Digital Trust
Publication Date: June 6, 2020
Abstract
Trust is a cornerstone of the digital economy and is what makes efficient markets possible. Without trust, few transactions would take place. While mutual benefit is often the reason behind a transaction, trust is the insurance or likelihood that the purchaser will receive that benefit. Consumers will not buy from a seller if they do not trust the seller to deliver the product as agreed. Businesses will not trade if they do not trust the other party to follow through with its promises. Clients may refuse to do business if they don’t trust the security and privacy practices of the vendor. Lack of trust can lead to costly legal protections, inefficient contracts, lost sales, and business failure.
Trust is a human construct that is based on the perception that another person or organization will deliver on a promise to do something. In the days of brick and mortar, people (salespeople, support staff, managers, etc.) provided the basis for trust. Now businesses are becoming digital, and that means there are fewer human touchpoints and interactions with customers. That drives the need for the digital platforms that demonstrate and reinforce this perception of trust; that you act honestly and upright (Integrity), are capable and competent within your fields (Competence), balance your own interests with the interest of others (Benevolence), and act with consistency (Predictability).
In a world where almost any product or service can be purchased online from countless companies globally, trust is a significant differentiator. This report defines trust for the digital world and how an enterprise can deliver on the explicit and implicit promises made with your customers and prospects. Note that trust builds or is eroded over time. We break down the dimensions of Digital Trust into two areas:
- Mechanical trust, in particular as it relates to and is supported by cybersecurity and Identity and Access Management is at the heart of Digital Trust. This is the technical foundation means that deliver predefined outputs reliably and predictably.
- Relational trust, the promise to abide by the social norms and agreements that address the complex realities of the relationship between the customer and the Digital Enterprise.
Authors:
| Gary Zimmerman
Principal Consulting Analyst |
Gary Rowe
CEO, Principal Consulting Analyst |
Executive Summary
The purpose of this report is to influence the way your organization approaches trust as your organization becomes a Digital Enterprise. The traditional approaches of creating a reputation for trustworthiness through branding, advertising, and physical presence are shifting to the trustworthiness customers perceive as they experience millions of digital interactions across their entire customer journey with you and others. Establishing and maintaining Digital Trust is an increasingly critical part of how enterprises do business.
Why is Digital Trust important? Well, the numbers tell the story.
- 83% of people trust brand recommendations from friends, and nearly 70% trust consumer opinions more than paid advertisements.
- 87% of shoppers now begin their hunt for products and services in digital channels.
- 81% say trust impacts their purchasing decisions.
And yet,
- 61% believe digital companies put profits ahead of the welfare of customers.
- 41% say they don’t trust brands’ marketing communications to be accurate or truthful.
- 45% of consumers would never trust a brand again after it displays unethical behavior or is involved in a scandal, and 40% say they’d stop buying from that brand altogether.
And all of these statistics are based on the fact that customers have shifted to predominantly interacting with companies digitally and are becoming increasingly uneasy in those interactions for the following reasons:
- Brands have ever-increasing amounts of customers’ personal information in their databases.
- There is increasing sophistication with which brands can target or track customers.
- There is increasing reliance of brands to add to their intelligence using advanced automation and artificial intelligence in their interactions with customers.
In order to build and maintain “digital” trust, enterprises need to shift their efforts in identity, security, and compliance from merely providing an enterprise “protection” activity to a more inclusive customer engagement activity and strategy.
In simple terms, digital trust can be defined as the confidence people have in an organization’s ability to keep their digital data secure and to handle it with integrity and accountability. Digital trust is seen as critical to the long-term success of enterprises in a connected world.
Digital trust is built on two main components: mechanical trust and relational trust.
- Mechanical trust, especially as it relates to cybersecurity, is the technical heart of digital trust. It is the means, mechanisms and controls to deliver predefined outputs reliably and predictably.
- Relational trust is the promise to abide by the social norms and agreements that address the complex realities of the evolving relationship between the customer and the digital enterprise.
To build and maintain trust, businesses need to make sure they are delivering on both mechanical and relational trust. Without the balance, customers will not share the data required to drive the proper customer experience. And if your customer experience is lacking it won’t be long before customers are seeking alternatives. This is particularly important as organizations transform to Digital Enterprises; if our digital interactions can’t be trusted, this will profoundly impact our customer’s engagement and, ultimately, our bottom line.
For mechanical trust, organizations should directly address the challenges and opportunities in IAM and security including new approaches such as Customer IAM, Decentralized Identity, Zero Trust Security and advanced authentication/authorization approaches. And look to the emerging trends that are shifting the “duty to protect” beyond the company borders.
For relational trust, refine privacy policies to reflect a more transparent and peer-like relationship between the business and its customers; and then make sure to deliver on the promises those policies represent. It is important to also provide assurance to your customers that your use of AI/ML capabilities leveraging “big data” are designed to make their experiences better and are being implemented in an ethical manner.
Companies that keep their promises and operate transparently enjoy more trust and should, as a result find that their customers are MORE likely to share their positive experiences and spread a good word through social media. Besides, dealing with customer complaints professionally via social can positively impact consumers’ trust, too. While some businesses consider it’s safer to keep sanitizing content and taking negative consumer conversations offline, those who manage to resolve it positively in public reap even bigger reward in terms of customer trust. Remember that customers don’t expect you to be faultless. However, the way you fix things when they go wrong proves what your business is worth and if they can trust you.
What Is Trust?
In simple terms, trust is a state in which on party believes in the reliability, truth or ability of the second party to perform a given task or meet an objective. That “party” could be a person, organization, process or even a “thing”. When you trust another party to deliver on a promise to do something, you put yourself in a vulnerable and risky situation that the other party won’t meet their end of the bargain. If the other party betrays us on a confirmed deal, this creates a zero-sum situation where they win this time, but you’ll never strike a bargain with them again. On the other hand, if our trust in is upheld, it creates a powerful incentive to engage them with them further in the future. This is why economists recognize that trust makes our trading world go around. Acting in a trustworthy manner, towards friends and strangers alike when it comes to exchanging goods and services, both extends and deepens meaningful, productive economic coordination. This is often called, in aggregate, a reputation. A good reputation means that the level of trust increases, and a bad reputation has the opposite impact.
When we think of trust and what it means, we quickly realize it encompasses many things. In the natural world, we use the word “trust” to:
- Interpret what people say
- Describe behaviors
- Decide if we feel comfortable sharing data
- Indicate whether we feel other people have our interests at heart
In a given situation, all of us can quickly measure our trust in someone using our experience and basic senses. But in the digital world our senses cannot play the same role. We are removed from the situation and the other person by electrons, time, and distance. And it’s becoming more complex. What’s on the other end of the Internet isn’t a person; it’s a server, a smart device, or a digital endpoint that represents a person or organization within the context of the situation.
The Importance of Trust in the Digital Economy
Trust is a cornerstone of the digital economy, and a lubricant that makes efficient markets possible. Without trust, few transactions would take place. While mutual benefit is often the reason behind a transaction, trust is the insurance or likelihood that the purchaser will receive that benefit. Consumers will not buy from a seller if they do not trust the seller to deliver the product as agreed. Businesses will not trade if they do not trust the other party to follow through with its promises. Clients also may refuse to do business if they do not trust the security and privacy practices of the vendor. Lack of trust can lead to costly legal protections, inefficient contracts, lost sales, and business failure.
The Trust Project at Northwestern University, an initiative designed to advance the study and management of trust in business and society, shares decades of research about this complex concept and resolves it into the four key components: competence, benevolence, integrity, and predictability.
Competence – Competence in business covers technical and operational matters that correspond to the product features or service quality itself, as well as the way you manage the operations within your company. In other words, competence is related to abilities, commitments, knowledge, and hard skills your staff demonstrates towards customers.
Poor usability / visual design and lack of ownership are among major drivers of distrust in digital experiences. At the same time, a demonstrated commitment to excellence and innovation makes a real difference for prospective customers and often positively influences their purchasing decisions.
Benevolence – Benevolence is more closely related to the impressions customers get as they deal with the staff and, more specifically, soft skills your employees demonstrate as they interact with customers. At this stage, an emotional connection with a brand emerges and starts developing, and the result of it largely comes down to whether customers believe the company has their best interests at heart and cares about them as a customer.
The success of maintaining customer trust within this dimension also depends on your ability to trust customers in return, make them feel their opinion matters and show your gratitude for doing business with you. It’s also important to keep in mind that given there’s enough trust on the part of the customer at this stage, you’ll have a chance of hearing their concerns if any. Otherwise, if you fail to create a meaningful connection, you won’t even know why they decided to leave and what exactly went wrong.
