Developing a Customer IAM (CIAM)Strategy and Roadmap
Initial Publication Date: 29 July 2020
Abstract
This is the third report TechVision has released on the topic of Customer Identity and Access Management (CIAM). In our report three years ago, we characterized CIAM as an “emerging” category. Eighteen months ago, we declared that CIAM had “emerged”, but now we see CIAM as maturing. We find that most large enterprises are leveraging CIAM in some way, major vendors (such as Akamai and SAP) have acquired early CIAM leaders (Janrain and Gigya) and other vendors (Okta and Ping) achieving successful IPOs.
CIAM is important and highly visible as it provides organizations with a public gateway to secure external engagement and is a critical element of any Digital Enterprise program. CIAM is often an organization’s first “touch point” with a prospect and an on-going reflection of a brand. The CIAMstakes are high; get it right and you’ll attract customers, drive revenue and positively represent your organization; get it wrong and your business/image will suffer.
This report offers recommended customer-centric IAM strategies, architectural approaches and pragmatic, experience-based advice. CIAM differs from traditional (internal enterprise-focused) IAM with a greater emphasis on user experience, privacy and consent management, increased scale,integration with CRM/marketing systems and a business/sales focus.
This report provides strategic and tactical recommendations for enterprises building an IAM foundation for customer/prospective customer engagement and external stakeholders in the context of business goals. This report covers:
- The enterprise CIAM value proposition, core requirements and business rationale
- Developing a CIAM strategy and action plan
- The CIAM market and vendor short list
- Recommendations and next steps
Authors:
| Gary Rowe | CEO & Principal ConsultingAnalyst [email protected] |
| Doug Simmons | Principal Consulting Analyst [email protected] |
Executive Summary
Customer IAM (CIAM) is an area every large organization should be paying attention to. It is one of the mostimportant foundational areas organizations should be investing in to prepare to become a truly Digital Enterprise. This IAM category is rapidly evolving and is critical to building trusted customer relationships and providing requisite security and privacy protection. Enterprises are architecting customer-centric IAM solutions and vendors are developing CIAM services that are differentiated from traditional Enterprise IAM solutions.
TechVision Research recommends the use of CIAM-centric, cloud-enabled services as opposed to simply fine-tuning traditional enterprise-centric IAM products and services—at least in the short-to-intermediate term. CIAM is particularly adept at supporting key Sales and Marketing objectives including enticing and engaging prospective customers, better serving and retaining current customers and establishing trusted, secure and sustainable relationships. For example, in TechVision’s recent report on the Digital Trust we describe CIAM as a core part of establishing Mechanical Trust.
A CIAM program, properly executed, is a conduit towards building lifetime digital customer relationships. Establishing trusted connections and building relationships that generate useful data and can be served by better customer knowledge are keys to digital business success. These digital relationships can be maintained and enhancedover time with a steady flow of updated contextual and progressive profiling-generated information that drives personalized customer offerings and improves business decisions.
CIAM is different than many infrastructure technologies in that the business benefits are so directly visible and impactful. In many cases the customer engagement process can make or break a lifetime relationship; get CIAM right and you can build a strong digital presence and business results; get it wrong and your competitive advantage can be forever lost.
In building a CIAM program, organizations should start by focusing on the customer experience and how CIAM can support the evolution of this experience throughout the suspect/prospect/customer lifecycle. Relationships to be managed may be initiated by anonymous users investigating your website and grow as offers are responded to and trust is built up. During this process data is aggregated and customer profile information naturally evolves throughoutthe lifetime of the relationship. This method of gaining customer insights as the customer journey evolves ischaracterized as progressive profiling and a key part of a strong CIAM offering.
CIAM is different in many ways from traditional IAM. The major focus within CIAM is on the customer – with an emphasis on minimizing friction and enticing engagement. This is different from employee-facing IAM in that employees are generally required to use the system as a condition of employment with an emphasis on security, compliance and provisioning. Prospects and customers may be lost forever if the registration, log-in, update process, consent management and other CIAM services are not deemed to be an intuitive, responsive and overall positive experience.
Another key area of focus in building a CIAM program is ensuring that trust is established with the proper data security, consent and privacy protection. Customers expect some control over how their data is collected, managed, stored and shared and the CIAM service needs to support this. In the era of more rigorous data protection and privacy regulations such as the General Data Protection Regulation (GDPR) in Europe, the Canada Privacy Act and the California Consumer Privacy Act of 2018 (AB 375), strong security and privacy controls and policies are necessary prerequisites for any CIAM program.
TechVision recommends that CIAM programs be considered a priority area of investment in most large enterprises given the direct business benefits and risks if customer data isn’t properly managed. Digitally connecting with customers and building sustainable business relationships require a strong and flexible Customer IAM foundation. This report describes the difference between CIAM and traditional IAM, key end-user requirements, CIAM architecture considerations, design guidelines and a short-list of vendors to consider. Traditional, enterprise-focused IAM is generally not the best solution to support customer facing applications and services, while CIAM is architected to specifically support the needs of current and prospective customers while minimize external risks.
Introduction – A Customer IAM Platform
For the past 25 years, most organizations have focused the bulk of their IAM investments in support of employees and contractors. This internally focused product/service has traditionally been called Identity and Access Management (IAM) or Enterprise IAM. Most large enterprises recognize that IAM needs to be extended to broaden its reach. Digital Enterprise (often called Digital Transformation) programs are extending digital connections to include customers and external stakeholders. CIAM can optimally support these connections and relationships throughout the prospect/customer lifecycle.
