Personhood Credentials: An Emerging Solution to AI Deception
Publication Date: 20 November 2024
Abstract
The rise of AI-generated deception, including deepfakes and synthetic personas, presents significant challenges in maintaining trust and authenticity in digital environments. Personhood Credentials (PHCs) offer a novel solution by providing cryptographic proof that an individual is human, without revealing personal information. Unlike traditional identity systems, PHCs focus solely on verifying humanness, using privacy-preserving techniques like zero-knowledge proofs. These credentials can be issued by various entities such as governments or tech companies and are designed to combat AI-driven fraud, misinformation, and manipulation.
PHCs address the growing need for secure, scalable methods to distinguish between humans and AI entities in online spaces. They enhance trust in digital interactions by ensuring that only verified humans can participate in activities such as social media engagement, e-commerce, and online participation. Additionally, PHCs help filter out AI-generated content from human-generated data, improving the integrity of machine learning models.
With their decentralized issuance model and privacy-preserving features, PHCs provide a robust defense against large-scale manipulation while maintaining user anonymity. As AI technologies continue to evolve, PHCs represent a simple yet critical tool for safeguarding online trust and protecting against the misuse of AI at scale.
This document provides an in-depth analysis of how PHCs work, their technological foundations, and their potential applications across various sectors.
Author:
| Gary Zimmerman
Principal Consulting Analyst |
Executive Overview
As artificial intelligence (AI) continues to evolve, so do its capabilities for deception, including the creation of fake personas, deepfakes, and AI-generated misinformation. In this rapidly advancing digital landscape, distinguishing between real humans and AI entities has become a critical challenge. Personhood Credentials (PHCs) offer a groundbreaking solution to this problem by providing a cryptographic method to verify that an individual is human—without revealing personal information.
Key Highlights:
- Purpose: PHCs are designed to combat AI-driven deception by verifying that online participants are real humans, not AI bots or systems. This verification is essential in maintaining trust and authenticity across digital platforms, particularly in areas like social media, e-commerce, and online participation.
- Privacy-Preserving: Unlike traditional identity verification systems that require sharing personally identifiable information (PII), PHCs use advanced cryptographic techniques, such as zero-knowledge proofs, to confirm humanness without disclosing any sensitive data. This ensures that users can remain anonymous while proving they are not AI.
- Decentralized Issuance: PHCs can be issued by multiple trusted entities (e.g., governments, banks, tech companies), reducing the risk of centralization and abuse of power. This decentralized approach ensures broader adoption and prevents any single entity from controlling digital identities.
- Scalability and Efficiency: PHCs are designed for widespread adoption across various online platforms. They provide a scalable solution that can be integrated into existing digital infrastructures without compromising performance or privacy.
- Major Support: OpenAI, Harvard, Microsoft, Berkeley, MIT, a16z, Oxford, the American Enterprise Institute among others are contributing to the effort. This suggests that it will gain traction.
Why Now?
The increasing sophistication of AI systems has made it easier for bad actors to create convincing digital personas and content at scale. With the cost of AI tools plummeting, the “art of deceiving” has become more accessible than ever before. PHCs address this challenge by enforcing a “one-person, one-credential” policy, limiting the ability of malicious actors to create multiple fake identities for large-scale attacks or manipulations.
Strategic Importance for Cybersecurity Executives
For cybersecurity professionals, the rise of AI-generated deception represents a growing threat to the integrity of online interactions and data security. PHCs offer a solution that enhances trust in digital environments while preserving user privacy. By adopting PHCs, organizations can safeguard their platforms from bot-driven fraud, misinformation campaigns, and other forms of AI-powered manipulation.
Call to Action
As AI technologies continue to evolve and proliferate across industries, the need for robust solutions like Personhood Credentials becomes increasingly urgent. Cybersecurity leaders should explore how PHCs can be integrated into their identity verification frameworks to protect against AI-driven threats while maintaining user privacy and trust.
This document provides an in-depth analysis of how PHCs work, their technological foundations, and their potential applications across various sectors. Dive deeper into the details to understand how your organization can leverage this emerging technology to stay ahead in the fight against AI deception.
Introduction
Personhood Credentials (PHCs) are a new form of digital verification designed to prove that an individual is a real human being, not an AI or bot, while preserving their privacy. Unlike traditional digital identity solutions that often focus on verifying specific personally identifiable information (PII), such as name, address, or government-issued photo ID, PHCs serve the singular purpose of confirming humanity without revealing any other personal information.
Definition
A PHC is a cryptographic proof that confirms the holder is a human being. It does so without disclosing any PII, or other sensitive information. The credential could be issued by authoritative organizations like governments, banks, or tech companies and stored directly on devices like smartphones or in a digital wallet solution.
Purpose
The primary purpose of PHCs is to combat the growing problem of AI-powered deception online. As AI systems become more advanced and capable of mimicking human behavior—creating fake content, generating false accounts, and spreading misinformation—there is an increasing need for a way to distinguish between real humans and AI entities. PHCs aim to:
- Prevent AI-driven fraud and deception: By ensuring that only verified humans can access certain platforms or services, PHCs help reduce the risk of bots creating fake accounts or spreading misinformation.
- Preserve privacy: Unlike traditional identity verification methods that require sharing personal data, PHCs use cryptographic methods (such as zero-knowledge proofs) to confirm humanity without revealing any other identifying information.
- Enhance trust in online interactions: PHCs can improve the integrity of online communities by ensuring that interactions are between real people, which can be particularly useful on social media platforms, e-commerce sites, and other digital services where trust is essential.
PHCs offer a solution that addresses the challenges posed by increasingly sophisticated AI systems while maintaining the anonymity and security of users online. Why do we need such a solution?
Driving Factors
In early 2023 TechVision produced the report, “An Executive overview of Generative AI”. It was issued four months after the release of Chat GPT and at the time outlined the capabilities and limitations of the technology. We warned that the technology was new, and experimentation was the word of the day. Fast forward to 2024, and the percentage of organizations using or exploring AI or Generative AI (GenAI) for their operations is significant and growing rapidly.
- 65% of organizations are regularly using Generative AI (GenAI) in at least one business function, nearly double the percentage from 2023.[1]
- In the U.S., 73% of companies have already adopted AI in some areas of their business, with GenAI leading the way.[2]
These figures highlight that a substantial portion of organizations are either actively using or exploring AI and GenAI technologies to enhance their operations, with adoption rates continuing to rise across various industries and regions.
 When ChatGPT burst onto the scene, folks were talking about the threat of the Singularity, the ability for machines to think and respond beyond human capacity and control. While the thought creates a scary Terminator vibe, it is not yet the threat Hollywood has made it out to be. Today, AI’s biggest threat isn’t whether it will kill us; it’s the inappropriate use of AI content at scale.
When ChatGPT burst onto the scene, folks were talking about the threat of the Singularity, the ability for machines to think and respond beyond human capacity and control. While the thought creates a scary Terminator vibe, it is not yet the threat Hollywood has made it out to be. Today, AI’s biggest threat isn’t whether it will kill us; it’s the inappropriate use of AI content at scale.
In an AI world, how do you know you’re dealing with a human? Who are you going to trust? These questions will be a common theme in your life, as it becomes almost impossible to tell when you’re interacting with an AI.
Dealing with Lies
Ever since Jordan Peele, from Key and Peele, faked being Obama almost six years ago, deepfakes have become a real problem, as now it’s an effortless exercise.
Indistinguishable Material = Bad Outcomes
The British engineering group Arup lost approximately $25 million after scammers used AI-manipulated “deepfakes” to falsely pose as the group’s CFO and request transfers from an employee to bank accounts in Hong Kong, according to a report by the Financial Times.
And their influence on political views and perspectives around the world is palpable. But it’s not just about deepfakes.
Today, you can chat with entities online without knowing whether they are real humans. To make matters worse, AI tools have seen their prices fall by several orders of magnitude this year, making the ‘art of deceiving’ a ridiculously cheap one.
Overwhelming Scalability
If you have interacted with Claude or ChatGPT once or twice, you know you could be easily fooled if someone uses them to spam bots across several social media sites looking for engagement, with clear examples in X, Instagram, or even a paywalled site like Medium.