Integrity – Integrity corresponds to the ethics and values that shape and guide the company. It largely refers to company’s honesty and ability to keep its promises, but also owes to the shared values that underlie more meaningful and purposeful connection with a customer.
It’s in our human nature to feel good about ourselves when we do business with a company that shares our own values and, for instance, makes an effort to go green and take care of the environment, or supports a social initiative aimed to make this world a better and safer place. This kind of connection creates joy and lets us enjoy a positive association with the brand, and consequently results in more trust and long-lasting loyalty.
Predictability – Predictability includes brand reputation and customer expectations toward a brand based on information they gathered and learned. According to a scientific research, certainty builds optimistic outlook and inspires more positive impressions.
Companies that keep their promises and operate transparently enjoy more trust as their customers are more likely to share their positive experiences and spread a good word through social media. Besides, dealing with customer complaints professionally via social can positively impact consumers’ trust, too. While some businesses consider it’s safer to keep sanitizing content and taking negative consumer conversations offline, those who manage to resolve it positively in public reap even bigger reward in terms of customer trust. No surprise, customers don’t expect you to be faultless. However, the way you fix things when they go wrong proves what your business is worth and if they can trust you
The Cost of Trust
There are many ways to think about the “cost of trust,” but generally speaking we can say that stakeholders are busy creating economic roles, developing organizations and building wholesale institutions to signal that they are trustworthy participants in the economy. The cost of trust potentially amounts to an enormous slice of aggregate economic value; in some studies, as much as 35% of the US workforce is focused on building and maintaining economic trust. Think about that and how your organization is protecting this economic trust.
In breaking down the components related to the cost of trust, it could be helpful to consider the impact of mistrust, and both its direct and induced cost to the overall economy where it takes place. From that standpoint, mistrust has been linked to a demand of restrictive regulations and costly control systems, but that is only the starting point.
Stephen M.R. Covey says, “Trust always affects two measurable outcomes: speed and cost.” When trust goes down—in a relationship, on a team, in a company, in an industry, with a customer—speed decreases with it. This results in redundancy in processes, everyone checking up on everyone else, cost more. Where trust is low, everything takes longer and costs more.”
Customer trust has eroded over the past few years on several fronts. The more that consumers learn about how their data is gathered, used, sold, and compromised, the less they trust organizations to use it only to create better experiences or offer more relevant products. Earning and keeping customer trust has never been as important or as difficult. Furthermore, individuals and the media are closely watching this dynamic.
With trust in such a precarious and fragile state, it takes an instant to gain or lose a customer. And it could be for anything, any indicator that your company is not worth trusting if the risks seem to outweigh the benefits of doing business with you. And maintaining trust is important whether you serve consumers or other businesses.
While most of this report is focused on consumer trust, it doesn’t mean that B2B companies are immune to trust issues. A key difference between B2C and B2B is that in B2C, individual consumers simply vote with their feet if things go wrong. In B2B, the customer is likely to complain to the department that fails to meet expectations or to the account manager. Another difference is the scale; a large organization may have hundreds or thousands of business-to- business connections, but millions or hundreds of millions of customers and prospective customers. If communication/action is rapid and efficient, the level of customer loyalty can actually improve; if it remains unacceptable then the customer will start to shop around for alternative propositions.
Regulatory Compliance
Businesses are comfortable with something called rules-based or deterrence-based trust because they can understand and quantify punitive measures and they can clearly see and measure boundaries and constraints. Their risk-assessment mechanisms are tuned to calculating the trade-offs to assure them that they are covered. Nowhere is that more apparent than in the world of regulatory compliance.
With corporate scandals (Enron, Worldcom, et al.) our trust in public markets went down because we realized there are some people out there “cooking the books.” Congress stepped in and passed Sarbanes-Oxley (Accounting Reform Act). Sarbanes-Oxley doesn’t generate trust itself; it’s a series of rules, regulations and compliance measures intended to help assure trust and protect those depending on this trust. It has helped in that markets didn’t collapse under extreme conditions, as they perhaps could have. But it came at a price. Sarbanes-Oxley takes a whole lot of time and costs an average of about $1 million annually to implement. And that’s just one example.
Thomson Reuters Regulatory Intelligence (TRRI) in 2019 captured 56,624 regulatory alerts from more than 1,000 regulatory bodies, averaging 217 updates a day. Regulatory change was reported as the top compliance challenge for 2020 with respondents anticipating that more information will be published by the regulator. The Covid-19 pandemic and Brexit will bring new challenges and regulations. Once again, speed goes down, cost goes up.
When we discuss compliance costs, we are really making the distinction between two types of costs:
- The cost of compliance, which is the amount that firms spend to manage their compliance programs, and
- The cost of non-compliance, which is the consequence of failure to comply (and which is not always monetary).
The Cost of Regulatory Compliance
The estimate for US regulatory compliance and economic effects of federal intervention is $1.9 trillion annually[1]. If the cost of federal regulations were a country, it would be the 9th largest, behind India and just ahead of Canada. And businesses in the U.S. on average spent $10,000[2] per employee on regulatory costs. While these costs are staggering, many regulations are focused on general business practices and are beyond the scope of IT. For this report, we’ll focus on the ones most germane to IT, data protection compliance regulations.
- The average annual data protection compliance cost for organizations across all industries worldwide is $5.47 million[3]
- The financial services industry has some of the highest data protection compliance costs, with the average cost of compliance equaling $30.9 million[4]
- Companies spend the most on specialized technology, with incident response and audits and assessments coming in second and third[5]
- GDPR is considered the most difficult framework to for businesses to achieve compliance[6]
- Most companies conduct one or more compliance audits each year[7]
It pays to invest in compliance: if companies spend more on compliance activities, such as audits, enabling technologies, training and expert staffing, it would generally be less costly (at least in the long-run) than if they were in non-compliance with data protection regulations and were caught.
According to a benchmark study conducted by Ponemon Institute, the significant costs associated with data protection compliance fall into the following categories.
Figure 1 – The costs of compliance
It’s interesting to note that 65% of compliance costs are directly (or indirectly) related to enabling security technologies, which shows that organizations are increasing expenditures across the board on technology infrastructure.
The Cost of Non-Compliance
While compliance with regulations like Payment Card Industry Data Security Standard (PCI DSS), Health Insurance Portability and Accountability Act (HIPAA), and General Data Protection Regulation (GDPR) come with hefty price tags, the alternative is far more costly. In fact, this recent report[8] finds that the cost of an incidence of non-compliance is 2.71 times higher than the cost of compliance.
- Non-compliance costs businesses on average $4,005,116 in revenue losses
- Spending on incident response has doubled since 2011
- Incident response costs businesses an average of $1 million
- Business disruption is the costliest consequence of non-compliance, with businesses losing $5,107,206 on average
- Fines and penalties are the least costly consequences of a data breach
Failure to comply presents a range of consequences that include both monetary and non-monetary costs. Fines — while the most obvious and public — actually represent the smallest cost when compared to the business disruption, revenue losses, and productivity losses. (See figure 2)
Figure 2 – The costs of non-compliance
While businesses often focus on the tangible, non-compliance costs, the most damage can often occur with the following types of non-monetary costs:
- Reputation damage: Because enforcement actions are generally made public, failure to comply can result in serious reputation damage, negatively spotlighting your firm to both customers and competitors. This concern looms large as media scrutiny continues to grow. If extreme, reputation damage can destroy a company.
- Personal liability: Regulatory bodies are increasingly targeting individuals, including compliance executives and CEOs. These liabilities are far-reaching, and laws (like the Park doctrine) can result in civil fines and even jail time. In 2018, the NFA’s work with the FBI, USPS, and CFTC led to significant prison sentences for nearly 30 individuals, including sentences of more than 20 years.
An important takeaway is that the costs of non-compliance are 2.71 times the costs of compliance — meaning it’s far more cost effective in the long run to invest in a strong data protection compliance program. And data protection is key to digital trust.
Customer Experience (CX) Drives Trust
The “cost of persuasion”, i.e. investments made in branding, advertisers, psychologists, marketing researchers, influencers, celebrities, telemarketers, website designers and data analysts are the business investments in building knowledge-based trust in the customer before the sale.
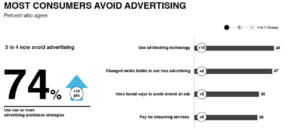
Today, digital advertising, currently running at about $130 billion annually, makes up a majority of the advertising budget of businesses. However, about 14% of that investment is wasted due to fraud. And calling into question the rest of that spend, 41 percent of consumers say they don’t trust brands’ marketing communications to be accurate and truthful. Nearly three-fourths of consumers also reported that they try to avoid advertising altogether.
