information databases, such as a PeopleSoft (Oracle) HR database with a rules engine that could write information into AD. At the time, this was a big step forward because it allowed organizations to systematically update AD with accurate user information, today typically referred to as the Joiner/Mover/Leaver (JML) set of processes. This solution was called the Microsoft Metadirectory Server (MMS).
Shortly after this (i.e., 2003), Microsoft used this experience to roll out the Microsoft Identity Integration Server (MIIS). MIIS replaced the proprietary “zscript” language with the emerging .Net framework. In the nearly 20 years since the availability of MIIS, it has received numerous updates and name changes. In 2007, it was called the Identity Lifecycle Manager (ILM). In 2008, it became the Forefront Identity Manager (FIM) and in 2016 it became the Microsoft Identity Manager (MIM) – as it is known today.
Over this lengthy period, organizations around the world deployed these various instantiations of AD integration tools in incredible numbers. While many vendors came and went and came back again, such as IBM, Oracle, Waveset, SailPoint, Novell, ForgeRock, Ping, Radiant Logic and so on, MIM is by far the most prevalent (if not popular) tool for identity data integration with AD.
MIM is by no means perfect. MIM does not include intelligent workflow capabilities, identity access governance, data transformation and virtualization or redundancy/scalability – this must be built by the organizations’ deployment staff. This is an important fact to consider, as it led thousands of organizations to deploy somewhat redundant IAM solutions to achieve a requisite level of integration and functionality. In other words, MIM was useful, but certainly not the end all, be all for most organizations’ identity data integration and lifecycle management requirements.
Azure and Azure AD
Arguably, the “cloudification” of the IT world began in the mid-to-late 2000s with the advent of public cloud offerings such as Google Cloud Platform (GCP), Amazon Web Services (AWS), too-many-to-list software as a service (SaaS) environments and Microsoft Azure.
The Azure cloud service is operated by Microsoft for application management via Microsoft-managed data centers, providing SaaS, platform as a service (PaaS) and infrastructure as a service (IaaS) capability. Azure supports many different programming languages, tools, and frameworks, including both Microsoft-specific and third-party software and systems.
Azure is utilized by pretty much every Microsoft shop today in some capacity. Azure Active Directory (Azure AD) is used to synchronize on-premises AD directories and enable SSO to these SaaS, PaaS or IaaS applications supporting the organization. Companies that use Microsoft 365 (aka “O365”) receive an Azure AD subscription to integrate their on-premises Active Directory environments to with Azure AD to synchronize user accounts, passwords and to set up single sign-on across the Azure and on-premises application spectrum – including support for multi-factor authentication (MFA) and passwordless authentication (Windows Hello).
This has proven to be very popular with Microsoft customers. There remains an elephant in the room, however, in that while Azure, Azure AD and Microsoft 365 work well together, many organizations have deployed applications on other cloud platforms as well – namely, GCP and AWS and the administration and access control of these environments from within the Azure framework left much to be desired. This situation leaves many organizations with no choice but to purchase and deploy more 3rd party solutions to bridge multi-cloud/hybrid cloud environments.
Privileged Access Management
Most current-day PAM solutions take privileged account credentials, such as systems administrator and application service accounts, and put them inside a secure repository typically called a ‘vault’. Once inside the vault, system administrators and application service accounts need to go through the PAM system to access the credentials in the vault, at which point they may authenticate to the target system and their access is monitored and logged. When the credential is checked back into the vault, it is reset to ensure administrators must go through the PAM system next time they want to use a credential from the vault. This method of vaulting credentials (or ‘secrets’) and checking credentials in and out on a real-time, as-needed basis accounts for the majority of PAM approaches today.
This being said, Microsoft has not been a vendor in the PAM market in the past. In fact, the company doesn’t really call it PAM, but Privileged Identity Management (PIM) coupled with Just Enough Access (JEA). Azure Active Directory (Azure AD) PIM is a service that lets organizations manage, control, and monitor access to resources, such as Azure AD, Azure resources, and other Microsoft Online Services like Office 365 or Microsoft Intune. Some of the key features of PIM include:
- Provides just-in-time privileged access to Azure AD and Azure resources
- Assigns time-bound access to resources using start and end dates
- Requires approval to activate privileged roles
- Enforces multi-factor authentication to activate any role
- Uses justification to understand why users activate
- Gives notifications when privileged roles are activated
- Conducts access reviews to ensure users still need roles
- Downloads audit history for internal or external audit
- Supports Just-in-Time VM Access, which enables organizations to deny persistent access while providing controlled access to Azure VMs when needed
With this little bit of a “historical perspective” of Microsoft’s IAM solution set, let’s see what the company established as its way forward beginning midway through 2022.
Enter Entra
As indicated in the previous section, Microsoft has established a very impressive installed base of its Azure AD and related solutions over the past 25+ years. In that same timeframe, we have worked as IAM consultants for major corporations in every industry, from Agriculture to Zoology and everything in between and we are hard pressed to name even one company that does not use some facet of Microsoft IAM technology, be it AD, Azure AD, ADFS, Microsoft MFA or MIM. Most use all of these features.
However, Microsoft has borne the brunt of significant criticism over the years because many of its customers want – and need, more. For instance, identity lifecycle management – including account provisioning/de-provisioning, seamless integration with identity data sources (e.g., HR systems, both on-premises and SaaS models), access governance, privileged access management for administrators of the entire IT ecosystem – not just the Microsoft pieces, but also GCP, AWS, SaaS workloads, endpoint management and security, and more.
Often, Microsoft would rebrand an existing solution rather than re-architecting a solution from the top. Witness, the identity data integration journey from MIIS to ILM to FIM to MIM. In fact, the identity data integration and identity lifecycle management needs have been largely the focus of criticism of Microsoft’s IAM strategy.