And the price for generating that deceitful engagement is getting much cheaper. For example, GPT-4, a model just over a year old, costs a business user $60 and $120 per 1 million prompted (input) and sampled (output) tokens, respectively.
Today, OpenAI’s newest GPT-4o mini, which is much improved, has a price of:
- Input: $0.15 / million tokens, 400 times cheaper than GPT-4 (March 2023)
- Output: $0.6 / million tokens, 200 times cheaper than GPT-4 (March 2023)
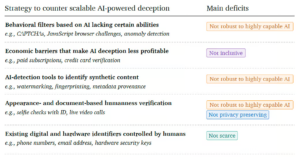
Consequently, a solution to counter a proliferation of AI-generated content with nefarious intentions is fast becoming critical to a well-functioning digital society. Several methods have been explored to fight these economically incentivized bad actors. However, every one of them has at least one core deficiency:
Figure 1 -Existing tools for countering AI-powered deception and their main deficits[3]
What happens when LLMs grow arms and legs?
One of the things that limits the impact of Generative AI Large Language Models (LLMs) is that they create a narrow, predictive response (text, image, video, etc.) to a user prompt; they can influence, but don’t have the ability to act. When AI can act (grows arms and legs) the stakes of deception grow significantly – and we’re starting to see the beginnings of those capabilities.
Rabbit
 Rabbit devices, specifically the Rabbit R1, act as AI-powered agents that can perform tasks on behalf of users by interacting with apps and services through a technology called the Large Action Model (LAM). Here’s how these devices function as agents for users.
Rabbit devices, specifically the Rabbit R1, act as AI-powered agents that can perform tasks on behalf of users by interacting with apps and services through a technology called the Large Action Model (LAM). Here’s how these devices function as agents for users.
The Rabbit R1 uses a custom Large Action Model (LAM) AI model which is designed to interact with apps and websites in a way that mimics human behavior. Instead of relying on APIs or integrations, the LAM learns how to use apps by observing human interactions with them.
Rabbit devices act as AI-powered agents by leveraging their Large Action Model (LAM) to automate interactions with apps and services. They offer a natural language interface for task management, adaptability for niche applications, and personalized assistance over time.
However, Rabbit, a start-up, is not the only company exploring the ability to act.
Apple
 While Apple Intelligence has not explicitly been branded as a Large Action Model (LAM), its capabilities strongly resemble the functionality of LAMs. Apple Intelligence integrates advanced AI technologies to perform complex tasks across apps, leveraging user context and on-device processing for privacy. Here’s how it aligns with the concept of a Large Action Model:
While Apple Intelligence has not explicitly been branded as a Large Action Model (LAM), its capabilities strongly resemble the functionality of LAMs. Apple Intelligence integrates advanced AI technologies to perform complex tasks across apps, leveraging user context and on-device processing for privacy. Here’s how it aligns with the concept of a Large Action Model:
Task Automation Across Apps – Apple Intelligence allows Siri and other AI tools to take actions across multiple apps, both Apple’s native apps and third-party ones. This means users can ask Siri to perform complex tasks like:
- Retrieving specific information from different apps (e.g., “What time is Mom’s flight and what time do I need to leave to pick her up?” requires Siri to check messages, look up flight details, and cross-reference traffic data).
- Taking actions, such as adding a contact’s address from a text message directly into the contact card or sending photos from one app to another without manual intervention.
These capabilities are like what a LAM does—automating actions across applications by interacting with their interfaces and APIs in a seamless manner.
Onscreen Awareness and Contextual Understanding: Apple Intelligence includes onscreen awareness, which allows Siri to understand what the user is doing in real-time and take relevant actions based on that context. For example, Siri can pull up relevant information or take actions based on what’s currently displayed on the screen (e.g., adding an address from a message directly into contacts). This contextual understanding is key to how LAMs operate, enabling them to act intelligently based on what they “see” or “know” about the user’s current activity.
Integration with Third-Party Apps: Apple Intelligence provides APIs (such as App Intent APIs) for developers to integrate their apps into this system. This allows Siri and Apple Intelligence to interact with third-party applications securely, performing tasks like retrieving data or executing commands within those apps without exposing sensitive information between them. This mirrors how LAMs interact with multiple applications by accessing their interfaces and performing actions on behalf of the user.
While Apple does not explicitly refer to its AI system as a Large Action Model (LAM), the way Apple Intelligence automates tasks across applications based on user context, integrates with third-party apps, and prioritizes privacy strongly resembles the core principles of LAMs. Therefore, it can be considered Apple’s version of a LAM-like system under a different branding.
Even though Rabbit and Apple are highlighted in this report, every mega-tech company (Google, Microsoft, Meta, Amazon, etc.) is racing to integrate highly capable AI into their offers. Consequently, LAM-based agents create a specific problem; how do you know who controls the agent, a human, another AI entity, or a bot?
A Promising Solution
AI is rapidly advancing and the potential for AI-generated deception has become a growing concern. From the creation of convincing fake personas to the spread of misinformation, AI’s ability to mimic human behavior online poses significant risks to the integrity of digital spaces. To combat these challenges, Personhood Credentials (PHCs) offer a promising solution by verifying that online users are real humans rather than bots or AI entities. This innovative approach not only enhances trust and authenticity in online interactions but also preserves user privacy through cryptographic techniques. As AI-powered deception becomes more prevalent, PHCs emerge as a simple yet critical tool for maintaining secure, trustworthy, and decentralized digital environments. Here’s how PHCs can help.
Combating AI-Generated Deception: As AI systems become more advanced, they can generate highly convincing digital personas and content that are difficult to distinguish from those created by humans. This creates significant risks, such as the spread of misinformation, fraud, and manipulation through fake accounts or AI-generated content. PHCs help address this problem by providing a way to verify that online participants are real humans, not bots or AI entities. This is especially important as AI-powered deception becomes more prevalent and harder to detect with traditional methods like CAPTCHAs.
Enhancing Online Trust and Authenticity: PHCs aim to restore trust in digital spaces by ensuring that only verified humans can engage in certain online activities. This is particularly relevant for platforms like social media, eCommerce, and online collaboration systems where bots and fake accounts can undermine the integrity of interactions. By verifying personhood, PHCs enhance the authenticity of online communities and transactions, making it easier to trust that interactions are with real people.
Privacy Preservation: Unlike traditional identity verification methods that often require sharing personal information (PII), PHCs use cryptographic techniques like zero-knowledge proofs to verify humanness without revealing any personal details. This privacy-preserving approach is a significant driver for adoption, as it allows users to maintain anonymity while proving they are human. In an era where data privacy concerns are growing, PHCs offer a solution that balances security with user privacy.
Addressing Synthetic Content and Data Integrity: AI-generated synthetic content can degrade the quality of data used in machine learning models, leading to biased or inaccurate outputs. PHCs help filter out bot-generated data from human-generated data, improving the accuracy and fairness of AI systems. This is crucial for maintaining the integrity of training data used in AI models. Additionally, PHCs can help reduce the prevalence of synthetic content in digital spaces, preserving the quality of online interactions.
Decentralization and Avoidance of Centralized Control: PHCs are designed to be issued by multiple trusted entities (e.g., governments, institutions), reducing the risk of centralization and abuse of power by any single entity. This decentralized approach is appealing because it prevents concentration of control over digital identities and ensures that users have more autonomy over their credentials. The ability to issue credentials from various sources also supports broader adoption across different regions and sectors.
Regulatory and Ethical Considerations: The rise of AI-generated deception has prompted discussions among policymakers about how to regulate digital spaces effectively while preserving privacy and freedom of expression. PHCs offer a potential solution that aligns with regulatory goals by providing a secure method for verifying personhood without compromising user rights. Governments and organizations are increasingly recognizing the need for such tools to ensure safe and trustworthy online environments.
Growing Demand for Secure Online Interactions: As more services move online—ranging from financial transactions to healthcare—there is an increasing demand for secure identity verification methods that protect against fraud while maintaining user privacy. PHCs provide a scalable solution that can be integrated into existing digital identity systems to meet this demand. Early adoption is expected in sectors where secure identity verification is critical.