Figure3 – Most Consumers Avoid Advertising: Edelman Trust Barometer
Because of significant fraud and the adoption of ad blocking, marketers are forced into driving additional investments into search platforms and social networks, where the platforms control the attention, not the brands.
While persuasion is still important to drive revenue, business have realized what’s more important is the experience across the entire customer journey. Customer experience is your customers’ perception of how your company treats them. These perceptions affect their behaviors and build memories and feelings to drive their loyalty.
Figure 4 – Touchpoints across the customer experience
Customers, not branding efforts, drive today’s business’ reputation and customers gauge trust based on what the business does at all of the journey’s touchpoints, not what it says.
Brands with a good online reputation are trusted more because people depend on the opinions of others. If people appear to trust a company or person, others are likely to follow suit with the same sentiment. If you can’t even get people to trust your brand, you’re going to have a difficult time selling your products. In fact, research shows that 83% of people trust brand recommendations from friends, and nearly 70% trust consumer opinions more than paid advertisements[9]. In other words, if they like you and continue to like you, they are going to do business with you for a long time and recommend you to others.
But, in order for your customers to like you, you need to get to know them, and then use this knowledge to deliver personalized experiences across their entire customer journey. But gaining this in-depth knowledge about customers isn’t something that just happens. You need to collect customer data and bring out valuable insights from that data with speed and precision.
As the Digital Enterprise gains momentum, given the increasing dependency businesses have on data, the consequences of consumer trust breaches will become more severe. IDC predicts that the amount of consumer data subject to “big data” analysis will surge by a factor of 50 by 2025, generating more than 5.2 trillion gigabytes of consumer data.
So, a big challenge for the Digital Enterprise is learning that the best-quality customer relationships and best-quality data come from people who are willing to give you their data, willing to watch the messages you send them, willing ultimately to engage with you because they have agreed to this particular thing and believe sharing their data with you is a win for them. This is what creates more value.
However, the bigger challenge is to use data to provide value to customers in a way that is inherently responsible, and also prevents you from becoming vulnerable to data breaches and even the kinds of scandals that have dogged certain tech companies recently.
The decay of consumer trust is a serious problem. Big data, generated by consumers, fuels the development of many new products and continued revenue growth. Should consumers choose to withhold their data — a likely result of large-scale data breaches such as the Experian episode, or unethical use shown in the Facebook/Cambridge Analytica data scandal — the growth of the new business will be impeded.
What is Digital Trust?
To understand digital trust, you should understand what’s driving the need for digital trust. Customers are becoming increasingly uneasy about trusting organizations for these reasons:
- The ever-increasing number of brands that have customers’ personal information in their databases.
- The increasing sophistication with which brands can target or track customers.
- The increasing reliance of brands on automation and artificial intelligence in their interactions with customers.
- Media focus and attention on the misuse of customer data
In simple terms, digital trust can be defined as the confidence people have in an organization’s ability to keep their digital data secure and to handle it with integrity and accountability. Digital Trust is seen as critical to the long-term success of enterprises in a connected world.
Digital Trust is built on two main components: mechanical trust and relational trust and we’ll now summarize each component.
Mechanical Trust
Mechanical trust, especially as it relates to cybersecurity, is the technology infrastructure needed to support Digital Trust. It is the means and mechanisms that deliver predefined outputs reliably and predictably. An automobile’s braking system provides a good metaphor. Step on the brakes. The car stops. No ambiguity, no uncertainty. Predictable, reliable outputs are expected to be delivered every time. If a system is secure and performs predictably, individuals will be more willing to use it. They’ll be able to trust it.
Cybersecurity is based on the assumption that if you make the effort to get an asset more expensive than the asset is worth, you have performed your “duty to protect”. Security is all about risk mitigation and threat deterrence—not complete protection. TechVision has provided a lot of published research in Cybersecurity and Identity and Access Management and, in this report, we’ll focus on those areas that are most relevant to Digital Trust. For example, in our report, “Evolving Against Vulnerabilities, Breaches, and The Next Cyber Attack” we describe the modern approach using the NIST security framework to defend against cyber-attacks and threats.
The specific problem with any security model is that the proof of security relies on assumptions. Specifically, the assumptions are that the implementation of any secure network, system, or application is consistent with that model, and that the system is installed, operated, maintained, and decommissioned consistently with that model. If it is not, the underlying assumptions are wrong. The proof may be correct, but it is irrelevant.
At the core of mechanical trust are decisions about which information risks to accept and how to mitigate them. Traditionally, CISOs and their business partners have made cyber-risk management decisions using a combination of experience, intuition, judgment, and qualitative analysis.
Digital transformation and the distribution of the workforce not only scatters resources and assets but continues to drive a divide between corporate confidence and actual ability to protect their interests in a transformed workplace and economy. The sheer number of assets and processes to protect, and the decreasing practicality and efficacy of one-size-fits-all protections, have dramatically reduced the applicability of traditional security operations and decision-making processes. These new elements and the speed by with changes occur in the Digital Enterprise impact both Security and Identity and Access Management. Getting these foundations right are key to Mechanical Trust and to establishing and maintaining overall Digital Trust.
So it isn’t just the Cybersecurity framework that is critical in supporting mechanical trust; it is the Identity and Access Management infrastructure as well. As we highlight in our report, “Identity as the New Perimeter”, Digital Enterprises can no longer be content with managing trust behind a firewall perimeter. The perimeter now must accommodate all of those external to the business itself. Enterprises need assurance not just about the identities of their own workers and contractors, but also those of their partners, customers, and a variety of “things” beyond the control of the business. This is changing the way a business needs to approach Identity and Access Management (IAM).
Even before addressing Digital Trust in this report, we believe there is a compelling case for most enterprises to upgrade and modernize their IAM foundation. This is based on expensive, hard to manage and fragmented nature of most IAM infrastructures at large organizations. This fragmentation is problematic from security, privacy and compliance perspectives and this becomes even more acute as organizations become Digital Enterprises. We’ll now look at a few key technologies that are critical in having the right Mechanical Trust foundation that enterprise must have going forward.
We’ll start with the authentication methods, ensuring that there is a binding between the purported identity and the real identity such as Multi-Factor Authentication and Risk-Based Authentication. We’ll then examine other areas such as authorization and new approaches such as Decentralized Identity.
MFA
As we outlined in our report, “Multi-Factor Authentication (MFA): Enterprise Strategy and Market Assessment”, cyber threats are becoming increasingly sophisticated and include a variety of techniques that involve guessed, hacked, or physically or virtually stolen credentials. These threats expose the inherent weakness within traditional username/password-based authentication schemes. Two-factor or multi-factor authentication (2FA or MFA) is an extra authentication method that’s becoming increasingly common to compensate for the weakness in user ID / Password authentication. The use of MFA and advanced authentication is critical to knowing your customer and to supporting Digital Trust.
Risk-Based Authentication
Risk-based authentication, or adaptive authentication, takes MFA a step further. It is an authentication paradigm that attempts to match the required authentication credentials to the perceived risk of the connection or authorizations requested. The objective is to try to reduce the authentication burden on users and provide a better experience on the one hand, while enforcing strong authentication where it is most needed on the other. This is another key element of a platform that supports strong Digital Trust.
All of these authorization approaches work to lessen the risks of a compromised digital identity, but they need to be augmented with more sophisticated access strategies in order to properly manage risk.
Authorization and Mitigating Risk
Once a user is authenticated (you know who they are) the next challenge is determining what they can access. From a security and Digital Trust perspective it is important to protect the most critical assets. The next type of protection called Privileged Access Management (PAM) tightly controls the administrators and super-users that can do the most damage if compromised. We’ll then look at role-based and attribute-based access control as scalable, more generalized methods of allowing the right people to access the right resources at the right time while mitigating risk. These technologies are intended to both scale to Internet levels and provide granular access control; both critical to establishing Digital Trust at scale.
PAM
As we outline in our report, “Privileged Access Management: More Necessary Than Ever as Cloud-Shift Intensifies”, Privileged access management (PAM) consists of the cybersecurity strategies and technologies for exerting control over the elevated (“privileged”) access and permissions for users, accounts, processes, and systems across an IT environment. By dialing in the appropriate level of privileged access controls, PAM helps organizations condense their organization’s attack surface, and prevent, or at least mitigate, the damage arising from external attacks as well as from insider malfeasance or negligence.