Having worked in this industry for decades, we have been aware of the IAM challenges facing Microsoft throughout this period and have witnessed the pain of many of its customers. When Microsoft announced Entra on May 31, 2022, as a “new product family to help secure access for a connected world” we were surely hopeful – but also a bit skeptical. Was this yet another rebranding of existing IAM-centric technology to lure existing (and new) customers into the belief that “this time they really mean it”? Let’s have a look:
According to in-depth product briefings provided by Kaitlin Murphy, Director of Product Marketing and Pamela Dingle, Director of Identity Standards, with the TechVision analyst team, Microsoft Entra is the new product family name for Microsoft’s identity and access products. It is not a renaming/rebranding of Azure AD, which remains a significant centerpiece of the Entra strategy. They chose the name Entra because they’re expanding functionality in several areas and wanted a name to convey “modern access security across a broad range of products.”
According to Kaitlin and Pamela, Microsoft emphasizes the need for a “trust fabric driving zero trust”, which to most readers is probably something that resonates quite well. Of course, zero trust is now an overused term that many security professionals deem more hype than reality. Nevertheless, TechVision feels zero trust is a journey more than a destination and its basic philosophy of identity centric authentication and authorization is a fundamental approach to cyber security we have been advocating for many years. For deeper insight into zero trust networking and identity management approaches, please see TechVision Research reports on “Zero Trust Networking” and “Zero Passwords in a Zero Trust World”, respectively.
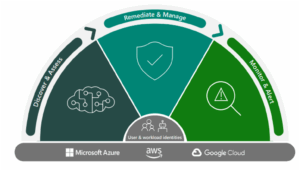
The Trust Fabric Microsoft describes is a merging of networking, identity management and device management in a multi cloud and hybrid world, which is basically consistent with our own view. This is further exemplified with Microsoft’s increased focus on machine learning and artificial intelligence to manage adaptive access control and governance. It is also refreshing to see they emphasize that an organization’s boundaries extend way beyond their own internal network to include business partners, managed service providers and so on. Illustratively then, Microsoft offers the following high-level view of Entra:
Figure 1: Microsoft Entra in a Nutshell (Source: Microsoft)
Entra’s proposed high level capabilities are:
- Protect access to any application or resource for every identity.
- Secure and verify every identity, including employees, contractors, customers, partners, devices, applications, and workloads.
- Provide only necessary access by managing identity lifecycles and ensuring least privilege for any identity – including people and resources (i.e., apps and service accounts).
- Simplify the user experience by simplifying the authentication process utilizing intelligent security and unified administration.
Let’s now take a look at each of these capabilities in the following sections.
Azure Active Directory
We described Azure AD (Azure AD) in the previous section, as it has been and will remain a cornerstone of Microsoft’s multi cloud and hybrid IAM journey. That’s a good thing, because as we’ve said, we would be hard-pressed to identify any medium or large enterprise that does not utilize AD and Azure AD. Effectively, they have become ubiquitous in the approach to network operating system (NOS) and related applications and services authentication and authorization of end users. We often recommend not throwing out the baby with the bathwater.
Until further notice, all identity and access management capabilities rely on a repository to store information about users, applications, services, policies and so forth. The extensibility and scalability of the identity repository is of utmost importance, and Azure AD seems to fit the bill.
IT administrators typically use Azure AD to control access to enterprise applications and application resources based on their business requirements. For example, administrators can configure Azure AD to require multi-factor authentication when accessing important, higher risk organizational information resources. Azure AD can also be used to automate user provisioning between existing on-premises Windows Server AD and cloud apps, including Microsoft 365. A summarization of the many capabilities supported by Azure AD are as follows:
- Application management of cloud and on-premises apps using Application Proxy, single sign-on, the My Apps portal, and Software as a Service (SaaS) apps.
- Authentication management via self-service password reset, MFA, custom banned password list, and smart lockout.
- Application development of apps that sign in all Microsoft identities, get tokens to call Microsoft Graph, other Microsoft APIs, or custom APIs.
- Business to Business (B2B) support for guest users and external partners, while maintaining granular access control.
- Business to customer (B2C) support allowing customization and control of how customer users sign up, sign in, and manage their profiles when using enterprise B2C apps.
- Conditional Access to cloud apps, including user entity behavior analytics (UEBA).
- Domain services that can join Azure virtual machines to a domain without using domain controllers.
- Management of license assignments, access to apps, and set up delegates using groups and administrator roles.
- SSO to provide a single user identity for authentication and authorization to all resources.
- Management of the organization’s identity through employee, business partner, vendor, service, and app access controls, including access reviews.
- Detection of potential vulnerabilities affecting the organization’s identities, configuring policies to respond to suspicious actions, and taking appropriate action to resolve them.
- Management of identities of Azure resources by providing Azure services with an automatically managed identity in Azure AD that can authenticate any Azure AD-supported authentication service, including Azure Key Vault.
- Proactive monitoring to gain insights into the security and usage patterns in across the multi cloud/hybrid environment.
From our perspective, these are significant capabilities, which we will discuss in terms of our Reference Architecture for IAM in subsequent sections.
Deployment-wise, Azure AD is typically deployed as a dedicated and trusted AD instance in the Azure cloud, called a Tenant. A single tenant is automatically created when an organization pays for a Microsoft cloud service subscription. These subscriptions include Azure, Microsoft Intune (mobile device management), or Microsoft 365. An Azure tenant represents a single organization. Azure tenants that access other services in a shared environment across multiple organizations are referred to as multi-tenant. There are also tenants for B2B and B2C services that encapsulate these principles.