Mitigating Large-Scale Manipulation: PHCs enforce a “one-person, one-credential” policy, which limits the ability of bad actors to create multiple fake identities for large-scale attacks or manipulations (e.g., spreading disinformation or manipulating markets). This feature makes PHCs particularly valuable for preventing coordinated efforts by malicious actors to exploit digital platforms using AI-generated personas.
These factors make PHCs a compelling solution for addressing the emerging challenges in today’s increasingly digital world.
How it works
As a summary in their 2024 publication, the personhood credentials researchers from OpenAI, Harvard, Microsoft, Berkeley, MIT, a16z, Oxford, the American Enterprise Institute, among others offer a visual on how this whole process would work:
Figure 2 -Privacy-preserving enrollment and usage of personhood credentials (PHCs)[4]
First, there is an enrollment phase, the phase where humans contact an issuer, who gives out the personhood credential (one per person).
To receive the credential, the user must provide a ‘proof of humanhood,’ which could be as simple as appearing physically in a certain place to collect the credential or, in simple terms, taking any action that could not be possibly exercised unless you’re human.
Verification required by know your customer (KYC) regulations, employment onboarding, driver’s license application, even smart phone setup all provide opportunities for PHC enrollment.
Then, to access services, the user presents a zero-knowledge proof (ZK-proof) of their personhood credential to validate their humanity. The web service then verifies the ZK-proof of the personhood credential, confirming the user’s claim of humanity.
This flow reduces the impact of sock puppeting[5], mitigates bot attacks, and helps verify human control of agents.
Key Features of Personhood Credentials
Personhood Credentials (PHCs) are designed to verify that an individual is a real human, not an AI or bot. Below are the key features of PHCs:
Privacy-Preserving Verification: One of the most important features of PHCs is their ability to verify personhood without revealing personal information. Through cryptographic techniques like zero-knowledge proofs, PHCs allow users to prove they are human without disclosing sensitive details such as their name, address, or other identifying data. This ensures that users can maintain anonymity while still proving their authenticity.
Cryptographic Security: PHCs rely on strong cryptographic methods to ensure security. These credentials are difficult to forge or spoof because they are based on cryptographic proofs that AI systems cannot break. This makes PHCs highly resistant to manipulation by bots or AI-generated entities, ensuring robust verification of human identity.
Offline Verification Component: To obtain a PHC, there is typically an offline component where individuals must physically verify their identity through a trusted institution, such as a government office or another verified entity. This ensures that only real humans can acquire the credential, as AI systems cannot perform this offline step (e.g., showing up at the DMV).
Decentralized Issuance: PHCs are designed to be issued by multiple trusted entities, such as governments, banks, universities, or even tech companies like Apple and Google. This decentralized approach prevents any single entity from having too much control over the issuance process and ensures that users have multiple options for obtaining their credentials.
Unlinkable Pseudonymity: PHCs offer unlinkable pseudonymity, meaning that a user’s interactions across different services cannot be traced back to them or linked together, even if service providers collude. This protects user privacy by ensuring that their activities remain anonymous and untraceable across platforms.
One-Person, One-Credential Policy: PHCs enforce a strict one-person, one-credential policy, which helps prevent bad actors from creating multiple fake identities to carry out large-scale attacks or manipulations. This feature limits the scale of deceptive activity and ensures that each user is uniquely verified as a human.
Scalability and Efficiency: PHCs are designed to be scalable and efficient for widespread adoption across various online platforms and services. By leveraging cryptographic techniques and decentralized issuance models, PHCs can be integrated into existing digital infrastructures without compromising performance or user experience.
Optional Use: While PHCs provide a powerful tool for verifying human identity online, they can be optional for users depending on the service provider’s requirements. This flexibility allows individuals to choose when and where they want to use their personhood credentials based on the level of trust they seek in online interactions.
Personhood Credentials offer a privacy-preserving, secure way to verify human identity in digital spaces that AI cannot replicate. Their key features make them an effective solution for combating AI-generated deception while maintaining user privacy and autonomy online.
Differentiation from traditional digital identity solutions
Personhood Credentials (PHCs) differ from traditional digital identity solutions in several ways, particularly in how they balance privacy, security, and the verification of human identity. Below is a detailed comparison highlighting the main differences between Personhood Credentials and traditional digital identity systems.
| Personhood Credentials | Traditional Identity Solutions | |
| Purpose and focus | The primary goal of PHCs is to verify that an individual is a real human, not an AI or bot. PHCs are designed to combat issues like AI-generated content, fraud, and impersonation by ensuring that only real people can participate in online activities. They focus on proof of personhood rather than identity. | Identity systems are designed to verify an individual’s identity for various online services, often for regulatory compliance and risk management. They focus on identifying who the person is by collecting and verifying personal information. |
| Privacy and Anonymity | PHCs prioritize unlinkable pseudonymity, allowing users to prove they are human without revealing their actual identity. This means that users can interact with different service providers using a pseudonym that cannot be traced back to their real identity or linked across services—even if service providers collude. This ensures a high level of privacy while still verifying humanness. | These systems often require users to disclose significant amounts of personal information for verification purposes. While some digital identities use cryptography to secure data, they typically do not offer the same level of anonymity as PHCs. Traditional systems often store sensitive data in centralized databases, which can be vulnerable to breaches or misuse. |
| Verification Process | PHCs use cryptographic proofs (such as zero-knowledge proofs) to verify that a user is human without needing to disclose personal details. The verification process can be done offline initially (e.g., physical presence verification), but once issued, the credential can be used online without further disclosure of personal data. | These systems typically rely on centralized authorities (e.g., governments or financial institutions) to verify identities using physical documents like passports or biometric data (e.g., fingerprints or facial recognition). The verification process often involves sharing personal information with service providers, which may then store this data for future use. |
| Decentralization vs Centralization | PHCs are designed to be decentralized, meaning they can be issued by multiple trusted entities (such as governments, institutions, or organizations), reducing the risk of centralization and abuse of power. This approach also adds resiliency and integrity central solutions cannot provide. | These systems are often centralized, with a single source controlling the issuance and management of digital identities. This centralization can lead to concerns about surveillance and misuse of personal data. |
| Security | PHCs use advanced cryptographic techniques to ensure that credentials cannot be forged or tampered with. Since they do not store personal information centrally, they reduce the risk of data breaches and unauthorized access. | While these systems also use encryption and other security measures (e.g., multi-factor authentication), they often involve storing sensitive personal information in centralized databases. This makes them more vulnerable to hacking and data breaches. |
| Use Cases | PHCs are particularly useful in scenarios where proving humanness is more important than proving identity—such as combating AI-generated content, preventing bot activity on social media platforms, or ensuring that only real people participate in online voting or discussions. | These systems are widely used in scenarios where proving identity is crucial to comply with regulation or minimize risk—such as commercial transactions or accessing sensitive digital services. |
| Portability | PHCs are portable across different platforms while maintaining privacy through pseudonymity. Users can use the same credential across multiple services without revealing their identity or linking their activities across platforms. | While digital identities can also be portable across platforms (e.g., using a single sign-on system), they typically involve sharing personal information with each service provider. This increases the risk of data exposure and reduces privacy. |
Table 1 – The differences between PHCs and Traditional Identity Systems
Personhood Credentials are simply focused on proving what you are (human) rather than who you are. Traditional digital identities are more focused on verifying who someone is for regulatory compliance and risk management purposes and often involve sharing significant amounts of personal information with centralized sources. While both systems aim to enhance trust online, PHCs offer a more privacy-centric approach suited for combating AI deception and ensuring human authenticity in digital interactions.
What about Passkeys?