While privilege management encompasses many strategies, a central goal is the enforcement of least privilege, defined as the restriction of access rights and permissions for users, accounts, applications, systems, devices (such as IoT) and computing processes to the absolute minimum necessary to perform routine, authorized activities. Best practice is to implement PAM as a means to limit the damage an intruder can create.
Role-Based Access Control/Attribute-Based Access Control
For more general access, Role-Based Access Control (RBAC) and Attribute-Based Access Control (ABAC) are two ways of controlling the authentication process and authorizing users. The primary difference between RBAC and ABAC is that RBAC provides access to resources or information based on user roles, while ABAC provides access rights based on user, environment, or resource attributes. Essentially, when considering RBAC vs. ABAC, RBAC controls broad access across an organization, while ABAC takes a fine-grain approach.
An organization might use RBAC to provide a baseline form of fine-grained access management that is easier to maintain because the policies don’t need to be changed every time a person leaves the organization or changes jobs: they can simply be removed from the role group or allocated to a new role. This also means new employees can be granted access relatively quickly, depending on the project or organizational role they fulfill.
Attribute-based access control draws on a set of characteristics called “attributes.” This includes user attributes, environmental attributes, and resource attributes.
- User attributes include things like the user’s name, role, organization, ID, and security clearance.
- Environmental attributes include the time of access, location of the data, and current organizational threat levels.
- Resource attributes include things like creation date, resource owner, file name, and data sensitivity.
Essentially, ABAC has a much greater number of possible control variables than RBAC. ABAC is implemented to reduce risks due to unauthorized access, as it can control security and access on a more fine-grained basis. Both services are critical in supporting the foundation for Digital Trust.
External identity Management
As business has become more digital and disbursed, the networks and infrastructure that supports it is no longer under the sole control of the enterprise. Businesses now have to securely interact with assets (people, data, applications, organizations, infrastructure) in a different way than they do with employees and controlled digital assets. An example of this is the supplier value chain.
The Supplier Value Chain
Digital enterprise technology investments are driving the supply chain evolution from linear, responsive-driven flows to interconnected and predictive smart networks enabling organizations to put the customer at the core of how products and services are designed and delivered, to meet unique customer value propositions. Several technologies are playing key roles in the digital supplier value chain, among them are cloud, big data, the internet of things (IoT), machine learning, “what-if” scenario planning, and social networks.
While these new supply chain technologies bring many benefits, organizations must diligently manage the full range of supply chain risk. Key issues include:
- Trust is regularly handed over to third party providers; unfortunately for many, without proper due diligence, risk assessment or examination of controls.
- Customer expectations of companies that form part of their supply chain are rising – particularly if a company wants to provide services like mass customization where the individual customer’s requirements are built into the product as it is being delivered. Sharing customer information is vital to customization, but third-party mismanagement of that information will damage the relationship and ultimately end in lost opportunity.
The first step in managing these risks is through managing who has access to the data that can impact trust.
Federated identity management allows organizations to securely exchange information with partners and is the key to managing access across the business value chain. Federated access management solutions allow authentication of users in the domain where their identities are stored, thus ensuring that each company in the partner network is responsible for managing its own identities and potentially limiting your liability.
Combined with single sign-on, federation provides access management for any type of application, including mobile, and centralizes access control for all types of clients, such as Web browsers, native mobile applications and server-to-server interactions. Using standards-based federated identity is a current best practice in supply chain identity management.
While you’ll still need to manage a robust set of authorization capabilities, the need to manage external authentication can be shifted to the suppliers, the ones that know the individual entities best.
The Customer Value Chain
The idea behind the customer value chain is when customers have to procure products and services, they go through a series of steps in order to achieve this goal.” If you want to buy a refrigerator, you have to go to visit a store, evaluate the options, compare all of the prices the features, choose a refrigerator, pay for it, receive it, use it, and a few years later, dispose it. All of these are activities in the customer value chain. All of these activities; across anything an individual buys, a company buys, or the government buys as a customer can be classified within this customer value chain.
In their relationships with Digital Enterprises, customers are now obligated to trust how organizations use data and algorithms during each step in the customer value chain. Helping to connect the business to external entities is Customer Identity and Access Management (CIAM). TechVision has written several reports on CIAM (with an update in 2020 planned) and this emerging identity category is the foundation for how individuals are identified, profiled and provisioned. It can also be a conduit for the collection of and organization of customer data. CIAM systems also often link to CRM systems and marketing systems.
Customer Identity and Access Management (CIAM)
CIAM was originally developed to enable organizations to securely capture and manage customer identity and profile data, and control customer access to applications and services. It has rapidly evolved into something much more, connecting with external endpoints, (customers, things, partners) to deliver:
- Personalized customer experiences and deliver omnichannel experiences
- The ability to secure and connect billions of customers’ and IoT identities and data
- Authentication and authorization for billions of logins and transactions daily
- Facilitation of data collection, security, analytics, privacy, and control
- Support for and adherence to regulations (GDPR, HIPPA Open Banking, PSD2, CCPA), such as privacy, consent, and erasure
- Integration with other systems, such as marketing automation systems
- Scale to meet demands and requirements
- Identification and protection against fraudulent or malicious activities
With a properly implemented CIAM platform, customers’ personal data and information is no longer siloed in different business units, but transparent across all lines of business — creating a single user profile company-wide. This allows each business unit to respond more quickly, consistently, and collaboratively as needs, trends, and regulations change.
CIAM platforms help organizations grow opportunities and revenue by allowing them to rapidly identity-enable new cloud, mobile, and IoT services in order to offer a richer, seamless customer experience across applications, devices, and internet-connected “things”. Additionally, advanced platforms use real-time context to feed into a single overview of the user in order to offer personalized services based on habits.
Importantly, in addition to growing revenue, CIAM platforms also help to build digital trust and customer loyalty by enabling increased user-driven privacy, consent, and control over personal data, as well as supporting regulations. Consent management and GDPR/CCPA compliance is a key aspect of CIAM and also important building Digital Trust with customers. CIAM services and regulatory controls are requiring more specific consent (not just the data being offered up, the specific use of that data) and capabilities such as the “right to be forgotten”. The advent of IoT is causing additional CIAM and privacy challenges as described next.
The Dilemma of Smart Things – Before digital transformation, the company’s responsibilities basically ended with the sale. With the advent of smart devices, assumptions about who owns a product are being challenged in a world entering a state of “forever beta.” As enterprises seek to introduce a new generation of products driven by digital experiences, addressing this new reality will be critical to success. Nearly three-quarters (74%) of executives report that their organization’s connected products and services will have more, or significantly more, updates over the next three years. That requires businesses to document and maintain relationships between “identities” to address the complexities and manage the risks of “forever beta” products.
Implementing a CIAM strategy is key to driving differentiation in the marketplace through better customer experience. We’ll now look at how security should support Digital Trust.
Shifts in Security in Support of Digital Trust
Analysts look for entropy, a lack of order or predictability, in a mechanical trust world of rules and assumptions. Specifically, the rules are encoded in governance and operational procedures and reflected in the code of various security solutions. The assumptions are that the implementation of any secure network, system, or application is consistent with an established framework (such as the NIST Cybersecurity Framework), and that the system is installed, operated, maintained, and decommissioned consistently with that framework.
Capgemini reports that, “Global business internet traffic is expected to increase three-fold by 2022.” At the same time, the number of unfilled cybersecurity positions has surpassed four million worldwide, up 28% from in 2019. Simply put, there just aren’t enough security analysts to deliver on mechanical trust. And those who are on board at digitally mature companies are overburdened. That’s why cyber-savvy businesses are implementing analytics and automation into their portfolio; to focus valuable cyber security experts on tasks of greater value. This section outlines solutions that enterprises are beginning to implement in response to the challenges of the cybersecurity gap.
In this section we’ll highlight a few security areas to pay attention to in the context of Digital Trust including Zero Trust, operational security approaches and automation using RPA and the impact of AI and ML. By automating and leveraging advanced analytics, the goal is to provide Digital Trust while offering a lower friction, user-friendly experience. Remember as we engage customers and prospective customers, while they value security, they often will not participate in a cumbersome experience.
Zero Trust
Zero Trust is a strategic initiative that most organizations are implementing or considering that helps prevent successful data breaches by starting with the principle of “never trust, always verify,” Zero Trust is designed to protect modern digital environments by leveraging network segmentation, preventing lateral movement, providing Layer 7 threat prevention, and simplifying granular user-access control.