In our report on CIAM three years ago, we characterized Customer IAM as an “emerging” category. In our report on CIAM 18 months ago we declared that it had “emerged”. At this point we are beginning to see some maturity, increased vendor investment, broader usage and major vendors (such as Akamai and SAP) acquiring early initial CIAM leaders. We’ve also seen Ping and Okta go public with Okta’s recent market cap at over $26 Billion. TechVision Research currently classifies CIAM as a separate and distinct Identity and Access Management category and we expect this to remain the case for the next several years. Ultimately there
CIAM reflects an expanding set of IAM requirements that are not fully accommodated by the traditional IAM solutions. The increased scale, the diverse contextual information requirements, the focus on an engaging user experience, key privacy considerations/ regulations and support for and integration with sales/marketing and business critical applications are areas of particular emphasis in CIAM. Simply put, identifying, securing, contextualizing, supporting and providing a greater focus on user experience while ensuring appropriate protection for Personally Identifiable Information (PII) is critical in supporting current and future customers.
Most enterprises that don’t have a separate CIAM solution still have an IAM service that supports customers, but they are often just extensions of existing enterprise-focused IAM platforms. Customers still must be supported, sothese organizations use legacy systems with different schemas (internal and external), different securityprocesses/policies and physical separation between customer and internally facing IAM services. This can be a workable solution, but the problem over time is that traditional EIAM platforms have not been optimized for the customer experience and are not optimized for scale nor the cloud.
All enterprises have access to a growing base of customer data, but this data is often in disparate silos, not structured or just not being leveraged in an optimal way. For competitive reasons, the business benefits of providing a secure, seamless and unified customer experience across multiple channels (omni- channel experience) as part of Digital Enterprise/ Transformation programs is driving the CIAM market. The immediate benefits to the customer are to reduce friction by offering choices of interfaces, offering simplified-yet-secure login, providing self-service capabilities and relevant contextual data leading to personalization, progressive profiling and transaction efficiency. These factors lead to increased customer engagement and the likelihood of brand loyalty as long as security is maintained and privacy is respected.
From a business perspective, the upfront investment in CIAM offers faster time to market (immediately connecting with customers), a reduction in administrative overhead (automated, electronic processes) and ultimately, an on-going increase in revenue and client retention. But the use of CIAM and the collection and use of contextual data provides much more than just engaging the customer; the consistent use of these platforms are core business opportunities to get to know and serve customers better and more efficiently.
The challenge for both CIAM and customer data in general is that typically most customer data is stored in distinct database instances that are uncoordinated and unsynchronized, providing minimal value-added functionality. In fact, the very lack of coherence between multiple forms of Customer Relationship Management (CRM) and customer databases systems can lead to customer frustration, security vulnerabilities and lost opportunities for the organization. The right customer-facing IAM service can provide valuable profile information, preference data, consent management and other contextual information to support the integration of the right data with the right customers/prospects. In short, it can support key business goals through efficiency, accuracy and security.
Hence, it not only makes sense but it becomes a business necessity to address the issue by adopting a CIAMstrategy that will give your customers’ data at the very least the same level of care as that of your employees and at the same time improve their online experience.
It would be easy for an organization to view CIAM as ‘simply’ an extension of their existing EIAM or CRM systems – or both. At one level, CIAM does provide a similar degree of access to company resources as compared to EIAM, but CIAM requires greater usability and autonomy in managing profiles and preferences in support of developing long-term relationships and uncovering business opportunities. We’ll now take a look at how CIAM is developing as a separate IAM category and how it differs from traditional, internally focused IAM.
Enterprise (traditional) IAM vs. Customer IAM
While CIAM is based on long-standing Identity Management principles originating within the enterprise, there are major differences and areas of emphasis that are driving the Customer IAM category. Key deltas include increased scale, new types contextual information/ relationships, personal data control, a high priority placed on the user experience and key privacy considerations/regulations. CIAM is optimized for customer engagement while protecting the company and the individuals engaging.
This specialized class of IAM services requires links into marketing systems, CRM systems, customer data basesand reporting systems and must handle both the scale and the imprecision in engaging with customers and prospective customers. Employees generally won’t leave if there is a poor IAM user experience, but customers andpotential customers need to be enticed and motivated to engage and reengage. These stakeholders are also increasingly technology-savvy and expect a fast, pleasant and secure user experience or they may simply find that experience elsewhere.
Building a customer-oriented identity management system demands a significant shift in the way vendors and their clients approach the management and use of identities. Employees and contractors are a captive audience; they generally won’t leave because of cumbersome identity registration, update, login or provisioning processes. Enterprise IAM has traditionally been confined to a predictable, often static environment, based on a set of mandated policies that, to date, have security and access control as their design goal, while often leaving the user experience as a lower priority.
Customer or consumer IAM on the other hand is driven by an organization’s desire to engage prospective customers and build loyalty with existing clients. CIAM also provides more insight into its customers and plants the seeds forlong-term business relationships, enabling closer online responsiveness based on behaviors and both observed andcustomer-provided preferences. In contrast with EIAM, CIAM is, by its very nature, open to the Internet and involves scaling to hundreds of thousands or potentially many millions of personal identities. Scale apart, there are considerable differences between the approaches taken by traditional IAM solutions, which focus on managing employees and, in some cases partners and a new breed of CIAM services intended to manage interactions and relationships with customers and consumers. The key drivers for both are radically different, driven by different parts of the business and requiring different technical solutions and architectures.
Stricter data protection and privacy regulations supported by the threat of heavy fines and penalties are also increasing the stakes for better organizing, managing and protecting customer data. Marketing systems, CRM andCIAM services house large volumes or personal information – if customer data isn’t properly managed it isn’t just an administrative headache, it can also become a significant potential liability to businesses and their brands. This (privacy/data protection) is an issue with IAM systems supporting employees, but customer data presents more expansive risks.
While a small number of vendors offer CIAM-only solutions, most of the EIAM market leaders are extending theirB2E portfolio to address the requirements of Business to Customer (B2C) to affect the convergence addressed in this document. Others, however, will continue to differentiate between the two – at least for the time being – oftenpartnering with a specialist vendor for CIAM. As we’ll describe later in this report, we are beginning to see vendors(e.g., Ping, Microsoft, ForgeRock, Okta) offering a core IAM service with different views or configurations for customer engagement.