Identity Governance
Application and system ‘owners’ generally have the responsibility to manage access to their environments and data within, but this capability becomes extremely onerous as time progresses. This is largely the fundamental reason that the specialized segment of IAM called Identity Governance and Administration (IGA) emerged nearly 15 years ago. In a nutshell, IGA combines entitlement discovery, the decision-making process, and the access review and certification of access governance with the identity lifecycle and role management of user provisioning. For many organizations today, IGA has become a critical service that provides operational management, integration, information security and overall integrity for an enterprise IAM program.
IGA operates at the intersection of business process management and access automation allowing people and systems to communicate with each other, fulfilling day-to-day operational needs. A comprehensive IGA program across diverse constituencies can help identify and manage these risks and address compliance requirements.
Organizations looking to get a handle on how access is being granted and managed over time and would like to evolve toward a “least privilege” approach to issuing access, should consider how IGA can help achieve these goals. Identity Governance Administration requires a fundamental understanding the current state of entitlements across all of the critical systems throughout the enterprise as well as what operations and data to which they actually grant access.
These capabilities include access certification, access request, role management, and the automated fulfillment and enforcement of changes to entitlement settings through identity lifecycle management as well as applying entitlement risk scoring in adaptive access control systems and aligning roles and activities with privileged access management. For a much more detailed investigation and analysis of IGA requirements and deployment best practices, please refer to the TechVision document titled “Establishing a Modern-Day Identity Governance and Administration (IGA) Framework”.
Microsoft defines IGA as Microsoft Entra Identity Governance. AD and Azure AD play central roles in the Entra identity access governance model. As illustrated below, the organization’s existing on-premises AD identity database (i.e., Windows Server Azure Directory) can be linked with the Azure AD cloud environment using Azure AD Connect.
Figure 2: Entra Identity Access Governance (Source: Microsoft)
Identity lifecycle management is how identities first become provisioned in Azure AD. Microsoft Entra Identity Governance provides automated provisioning from human resources (HR) apps to Azure AD, from Azure AD to apps, and between Azure AD and on-premises Active Directory domain services. Illustrated below is Microsoft’s illustration of the typical Azure centric identity lifecycle landscape.
Figure 3: Entra Identity Lifecycle Management (Source: Microsoft)
In Azure AD, as in other IAM solutions, “provisioning” refers to automatically creating user identities and roles based on certain conditions. In addition to creating user identities, automatic provisioning includes maintenance and removal or deprovisioning of user identities as status or roles change.
Azure AD application provisioning refers to automatically creating user identities and roles in the applications that users need to access. In addition to creating user identities, automatic provisioning includes the maintenance and removal of user identities as status or roles change. Common scenarios include provisioning an Azure AD user into SaaS applications like Dropbox, Salesforce, ServiceNow, and more.
Azure AD also supports provisioning users into applications hosted on-premises or in a virtual machine without having to change firewall rules. If the application supports the System for Cross-Domain Identity Management (SCIM), or the organization has built a SCIM gateway to connect to legacy applications, the Azure AD provisioning agent can be used to connect with the application and automate provisioning and deprovisioning. If there are legacy applications that don’t support SCIM and rely on an LDAP user store or a SQL database, Azure AD can support those as well.
To manage the identity lifecycles of employees, vendors, or contingent workers, the Azure AD user provisioning service offers “out of the box” integration with cloud-based human resources (HR) applications. Examples of such integrated applications include Workday or SuccessFactors, which are accessible directly from Azure AD to their respective APIs. Azure AD uses this integration to enable the following cloud HR application (app) workflows:
- Provision users to Active Directory: Provision selected sets of users from a cloud HR app into one or more Active Directory domains.
- Provision cloud-only users to Azure AD: In scenarios where Active Directory isn’t used, provision users directly from the cloud HR app to Azure AD.
- Write back to the cloud HR app: Write the email addresses and username attributes from Azure AD back to the cloud HR app.
We consider this level of direct integration with ever-popular cloud-based HR solutions as very advantageous for many of our customers. However, for integration with on-premises HR databases, Microsoft still recommends using the Microsoft Identity Management (MIM) tool, even though MIM is theoretically end-of-life – yet supported until 2029. We will watch this carefully but bear in mind that Microsoft is going “all in” on cloud integration and this may leave many organizations saddled with sizeable legacy on-premises environments wanting for better Microsoft Entra integration tools. There will likely be much anticipation of new out-of-the-box source system connections but suffice it to say that having Workday and SuccessFactors connectivity available today is noteworthy.
Also regarding MIM, Microsoft is investing in MIM migration tools to help their customers move away from MIM and into Entra in a thoughtful, reasonably paced manner so that most, if not all, of their customers will be satisfactorily off of MIM entirely well before 2029. In this regard, we do not feel that Microsoft is ignoring the significant effort required by its customers to move to Entra. Put another way, these tools and timeframe should support a well-orchestrated migration.
Workflows
Lifecycle Workflows are a Microsoft Entra Identity Governance capability in the Azure spectrum. The other capabilities are entitlement management, access reviews, Privileged Identity Management (PIM), and terms of use. Together, they are positioned by Microsoft to address these questions:
- Which users should have access to which resources?
- What are those users doing with that access?
- Is there effective organizational control for managing access?
- Can auditors verify that the controls are working?
- Are users ready to go on day one or do they have access removed in a timely manner?
A lifecycle workflow can be broken down in to the following three main parts:
| Workflow part | Description |
| General information | This portion of a workflow covers basic information such as display name and a description of what the workflow does. |
| Tasks | Tasks are the actions that will be taken when a workflow is executed. |
| Execution conditions | The execution condition section of a workflow sets up: – Who(scope) the workflow runs against – When(trigger) the workflow runs |
Creating a workflow via the Microsoft Entra admin center requires the use of a template that can be extended to include Azure Logic Apps, the Azure cloud-based platform for creating and running automated workflows that integrate apps, data, services, and systems. A Lifecycle Workflow template is a framework that is used for pre-defined tasks and helps automate the creation of a workflow.