As we point out in our report, “Zero Trust Networking”, in Zero Trust, you identify a “protect surface.” The protect surface is made up of the network’s most critical and valuable data, assets, applications and services – DAAS, for short. Protect surfaces are unique to each organization. Because it contains only what’s most critical to an organization’s operations, the protect surface is orders of magnitude smaller than the attack surface, and it is always knowable.
With the protect surface identified, you can identify how traffic moves across the organization in relation to protect surface. Understanding who the users are, which applications they are using and how they are connecting is the only way to determine and enforce policy that ensures secure access to your data. Using zero trust concepts, enterprises are better equipped to address Advanced Persistent Threats (APTs), monitor behavior, record patterns, and alert when unusual activity is detected. The automation of operational security is also important as now describe.
Security Orchestration Automation and Response (SOAR) and Security Incident and Event Management (SIEM)
SOAR refers to a combination of solutions that optimize the capabilities and efficiency of your security operations center without tying up your human assets in low-level tasks.
It serves to optimize three main cyber security-related tasks — security orchestration, security automation, and security response — by improving threat and vulnerability management capabilities, security incident response, and security operations automation.
In many ways, SOAR and SIEM are similar —after all, they both collect and use relevant data from multiple sources for analysis to identify any anomalous activity. While these two solution stacks often work hand-in-hand for security operations centers (SOCs), they’re still different in a few ways:
- SIEM is more manual in nature. This system of stacked solutions requires manual responses to alerts and regular upgrades and tweaks to the technologies, rule sets, and signatures for optimization, efficiency, and detection effectiveness. However, it’s primarily limited to identifying known threats and are less effective at identifying new or unknown threats.
- SOAR is a bit more diverse in its use of internal and external applications, and it takes those SIEM alerts and responds to them automatically for triage and remediation when necessary. It relies on cognitive technologies and tools that use artificial intelligence (AI) and machine learning (ML) to learn from existing threats and to help identify new ones.
SOAR is all about using automation to improve your security operations and incident response by eliminating repetitive tasks and organizing (or “orchestrating”) the technology, people, and processes within your organization to their full advantage. For example, in a security operations center (SOC), SOAR complements SIEM capabilities by building upon them and providing extra value.
Security orchestration even has benefits in terms of preventing phishing attacks from being successful. Ernst and Young reports a “50% to 70% reduction in time to detect and response to a phishing attack” through the use of robotic automation in the data gathering, analysis, and remediation processes.
RPA
As we highlighted in our report “The State of Robotics Process Automation (RPA),” robotic process automation refers to the process of using robots — whether physical or virtual, such as software bots, to automate repetitive tasks. With regard to cyber security and security automation, this typically refers to allowing automated systems to handle low-cognitive functions such as scanning, monitoring, and low-level incident response. You know things like, extracting and aggregating data, performing basic threat search and detection processes, and other low-cognitive tasks.
There are multiple benefits of using RPA from logistical, risk, and compliance standpoints. For one, it makes cyber security more efficient by removing the burden of manually performing repetitive tasks. It also helps you to minimize the biggest cyber security vulnerability: human interaction. Whether intentional or by human error, people pose the biggest risk to the cyber wellbeing of organizations and businesses. By removing the human aspect, it makes your data more secure.
There are several ways that software robotics can aid in reducing cyber security vulnerabilities:
- RPA reduces threat detection and response time though automated detection and alert notifications.
- RPA aids in application and device discovery and inventory, helping to identify exposed attack surfaces to mitigate security risks.
- RPA improves security with automated rollout of updates and patching.
- RPA helps to fill the talent shortage gap of cyber security teams.
- RPA doesn’t tire or mentally “clock out” on the job, providing 24/7/365 security coverage.
- RPA limits the involvement of IT security pros so they can focus on other high-cognitive tasks.
- RPA limits human involvement in the management of sensitive personal information.
Additionally, RPA can help your business stay compliant with some regulations such as the EU’s General Data Protection Regulation (GDPR) or Payment Card Industry Data Security Standards (PCI DSS). For example, automation can be used for data collection, to roll out informed consent notifications, data breach notifications, as well as to document all data that’s held by your organization for audits. Why dedicate many employees to performing such tedious tasks when automation technologies can do it for you?
RPA offers many advantages to enterprises and other organizations. However, no organization should rely on RPA alone for more in-depth security operations that require higher cognitive and analytical capabilities. This part is still best left to a mix of cognitive-learning technologies and the intervention of human analysts.
Artificial Intelligence. (AI) and Machine Learning (ML)
All of the previous solutions are heavily dependent on rules-based logic to automate and enforce compliance and mechanical trust. These tools rely on a certain defined set of activities, alerts and signature-based detection. This defined set requires constant tuning in order to allow legitimate transactions while preventing evolving threats. A good cyber analyst commits hours to query the system, sort and filter the data, confirm their suspicions, and identify the nature of the threat.
AI/ML and automation greatly enhance endpoint protection, but where we see the most benefit in the technology is guiding security operations in what exactly to do with those threats once they hit the enterprise. The ever-increasing sophistication and persistence of cybercriminal activity is requiring security operations teams to rethink how they use people, processes, and technology.
By training AI software on large datasets of cybersecurity, network, and even physical information, cybersecurity solutions providers aim to detect and block abnormal behavior, even if it does not exhibit a known “signature” or pattern. By applying practical AI and machine learning, you can make your cybersecurity team’s work more effective, productive, and efficient; creating a more proactive approach to cyber defense. By seeing unknown threats steps ahead of the impact, behavioral analytics can spot out-of-norm data patterns in network traffic (such as malicious DNS tunneling activities), detecting the unidentified and more sophisticated attacks that are now evading traditional preventative techniques.
In order to make this work, you need access to data — lots of it. The more malware and benign samples you have, the better your model will be. No SOC has access to all of the data necessary to assure success. In order to do that, enterprises need to think about collective defense. One of the primary values of applying collective defense to cybersecurity comes from multiplying the number of data streams analyzed, far beyond what any one company or SOC can see on its own.
Assuming you have the data scientists and data engineers to be able to build a pipeline to process the samples continuously and design effective models, access to collective defense data is becoming more broadly available. The community of open source threat intelligence feeds has grown over time. There are new sources being offered all the time. Many companies offer freemium services to entice the usage of their paid services. There are community projects which aggregate data from new sources of threat intelligence. And there is an emerging market of companies who pull all this and other data into Threat Intelligence solutions. Finally, there are security companies who offer their threat intelligence as a community service. The result is a massive amount of information.
However, for many enterprises, it makes more sense to leverage commercial offerings, such as those from IBM, Microfocus, FireEye and others that provide a collective defense posture and integrate the intelligence into their SOAR/SEIM, RPA, and new security gateway platforms.
Placing automation and AI side-by-side with analysts on the frontlines enhances the effectiveness of both. Human security operations are not going to be replaced by machines; rather, analysts’ skills and effectiveness will be enhanced by automation, enabling them to offload data crunching and mundane tasks and focus on cognitive processes machines can’t carry out.
Providing security operations with automated tools can help to find the needle in the haystack and use valuable human intellect where it’s needed most. A skilled SOC analyst is the very best defense we have in combating threats; however, most of the analysis and processing they deliver is mundane and amounts to a waste of human capital. Ideally, human SOC analysts should be focused on more advanced and more valuable tasks like threat hunting, threat intelligence, and attribution. By employing automation, the idea is to free analysts up to work on highly important tasks, and let automation do the grunt work.
This is true not just for IT security teams but of identity teams as well who face a similar big data problem of the identity variety during their digital transformation. This means more identities (human and non-human) have to be managed across more applications (legacy and cloud) and data (structured and unstructured).
In summary the existing IAM and security services should be examined and potentially upgraded to support pervasive Digital Trust. But be aware that there are new approaches that are a bit more revolutionary that should also be examined and considered in the intermediate-to-long-term as follows in the next section.
Emerging Mechanical Trust approaches
All of the previous IAM and Security recommendations are great improvements how businesses can improve on Digital Trust, but they all focus on what a business can internally do to deliver on its responsibilities. There is another set of technologies that are emerging that has the potential to redistribute those responsibilities outside the business itself. Those include:
- Shifting the responsibility for “duty to protect” to the individual.
- Increasing transparency by actively engaging the individual in data sharing decisions.
- Embedding digital trust in shared software and networks
- Providing ethical alternatives to personal data collection and brokering.
We have written extensively on several of these emerging technologies in our research and in this report, we briefly describe them again in the context of the impact on Digital Trust.
Standardizing Identity and Data Rights
Global standards for data rights and obligations can potentially be embedded in the very fabric of the Internet through rules and protocols around data exchange.