The following table provides a summary of the more important differentiators between CIAM and EIAM requirements and characteristics. These deltas as well as the increasing investment in the CIAM area (by both the vendors and their customers) are driving the movement towards purpose-specific CIAM service offerings.
| Characteristic | Enterprise IAM | Customer/Consumer IAM |
| Business | ||
| Purpose | Platform for employee engagement and the encouragement/enforcement of good corporate behavior | Platform for discovery and development of a relationship with the customer to drive consumption, brand loyalty and revenue |
| Drivers | Security risk and cost reduction, employee productivity, on- boarding and off-boarding efficiency | Acquisition, engagement, recommendation & retention; revenue-driven |
| Intelligence | Static, rules-driven intelligence; but changing with increased use of
contextual awareness |
Dynamic, real-time, analytics-based; Progressive profiling, personalized,
frictionless security based on analytics |
| Governance, Risk and Compliance | ||
| Access Management | Information protection and appropriate access is key to the enterprise | Dynamically balance ease of use/engagement against risks |
| Access Governance | High priority | Low-to-medium priority, transaction value- based |
| Policies & Permissions | CIO/IT/CISO with perhaps some input from LOBs | LOB/Marketing and CIO/IT/CISO as well as (increasingly) the customer directly |
| Privacy Compliance | Centralized policy-driven with further controls for regulatory compliance; Implicit consent | Policy-driven as well as customer-driven and opt-in/opt-out and explicit consent management. Protection of PII is key as is
privacy regulation compliance |
| Architecture | ||
| Adaptability | Integration with back-end systems such as HR and Active Directory, with growing SaaS integration | Dynamic schema required to support managing consent, opt-ins and preferences; Integration with CRM and customer reporting solutions |
| Agility | Traditionally monolithic and
predictable |
Modular and adaptable |
| Architecture | SOAP/REST, principally desktop/laptop centered | REST, often “mobile device first” |
| Extent | Perimeter-based, enterprise-defined; but evolving to perimeter-less | Borderless, inclusive, internet-scale |
| Network | On-premise, moving to cloud/hybrid as well as BYOD/BYOI/BYON | Mobile and cloud-first; on-premise/hybrid if necessary |
| Performance | Higher latency using captive IDs, primarily for security | Lower latency for frictionless user experience, taking account of busy hours (evenings and weekends) |
| Scalability | Tens or hundreds of thousands, relatively stable size | Hundreds of thousands or millions,
sometimes expanding with Sales & Marketing campaigns |
| Velocity | Corporate or LOB requirements for on- boarding, often slow and methodical | Internet speed with risk awareness |
| Data | ||
| Data | Predefined by IT, stored in directories and relational databases | Derived from many sources, often using unstructured data requiring dynamic schema and progressive profiling,
increasingly adding IoT devices and data |
| Enrollment | Triggered by employer | Initiated by consumer or through registration invitation link |
| Profile & Preferences | HR and employee with limited scope | LOB from CRM and consumer through self-
service, with personalization a key to long- term engagement |
| Provisioning | HR-driven, defined by CIO/IT policies | Users voluntarily register through self- service or registration invitation link, define desired interactions |
| Scope | Employees, contractors, consultants and sometimes partners | Customers/prospects/consumers; optionally employees, contractors, partners, service providers who are also
customers (e.g., Retail employees) |
| User Experience | ||
| User Experience Priority | Generally low priority, but gradually improving, driven by more by non- security focused departments, such as
HR or Engineering |
Unified user experience is high priority, further enhanced by self-service, fast response time and simple registration |
| Personalization | Limited but beginning to add personalization/birth rights, largely driven by HR | Considered a differentiator and a benefit to both enterprise Marketing-focused LOBs and consumers |
Table 1: Enterprise IAM vs. Customer IAM Comparison
CIAM Opportunities and Business Benefits
One of the areas TechVision spends a lot of time covering is the new digital world enterprises are facing and this world is accelerating at unprecedented speed in the wake of the COVID-19 global lockdown. We believe that organizations aren’t just transforming, they are becoming Digital Enterprises. The transformation is on-going and pervasive as the Digital Enterprise is evolving to better enable the way we do business. One of the most criticalfactors towards securing and managing this new digital reality is a robust and inclusive Identity Management foundation. And the most visible part of this IAM foundation is how organizations engage their customers viaCIAM.
The business benefit that CIAM brings is so much more direct than other “infrastructure” services; CIAM allows anenterprise to better connect with and better understand customers and prospective customers by observing their activity and collecting data while on their website(s). If this is done right and supported by other services, there can be a positive impact on revenue and customer satisfaction; it is hard to make such a strong claim with other infrastructure technologies. CIAM, done right, drives revenue growth by connecting with customers, responsiblycollecting data and using the insights from that data to acquire, retain and grow customer revenue and loyalty.
Functional areas that drive CIAM-based business benefits fit into almost every element of external relationships, but IT, Marketing, Sales, Legal and a variety of LOBs benefit directly from a strong CIAM program. The most visible area of CIAM is Sales/Marketing given their involvement in engaging, analyzing and selling and we’ll discuss these direct benefits next.
CIAM is all about engaging current and future customers and it can be a game changer for enterprise sales and marketing teams by efficiently improving connections and insights at scale. Marketing is all about is understanding and categorizing a target market and understanding user preferences, buying patterns, intent and influencers. CIAM and the Digital Enterprise together provide a wide range of connections and generate data to be analyzed at scale to increase insights, brand loyalty and, ultimately sales.
But remember, collecting customer data can also increase enterprise risk as regulatory controls increase in volume and complexity. Collecting data without consent or in amounts deemed excessive can damage trusted relationshipsand can also create legal and regulatory risks. The good news is that proactively and transparently addressing the security and privacy challenges (like clear and simple privacy policies, implementing Privacy By Design…) can also build customer loyalty and is a foundational principle in good CIAM programs. Customer connections and building relationships supported by CIAM is a major business benefit as long as you maintain the trust your customers and prospective customers are implicitly offering by engaging with you.