The template is used to define the task that is to be used and then guide the creation of the workflow by providing input for description information and execution condition information. Lifecycle workflows, which is in public preview as of this writing, currently has six built-in templates to use or customize. The current list of lifecycle workflow templates are as follows:
- Onboard pre-hire employee
- Onboard new hire employee
- Real-time employee termination
- Pre-Offboarding of an employee
- Offboard an employee
- Post-Offboarding of an employee
Entitlement Management and Access Reviews
Entra Identity Governance’s entitlement management feature enables organizations to manage identity and access lifecycles by automating access request workflows, access assignments, reviews, and expiration. It is used to manage access to groups, applications, and SharePoint Online sites for internal users, and also for users outside the organization who need access to those resources. Here are some of capabilities of entitlement management:
- Control who can get access to applications, groups, Teams and SharePoint sites, with multi-stage approval, and ensure users don’t retain access indefinitely through time-limited assignments and recurring access reviews.
- Give users access automatically to those resources, based on the user’s properties like department or cost center, and remove a user’s access when those properties change (preview).
- Delegate to non-administrators the ability to create access packages. These access packages contain resources that users can request, and the delegated access package managers can define policies with rules for which users can request, who must approve their access, and when access expires.
- Select connected organizations whose users can request access. When a user who isn’t yet in the organizational directory requests access, and is approved, they’re automatically invited into the directory and assigned access. When their access expires, if they have no other access package (see below) assignments, their B2B account in the directory can be automatically removed.
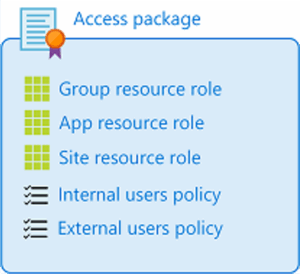
Microsoft Entra Identity Governance introduces the concept of an access package. An access package is a bundle of all the resources with the access a user needs to work on a project or perform their task. Access packages are used to govern access for internal employees, and also users outside the organization. These can be integrated within lifecycle workflows discussed previously to automate entitlement assignments. Here are the types of resources that user’s access can be managed to:
- Membership of Azure AD security groups
- Membership of Microsoft 365 Groups and Teams
- Assignment to Azure AD enterprise applications, including SaaS applications and custom-integrated applications that support federation/single sign-on and/or provisioning
- Membership of SharePoint Online sites
This can also control access to other resources that rely upon Azure AD security groups or Microsoft 365 Groups. With an access package, an administrator or delegated access package manager lists the resources (groups, apps, and sites), and the roles the users need for those resources. Access packages also include one or more policies. A policy defines the rules or guardrails for assignment to access package. Each policy can be used to ensure that only the appropriate users are able to have access assignments, and the access is time-limited and will expire if not renewed.
Figure 4: Microsoft Entra Identity Access Governance Access Package (Source: Microsoft)
An organization can have policies for users to request access, and in these kinds of policies, an administrator or access package manager defines:
- Either the already-existing users (typically employees or already-invited guests), or the partner organizations of external users that are eligible to request access
- The approval process and the users that can approve or deny access
- The duration of a user’s access assignment, once approved, before the assignment expires
There can also be policies for users to be assigned access, either by an administrator or automatically. Access packages are defined in containers called catalogs. An organization can have a single catalog for all their access packages or can designate individuals to create and own their own catalogs. An administrator can add resources to any catalog, but a non-administrator can only add to a catalog the resources that they own. A catalog owner can add other users as catalog co-owners, or as access package managers. In this way, the Entra identity access governance capabilities support delegated administration of access control workflows and approvals.
Access Reviews enable organizations to manage group memberships, access to enterprise applications, and role assignments. User’s access can be reviewed on a regular basis to make sure only the right people have continued access.
Depending on what access rights to review, Entra consolidates and presents a single dashboard that leverages existing utilities such as Access Reviews, Azure AD enterprise apps, PIM, or entitlement management.
Cloud Infrastructure Entitlement Management
Over the past 10+ years, much of enterprise IT has moved to the cloud. In conjunction with this trend TechVision has written about IAM migrating to the cloud, Customer IAM is becoming primarily cloud-based and even Privileged Access Management (PAM) is moving to the cloud. Today, we find ourselves with a largely mixed set of IAM capabilities residing on-premises, in the cloud, or both. Adding to this complexity for many organizations is that they may be using multiple Identity as a Service (IDaaS) offerings, may have multiple on-premises IAM systems and may be leveraging multiple cloud service providers. The many components that comprise an IAM environment, such as authentication, authorization, account lifecycle management and privileged access today can be sliced and diced in such ways that enterprises can select to run in the cloud certain capabilities that run more efficiently, are more cost effective and retain requisite security. TechVision dives into this topic of significantly in recent reports, such as “Architecting and Managing Hybrid and Cloud-based Identity Services”, “Privileged Access Management: More Necessary Than Ever as Cloud-Shift Intensifies” and “Privileged Access Management: Will We Never Learn?”.
A consistent set of well thought out permissions management controls that are aligned to a comprehensive cybersecurity framework is an imperative for nearly every organization, enabling the automation and enforcement of controls over privileged credentials in any system, platform, or environment. Permissions management controls also identify all known exceptions that require special access control and monitoring implementation. This is particularly important considering the large number and dynamic nature of resources many organizations are deploying in the cloud, coinciding with requirements to provide on-going support for multi-cloud environments. Most of these cloud environments (e.g., Azure, AWS, Google) have powerful management consoles and APIs that can expand the available attack surface requiring protection and defense. The challenge many organizations have today is that multiple cloud consoles for managing permissions granularly are redundant, repetitive, disparate and cloud platform specific. While manageable to a degree, there is a dire need for a single administrative console to granularly manage permissions across each of these three major cloud platforms.