The Internet could serve as a precedent. In its early days the Internet was restricted and focused on non-commercial exchange. The World Wide Web standards were adopted in 1990, embedding critical principles for the connection of servers including that any person could share information with anyone else, anywhere. After commercial use of the Internet was allowed in the mid-1990s, these shared protocols and principles enabled tremendous innovation.
By decentralizing the identity system (since the Internet doesn’t have an identity layer), we are effectively replacing the tightly coupled identity solutions each service has, with a more open, flexible and powerful alternative. This unlocks a whole set of experiences and opportunities for everyone. We have reached a pivotal moment in history where technology is making this possible, and people, businesses and other entities are more sensitive than ever on the matter of digital identity, as it has become an integral part of our lives.
Decentralized Identity and Verifiable Credentials
In short, Decentralized Identifiers (DIDs) are user-generated, self-owned, globally unique identifiers rooted in decentralized systems, such as distributed ledger (blockchain) networks. DIDs resolve to DID Documents which describe how to use that specific DID. Most importantly, it contains a set of cryptographic material and endpoints that can be used to interact with the identity subject.
DIDs begin by being “trustless” in the sense that they don’t directly provide meaningful identity attributes. However, trust between DID-identified peers can be built up through the exchange of Verifiable Credentials — credentials about identity attributes that include cryptographic proof. These proofs can be verified by reference to the issuer’s DID and DID Document.
Both of these open standards are becoming important as they grow in adoption. For example, Microsoft has recently announced they are building a Decentralized Identity solution which uses DIDs and Verifiable Credentials, highlighting the potential importance these standards might have in our future lives.
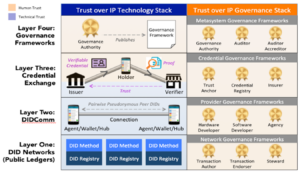
In an effort separate from Microsoft’s, the Linux foundation announced on 5 May 2020 the formation of the Trust Over IP (ToIP) foundation to further open standards around decentralized identity. The IBM Security Group recently provided TechVision Analysts with a detailed perspective on ToIP as IBM is embracing this model. The ToIP Foundation will use digital identity models that leverage interoperable digital wallets and credentials and the new W3C Verifiable Credentials standard to address these challenges and enable consumers, businesses and governments to better manage risk, improve digital trust and protect all forms of identity online. As shown in the following figure, the ToIP foundation will be focusing on building out both the technology and governance stacks of the ToIP framework.
Figure 5 – TiOP Framework
The ToIP Foundation has been established with global, pan-industry support from leading organizations with sector-specific expertise. Founding Steering members include Accenture, BrightHive, Cloudocracy, Continuum Loop, CULedger, Dhiway, esatus, Evernym, Finicity, Futurewei Technologies, IBM Security, IdRamp, Lumedic, Mastercard, MITRE, the Province of British Columbia and SICPA. Contributing members include DIDx, GLEIF, The Human Colossus Foundation, iRespond, kiva.org, Marist College, Northern Block, R3, Secours.io, TNO and University of Arkansas.
Solid/InRupt
Solid/Inrupt is another effort to standardize identity and data ownership/exchange. Since 2015, Tim Berners-Lee (the inventor of the Web and director of the W3C) has been working on a new web infrastructure called Solid, which rethinks how web apps store and share personal data. Inrupt aims to drive the development of the Solid platform and transform it from an innovative idea to a viable platform for businesses and consumers.
Over the past three decades, the web has evolved into something very different from Berners-Lee’s original vision of openness, co-operation and creativity. Most of the data we put online is now siloed on the servers of companies like Google, Facebook, LinkedIn and Twitter, and used to sell individuals as an audience for targeted advertising. We can download and delete our online histories, but we still can’t easily move our data between services.
The big idea behind Solid is that, instead of a company storing all your personal data on their servers, you would keep it on your own personal data “pod”, located on a Solid server. You could run your own server or host it with a provider, much like a personal website. You could then give individual apps permission to read and write to your pod. When you want to stop using an application, you just revoke its access. The data remains on your pod, and businesses making applications never have to worry about storing it, deleting it, or making it easily exportable. Solid uses existing web standards like URLs, DNS, HTTP, and Linked Data to accomplish this. Solid and Inrupt (Inrupt started in 2019) are newer projects and are just beginning the experimentation phase but promising in that they are backed by Tim Berners-Lee and fit within this Digital Trust concept.
Both Decentralized Identity and Solid are based in standards and are in essence shifting the responsibility for data security back to the data provider, the individual. Where Decentralized Identity is initially focused on building trust through the collection and sharing of attributes (credentials) that are issued and verified by trusted third parties, Solid is focused on creating a sharable version of truth that belongs to the individual and is portable across hosts and applications.
As businesses start to embrace this trend, their “duty to protect” personal data becomes less burdensome. The business no longer needs to keep centralized stores of customer information as a matter of convenience. As an example, businesses routinely keep user IDs, passwords, credit card numbers, and a whole host of personal data to maximize the customer experience. If those data could be made available to the business as needed (and permitted) from the customer’s data stores, then the need to retain that information is eliminated.
Data Utilities
Companies now use data to add value to almost every aspect of life, enhancing people’s social lives, lowering business costs and providing services and information that facilitate all manner of daily interactions. To achieve this, many employ cookies and device-tracking technology to follow online activity and infer information such as preferences. They then use these not only to improve their own services but also to send notifications and targeted advertising.
These proprietary data platforms provide access to unique aspects of data activities, along with the accumulation of data and analytics, and this has produced deep network effects. Each platform also has its own approach to how much data is shared and how much control consumers have. This is driving governments to intervene with privacy regulations that are placing more burdens on consumers and businesses to manage personal data.
Data utilities are an emerging trend that could offer a simpler way for users to manage data without having to manage consent with every firm with which they come into contact. Marketplaces, where firms could trade consumer data, would give individuals centralized control over how information about them is used and shared. There are several start-ups exploring this new concept, including an open-standard, Ethereum-based platform, XBR, based in the EU.
Consumer-centric data utilities may not replace the need for baseline data protections entirely, but they could streamline the complex web of data management responsibilities that businesses now have. Models could also emerge that allow individuals not only data control but also data monetization. This trend is shifting the responsibilities of consent management and privacy protection towards the individual (end point) and away from the business which manages fewer personal data on behalf of the consumer.
Even without a broader adoption of personal data marts, data utilities run by coalitions of firms could help businesses exchange aggregate, rather than individual data. Sharing aggregated data could help alleviate privacy concerns associated with sharing individual-level data (providing the data is anonymized) and facilitate the sharing of “data insights” that help solve broader challenges, for example in cyber security.
Data.World is an example of business-focused data utility. Data.World is a public benefit corporation that:
- strives to build the most meaningful, collaborative and abundant data resource in the world in order to maximize data’s societal problem-solving utility,
- advocates publicly for improving the adoption, usability, and proliferation of open data and linked data, and
- serves as an accessible historical repository of the world’s data.
The Data.World platform is built on Linked Data and Semantic Web technology that makes it easy for both humans and machines to consume the vast collection of open/public data available on the platform. When each dataset that is added to the network increases the incremental value of every dataset on the platform, the network effect can be an incredible multiplier for people solving the world’s most difficult problems. While broad adoption is a way off, this is a trend to monitor.
Blockchain
Blockchain/Distributed Ledger technology is an example of imbedding trust in a system or network. Blockchain is simply a secure, shared database. In its purest form, everyone connected to a blockchain network has access to the same set of information. Think of blockchain as a permanent, replicated, distributed, yet secure ledger where all parties have access to the same information. Much like an accounting ledger, blockchain is a platform for recording transactions, but it intrinsically makes this shared data available. Blockchain, or distributed ledger technologies don’t change our need for financial or operational transactions, but they do radically change the way we execute and confirm those transactions.
L et’s start by looking at what most enterprises are typically doing today. Whether it is between internal applications or across enterprise boundaries, the general architecture template is to capture and process transactions in internally controlled data stores. That creates a workflow similar to this.
et’s start by looking at what most enterprises are typically doing today. Whether it is between internal applications or across enterprise boundaries, the general architecture template is to capture and process transactions in internally controlled data stores. That creates a workflow similar to this.
- Receive transaction,
- Record transaction,
- Verify transaction,
- Accept transaction,
- Reconcile transaction,
- Audit transaction,
- and all along the way, handle errors and exceptions.
Of course, applications add value beyond these simple steps, but this is a good portion (as much as 40%) of the processing typical enterprise operational systems and organizations do every day to ensure transactional trust between parties.