A key component of the Digital Enterprise is getting to know your customer and prospective customers better and CIAM is perfectly positioned to support this. The principles of Know Your Customer (KYC) require businesses to verify who their clients are and specifically determine that they are neither laundering money nor engaged in fraud, not involved in terrorist activities or any form of illicit trafficking and are anti-bribery compliant. Although KYC is mandated for the banking and finance community, enterprises of all sizes engaged in any financial transaction have a need to know that their customers are legitimate; in other words, ‘they are who they say they are’, not on any transactional blacklist, and of low or accepted risk. One of the key capabilities of CIAM services is to identify anomalous or suspicious behavior, not only at the beginning of a customer relationship but throughout the full customer lifecycle.
Most organizations benefit from improving their knowledge of targeted customers and prospects. Behavior patterns are discernible from a variety of different input sources, such as purchasing preferences, location-based information, social media feeds, and data collected/verified from identity profiling. CIAM services, often in combination with Marketing systems and CRM services, can provide insights to business leaders (Marketing, Sales, LOB executives) about customer trends, leads generated, conversion rates by market segment, cross-selling opportunities and, of course projected and actual sales results.
Correlating customer patterns/usage data with identity data can provide insights as to who the customer is, withwhom they associate, and what they are likely to buy. The primary goals of present day commercial digital marketingare to determine who you are, who your friends are, and your habits in order to predict what you’re going to want next and figure out how to offer it to you at a compelling price point. CIAM services combined with the right privacy controls can enhance customer confidence and trust that is critical in determining if the brand reputation is strengthened rather than compromised.
Some of the most valuable sources of marketing and sales data comes from customer self-interest and usage. Whensomeone identifies himself or herself online, they voluntarily give up a certain amount of data before participating in a loyalty program or even before making their first purchase. The more confidence this individual has in the brand and the privacy protection, the more complete and genuine the responses, will generally be. For example, if a consumer doesn’t trust the brand, doesn’t like the digital experience, isn’t confident as to how the data generated will be used or shared, then the data they provide (if they provide any data) may not be accurate or complete. This is a critical business area that can be supported by the right CIAM infrastructure.
It is important to understand that CIAM is a critical element of an externally facing Digital Enterprise program, but only a piece of the puzzle. While CIAM helps to identify and contribute to decisions concerning appropriate access, these services do not replace marketing automation or CRM systems. They integrate with and augment these systems to help organizations get maximum business value out them. We’ll next net out some of the key Customer IAM requirements we typically find and recommend in working with large organizations.
CIAM Requirements for Large Enterprises
TechVision Research has extensive experience “on the ground” working with large enterprises in helping to develop strategies, architectures, tactical plans, collecting requirements, developing vendor RFIs and RFPs and helping to establish how CIAM fits within the overall IAM, Business and Security portfolios. While every organization is different, we’ll now describe key features and capabilities generally required for large enterprise CIAM programs.Many of these topics were addressed at a high-level in comparing CIAM to EIAM, but we’ll now look at it from the context of the core capabilities enterprises need in their CIAM program. This will also be a foundation as we describe how the core requirements and pieces fit together in the TechVision CIAM reference architecture we’ll describe later in this report.
Let’s start by netting out the most important aspect of CIAM: engaging your customer/ prospect in an easy, compelling way. It is all about that experience; connecting with your current/future customer should be seamless, fast, mobile device optimized and provide the perception that the user controls the experience. This needs to be done in a way that complies with regulatory controls, data protection legislation and provides the requisite security controls, but remember that if you can’t engage your prospects/customers on an on-going basis, none of this matter. So start with the user experience.
The core CIAM requirements enterprises are seeking include the following areas we’ll break out by category. We’ll start with the business benefit, then user/customer facing requirements and then consider some of the technical requirements by category or service offerings.
- CIAM Business Benefit: Maximizing Conversion Rates and Building the Brand: This is where business goals meet CIAM. Turning suspects into prospects, into customers, into loyal customers can be greatly enhanced by a strong CIAM program. It bears mentioning, though, that such strong CIAM business benefits can also contribute to LOBs sometimes circumventing IT (especially using IDaaS solutions) and establishing their own CIAM-based customer interactions in order to achieve a better time-to-market that is perceived (often correctly) to be slowed down too much because of “governance bureaucracy”. While TechVision doesn’t advocate building a CIAM program in the absence of governance, it bears mentioning that this a significant
- On-Boarding and Registration: This is where it all starts. This experience must be “frictionless”, a word we’ll use a lot in CIAM as it is all about enticing your (prospective) customer to engage and build the relationship. This can be supported by an attractive user interface that is fully optimized for both the web and mobile devices, simple on-boarding requiring minimal user information initially, perhaps pre-built registration forms, self-service support and API support to seamlessly integrate with various social The easier and faster this is for your customer the better.
- Identity Proofing/Verification: The amount of data and degree of required proof of identity (also called identity vetting) can be progressive based on the point a user is in the lifecycle (e.g., just registered, long-time customer) and the related security and risk management policies. Flexibility in terms of choices for the user is of value, but remember to evaluate the risks associated with lower quality identity proofing and the value of the customer transactions before accepting that
- Customer Profile Management: This involves understanding your customer, their likes, dislikes and usage Customer profile management includes preference management (how the customer manages their interactions), self-service, consent management, privacy/data protection (GDPR, CCPA…) compliance and support/management of both structured and unstructured data.
- Progressive Profiling: This process gradually collects and aggregates data about users. The concept is that you start small and don’t scare off prospective customers and then throughout the lifecycle continue to refresh and update your profile data. This can both increase conversion rates and support acquiring more contextually relevant data. There must be a balance between the amount of profile information being captured and the point where a customer feels he or she is being ‘spied on’.