Microsoft has been aware of this issue for the past few years. With the acquisition of CloudKnox Security in 2021 and some Entra platform integration, Microsoft now offers a comprehensive Cloud Infrastructure Entitlement Management (CIEM) solution, which they call Entra Permissions Management. This CIEM solution provides visibility into permissions assigned to all identities – users and workloads – actions, and resources across cloud infrastructures and identity providers. Permissions Management is intended to be a proactive solution in that it can detect unused and excessive permissions that are constantly throttled through a least privilege access model across Azure, AWS, and GCP. This is illustrated below.
Figure 5: Microsoft Entra Permissions Management (Source: Microsoft)
Microsoft Entra Permissions Management provides granular cross-cloud visibility to uncover permission risks, enforce least privilege, and continuously monitor and detect anomalies. This allows security administrators to obtain a comprehensive view all actions performed by any identity across AWS, Azure and GCP. This will also allow the system to right-size permissions and enforce the principle of least privilege based on historical usage and activity. It is also able to detect anomalous permission usage using machine learning and AI, and generate detailed forensic reports, which are capabilities sorely needed by security administration and operations. Microsoft Entra Permissions Management allows customers to address three key use cases: discover, remediate, and monitor.
Discover
- Assess permission risks by evaluating the gap between permissions granted and permissions used for any identity (irrespective of the identity type and origin) across any cloud.
- Analyze granular and normalized metrics for all identities across AWS, Azure, and GCP.
- Track permission risks with the Permission Creep Index (PCI), An aggregated metric that continuously evaluates the level of risk based on the number of unused or excessive permissions and resources for all identities. The PCI is a quantitative measure of risk associated with an identity or role determined by unused high-risk permissions and resources. It allows users to instantly evaluate the level of risk associated with the identities and resources.
Remediate
Microsoft claims organizations can right-size permissions based on historical usage, grant new permissions on-demand, and automate just-in-time access for cloud resources.
- Automate deletion of permissions unused for the past 90 days.
- Permissions on-demand: Grant identities permissions on-demand (with self-service workflow) for a time-limited period or an as-needed basis.
Monitor
With Microsoft Entra Permissions Management organizations can detect anomalous activities with machine learning-powered (ML-powered) alerts and generate detailed forensic reports.
- ML-powered anomaly and outlier detections.
- Context-aware forensic reports around identities, actions, and resources to support more rapid investigation and remediation.
Microsoft Entra Permissions Management is a standalone offering generally available worldwide and is integrated within the Microsoft Defender for Cloud dashboard, in order to extend Defender for Cloud’s protection with this newer CIEM approach. This means non-Azure customers can use the solution as well. However, Permissions Management currently doesn’t support hybrid environments, nor does it currently support U.S. Government clouds: only Azure, AWS and GCP at this point.
For any break-glass or one-off scenarios where an identity needs to perform a specific set of actions on a set of specific resources, the identity can request those permissions on-demand for a limited period with a self-service workflow. The user experience is the same for any identity type, identity source (local, enterprise directory, or federated) and cloud.
Additionally, with workload identity management in Microsoft Entra, organizations can assign and secure identities for apps and services hosted in Azure AD, which extends the reach of access control and risk detection capabilities to apps and services – not just user identities. This is an important facet of zero trust that is often overlooked but is gaining more significant traction now.
Microsoft Entra Permissions Management complements Azure PIM. While Azure PIM provides just-in-time access for admin roles in Azure (as well as Microsoft Online Services and apps that use groups), Permissions Management allows multi-cloud discovery, remediation, and monitoring of privileged access across Azure, AWS, and GCP.
Verified ID
TechVision has written four research reports that cover Decentralized Identity and Verifiable Credentials over the past 6 years (and one more in process) – so we’ll describe this model at a high-level here. Decentralized Identity with a verifiable credential ecosystem has the potential to be the foundation for the new Digital Enterprise by supporting the sharing of only the relevant elements of verifiable information necessary to perform specific transactions. It can also support identity authentication, identity proofing and has the potential of moving the industry to a user-centric identity model that has been discussed and explored over the past 30 years.
These new models can be applied to a diverse set of services ranging from logging on to an employer’s network, accessing services from a healthcare provider network or leveraging the on-line services of Amazon, Netflix or other service providers. The goal of Decentralized Identity is to develop mechanisms to easily establish trust, gain explicit consent and easily share relevant information with these services without requiring a 3rd party to control and/or intermediate every transaction. It is effectively the basis for a viable Bring Your Own Identity (BYOI) universe.
This new piece in the modern identity puzzle is called a verifiable credential. This can be thought of as an Identity metasystem that uses credential exchange as the unifying protocol for exchanging Identity data and to verify the claim being made from an authoritative source. A verifiable credential is a qualification, achievement, quality, or piece of information about an entity, such as a name, government ID, payment provider, home address, or university degree. Such a credential describes a quality or qualities, property or properties of an entity that establish its existence, uniqueness and trustworthiness. Entities (people, organizations, devices) need to provide many kinds of credentials as part of their everyday activities.
As we described in our recent reports “The Future of Identity Management 2022-2027”, “Decentralized Identity and Verifiable Credentials”, and “TechVision’s IAM Reference Architecture”, decentralized identity’s transparent model can support Bring Your Own Identity (BYOI) in a more secure, immutable, and non-repudiated identity ecosystem that effectively crosses enterprise and personal identity boundaries.
Microsoft has been a meaningful contributor to the verifiable credential, distributed identity model for several years, albeit mostly in relatively small deployments within organizations. However, with the release of Microsoft Entra Verified ID, Microsoft ups the proverbial ante with a more significant investment in this identity management model. As Ankur Patel, Microsoft’s Head of Product for Verified ID has shared with us, their technical foundation is made up of several innovations, including identifiers that are owned by the user, a user agent to manage keys associated with such identifiers, and encrypted, user-controlled datastores. Microsoft provided the illustration below to represent their Entra Verified ID strategy.