Blockchain replaces those redundant processes with a software-based distributed database visible to and replicated across all of the participants of the blockchain network. The governing frameworks, protocols, and peer-reviewed / open-sourced software assure consistency, validity, immutability, and finality for every transaction recorded on the blockchain.
Shifting from a “record and verify” model to one where trust in the data is imbedded in the system is why so many enterprises are experimenting with Blockchain technology today.
Relational Trust
Even when all the mechanical systems work, if people don’t believe that we’re all playing by the same rules, trust breaks down. That is why relational trust—the social norms and agreements that address life’s complex realities—is vital. While the brakes in a car may be highly reliable, we also need a shared agreement that a red light means that we use them. Similarly, we need a shared agreement on when, where, why, and how technologies are used. This aspect of trust is harder for most businesses because it has more to do with behavior than technology.
Relational Trust Begins with Reputation
 Executives know the importance of their companies’ reputations. Firms with strong positive reputations attract better people. They are perceived as providing more value, which often allows them to charge a premium. Their customers are more loyal and buy broader ranges of products and services. Because the market believes that such companies will deliver sustained earnings and future growth, they have higher price-earnings multiples and market values and lower costs of capital. Moreover, in an economy where 70% to 80% of market value comes from hard-to-assess intangible assets such as brand equity, intellectual capital, and goodwill, organizations are especially vulnerable to anything that damages their reputations. An enterprise’s online reputation determines whether a prospect would even be willing to engage and for many, that’s a problem.
Executives know the importance of their companies’ reputations. Firms with strong positive reputations attract better people. They are perceived as providing more value, which often allows them to charge a premium. Their customers are more loyal and buy broader ranges of products and services. Because the market believes that such companies will deliver sustained earnings and future growth, they have higher price-earnings multiples and market values and lower costs of capital. Moreover, in an economy where 70% to 80% of market value comes from hard-to-assess intangible assets such as brand equity, intellectual capital, and goodwill, organizations are especially vulnerable to anything that damages their reputations. An enterprise’s online reputation determines whether a prospect would even be willing to engage and for many, that’s a problem.
A fact of life these days is that 87% of shoppers now begin their hunt in digital channels (according to Salesforce), and reputation is front and center in those searches.
Reputation is now reflected online, by algorithms which take the trust attributes of competence, integrity, benevolence, and predictability and turn them into measurable scores. It’s “digitizing” relationships and social connections, extracting value and insights from our associations and both codifying and commoditizing trust. The big search and social platforms have trust scores for participants that evaluate reputation based on “proof sources” such as:
- Vouching – by people you know (friends, family, celebrities, influencers)
- Certificates – from sources you trust (government agencies, schools, watchdogs)
- Reviews – from people with brand or personal experience
- Fact checking – corroborating statements of fact through various methods
The trust scores signal that the trustee’s claims of trustworthiness are true. And trust is a highly valuable currency in the world of commerce. And it’s being reflected in everything from search ranking to the cost of digital ad placement.
Transparency is another key factor in how consumers interact with and trust brands; the Salesforce Trends in Consumer Trust Research Study demonstrates that 91% of consumers are more likely to trust a company with their data if the company is transparent about the way in which it is used. Furthermore, 79% of consumers are willing to share relevant personal information about themselves with companies in exchange for contextualized interactions, such as personalized offers before purchases. Personalization, protection, and transparency are differentiators and their absence can be costly.
It’s not What You Say, It’s What You Do
The 2019 Edelman Brand Trust Survey revealed only 39% believe digital companies put welfare of customers ahead of profits. What’s more, although 81% say trust impacts their purchasing decisions, only a third of people say they trust the brands they buy from. And, 41% say they don’t trust brands’ marketing communications to be accurate or truthful.
Those are some pretty concerning data. And once customer trust is lost, it’s hard to get back. According to Edelman’s survey, 45% of consumers would never trust a brand again after it displays unethical behavior or is involved in a scandal, and 40% say they’d stop buying from that brand altogether.
Consumers aren’t only wary about the truthfulness of a brand’s communications they’re concerned about their data being used improperly. Salesforce reports that over half of consumers fear their personal data are vulnerable to hackers and think companies don’t operate with their best interests in mind. Bottom line, customers trust companies that:
- Act honestly and upright (Integrity)
- Are capable and competent within their fields (Competence)
- Balance their own interests than with the interest of others (Benevolence)
- Act with consistency (Predictability).
And relational trust is reinforced when words and actions at the communication points of the customer journey consistently reflect those attributes. As the title says, it’s not what you say it’s what you do that fosters trust.
Privacy Policies Make the Promise
Begin by shifting privacy policies from corporate rights documents into something reflecting a more equitable relationship between your business and your customers. Most organizations can start with the Privacy by Design principles. Specific areas of focus include:
- Craft Trust and Transparency – tell customers the who, what, where, when, and why of your data collection practices. Better yet, share why and how that data will be leveraged in the big picture. When customers understand the details, it’s much easier to get them on board and build trust in the brand relationship and the ensuing business they represent to the enterprise.
- Build Peer Relationships – In the digital enterprise, the customer has become the gatekeeper of the data that drives customer experience. It takes transparency, strong tactics, and quality outreach tools for brands to gather active permission from customers. With detailed information and permission gathered through active consent, brands can then use data tools to figure out how to deliver unique value at scale for each customer and lead in the sales pipeline. This requires the enterprise to shift asymmetric privacy policies and terms of service that advantage the business and disadvantage the customer to something that reflects the shift to a balanced relationship.
- Outline Specifics of Data Collection – Customer’s value clear policies that spell out their rights vs. a brand’s rights. So, actively create one. Be upfront with customers about data details, including who gets to view and work with the data, then put it in writing. Also, let them know how long their data will be stored. In short, provide good data stewardship throughout the customer relationship. It’s quickly shifting from nice-to-have policy to one that is expected as part of the customer experience.
- Offer Customer Data Review Rights – As an active part of gathering all the necessary customer data it’s important to offer an easy option for customer data review. When customers see the data that brands are using with their own eyes and can correct any misinformation, they feel they have a voice.
Trust frameworks.
Trust Frameworks are replacing individual corporate privacy policies in instances where identity federations are in use. Examples are Sovrin in the world of self-sovereign identity or the payment card framework that is the basis for today’s ATM networks. The trust framework is a document that publishes the tools and rules together with an assessment and enforcement infrastructure that operationalizes them. In most cases the document serves as a new type of contract that legally binds the members of the trust community to the policies. In this fashion, a trust framework operates on a much higher level than site-specific privacy policies or TOS (terms-of-service)”. At the core of any framework is the concept of relational trust.
The American Bar Association (ABA) defines a trust framework as follows:
A Trust Framework is the governance structure for a specific system consisting of:
- The Technical and Operational Specifications that have been developed –
- to define requirements for the proper operation of the system (i.e., so that it works),
- to define the roles and operational responsibilities of participants, and
- to provide adequate assurance regarding the accuracy, integrity, privacy and security of its processes and data (i.e., so that it is trustworthy); and
- the Legal Rules that govern the identity system and that —
- regulate the content of the Technical and Operational Specifications,
- make the Technical and Operational Specifications legally binding on and enforceable against the participants, and
- define and govern the legal rights, responsibilities, and liabilities of the participants of the system.
It is written in terms of equal peers not users and applications, and every member of the network agrees to comply with the framework. The trust framework is a digital form of social contract that manages behavior and can be enforced for every transaction that occurs.
Regardless of whether the agreement is through an individual privacy policy or a network trust framework, once the promise is made, you have a duty to deliver on that promise. And now that promise extends to your supply partners as well as traditional supply chains become adaptable digital supply networks.
Data Stewardship Delivers on That Promise
The definition of stewardship is “an ethic that embodies the responsible planning and management of resources.” In the realm of data management, data stewards are the keepers of the data throughout the organization. A data steward serves as the conduit between data governance policymaking bodies, like a data governance council, and the data management activity that implements data policies. Data stewardship is critical in maintaining Digital Trust in that proper data stewardship delivers on the promises of the privacy policies as it carries out its governance and management responsibilities.
Data Governance – Data governance is a system for defining who within an organization has authority and control over data assets and how those data assets may be used. It encompasses the people, processes, and technologies required to manage and protect data assets. The goal of data governance is to establish the methods, set of responsibilities, and processes to standardize, integrate, protect, and store corporate data. Data governance needs to include a role for the customer so that the governance function reflects the reality of relational trust.