Passkeys and personhood credentials are both emerging authentication technologies aimed at improving online security and privacy, but they have some key differences:
| Passkeys | PHCs | |
| Purpose | Passkeys are designed to replace traditional passwords for logging into websites and apps. | PHCs aim to prove that a user is a real human being, not an AI or bot, without revealing personal information. |
| Authentication method | They use public key cryptography, with a private key stored on the user’s device and a public key on the server. | They also use cryptographic techniques but focus on proving “personhood” rather than account access. |
| User experience | Users authenticate using biometrics (like fingerprint or facial recognition) or device PINs. | The proposed system would involve obtaining credentials from trusted issuers, potentially requiring in-person verification. |
| Scope | Passkeys are specific to individual accounts on websites or apps. | PHCs are intended to be used across multiple platforms and services to prove human status. |
| Identity verification | They don’t necessarily verify a user’s real-world identity or “personhood.” | They involve some level of real-world identity verification to obtain the credential, though usage is designed to be privacy-preserving. |
Table 2 – The differences between passkeys and PHCs
While passkeys and personhood credentials share some similar goals in improving online security, they address different aspects of the authentication problem. Passkeys focus on secure account access, while PHCs aim to verify human status across the internet ecosystem. These technologies could potentially complement each other: passkeys could secure account access, while personhood credentials could prove human status across multiple platforms. While passkeys are already being adopted by major tech companies, personhood credentials still being developed with a focus on combating AI-based deception and bot activity.
Technological Foundations
Personhood Credentials (PHCs) are built on several advanced technologies to ensure privacy, security, and scalability in verifying that individuals are real humans. Three key technological foundations of PHCs include Blockchain/Distributed Ledger Technology (DLT), Verifiable Credentials Standards, and Advanced Cryptographic Techniques. These technical foundations have their roots in Decentralized Identity, and TechVision has published several reports, including two in 2024, “Digital Identity Wallets” and “Developing a Decentralized Identity Reference Architecture” outline these foundations in more detail. Below is a breakdown of how each of these technologies supports the concept of PHCs.
Blockchain and Distributed Ledger Technology (DLT)
Blockchain/DLT provide the underlying infrastructure for securely managing and verifying Personhood Credentials in a decentralized manner. DLT offers several advantages for PHCs:
Decentralization: Unlike traditional identity systems that rely on a centralized authority, DLT allows for multiple authoritative entities (governments, institutions) to issue personhood credentials into a decentralized network. This reduces the risk of centralization and prevents any single entity from controlling the system.
Distributed Economic Incentives: Every validator node securing the network gets paid in cryptocurrency to do so, generating economic incentives to protect and secure the entire network.
Immutable Recordkeeping: Blockchain ensures that once a credential is issued, its existence and integrity are recorded immutably on the ledger. This means that credentials cannot be tampered with or forged after issuance, ensuring trustworthiness in the system.
No Storage of Personal Data: One of the key benefits of using DLT for PHCs is that no personally identifiable information (PII) is stored on the blockchain itself. Instead, only cryptographic proofs or metadata about the credential are recorded, ensuring privacy while maintaining transparency.
Verification Without Issuer Involvement: Distributed ledgers allow verifiers to check the validity of a credential without needing to contact the issuer directly. This is achieved by publishing cryptographic material (e.g., public keys) on the ledger that can be used to verify signatures associated with the credential. This creates a trustless system where verifiers can independently confirm the authenticity of credentials.
Verifiable Credentials Standards
The World Wide Web Consortium (W3C)’s Verifiable Credentials (VC) standards provide a framework for issuing, holding, and verifying digital credentials in a secure and interoperable way. These standards are crucial for PHCs because they ensure consistency across different platforms and services:
Issuer Identification: The VC model ensures that each credential includes information about who issued it, allowing verifiers to trace its origin and trustworthiness. This is important for ensuring that personhood credentials come from legitimate issuers.
Holder Control: In line with privacy principles, verifiable credentials allow users (holders) to control their credentials via digital wallets. They can decide when and with whom to share their credentials without revealing more information than necessary. This aligns with the privacy-preserving goals of PHCs.
Interoperability: The W3C standards ensure that verifiable credentials can be used across different systems and platforms globally. This means that personhood credentials can be recognized by various online services, enhancing their utility and scalability.
Minimal Disclosure: Verifiable credentials support selective disclosure, meaning users can share only specific claims from their credential without revealing unnecessary personal data. For example, they can prove they are human without disclosing their name or other identifying information.
Advanced Cryptographic Techniques
PHCs employ advanced cryptographic techniques to ensure security, privacy, and scalability:
Zero-Knowledge Proofs (ZK-Proofs)
At the core of PHCs is the use of zero-knowledge proofs (ZK-proofs), a cryptographic technique that allows one party (the prover) to prove to another party (the verifier) that they possess certain information (in this case, proof of being human) without revealing any additional details about that information.
To generate a zero-knowledge proof from a personhood credential, the process involves several cryptographic steps that allow the credential holder to prove they possess a valid credential without revealing any specific information about their identity. Here’s an overview of how this works:
Credential Structure
First, it’s important to understand the structure of a personhood credential:
- The credential contains a standard set of verified attributes (claims) about the person (e.g., name, date of birth, unique identifier, etc.).
- It is cryptographically signed by a trusted issuer.
- The credential is stored securely on the holder’s device or in their digital wallet.
Zero-Knowledge Proof Generation
When the credential holder needs to prove their personhood to an online service:
- Selects relevant attributes: The holder chooses which attributes from their credential are necessary to prove they are human.
- Creates a cryptographic commitment: The holder generates a commitment to the selected attributes using a cryptographic hash function.
- Constructs the proof: Using advanced cryptographic techniques (such as zk-SNARKs or zk-STARKs), the holder creates a proof that:
- Demonstrates knowledge of the credential’s attributes
- Shows the attributes satisfy the required conditions
- Proves the credential is properly signed by a trusted issuer
- Generates auxiliary information: This includes public parameters needed for verification but doesn’t reveal the actual credential data.
Verification Process
When the online service receives the zero-knowledge proof:
- It verifies the cryptographic proof using the public parameters of the system.
- If the verification succeeds, the service gains confidence that the user possesses a valid personhood credential without learning any specific details about the user’s identity.
By using these advanced cryptographic techniques, personhood credentials can be converted into zero-knowledge proofs that provide strong privacy guarantees while still allowing for effective verification of a person’s attributes or status.
Asymmetric-Key Cryptography
PHCs also rely on asymmetric-key cryptography (a.k.a. PKI), where each user has a pair of cryptographic keys: a public key (shared openly) and a private key (kept secret). The public key is used by verifiers to confirm that the person presenting the credential is indeed its rightful holder. This method ensures secure communication between users and verifiers during credential presentation while protecting against unauthorized access or impersonation.
The trustworthiness and reliability of Personhood Credentials rest on a combination of blockchain/DLT, verifiable credentials standards, and advanced cryptographic techniques. Together, these technologies ensure that PHCs can provide secure, privacy-preserving verification of human identity while remaining scalable and interoperable across different platforms.
Integration with Existing Systems
The integration of Personhood Credentials (PHCs) into existing systems involves ensuring compatibility with current identity verification methods, incorporation into digital identity wallets, and interoperability across various platforms and services. Below is a detailed explanation of how PHCs can be integrated in these areas:
Compatibility with Mobile Identity Verification
PHCs are designed to be compatible with modern mobile identity verification systems, which are increasingly used for online authentication. Here’s how they achieve this:
Mobile-Friendly Cryptographic Proofs: PHCs leverage cryptographic techniques such as zero-knowledge proofs (ZK-proofs) that can be easily implemented on mobile devices. These proofs allow users to verify their personhood without revealing sensitive information, making them ideal for mobile environments where privacy and security are paramount.
Seamless Integration with Biometric Systems: Many mobile devices already use biometric verification (e.g., fingerprint or facial recognition) for identity authentication. PHCs can complement these systems by adding an extra layer of verification that proves the user is human, not a bot or AI. For example, a user could use their mobile device to present a PHC alongside biometric data to access secure services.
Offline and Online Components: Mobile identity verification often includes both online and offline elements. PHCs can integrate with this model by requiring an initial offline verification (e.g., in-person proof at a government office) before issuing a digital credential that can be used online via mobile devices.