Figure 6: Microsoft Entra Verified ID Model (Source: Microsoft)
This is summarized as follows:
- Portable Credentials exist in the form of W3C Decentralized Identifiers (DIDs). Identifiers that users create, own, and control independently of any organization or government. DIDs are globally unique identifiers linked to Decentralized Public Key Infrastructure (DPKI) metadata composed of JSON documents that contain metadata such as public key material, authentication descriptors, and service endpoints.
- Trust System. To be able to resolve DID documents, DIDs are typically recorded on an underlying network of some kind that represents a Trust System. Microsoft currently supports two trust systems, which are:
- ION (Identity Overlay Network) ION is a Layer 2 open, permissionless network based on the purely deterministic Sidetree protocol, which requires no special tokens, trusted validators, or other consensus mechanisms; the linear progression of Bitcoin’s time chain is what’s required for its operation. Microsoft has open sourced an NPM package to facilitate working with the ION network to integrate into apps and services. Libraries include creating a new DID, generating keys and anchoring the DID on the Bitcoin blockchain.
- DID:Web is a permission-based model that allows trust using a web domain’s existing reputation.
- Microsoft Authenticator App. Enables people to use decentralized identities and Verifiable Credentials. Authenticator creates DIDs, facilitates issuance and presentation requests for verifiable credentials and manages the backup of DID’s seed through an encrypted wallet file.
- Microsoft Resolver. An API that looks up and resolves DIDs using the did:web or the did:ion methods and returns the DID Document Object (DDO). The DDO includes DPKI metadata associated with the DID such as public keys and service endpoints.
- Microsoft Entra Verified ID Service. An issuance and verification service in Azure and a REST API for W3C Verifiable Credentials that are signed with the did:web or the did:ion method. They enable identity owners to generate, present, and verify claims. This forms the basis of trust between users of the systems.
Microsoft Entra Verified ID includes the Request Service REST API to issue and verify credentials. It is also important to note that the organization or system acting as the verifier can use open standards to perform the presentation and verification or configure their own Azure AD tenant to let the Entra Verified ID service perform the work.
TechVision will be monitoring the Verified ID solutioning and deployments very carefully over the next couple of years. TechVision believes, along with Ping Identity, IBM, Microsoft and many others that the future of IAM is intertwined with this emerging BYOI culture that facilitates identity data sovereignty and privacy. The most critical piece of the puzzle appears to be the establishment of a truly heterogeneous, global trust framework. In some ways, this is similar to the emergence of federation using SAML protocols nearly 20 years ago: while it took some time to shake out the interoperability and PKI-centric trust issues, such federation has become a stable pillar of cross-domain, global SSO. We think such an opportunity exists now for decentralized identity.
An industry challenge with Decentralized Identity and Verifiable Credentials is to achieve sufficient critical mass where the “networking effect” kicks in. The industry needs to move from POCs (Proof of Concepts) and testing to production use at scale. As Microsoft moves forward with verified credentials, we see this as a means of improving the quality of information in support of Attribute Based Access Control (ABAC).
Microsoft Entra and the IAM Reference Architecture
There are a lot of capabilities (or, moving pieces!) within the new Microsoft Entra IAM product family! In this section, we will map the Microsoft Entra capabilities with the TechVision Research Reference Architecture for IAM, which is a master template that identifies the IAM capabilities (rather than technologies) that can be improved or enabled, allowing business stakeholders and technical architects to achieve a common language for IAM functions. These functions can then be refined over time, and the purpose of the Reference Architecture is to maintain a “living, breathing” representation of the organization’s IAM strategy. Please note that considerably more information is available in the many TechVision Research documents that encapsulate the Reference Architecture for IAM within discussions about authentication, MFA, PAM, IGA, and Application Development. The overarching TechVision Research document titled “IAM Reference Architecture” is recommended as a good starting point to gather more information.
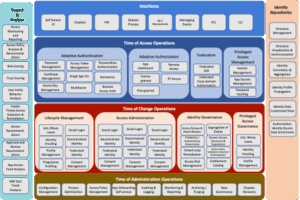
The following high-level template starts the IAM journey:
Figure 7: Top Level IAM Reference Architecture Template
These IAM capabilities are described at the highest level as:
Interact: Interact is a layer of user interaction (UI) and application programming interfaces (API) that simplify end user and application developer interaction with the rest of the IAM infrastructure. In this way, non-experts can follow the best practices of IAM without having to be experts in the field.
This allows the enterprise to:
- Incorporate new security capabilities without having to reengineer applications.
- Increase speed to market by removing security from the critical path of service development.
- Enhance security through the automatic adoption of best of breed security and privacy components.
- Decrease on-boarding friction by isolating complex security infrastructure through intuitive user interfaces.
From the Microsoft Entra perspective, the Interact layer includes the Microsoft Entra admin center, Azure Portal, Console, Microsoft 365 Portal and exposed APIs related to these functions.
Access: Access is the layer that answers the “Who has access to what?” question. It ensures customers can confidently exchange information and get the services they need to buy and use your products. It ensures employees and partners have all the digital resources they need to get the job done, nothing less and nothing more.
This allows the enterprise to:
- Ensure the right people have the right access to the right resources at the right time.
- Protect the assets of the company and its customers.
- Reduce productivity drains and costs caused when people can’t access the resources they need.
Microsoft Entra supports these capabilities through the Entitlement Management, Lifecycle Workflows, provisioning, and Cloud Infrastructure Entitlement Management services, as well as the Authentication, MFA, SSO and Verified ID services.