Data Management – Data management is the set of functions designed to implement the policies created by data governance. These functions have both business and IT components, so it is vital that the overall program be designed holistically. Data management functions include data quality, metadata, architecture, administration, data warehousing and analytics, reference data, master data management and other factors. Reflecting the growing role of the customer and regulators requires building flexibility into data management functions to enact and demonstrate transparency and compliance.
Define and implement an ethical framework for AI/ML
The final aspect of improving relational trust is to be transparent about how AI and ML capabilities will be applied to customer data. The most commonly deployed form of AI can be described as a set of math functions (model) that given some inputs (data), learn “something” and use that to 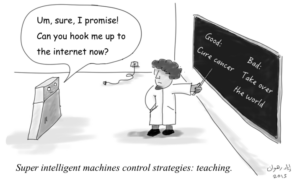 “infer” something else (make predictions). In other words, AI is data, model and predictions. Ethical exploration of this realm covers issues like bias in a models’ predictions and fairness of the outcomes; as well as approaches to address them via accountability and transparency. Most of the mistrust customers have of AI capabilities can be summarized in three points.
“infer” something else (make predictions). In other words, AI is data, model and predictions. Ethical exploration of this realm covers issues like bias in a models’ predictions and fairness of the outcomes; as well as approaches to address them via accountability and transparency. Most of the mistrust customers have of AI capabilities can be summarized in three points.
- Safety – Safety in AI can be understood as “AI must not cause accidents or exhibit unintended or harmful behavior”. For a hardware-software composite to make the right calls requires that it be responsive to contexts as they arise, be able to model this uncertainty in its environment, and be aligned on what is “right”. Alignment to the “right” goal, aka value-alignment, is a key theme of safety in AI.
- Cyber-security and Malicious Use – While, as we described earlier, AI is increasingly finding use in enabling cyber-security by detecting and preventing intrusions, it is itself susceptible to gaming and malicious use. In a data-driven, highly networked, always online world the risks are significant. In addition to classical threats, AI systems can be gamed by poisoning the input data or modifying the objective function to cause harm.
- Privacy, Control and Surveillance – Along the lines of harms and misuse of tech is AI’s ability to be repurposed, or even intentionally designed, for surveillance. Ask people to describe privacy and you’ll get multiple definitions. This is reasonable given privacy is a social construct, evolving with time and influenced by cultural norms. While defining privacy is hard, identifying its violation is intuitive; it involves dignity and control. That’s why commercial DNA mapping and facial recognition have become such hot issues.
To get people to trust your use of AI capabilities in the customer journey, you must articulate and abide by an ethical framework that provides, safety, protection from malicious use, and dignity and control. That framework should articulate the following:
- Accountability – The business, including the AI designers and developers are responsible for the AI design, development, decision processes, and outcomes. In other words, the business needs to take responsibility for the results, even if they are misused or proven faulty.
- Value Alignment – AI should be designed to align with the norms and values of your user group in mind. This gets back to the idea of benevolence. An “I win; you lose” perception of the AI capability will reduce trust dramatically.
- Explainability – AI should be designed for humans to easily perceive, detect, and understand its decision process. The decisions made should be shared with the customers including the rationale behind them.
- Fairness – AI must be designed to minimize bias and promote inclusive representation. This needs to be proven over time. If implicit bias shows in patterns over time, the AI capability needs to be “retaught”.
- User Data Rights – AI must be designed to protect user data and preserve the user’s power over access and uses as described in the privacy policy.
Conclusions and Recommendations
So, what can you do to actively build trust with your customers? In a world where your brand is less what you say and more the collective experiences of everyone using it, you can’t simply rely on marketing to meet the challenge for you in the future. Your organization needs to prove itself in your policies supported by a strong Security and Identity foundation.
To build and maintain trust, businesses need to make sure they are delivering on both mechanical and relational trust. Without the balance, customers will not share the data required to drive the proper customer experience. And if your customer experience is lacking it won’t be long before customers are seeking alternatives.
For mechanical trust, address the challenges in IAM and security that infrastructure decentralization and enhanced customer engagement pose to traditional approaches. And look to the emerging trends that are shifting the security landscape as digitalization and decentralization increases.
Enterprise security/IT leaders have refined their authorization strategy through PAM, RBAC, and Zero Trust to a least privilege stance. For external identities, they have also deployed Federation and CIAM to manage the scale, consent, and relationships for millions of entities.
Furthermore these leaders are applying automation through SOAR/SIEM and RPA driven by AI/ML to manage the complexity of shifting and increasing volumes of transactions.
Finally, explore and plan for the adoption of emerging technologies that are shifting the “duty to protect” to the owners of the data or embedding them into a shared network or system.
For relational trust, refine privacy policies to reflect a more transparent and peer-like relationship between the business and its customers; and then make sure to deliver on the promises those policies represent. Assure your customers that the AI capabilities that are designed to make their experiences better are designed and used in an ethical manner.
Companies that keep their promises and operate transparently enjoy more trust as their customers are more likely to share their positive experiences and spread a good word through social media. Besides, dealing with customer complaints professionally via social can positively impact consumers’ trust, too. While some businesses consider it’s safer to keep sanitizing content and taking negative consumer conversations offline, those who manage to resolve it positively in public reap even bigger reward in terms of customer trust. No surprise, customers don’t expect you to be faultless. However, the way you fix things when they go wrong proves what your business is worth and if they can trust you.
About TechVision
World-class research requires world-class consulting analysts and our team is just that. Gaining value from research also means having access to research. All TechVision Research licenses are enterprise licenses; this means everyone that needs access to content can have access to content. We know major technology initiatives involve many different skill sets across an organization and limiting content to a few can compromise the effectiveness of the team and the success of the initiative. Our research leverages our team’s in-depth knowledge as well as their real-world consulting experience. We combine great analyst skills with real world client experiences to provide a deep and balanced perspective.
TechVision Consulting builds off our research with specific projects to help organizations better understand, architect, select, build, and deploy infrastructure technologies. Our well-rounded experience and strong analytical skills help us separate the “hype” from the reality. This provides organizations with a deeper understanding of the full scope of vendor capabilities, product life cycles, and a basis for making more informed decisions. We also support vendors in areas such as product and strategy reviews and assessments, requirement analysis, target market assessment, technology trend analysis, go-to-market plan assessment, and gap analysis.
TechVision Updates will provide regular updates on the latest developments with respect to the issues addressed in this report.
About the Authors
 Gary Zimmerman is an experienced executive known for helping companies deliver new offers and expand markets. Accomplishments include launching four companies, 20+ products, building high-performance organizations, and generating millions in sales.
Gary Zimmerman is an experienced executive known for helping companies deliver new offers and expand markets. Accomplishments include launching four companies, 20+ products, building high-performance organizations, and generating millions in sales.
His experience at Neustar, Respect Network, and Sovrin allows him to provide a broad perspective on a variety of subjects including self-sovereign identity, blockchain, enterprise data management, and the data brokerage industry. His experience both enterprise and startup product development give him a unique perspective on innovation.
 Gary Rowe is a seasoned technology analyst, consultant, advisor, executive and entrepreneur. Mr. Rowe helped architect, build and sell two companies and has been on the forefront the standardization and business application of core infrastructure technologies over the past 35 years. Core areas of focus include identity and access management (IAM), Decentralized Identity, Blockchain, Internet of Things, cloud computing, security/risk management, privacy, innovation, AI, new IT/business models and organizational strategies.
Gary Rowe is a seasoned technology analyst, consultant, advisor, executive and entrepreneur. Mr. Rowe helped architect, build and sell two companies and has been on the forefront the standardization and business application of core infrastructure technologies over the past 35 years. Core areas of focus include identity and access management (IAM), Decentralized Identity, Blockchain, Internet of Things, cloud computing, security/risk management, privacy, innovation, AI, new IT/business models and organizational strategies.
He was President of Burton Group from 1999 to 2010, the leading technology infrastructure research and consulting firm. Mr. Rowe grew Burton to over $30+ million in revenue on a self-funded basis, sold Burton to Gartner in 2010 and supported the acquisition as Burton President at Gartner.
[1] Competitive Enterprise Institute – Ten Thousand Commandments 2019
[2] Ibid.
[3] Corporate Compliance Insights – The True Cost of Compliance 2018
[4] GlobalScape – 3 Factors Driving Compliance Costs for Financial Services 2018
[5] Ibid.
[6] Ibid.
[7] Ibid.
[8] GlobalScape – 3 Factors Driving Compliance Costs for Financial Services 2018
[9] Nielsen Global Survey of Trust in Advertising