Incorporation into Digital Identity Wallets
PHCs can be easily incorporated into digital identity wallets, which are becoming a standard tool for managing digital credentials. Digital wallets provide a secure and convenient way for users to store and present their credentials across multiple platforms.
Verifiable Credentials Standards: PHCs align with the W3C Verifiable Credentials (VC) standards, which are widely used in digital identity wallets. This ensures that PHCs can be stored, managed, and presented through existing wallet solutions without requiring significant changes to the underlying infrastructure.
Selective Disclosure: Digital identity wallets often support selective disclosure, allowing users to share only specific pieces of information from their credentials. PHCs enhance this capability by enabling users to prove they are human without revealing any additional personal details. For example, when interacting with a service provider, the wallet can present only the fact that the user holds a valid personhood credential, preserving privacy.
User Control and Privacy: Digital wallets give users full control over their credentials, allowing them to decide when and where to use their PHC. This aligns with the privacy-preserving nature of PHCs, which prioritize user autonomy and ensure that credentials cannot be linked across different services.
Refer to our report “Digital Identity Wallets” for our latest take on the development of these wallet capabilities.
Interoperability Across Different Platforms and Services
For PHCs to be effective on a global scale, they must be interoperable across various platforms and services. This is achieved through several mechanisms:
Decentralized Issuance and Verification: One of the key features of PHCs is that they can be issued by multiple trusted entities (e.g., governments, institutions). This decentralized approach ensures that credentials are recognized across different platforms without relying on a single central authority. By using decentralized identity standards like verifiable credentials, PHCs can function seamlessly across different ecosystems.
Cross-Platform Compatibility: The use of standardized cryptographic protocols ensures that PHCs can be verified by any service provider that supports these standards. This means that whether a user is interacting with an eCommerce platform, social media site, or government service, they can present their personhood credential in a way that is universally recognized.
Global Standards for Interoperability: Researchers and technologists are advocating for the development of global standards to ensure that PHCs can be adopted widely across different regions and industries. By aligning with existing frameworks like decentralized identifiers (DIDs) and verifiable credentials, PHCs can integrate smoothly into various systems while maintaining high levels of security and privacy.
The integration of Personhood Credentials into existing systems ensures that PHCs can provide secure, privacy-preserving human verification in a scalable and user-friendly manner across diverse digital environments.
Artificial Intelligence, Machine Learning and Personhood
Artificial Intelligence (AI) and Machine Learning (ML) can significantly enhance the use of Personhood Credentials (PHCs) in an enterprise setting by improving the security, efficiency, and scalability of human verification processes while maintaining privacy. Here’s how AI and ML can contribute:
Enhanced Fraud Detection and Prevention: AI and ML algorithms can analyze patterns in credential usage to detect anomalies or suspicious behavior that may indicate fraud or misuse. For example, AI could flag instances where a PHC is being used in multiple locations simultaneously or identify attempts to bypass the system with AI-generated content. This would strengthen the integrity of PHCs by ensuring that only legitimate users are granted access to enterprise systems.
Automated Verification Processes: AI-powered systems can streamline the issuance and validation of PHCs by automating identity verification tasks, such as biometric checks or zero-knowledge proof verifications. This reduces the need for manual intervention, speeding up the process while minimizing errors. ML models can also improve over time by learning from previous verification attempts, making the process more efficient.
Scalability for Large Enterprises: Enterprises often must manage a large number of users across different platforms. AI can help scale PHC systems by automating routine tasks like credential issuance, revocation, and renewal. This allows enterprises to handle high volumes of users without compromising security or performance.
Adaptive Security Measures: ML algorithms can dynamically adjust security protocols based on real-time threat intelligence. For instance, if a particular region or industry is experiencing increased bot activity, AI could trigger stricter verification measures for PHC holders in those areas, ensuring that enterprises remain protected against evolving threats.
Data Integrity and Privacy Preservation: AI systems can assist in ensuring that PHCs are used in a privacy-preserving manner by enforcing cryptographic techniques like zero-knowledge proofs. This ensures that while verifying personhood, no personal data is exposed or stored unnecessarily. AI can also help monitor compliance with privacy regulations, alerting enterprises if any data handling practices deviate from established protocols.
Integrating AI, ML, and PHC capabilities allows enterprises to enhance security, automate processes, and scale operations while maintaining user privacy and trust.
Privacy and Security Considerations
Personhood Credentials (PHCs) are designed to balance privacy and security while verifying real humanity online. This raises several important privacy and security considerations, particularly in terms of balancing anonymity and accountability, protecting against credential theft or transfer, and ensuring compliance with data protection regulations like the General Data Protection Regulation (GDPR). Below is an exploration of these considerations.
Balancing Anonymity and Accountability
One of the key challenges for PHCs is balancing the need for anonymity with accountability in online interactions. PHCs aim to provide a way to prove that a user is a unique human without revealing personal information, which is crucial for maintaining privacy in digital spaces.
Anonymity through Pseudonymity: PHCs use unlinkable pseudonymity, meaning users can interact with services anonymously through service-specific pseudonyms. This ensures that their activities cannot be traced back to their real identity or linked across different platforms, even if service providers or issuers collude. This feature is crucial for protecting user privacy while still verifying personhood.
Accountability Without Identity Disclosure: While PHCs allow for anonymous interactions, they also ensure accountability by proving that each user is a real human. This is achieved using zero-knowledge proofs (ZK-proofs), which allow users to prove they hold a valid credential without revealing any personal information. This balance ensures that users can participate in online environments without being tracked, but still be held accountable as real humans.
One-Person, One-Credential Policy: To prevent abuse, issuers of PHCs enforce a strict one-person, one-credential policy. This ensures accountability by preventing users from creating multiple fake identities to manipulate systems or engage in fraudulent activities. However, this does not compromise anonymity since the credential itself does not reveal personal information.
Protection Against Credential Theft or Transfer
Ensuring that PHCs are secure from theft or unauthorized transfer is critical for maintaining trust in the system. Several mechanisms are employed to protect against these risks:
Regular Re-authentication and Expiry: To mitigate the risk of credential theft or transfer, PHCs often include mechanisms for regular re-authentication or credential expiry. This ensures that only the original holder can continue using the credential over time. If a credential is stolen or compromised, it will eventually expire or require re-verification to remain valid.
Cryptographic Security: PHCs rely on advanced cryptographic techniques like asymmetric-key cryptography and ZK-proofs to ensure that credentials cannot be forged or tampered with. These techniques make it extremely difficult for attackers to steal or misuse credentials without detection.
Minimal Data Storage During Enrollment: During the enrollment phase, only minimal identifying information is stored by the issuer. This reduces the risk of sensitive data being exposed in case of a breach. Additionally, because PHCs do not store personal information like names or addresses on the blockchain (or other distributed ledgers), even if an attacker gains access to the system, they cannot extract meaningful personal data.
Compliance with Data Protection Regulations (e.g., GDPR)
PHC systems must comply with stringent data protection regulations like the General Data Protection Regulation (GDPR) in Europe, which sets high standards for privacy and data security.
Data Minimization: One of the core principles of GDPR is data minimization—only collecting and processing the minimum amount of personal data necessary for a given purpose. PHCs align well with this principle by using cryptographic techniques like ZK-proofs to verify personhood without collecting personally identifiable information (PII). This ensures that only minimal data is processed during both enrollment and credential usage.
User Control Over Data: GDPR emphasizes giving users control over their personal data. With PHCs, users maintain full control over their credentials through digital wallets. They can choose when and where to present their credentials without disclosing unnecessary information. This aligns with GDPR’s focus on user consent and control over personal data.
Right to Be Forgotten: Under GDPR, individuals have the right to request deletion of their personal data. Since PHCs store minimal personal information during enrollment and do not link user activity across services, they inherently support this principle by minimizing stored data that could be subject to deletion requests.
Data Security Measures: GDPR requires organizations to implement strong security measures to protect personal data from breaches or unauthorized access. The use of cryptographic methods in PHC systems provides robust protection against such risks, ensuring compliance with GDPR’s security requirements.