- Unified Customer View: This is of tremendous value especially for large organizations with related but different product lines or businesses. This should also support consistency across multiple channels. This allows an organization to view an individual customer across multiple properties or LOBs. The CIAM service can also help to normalize and correlate all customer interactions and integrate third party data sources for this comprehensive customer view. This is important for the business, but also of value to the customer in providing a more seamless user experience. One of the most commonly heard complaints from customers is that a business doesn’t do an appropriate job of “remembering them” because they have not normalized customer identities across multiple lines of business, forcing the customer to reenter or correct data, or create multiple accounts and
- Scalability/Performance: CIAM solution must be able to handle millions of users across multiple channels with no perceived performance degradation. The CIAM system must be able to accommodate large volumes of users, data and spikes in registrations and access requests while maintaining a high level of This is of particular importance when the business rolls out a new sales and marketing campaign that causes both new registrations and logins to spike dramatically. It is also extremely important to factor in Business Continuity and Disaster Recovery plans – so the ‘sales light’ can never go out.
- Cloud/Hybrid Support: Most enterprises are moving to or have moved to a cloud first strategy in particular in engaging external users. That said, many organizations have substantial legacy systems and services on premise and may not be ready to “jump into the deep end” when it comes to complete cloud engagement. Flexibility in this area is of considerable value and often required by large organizations. Specific capabilities such as Federation using OIDC, OAuth2 and SAML are critical to providing seamless customer identity integration across multi-cloud and hybrid
- API Support, Integration and Orchestration: Support for APIs and developer toolkits overall is critical in integrating current and future environments. Few large organizations have “greenfields” and support should include support for simple integration with CRM, ERP, Marketing Automation and internal external datasources. For this reason in particular, a CIAM strategy that creates an Identity Data Service that supports discrete IAM services such as Login, Register, Self-Service and so forth is critical to consistent and secure adoption of CIAM features embedded in multiple customer-facing apps – both commercial off-the-shelf and homegrown.
- Advanced Analytics: The use of AI/ML, big data to better understand customer intentions, understand your customer and support for security through anomaly detection, adaptive access control, User Entity Behavior Analytics, Insider Threat monitoring and so
We’ll now describe a few areas that are particularly important in greater detail and then summarize key enterpriserequirements later as we use that as a basis for enterprises to use our capabilities-based reference architecture in developing the framework for your CIAM strategy and, ultimately, implementation. CIAM always starts with theCustomer Experience; if you can’t entice and engage the customer, nothing else matters.
Customer Experience
A positive result of a strong CIAM and customer engagement program is that enterprises can cement customerloyalty by taking the opportunity to streamline and personalize users’ online experience. Think about CIAM engagement as analogous to how a high-end brick and mortar retail store associate uses customer knowledge to recognize and welcome customers when they enter a store, remember their buying preferences and steer them towards profile- relevant deals or promotions. CIAM and supporting applications should digitally replicate and improve upon this positive in-store experience. CIAM can similarly help support all phases of a customer’s digital journey through your “online store”.
The key here is to regularly update and adapt the customer experience based on customer input (direct or observed) throughout their online relationship and journey with your organization. There may be times when there are buying signals and times when they are getting too much information and may completely disengage if there is not anoption to “dial back” the interactions – this is about striking that balance between helpful and intrusive, as wementioned previously. To achieve this balance, the CIAM platform and supporting ecosystems must be flexible, adaptive and contextually aware while conforming to regulatory controls and honorable principles, which we’ll cover next.
CIAM Regulatory and Security Control Considerations
In connecting with customers and prospects there are different expectations, different security controls and evolving regulations to consider. GDPR, CCPA and other privacy and data protection regulations are adding significant financial penalties to those enterprises that don’t comply. That said, there is a balancing act in that the customerexperience must be fully optimized and business insights collected – but not at the expense of personal data protection and regulatory compliance. The best implementations provide “frictionless security” while using big data, analytics, perhaps AI/ML to provide strong underlying security controls. The CIAM solution should support both basic compliance requirements (consent management, right to be forgotten, etc.) while meeting the marketing and sales requirements.
Security/Risk
Introducing a CIAM system brings with it a new set of challenges required to balance meeting the usabilityexpectations of customers and maintaining a high degree of security. Most CIAM vendors provide a range of security levels including multi-factor, adaptive and/or step-up authentication and increasing contextual awareness regarding the geo-location, device and usage patterns normally associated with each customer. This provides an additional level of security for those applications or use cases requiring it, but can also strain the path towards engagement in initial interactions with prospective customers or in support of low value/low risk interactions.
When designing CIAM programs, it is important to be flexible in the early stages of the relationship with a prospective customer and not let invasive security controls derail the ‘preliminary’ relationship. In these earliest stages, often no identification is required (typically low value, non-financial applications) and this can generally ramp up to some “light-weight” identification or registration leveraging social login, federation or simple user name/password. This is what we refer to as step up authentication supported by progressive profiling. Most users desire a “frictionless” registration process and will show a degree of intolerance if engagement is difficult, time consuming or requires too much personal information to be disclosed in relation to the value of the transaction being conducted.
A key concept to remember is that the level of security controls need to be carefully evaluated in the context of the user experience and where the user is in terms of the relationship with your organization. These decisions are, of course, based on risk management as well as your business assessment. Most enterprises have invested heavily in risk management over the past decade, principally through the deployment of Governance, Risk and Compliance (GRC) systems that help decision-makers and enterprise governance bodies monitor the level of risk associated with their IT environments. That said, enterprise LOBs that are more heavily focused on sales and marketing have a vested self interest in operating outside the influence of enterprise GRC and sometimes do; be careful to not let this happen.
Proper institutional governance with an understanding of the often not-so-subtle nuances between the two missions (business and risk/compliance) will go a long way towards achieving balance of CIAM right controls and a strong customer user experience.