Change: Change manages the relationships between all the moving parts within the digital environment. Change establishes the connections between people, devices, applications, and data when they enter the environment, manages the connections while the relationship exists, and disconnects when access is no longer necessary.
This allows the enterprise to:
- Establish and maintain the proper rights, entitlements, and restrictions in order to reduce your attack surface, because Users and their identities are the most vulnerable link in a network.
- Orchestrate identity across device, network, and application boundaries because in the absence of the traditional security perimeter, identity is the common denominator across the entire digital environment.
- Prevent toxic combinations through transparency of entitlements across business processes.
Entra supports these capabilities through the Entitlement Management, Lifecycle Workflows, provisioning, and Cloud Infrastructure Entitlement Management services.
Manage: Manage is where the administrators of the IAM platform upgrade, configure, tune, troubleshoot, document, and audit the platform and its components.
This allows the enterprise to:
- Incorporate new security capabilities without having to reengineer applications.
- Increase speed to market by removing security from the critical path of service development.
- Enhance security through the adoption of best of breed security and privacy components.
- Increase agility through isolating security software releases and patches to the underlying infrastructure components.
These capabilities are enabled by the Azure Console, Portal and Cloud Entitlement Management services within Entra.
Measure: Measure is the lens into the digital environment. It allows live behavior observation, anomaly detection, platform health checks, and deeper analysis of usage and threats. It also provides the audit and reporting capabilities necessary to prove you are performing your duty to protect.
This allows the enterprise to:
- Understand behavior to improve the customer experience.
- Detect vulnerabilities before they are crises. The costs of prevention are much less than the costs of a breach.
- Prove compliance as required by law.
These capabilities are also enabled by the Azure Console, Portal and Cloud Entitlement Management services within Entra.
Store: Store is the shared place where the identity profiles, attributes, and relationships are kept and maintained. It may be physically centralized or distributed and contains the map which defines “who has access to what?”, often in the form of an entitlements catalog or database.
This allows the enterprise to support two important groups:
- For customers, it becomes the backbone for the entire customer experience; the customer data layer where all your interactions are captured.
- For employees, it becomes a user-centric view of entitlements across the entire digital environment.
Of course, Azure AD and on-premises AD provide the lion’s share of identity repositories in the Microsoft Entra solution. However, while Azure AD is not an entitlements catalog inherently, Microsoft has instructed us that this capability is in development.
We will now dissect these IAM capability descriptions in more detail below.
Capabilities of the IAM Functional and Technical Landscape
Now, let’s look at the next level of the architecture, which we subtly tailor to identify the functional capabilities that are the foundation for a best-in-class IAM Reference Architecture. Each category is broken up into multiple capabilities at a level of greater detail. For example, interfaces can be for applications / developers (APIs, messaging services), lines of business/LOBs, self-service, or even robotic processes. This applies to each category and, based on stakeholder input, use cases and priorities can be further developed into Reference Architecture patterns or templates for specific services.
Remember, at this level the Reference Architecture is not focused on the actual implementation of things that carry out these controls. Rather it is a model of what the controls are, how they work, and how they interact to assure the utility of content.
It is important to understand that these functional capabilities consider all type of objects and use cases within the IAM foundation. As ultimately implemented, different enterprises enable different IAM capabilities in different ways to meet different protection needs. And they do so differently for different content and business functions because of the different risks and potential consequences associated with failures and costs associated with protection. And they may do so with hybrid solutions that simultaneously run on-premises and in the cloud. One size does not fit all.
The next layer of the TechVision Research Reference Architecture for IAM (see below) allows us to identify the IAM capabilities that are to be supported in the hybrid IAM infrastructure.
Figure 8: IAM Capabilities Within Reference Architecture
With this information, technical architects can rapidly zero-in on the current options (technology and process) their IAM architecture should encompass to achieve the required capabilities for the business. In the form of architecture considerations, each of the options available is then described in more detail to help identify the right approach for an optimal IAM architecture and deployment strategy. In the subsequent section, we’ll look at sample IAM Reference Architecture patterns and map them to some of the key capabilities enabled by Microsoft Entra.
Sample Microsoft Entra Reference Architecture Patterns
Now let’s look at some examples where our customers have deployed various IAM services. We will take a look at Microsoft Entra’s authentication, SSO, runtime access management, IGA and entitlement management capabilities in the context of the Reference Architecture for IAM. Generically, the IAM capabilities are used as input to the development of the Reference Architecture pattern illustrated below:
Figure 9: Typical IAM Service Pattern
It is important to note that much of the overall IAM infrastructure supports or consumes the provisioning and IGA processing output. For example, the “login service” in the upper left corner relies on the IGA policies, birthright access provisioning, workflow and approvals and so on to be able to function appropriately and securely through the “App Dashboard” (PEP, for policy enforcement point) – which interacts during runtime with the access policy repository (PDP, for policy decision point), the enterprise Active Directory/Azure AD and the entitlements catalog.
Now, let’s take a look at this IAM architecture pattern when the enterprise determines that it wants to leverage Microsoft Entra.
Microsoft Entra Pattern Example
Below is an illustration the Microsoft Entra solution functions at a high level:
Figure 10: IAM Reference Architecture Using Microsoft Entra Capabilities
As this modified pattern shows, just about all of the standard, required IAM capabilities as defined by our Reference Architecture are supported across Entra. the administrative and self-service interfaces along with the associated service request/response workflows are supported natively by the Entra platform. Going through this exercise gives us increased confidence that Microsoft is evolving to a much more complete IAM platform that provides a basis for using Microsoft Entra as the primary enterprise IAM foundation.
Summary and Recommendations
Most organizations have a large base of Microsoft Active Directory and Azure AD surrounded by many other Identity, Security, Governance and related technologies. Given the historic limitations of Microsoft’s IAM and related offerings, building capabilities around an AD foundation was a necessity, in particular for large enterprises. The Introduction of Microsoft Entra has the potential to increase Microsoft’s IAM footprint while allowing enterprises to potentially retire 3rdparty solutions.