The privacy and security considerations surrounding Personhood Credentials are crucial for their successful implementation. By balancing anonymity with accountability, PHCs ensure privacy while maintaining trust in online interactions. Additionally, mechanisms like regular re-authentication protect against credential theft or transfer, while minimal data storage and cryptographic security ensure compliance with regulations like GDPR. These features make PHCs a promising solution for verifying human identity in an increasingly AI-driven digital world.
Potential Applications
Personhood Credentials (PHCs) have the potential to revolutionize various digital environments by providing a privacy-preserving way to verify human identity. They can be applied across multiple sectors, including social media, e-commerce, digital services, and voting systems. What follows is a detailed description of the potential applications of PHCs in these areas.
Social Media Verification
One of the most pressing challenges on social media platforms is the proliferation of bots, fake accounts, and AI-generated content. PHCs can help address this by ensuring that only real humans are participating in online discussions and content creation.
Preventing Bot Activity: PHCs can be used to verify that users on social media platforms are real people, not bots or AI-generated personas. This would allow platforms to filter out non-verified accounts, reducing the spread of misinformation and spam.
Enhanced Trust: Users could choose to interact only with other verified humans, improving trust in online conversations. For example, social media platforms could offer filters that allow users to see only content created by verified humans, thereby reducing the influence of fake accounts and AI-generated posts.
Combatting Misinformation: By ensuring that only human users can create and share content, PHCs could help reduce the spread of misinformation and disinformation campaigns driven by bots or malicious actors using AI-generated profiles.
E-commerce and Online Transactions
In e-commerce, trust between buyers and sellers is crucial. PHCs can enhance security and trust by verifying that both parties in a transaction are real humans.
Fraud Prevention: One of the key benefits of PHCs in e-commerce is their ability to prevent fraud. By verifying that customers are real people, e-commerce platforms can reduce the risk of fraudulent transactions conducted by bots or stolen identities. This would be particularly useful in industries where trust is critical, such as financial services and online retail.
Account Takeover Protection: PHCs can add an extra layer of security to user accounts, making it harder for attackers to take over accounts using stolen credentials. This would help reduce identity theft and account hijacking incidents.
Improved Customer Confidence: By ensuring that both buyers and sellers are verified as real people, PHCs can boost consumer confidence in online transactions. This could lead to increased adoption of e-commerce services as customers feel more secure making purchases online.
Access to Digital Services and Platforms
Digital services—ranging from entertainment platforms to government services—can benefit from PHCs by ensuring that only legitimate users access their systems.
Access Control: PHCs can be used as a form of access control for digital services, ensuring that only verified humans can use certain features or access sensitive information. For example, streaming platforms could use PHCs to verify subscribers’ identities without collecting personal data.
Reduced Abuse in Online Communities: Many digital services face challenges with abusive behavior from anonymous users or bots. By requiring personhood verification for participation in forums or community spaces, service providers could create safer environments for users.
Simplified Onboarding: For new users signing up for digital services, PHCs could streamline the onboarding process by providing a quick way to verify their humanness without requiring extensive personal information or documentation.
Challenges and Limitations
Personhood Credentials (PHCs) offer a promising solution for verifying human identity online, but they also face several challenges and limitations. Below is a detailed description of these challenges.
Scalability and Widespread Adoption
One of the most significant challenges for PHCs is achieving scalability and widespread adoption across platforms, governments, and digital services.
Resistance from Platforms and Governments: For PHCs to be effective, they need to be universally adopted by a wide range of stakeholders, including social media platforms, eCommerce sites, governments, and other digital service providers. However, many entities may be reluctant to adopt a system they do not control or fully understand. As noted by experts, platforms may resist conforming to standards that are externally imposed or not aligned with their proprietary systems. Governments may also be slow to adopt such technologies due to bureaucratic inertia or concerns about centralizing too much control over digital identities.
Global Standardization Issues: Achieving global standardization is another hurdle. For PHCs to function effectively across borders, there needs to be consensus on technical standards and governance frameworks. This requires cooperation between governments, companies, and standards bodies, which can be difficult to achieve given the varying regulatory environments and priorities across different regions. Our work with Digital Wallets in Europe underscores this issue.
Infrastructure Requirements: The infrastructure needed to support PHCs—such as cryptographic verification systems, decentralized ledgers, and physical verification points—must be robust enough to handle large-scale operations. This could be a barrier in regions with limited technological infrastructure or where access to verification centers is restricted.
User Education and Acceptance
Like the challenge Decentralized Identity solutions are facing, PHCs have a major challenge is ensuring that users understand their purpose and accept them as part of their online interactions. That challenge includes the following:
Complexity of Cryptographic Concepts: The underlying technology behind PHCs—such as zero-knowledge proofs (ZK-proofs) and decentralized identity systems—can be complex for the average user to understand. Educating users about how these credentials work without overwhelming them with technical jargon will be critical for widespread adoption. Users need to trust that their privacy is protected while still understanding how PHCs verify their humanity without revealing personal information.
Trust in Issuers: Users must trust the entities issuing PHCs (e.g., governments or private organizations). If there is skepticism about the trustworthiness of these issuers—whether due to past data breaches or concerns about surveillance—users may hesitate to adopt PHCs. Building trust will require transparent governance structures and clear communication about how personal data is handled.
User Convenience: While PHCs offer privacy-preserving benefits, they may introduce friction into online interactions. For example, requiring users to physically visit a verification center or regularly re-authenticate could be seen as burdensome. Ensuring that the process is as seamless as possible will be crucial for user acceptance.
Potential for Exclusion or Discrimination
PHCs also raise concerns about the potential for exclusion or discrimination if not implemented carefully.
Access Inequality: Not everyone may have equal access to the infrastructure required to obtain a personhood credential. For example, individuals in rural areas or underdeveloped regions may struggle to access physical verification centers where credentials are issued. Additionally, marginalized groups who face barriers in accessing government services (e.g., refugees or undocumented individuals) may find it difficult or impossible to obtain a credential.
Sociopolitical Risks: In some countries with authoritarian regimes or restrictive policies, requiring citizens to obtain personhood credentials from government entities could lead to surveillance or suppression of free speech. If only certain entities are allowed to issue credentials, this could centralize power in ways that disadvantage certain populations.
Discrimination in Digital Spaces: There is also a risk that PHCs could create a two-tiered internet where only those with credentials can access certain services or participate in online discussions. This could lead to further exclusion of vulnerable populations who are unable—or unwilling—to obtain such credentials. For instance, platforms might restrict access only to verified users, limiting uncredentialed individuals’ digital participation.
The challenges facing Personhood Credentials are significant but not insurmountable. Achieving scalability will require cooperation between governments, platforms, and service providers on a global scale. User education will be key in ensuring that people understand and trust the technology behind PHCs, while minimizing friction in the user experience. Finally, careful consideration must be given to ensuring that PHCs do not exacerbate inequality or discrimination by excluding vulnerable populations from digital spaces. Addressing these challenges will be critical for the successful implementation of PHCs as a solution for verifying human identity online.
Future Developments
Personhood Credentials are a new concept and future development of PHCs will be influenced by ongoing efforts in standardization, integration with emerging technologies, and the potential for creating global, interoperable systems.
Standardization Efforts
Standardization is critical for ensuring that PHCs can be widely adopted and interoperable across different platforms, services, and jurisdictions. Several key initiatives are driving this forward:
Verifiable Credentials (VC) Standards: PHCs are closely aligned with the W3C Verifiable Credentials (VC) standards, which provide a framework for issuing, holding, and verifying digital credentials in a secure and interoperable manner. These standards ensure that PHCs can be used across various platforms while maintaining privacy and security. By adhering to VC standards, PHCs can be integrated into existing digital identity ecosystems without requiring significant changes to infrastructure.
Decentralized Identity Organizations: Organizations such as the Decentralized Identity Foundation (DIF) are working to develop privacy-preserving digital identity solutions that align with the principles of decentralization and user control. DIF’s work on Proof of Personhood and Credential Schemas directly supports the development of PHCs by addressing interoperability challenges and ensuring that PHCs can function within decentralized ecosystems. Other organizations, such as the Trust Over IP foundation should take note.