Privacy & Consent
While the benefits and opportunities of extending IAM systems to incorporate context and relationships are substantial, there is a real danger of a gradual encroachment on the dividing line between what customers and regulators find acceptable. This customer discomfort is increasingly being supported by legislation such as GDPRand CCPA that define obligations for protection of consumer data, the right to be forgotten and various privacy rights. This gets increasingly complicated as enterprises collect and leverage big data, gain identity insights and develop nested relationships with consumers around the globe and in differing privacy regulation jurisdictions.TechVision has written several reports on privacy, regulatory controls and consent management if you wantadditional details, but understand that customer-facing interactions will have high visibility and scrutiny from a privacy and regulatory perspective.
In order to achieve compliance with data protection legislation in any jurisdiction, and at the same time achieve anacceptable level of business agility, separate views on a user’s identity are not feasible: it is vital to have a unified, single view of a customer’s identity profile, consents (opt-ins) and preferences. In order to bring about this coherentpicture and support diverse regional privacy regulations, stringent business rules will need to be captured, modeled and codified in systems. Juggling the constraints imposed by one jurisdiction over another places higher demands onthe modeling than in most other system rollouts and may have more than GRC ramifications. In this sense, the best course of action is to view a regulation such as GDPR as the common denominator for regulatory compliance controls worldwide, unless the enterprise steadfastly only intends to operate in a single ‘regulatory region’. Areas such as consent management are critical in achieving GDPR compliance and protecting your organization. Forfurther details, TechVision has produced reports on GDPR, CCPA, consent management and developing a Privacy Program in light of increased legislation.
In addition to basic identity data, there are also categories of derived data based on behavior patterns such as social, retail, travel as well as device usage that need to be managed and secured. Putting habit and usage data together with identity data can enrich the customer experience and drive business results. As stated earlier, the primary goals of present-day commercial marketing are to determine who you are, who your friends are, and your habits in order to predict what you’re going to want next and figure out how to offer it to you at a compelling price point. Properly correlated customer data strongly supports those goals.
Lastly, there are many occasions when simply conforming to privacy regulations is not enough. As we mentionedabove, there is a growing need for honorable principles that show the customer that you have spent miles in their shoes, and that you truly have their best interests at heart. It may be perfectly legal to ask for some piece of personal information – but you have to ask yourself why you really need it. Customers are more sensitive to the collection and subsequent sharing (or blatant misuse) of information than many companies currently give them credit for. Justbecause it is not illegal, doesn’t always make it right or necessary and can impact your trusted relationship with your customer.
Building a CIAM program
Most large enterprises are architecting and viewing Customer IAM as a separate and distinct program. TechVision has been working with several large clients in helping to build their CIAM strategies, reference architectures, vendor evaluations and implementation plans so we’ll be providing insights here based on real-world experience. We’ll now describe key strategies, major architectural elements and design guidelines to consider in building your CIAM program.
These programs are often initiated by major customer facing digital programs and more pervasive Digital Enterprise programs. A core theme within these programs is to better connect with and engage customers with the proper balance between security, privacy and business goals. Note that while virtually all large enterprises have some level of Customer- facing IAM in place, many of these solutions are static older generation iterations on existing Enterprise IAM, repurposed for customers. They are generally not mobile device friendly, not user friendly, have little integration with marketing systems and were put in place long before more stringent privacy regulations came to bear.
Whether your enterprise is starting CIAM up in a green field mode or you’re replacing/ enhancing an existingCIAM solution base, the recommendation of separating and upgrading your CIAM services are germane.
TechVision recommends starting any CIAM program (or any key infrastructure initiative) by engaging key stakeholders and developing a base-line set of requirements. While our assessment of typical CIAM requirementsmay not fully represent your organization’s needs and was broadly covered earlier in this document, we find thatstakeholders are often better equipped to modify a base-line set of requirements than to start from scratch. We’ll provide this guidance in the next section.
Identify Stakeholders, Understand Current State/Requirements
Step one is to identify key stakeholders in the CIAM area. This often includes LOB leaders, application development teams, IT, security, marketing, customer support, digital transformation teams and sales. You’ll want to understand key initiatives and how CIAM might help support these programs. You’ll also need to understand the current state of your CIAM program, other IAM efforts/data sources and customer-facing initiatives. Interviewing key stakeholders in the LOBs, Marketing, Sales and IT/security will help frame the initial requirements. This is typically what TechVision does early in our consulting engagements and this nets out the following general CIAMrequirements:
| Requirement | Description |
| User (Customer) Experience | This is typically the most important area in a CIAM program as it is all about engaging current and future customers. Any CIAM service should prioritize the user experience. Key elements of this engaging user experience include response time (less than 2 seconds), ease use and flexible sign-on process allowing user choice, an engaging/easy tounderstand user interface, simple self- registration and update capabilities as well as a reduction in repetitive user processes. |
| Support for Single-Sign-On (SSO) Across Multiple Customer Facing Applications | In a TechVision work with large end-user organizations, SSO is oftenthe number one requirement. Signing-in multiple times from various applications and sites across a large organization is a major end-userpain point and should be an area of emphasis in
evaluating CIAM solutions. |
| Customer Self-Registration and Update | Users want to control their information and make sure it is accurate. There is also greater trust in the data (and the
organization keeping the data) if the users can control their own PII. This also generally results in more accurate data. |
| Cloud Integration and Cloud Native Support | Most IAM solutions are moving to the cloud, but CIAM is moving even faster to the cloud than Enterprise IAM and is a key requirementfor many enterprises. The fact that the customers are
generally, geographically distributed and leverage various SaaS applications also drive the requirement for cloud support. |
| Customer Enrollment/Provisioning/De- Provisioning | These are critical areas for most clients in that they can either grow therelationship or end it at enrollment and provisioning time. The enrollment needs to be seamless and the deprovisioning needs to be fast, complete and transparent (all connected systems/applications deprovisioned) from a security and regulatory perspective. |