The bottom line is that Microsoft Entra has significantly elevated and modernized the Microsoft IAM portfolio and those organizations that are currently using some combination of Microsoft and 3rd party IAM solutions may want to take a fresh look at their architecture, service capabilities and patterns. There may be many advantages to adopting Microsoft Entra, in particular for a Microsoft-centric organization. That said, there are often reasons why an organization does not want to “put all their eggs in one basket” and run the risk of vendor lock-in. We normally have been reluctant to push our customers to build out their infrastructure using a single vendor’s solution suite. In fact, we’ve almost as a rule been recommending “best of breed” solutioning to fit the various capabilities of the IAM Reference Architecture with the best of the best. That argument is becoming more difficult in light of the Microsoft Entra strategy.
For example, the cost effectiveness of leveraging an existing enterprise-wide licensing agreement for Microsoft Azure that includes Microsoft 365 and Azure AD must be intelligently understood. There may likely be 3rd party solutions in place across the organization that are effectively no longer necessary. This may bring very significant cost saving to the organization in terms of end user licensing but also terms of integration costs and user experience costs. Such costs should not be taken lightly.
Furthermore, most of our customers are currently reliant on Microsoft Identity Manager (MIM), which is end-of-life in 2029. The replacement for MIM is Microsoft Entra. Even though 2029 is six years away, the time to migrate is sooner rather than later. The migration path from MIM to Microsoft Entra is much more straightforward than to any other 3rdparty identity provisioning and governance solution. Yes, there will be somewhat of a learning curve, but for Microsoft shops, this is nothing extraordinary. Product evolution should be expected, and the enormous transformation from on-premises IT to in-cloud IT in general, spurs such evolution. And, Microsoft is not tone deaf regarding the need for robust MIM migration tooling, as they have demonstrated that Entra is tuned specifically to aid this migration.
The investment into decentralized identity in the form of Microsoft Entra Verified ID is also reason for optimism. While TechVision has been reasonably bullish on the eventual emergence of a global, heterogeneous, and ubiquitous trust fabric to enable privacy enhanced BYOI, it takes “big vendors” like Microsoft, IBM and others to establish the foundation.
In summary, our first in-depth look at Microsoft Entra shows that there is a good reason for enterprise identity and security groups to increase the Microsoft capabilities that are ideally already at their disposal. This tectonic plate shift may need to take a “crawl, walk, run” strategy in order to bring measurable improvements on a regular cadence. Taking small but increasingly larger steps down the Microsoft Entra path to IAM enlightenment may benefit many organizations that are already heavily invested in Microsoft products and solutions.
At a minimum, organizations should understand that the Microsoft Entra direction is changing the IAM landscape and it may be a good time to assess requirements, evaluate your current state, assess gaps and architect your next generation solution. TechVision generally recommends a structured approach to such a critical infrastructure element like IAM and has developed a reference architecture that may be useful in evaluating the set of capabilities necessary for your future state IAM foundation. TechVision can help with this process.
About TechVision
World-class research requires world-class consulting analysts, and our team is just that. Gaining value from research also means having access to research. All TechVision Research licenses are enterprise licenses; this means everyone that needs access to content can have access to content. We know major technology initiatives involve many different skillsets across an organization and limiting content to a few can compromise the effectiveness of the team and the success of the initiative. Our research leverages our team’s in-depth knowledge as well as their real-world consulting experience. We combine great analyst skills with real world client experiences to provide a deep and balanced perspective.
TechVision Consulting builds off our research with specific projects to help organizations better understand, architect, select, build, and deploy infrastructure technologies. Our well-rounded experience and strong analytical skills help us separate the “hype” from the reality. This provides organizations with a deeper understanding of the full scope of vendor capabilities, product life cycles, and a basis for making more informed decisions. We also support vendors in areas such as product and strategy reviews and assessments, requirement analysis, target market assessment, technology trend analysis, go-to-market plan assessment, and gap analysis.
TechVision Updates will provide regular updates on the latest developments with respect to the issues addressed in this report.
About the Authors
 Doug Simmons brings more than 25 years of experience in IT security, risk management and identity and access management (IAM). He focuses on IT security, risk management and IAM. Doug holds a double major in Computer Science and Business Administration.
Doug Simmons brings more than 25 years of experience in IT security, risk management and identity and access management (IAM). He focuses on IT security, risk management and IAM. Doug holds a double major in Computer Science and Business Administration.
While leading consulting at Burton Group for 10 years and security, and leading global identity management/security consulting at Gartner for 5 years, Doug has performed hundreds of engagements for large enterprise clients in multiple vertical industries including financial services, health care, higher education, federal and state government, manufacturing, aerospace, energy, utilities and critical infrastructure.
 Gary Rowe is a seasoned technology analyst, consultant, advisor, executive and entrepreneur. Mr. Rowe helped architect, build and sell two companies and has been on the forefront the standardization and business application of core infrastructure technologies over the past 35 years. Core areas of focus include:
Gary Rowe is a seasoned technology analyst, consultant, advisor, executive and entrepreneur. Mr. Rowe helped architect, build and sell two companies and has been on the forefront the standardization and business application of core infrastructure technologies over the past 35 years. Core areas of focus include:
Identity and Access Management, business/technology trends, cloud computing, security/risk management, privacy, innovation, AI, new IT/business models and organizational strategies.
Prior to starting TechVision Research he was President of Burton Group from 1999 to 2010, the leading technologyinfrastructure research and consulting firm. Mr. Rowe grew Burton to over $30+ million in revenue on a self-funded basis, sold Burton to Gartner in 2010 and supported the acquisition as Burton President (now Gartner for Technical Professionals) at Gartner.