NIST Identity Assurance Levels (IALs): In the U.S., frameworks like NIST’s Identity Assurance Levels (IAL2 and IAL3) are widely used for identity verification in sectors like healthcare and finance. These frameworks could influence how PHCs are standardized, particularly in terms of verifying the authenticity of identity evidence while minimizing the collection of personal data. Aligning PHCs with such standards could help ensure regulatory compliance and foster adoption by government agencies.
Challenges in Standardization
Achieving global standardization requires cooperation between governments, companies, and international organizations. Different regions may have varying regulations and privacy laws (e.g., GDPR), which could complicate efforts to create a unified standard for PHCs.
Ensuring that PHCs remain interoperable across multiple issuers while maintaining privacy protections (e.g., unlinkability between services) is a complex challenge that will require ongoing collaboration between technologists and policymakers.
Integration with Emerging Technologies
As technology evolves, PHCs will need to integrate with new tools and systems to remain secure and effective. Two key areas where emerging technologies will play a role are quantum-resistant cryptography and biometric verification.
Quantum-Resistant Cryptography: As quantum computing advances, traditional cryptographic methods may become vulnerable to attacks. To future-proof PHC systems, there is growing interest in integrating quantum-resistant cryptographic algorithms. These algorithms would ensure that even if quantum computers become capable of breaking current encryption methods, PHC systems remain secure. This is particularly important given the long-term nature of digital credentials, which may need to remain secure for decades.
Biometric Verification: While PHCs aim to minimize the use of personal data, biometric verification (e.g., fingerprints or facial recognition) could still play a role in ensuring that credentials are tied to real individuals. However, this introduces challenges related to privacy, bias in biometric systems, and the integrity of hardware used for biometric collection. Advances in biometric technology—such as more accurate liveness detection—could help address these concerns while enhancing the security of PHC issuance.
Blockchain Technology: Blockchain or other forms of Distributed Ledger Technology (DLT) can be used to securely manage the issuance and verification of PHCs in a decentralized manner. Blockchain ensures transparency and immutability without storing sensitive personal data on-chain. This integration allows for decentralized verification processes where no single entity has control over all credentials.
Challenges in Integration
Ensuring that quantum-resistant cryptography is implemented without compromising performance or user experience will be a key challenge as quantum computing becomes more feasible.
The use of biometrics must be carefully managed to avoid privacy violations or biases against certain demographic groups, especially since biometric data is highly sensitive.
DLTs have their adoption issues, including cost, scaling, and performance. Working to overcome these issues will help the integrity and resiliency of the PHC infrastructure.
Potential for Global, Interoperable PHC Systems
The goal for PHC development is to create a global system that allows for seamless interoperability across platforms, services, and jurisdictions while maintaining strong privacy protections.
Multi-Issuer Ecosystem: A global system would likely involve multiple trusted issuers (e.g., governments, private institutions) providing personhood credentials within a decentralized framework. This ensures that no single entity has control over all credentials while giving users flexibility in choosing their preferred issuer based on trust or convenience. This approach also mitigates risks associated with centralization by distributing power across multiple entities.
Interoperability Across Platforms: For PHCs to reach their full potential, they must be interoperable across various platforms—social media networks, eCommerce sites, government services—without requiring users to obtain separate credentials for each service. The use of standardized protocols like W3C Verifiable Credentials ensures that credentials issued by one entity can be verified by another without compromising security or privacy.
Cross-Border Recognition: A global PHC system would need to account for differing regulatory environments across countries. For example, compliance with data protection regulations like GDPR in Europe or CCPA in California will be essential for ensuring user trust. Governments would need to collaborate on establishing mutual recognition agreements so that credentials issued in one country can be recognized globally.
Challenges in Global Interoperability
Achieving cross-border recognition will require significant coordination between governments and international organizations. Differences in privacy laws and regulatory frameworks could slow down adoption.
Ensuring equitable access to personhood credentials globally is another challenge. In regions with limited infrastructure or under authoritarian regimes, individuals may face barriers in obtaining credentials or risk surveillance by their governments
The future development of Personhood Credentials hinges on efforts toward standardization, integration with emerging technologies like quantum-resistant cryptography, and creating globally interoperable systems. Standardization efforts led by organizations such as W3C and DIF will ensure interoperability across platforms, while technological advancements will future-proof these systems against evolving threats. However, achieving global adoption will require overcoming challenges related to regulatory compliance, cross-border recognition, and ensuring equitable access for all users.
Different approaches to personhood credentials
While this report focuses on PHCs, there are other efforts underway to solve the problem of personhood. Chief among these are Idena and the World Network.
Idena
Idena is a decentralized, open-source blockchain project that was initiated in October 2018. It is unique in its focus on creating proof of personhood, which ensures that each participant in the network is a real human and not an AI or bot. The system operates without collecting personal information, using a novel consensus mechanism called Proof-of-Person (PoP) to validate the humanness and uniqueness of participants.
Since its inception in 2018, Idena has pioneered the concept of Proof-of-Personhood through its innovative use of validation sessions and crypto identities. By ensuring that each participant is a real human with equal voting power, Idena provides a decentralized solution for identity verification that is privacy-preserving, inclusive, and resistant to Sybil attacks. Its native cryptocurrency iDNA powers various use cases within the network, ranging from governance to decentralized applications like universal basic income (UBI) distribution and censorship-free publishing.
World Network
World Network, originally called Worldcoin, is a cryptocurrency and digital identity project co-founded by Sam Altman, CEO of OpenAI, along with Alex Blania and Max Novendstern in 2019. The project aims to create a global, decentralized identity and financial network by using biometric data, specifically iris scans, to verify the humanness and uniqueness of individuals. Below is a detailed history of the World Network:
The network’s ecosystem revolves around three main components:
- World ID: A unique digital identity created through an iris scan using the Orb device. This ID is stored on a decentralized blockchain and is designed to prove that a person is human without requiring personal information like names or email addresses.
- World App: A mobile application that serves as a wallet for holding WLD tokens and other digital assets. It also stores users’ credentials and allows them to use their World ID for various online services.
- WLD Token: Worldcoin’s native cryptocurrency token used within its ecosystem for payments, transfers, and other transactions.
World Network aims to create a global financial network based on proof of personhood that can be used for various applications beyond cryptocurrency. Potential use cases include secure online voting systems (“one person, one vote”), financial transactions without fraud or duplication, remittances, website logins without passwords, and even facilitating Universal Basic Income (UBI)
The network’s history reflects both innovation and controversy since its founding in 2019 by Sam Altman and his team at Tools for Humanity. While it aims to solve critical issues related to identity verification in an AI-dominated world through its biometric-based proof-of-personhood system, it has faced significant backlash over privacy concerns and regulatory hurdles worldwide. As it continues expanding globally under its new branding as “World Network,” it must address these challenges if it hopes to achieve widespread adoption as a decentralized identity solution.