| Bring Your Own Identity (BYOI)/Social Media and Login/Federation | This is critical for the extensibility and flexibility of the CIAM service and is also a key trend; especially with the COVID-19 lockdown.With user environments now known and without direct governance support for federated authentication, mobile IDs/phone numbers and other BYOIs as well as social media credentials will increase adoption and lower risk. The mantra is
federate what you can’t directly manage/control. |
| Customer Identity Data Management and Integration with Authoritative Source Systems | The two successful CIAM and Digital Enterprise programs is the inclusion of multiple applications, systems, data sources and servicesand tools to support this integration are critical to support
inclusion and/or migration of these types of data sources while maintaining security controls. |
| CIAM Integration with Customer- facing Portals and Applications | CIAM is an important infrastructure, but still a tool in larger customer-facing programs and business initiatives. Single sign-on and more seamless integration, often via RESTful APIs is critical. |
| Incorporating IoT and other New Object Classes | CIAM services will increasingly need to incorporate IoT devices and the sometimes-complex set of relationships within the IAM service. This may dramatically increase scale and provide challenges in terms of the identification of smart meters, home
security systems, set-top boxes and devices ranging from dumb to very complex. |
| Scalability | Even very large enterprise IAM services may only get up to a few hundred thousand-person objects in their identity store. CIAM may move this number to the hundreds of millions and if you add IoT devices, RPA processes and relationship data the numbers can getmuch larger. This increased set of connected objects combined with faster response increases the importance of scalability for CIAM solutions. |
| Compliance with Regional Privacy Regulations Consideration | The Global Data Protection Regulation (GDPR) in Europe and privacy laws in California, Brazil, Canada and other parts of the world are increasing the stakes. This includes gaining explicit consent for the use of data and having the right to erase data including the “right to be forgotten” based on user requests. It is incumbent upon the CIAM service to support these capabilities
including the means of maintaining user consent data and proper audit trails. |
| Future State Technology Adoption | An often understated but important requirement is the ability to integrate with and migration to emerging technologies such as edge computing, microservices, DevOps, blockchain, verifiable claims and new self-sovereign identity models. Some of these emerging initiatives include bring your own identity (BYOI) ecosystems that should seamlessly integrate and with and be recognized by your CIAM solution. As TechVision has always maintained, it is important for your CIAM (and EIAM) architectures to remain loosely-coupled and federated to best ensure an easier adoption path for these emerging approaches to identifying oneself in the digital world. |
| Mobile Device Support | Many CIAM and most EIAM environments were not initially designed for mobile devices and have been put into device wrappers that do a poor job of facilitating registration and login
from mobile device. Mobile is a key capability and must be designed in from inception. |
Table 2 – CIAM Requirements
The above list is a starting point for key requirements organizations may consider in evaluating the need and possible solutions for Customer-facing IAM services. Note that we also covered typical enterprise CIAM requirements earlier in this report and our clients should use these as starting points and then build your own set of requirements as you see fit. A strong set of core requirements is a necessary pre-requisite for developing your CIAM reference architecture.
Development of a CIAM Capabilities-Based Reference Architecture
After assembling a team of key stakeholders, assessing the current state and collecting prioritized requirements, we generally recommend organizations develop a reference architecture taking our templates (or your favorite reference architecture model) and mapping these requirements into the key capabilities associated with a CIAM solution.
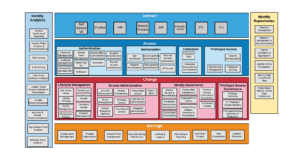
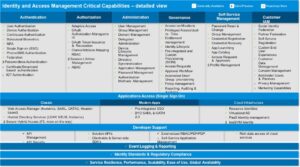
The TechVision Research Reference Architecture for IAM is this starting point; a master template, shown inFigure 1, below, identifies the IAM capabilities (rather than technologies) that can be improved or enabled, allowingbusiness stakeholders and technical architects to achieve a common language for IAM functions, which can then be refined over time. While this is the same definition that we apply to people identity-oriented use cases, there are specificchallenges as we’ve discussed in managing things and the relationships they support. This high-level template starts the journey.

Figure 1: IAM/IDoT Master Template
The capabilities that frame the CIAM architecture illustrated above are described at a high – level as:
Interact – how end-users and application developers interact with the IAM platform. In the case of CIAM this will involve how a wide customer, prospect and application interactions.
Access – the rules that define the roles, rights, and obligations of any actor or proxy wishing to access enterprise or connected external assets.
Change – the capability to define and manage the relationships between the user/ application developer and the enterprise assets.
Manage – the capabilities required to manage and upgrade the IAM solution itself.
Measure – the capabilities required to audit and improve IAM activities.
Store – the capabilities required to share identity information and relationships between the components of the IAM solution. The scale and responsiveness requirements for connected devices may impact this element.
Figure 2, below, highlights our more detailed capabilities portfolio to consider in the context of technical interactionsbetween the typical components comprising a comprehensive CIAM ecosystem.
Figure 2: Elements of a Combined Portfolio Architecture
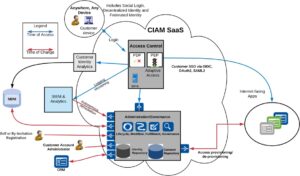
Generally, enterprises should consider CIAM in the context of their overall IAM program, but as we have said – it is important to understand the specific context of and risks associated with connecting to customers and prospective customers, defining their inter-relationships and managing those data generated by these users. It is also important to recognize that the reference architecture patterns of interfaces, authentication, authorization, lifecycle management, persistent storage, and analytics are supported as CIAM. Figure 3 below illustrates an example of how an enterprise consumer IAM reference configuration could be deployed relative to cloud-based customer-facing identity and access services.
Figure 3: High Level CIAM Architecture and Flows
Of note in Figure 3 are the multiple cloud-based and on-premise customer data repositories and systems, such as CRM and reporting systems that all work together to capture, retain and provide relevant customer identity data that can be augmented with behavioral and contextual data to really help enterprises better know their customers, servethem with what they want and improve the user experience by federation and looser-coupling. Even though most large organizations are moving to a “cloud-first” strategy, many legacy on-premise applications and data sources will exist for many years and must be properly managed and integrated.