Personhood Credentials, Idena, and World Network are all designed to address the growing challenge of distinguishing real humans from AI systems online, but they differ in their approaches, technologies, and privacy implications. The table below outlines these differences.
| Feature | Personhood Credentials | Idena | World Network |
| Verification Method | Offline physical verification (e.g., in-person with ID) combined with cryptographic proofs | Solving time-bound puzzles that are difficult for bots. | Biometric iris scanning via a device called “The Orb” |
| Privacy Focus | High: Uses zero-knowledge proofs to verify humanness without revealing identity or personal data. | Moderate: No biometric data collected but relies on solving puzzles that may link users to specific behaviors. | Low: Collects biometric data (iris scans), though claims to delete raw images after creating a unique code. |
| Decentralization | Decentralized: Multiple trusted issuers (governments, institutions) can issue credentials. | Decentralized blockchain-based system. | Centralized around World Network’s infrastructure and hardware (The Orb). |
| Scalability | Potentially global if adopted by multiple governments and institutions. | Scalable within the blockchain community but limited by puzzle-solving requirements. | Global reach with operations in over 100 cities, but reliant on physical hardware for biometric scans. |
| Security | High: Cryptographically secure and resistant to AI forgery due to offline verification and cryptographic protections. | Moderate: Puzzle-solving is effective against bots but may not scale well against advanced AI systems. | High: Biometric verification is difficult to forge, but concerns exist over biometric data misuse. |
| User Experience | Requires physical presence for credential issuance but is seamless online due to cryptographic proofs. | Requires periodic participation in puzzle-solving sessions, which might be inconvenient for some users. | Requires users to visit locations for iris scans and use a dedicated app for verification and transactions. |
| Adoption Challenges | Requires cooperation from multiple governments and institutions; potential equity issues in access to credentials. | Limited to users who are willing to participate in puzzle-solving; may not appeal to broader audiences. | Faces regulatory scrutiny over privacy concerns and potential exploitation of vulnerable populations. |
Table 3 – Different approaches to Personhood
While all three approaches—Personhood Credentials, Idena, and World Network—aim to solve the problem of distinguishing humans from AI online, they do so through different methods with varying trade-offs between privacy, security, scalability, and accessibility. Personhood Credentials offer a balanced approach with strong privacy protections through cryptographic proofs but face challenges in adoption. Idena provides a decentralized solution but may struggle with scalability as AI improves. World Network offers robust security through biometrics but raises significant privacy concerns due to its collection of sensitive biometric data and its ties to its own cryptocurrency.
Conclusion
Personhood Credentials (PHCs) have the potential to significantly reshape the digital identity landscape by offering a privacy-preserving and decentralized method for verifying human identity. As AI-generated content becomes more sophisticated, the need for a reliable way to distinguish between humans and AI entities is becoming more critical. PHCs provide a solution by ensuring that only real people can participate in online interactions, mitigating the risks of AI-driven deception, such as fake accounts, misinformation, and fraud. This shift toward decentralized identity verification could reduce reliance on centralized authorities and enhance user privacy across digital platforms.
Personhood credentials are still being developed, but that doesn’t mean that you shouldn’t start planning and preparing. To get ready for the adoption and integration of Personhood Credentials (PHCs), enterprises should focus on several areas to ensure a smooth transition and harness the benefits of this emerging technology. Here’s a breakdown of what companies can do:
Understand the Technology and Its Benefits
- Become Familiar with PHC Concepts: Enterprises need to understand how PHCs work, particularly their ability to verify humanness without revealing personal data. PHCs use cryptographic methods like zero-knowledge proofs to confirm that users are real humans while preserving privacy, making them ideal for combating AI-driven deception (e.g., bots, fake accounts) in digital spaces.
- Evaluate Use Cases: Identify areas where PHCs can add value, such as enhancing trust in social media interactions, improving security in e-commerce transactions, or ensuring authenticity in digital services like online collaboration or content creation.
Integration with Existing Systems
- Assess Compatibility with Current Identity Solutions: Companies should evaluate how PHCs can be integrated with their existing identity and access systems. Since PHCs focus on proving humanness rather than identity, they complement traditional identity systems by adding an extra layer of security without requiring personal data disclosure.
- Incorporate into Digital Wallets: Companies offering digital wallets or identity management solutions should explore integrating PHCs as a form of digital credential. This could allow users to store and present their PHC alongside other forms of identification, providing a seamless experience when interacting with services that require proof of personhood.
Invest in Infrastructure and Scalability
- Prepare for Decentralized Issuance: PHCs are designed to be issued by multiple trusted entities (e.g., governments, banks, tech companies), so companies should consider becoming issuers or partnering with trusted issuers. This decentralized approach reduces the risks associated with centralized control over digital identities.
- Ensure Scalability: As PHCs gain wider adoption, companies need to ensure that their systems can handle the increased demand for verification requests. This includes investing in infrastructure that supports cryptographic verification methods like zero-knowledge proofs and ensuring that these processes do not compromise user experience.
Address Privacy and Security Concerns
- Prioritize Privacy: One of the key advantages of PHCs is their privacy-preserving nature. Companies should ensure that they implement PHC systems in ways that respect user privacy, such as minimizing data collection during enrollment and using pseudonymous credentials that cannot be linked across services.
- Mitigate Credential Theft Risks: Companies must implement security measures to prevent credential theft or misuse. This could involve regular re-authentication processes or setting expiration dates for credentials to ensure that only legitimate users retain access over time.
Educate Users and Build Trust
- User Education: Since PHCs are a relatively new concept, companies must invest in educating their users about how these credentials work and the benefits they offer (e.g., enhanced privacy, protection against bots). Clear communication will help build trust and encourage adoption.
- Transparency in Data Handling: To foster user confidence, companies should be transparent about how they handle data related to PHC issuance and verification. Ensuring compliance with data protection regulations like GDPR will be critical for maintaining trust.
Ensure Compliance with Regulations
- Adhere to Data Protection Laws: Given the privacy concerns surrounding digital identities, companies must ensure that their use of PHCs complies with relevant data protection regulations such as GDPR. This includes ensuring that personal data is not stored unnecessarily and that users have control over how their credentials are used.
- Monitor Regulatory Developments: As governments around the world begin to regulate AI-generated content and digital identity systems more closely, companies should stay informed about evolving legal frameworks related to personhood verification and AI deception prevention.
Encourage Further Research and Development
- Invest in Innovation: Companies should actively contribute to the development of PHC technologies by investing in research and collaborating with standards bodies like W3C and the Decentralized Identity Foundation (DIF) to refine cryptographic methods, improve scalability, and enhance interoperability across platforms.
- Pilot Programs: Launch pilot programs to test the effectiveness of PHCs in real-world scenarios before full-scale implementation. This will allow companies to identify potential challenges and optimize their systems accordingly.
To prepare for the adoption of Personhood Credentials (PHCs), enterprises must focus on understanding these key areas. By taking these steps, companies can position themselves at the forefront of digital identity innovation while enhancing online trust and security in an increasingly AI-driven world. Being unprepared will eventually lead to bad outcomes.
About TechVision
World-class research requires world-class consulting analysts, and our team is just that. Gaining value from research also means having access to research. All TechVision Research licenses are enterprise licenses; this means everyone that needs access to content can have access to content. We know major technology initiatives involve many different skills across an organization and limiting content to a few can compromise the effectiveness of the team and the success of the initiative. Our research leverages our team’s in-depth knowledge as well as their real-world consulting experience. We combine great analyst skills with real world client experiences to provide a deep and balanced perspective.
TechVision Consulting builds off our research with specific projects to help organizations better understand, architect, select, build, and deploy infrastructure technologies. Our well-rounded experience and strong analytical skills help us separate the “hype” from the reality. This provides organizations with a deeper understanding of the full scope of vendor capabilities, product life cycles, and a basis for making more informed decisions. We also support vendors in areas such as product and strategy reviews and assessments, requirement analysis, target market assessment, technology trend analysis, go-to-market plan assessment, and gap analysis.
TechVision Updates will provide regular updates on the latest developments with respect to the issues addressed in this report.
About the Author
 Gary Zimmerman is an experienced executive known for helping companies deliver new offers and expand markets. Accomplishments include launching four companies, 20+ products, building high-performance organizations, and generating millions in sales.
Gary Zimmerman is an experienced executive known for helping companies deliver new offers and expand markets. Accomplishments include launching four companies, 20+ products, building high-performance organizations, and generating millions in sales.
His experience at Neustar, Respect Network, and Sovrin allows him to provide a broad perspective on a variety of subjects including self-sovereign identity, blockchain, enterprise data management, and the data brokerage industry. His experience in both enterprise and startup product development gives him a unique perspective on the application of new technologies.
[1] https://www.mckinsey.com/capabilities/quantumblack/our-insights/the-state-of-ai
[2] https://www.pwc.com/us/en/tech-effect/ai-analytics/ai-predictions.html
[3] https://arxiv.org/pdf/2408.07892
[4] https://arxiv.org/pdf/2408.07892
[5] Sock puppetry refers to the act of creating and using false online identities to deceive others, usually for manipulative purposes. This practice involves a single individual controlling multiple accounts to create the illusion of independent voices supporting or opposing a particular person, organization, or viewpoint.