Achieving this flexibility and loose-coupling often requires federation, virtualization and connectors to bring in bothlegacy and new environments. Vendors such as Radiant Logic are often leveraged as part of the “integration glue” to provide better Identity inclusion.
Additionally, note the predominant usage of RESTful APIs and federation protocols in use to better support mobile device integration – and multiple backend system integration in general, along with establishing a firm base forfederated authentication that leverages social login and multi-party service offerings integrated through single sign-on.
After understanding key stakeholder requirements, assessing current state and building reference architecture most organizations are ready to consider vendor alternatives. We’ll consider CIAM vendor alternatives next.
TechVision Research Vendor Shortlist
CIAM has been a major area of vendor and end-user investment over the past few years and as a result, the bar hasbeen raised in terms of expected capability and performance. Several vendors have answered that call and those are the firms we are including in this short list. Remember, the TechVision Research short-list is tightly aligned with ourconsulting business and represents our initial recommendations for vendors to consider for further evaluation inRFIs, RFPs, POCs and other methods of selecting vendor partners. This doesn’t necessarily mean that the vendors selected on our shortlist are the best overall identity management providers or the only vendors to consider in theCIAM space for your organization. We highly recommend a formal evaluation process starting with key stakeholder requirements, reference architecture and an overarching CIAM strategy, but when you are narrowing down potential vendor partners, this short-list may be a starting point.
An interesting development in the CIAM space is that we are now seeing a few vendors that are leveraging theircore IAM service and offering a customer view rather than a completely separate CIAM offering. To varying degrees this is what we have been hearing in our interviews with and research of Ping Identity, Okta, Microsoft andForgeRock. Other vendors such as SAP/Gigya, Akamai/Janrain, iWelcome Cloudentity are offering more CIAM-centric services. There is also a disruptive CIAM model called Decentralized Identity that vendors such as IBM, Microsoft, Ping Identity and SAP are pursuing and worth consideration in longer-term IAM plans.
In characterizing how and why vendors are on this shortlist, our primary considerations include the scalability of the solutions, the strength of the user experience, progressive profiling capabilities, global support, security/compliance controls, scale/performance, GDPR/privacy support, consent management, single sign on support, federation,integration tools (connectors, synchronization, meta-directories, virtualization), how effectively contextual information is used, the sophistication of the relationships that are being managed, marketing/sales system integration, and the accessibility of information to users.
From this point of view TechVision’s CIAM vendor short-list in 2020 includes Akamai, Cloudentity, ForgeRock, IBM, iWelcome, Microsoft, Okta, Salesforce.com and SAP. It is also important to understand that there are other viable approaches to directly supporting Customer IAM and providing the integration capabilities, ecosystems and governance services that will help to achieve success in major Customer IAM programs. These vendors include Google, Amazon, SailPoint, Micro Focus and Radiant Logic.
We’ll provide a brief background on each shortlist vendor in the main CIAM category and a brief description of their solution and TechVision’s perspective on each vendor in alphabetical order as follows:
Akamai
Akamai’s acquisition of Janrain in 2019 has propelled them into a leadership position in the CIAM space. Janrain made both previous TechVision short-lists as a leading early vendor in this space and they are still a major player inthe CIAM area. Akamai subsequently rebranded the service the Akamai Identity Cloud and is increasingly integrating their Customer IAM IDaaS service with other core company services. In writing this research report, TechVision had the opportunity to speak with Lorenz Jakober, Senior Director of Product Management and Andrew Ward, Senior Director of Product Management for the Akamai Identity Cloud.
Figure 4: The Akamai Identity Cloud
Akamai’s Identity Cloud is designed to be an end-to-end IDaaS CIAM solution engineered with a cloud-native architecture. This allows the solution to scale with application capacity needs as well as to accommodate spikes intraffic for managed performance and availability.
The Akamai solution offers a centralized, standardized, but configurable user experience and open protocols focusing on minimizing client-side complexity. Their CIAM solution has moved all identity components to the cloud andabstracts identity from applications. Akamai Identity Cloud provides:
- Customizable registration and data collection forms designed to be customized and styled to its customers’
- Optimized registration screens for mobile and IoT to create device-aware registration
- Real-time field validation on form fields, bad word filters, and terms of service and privacy policy acceptance. Validate email address or postal code formats in real- time, verify age or password requirements.
- Fraud Scoring recognizes fraudulent and fake accounts at registration time, before they enter connected systems and
- Conditional workflows for progressive profiling designed to dynamically trigger personalized form fields and distinct user flows based on customer profile
- Support for social login from Facebook, Twitter, Google, LinkedIn, WeChat, and more than 30 other social
- Support for authentication options including MFA, Push, OTP and phone-based. Adaptive authentication escalates or deescalates authentication requirements based on fraud analytics or other factors enterprise customers
- Consent management for users to control multiple areas of consent — including email and othercommunication preferences and app Customers can also view consent profile.
- Heavy on customer analytics by leveraging path analysis, enhanced fingerprinting, and predictive modeling – stated goal to help enterprises build a holistic view of user interactions, increase ‘match rates’ and combine journeys across
They described the future state roadmap as including 5 pillars as follows:
- Customer End User Experience: focus on engaging customers, progressive profiling and appropriateness for the business
- Platform and Scale: Leverages Akamai core strength, modernizing infrastructure, OIDC APIs
- CIAM Modernization: Includes “guided workflows”, real-time integration,
- Adaptive Access: 2FA, Risk-based authentication and risk signaling in the next year, leveraging Akamai intelligence database
- Service Insertion in Edge Authentication: Moving core components to the edge (such as authentication) for bot management
Janrain was one of the leaders in the CIAM IDaaS market before the acquisition by Akamai last year. We see continued investment by Akamai into this expansively-deployed solution as Akami looks to leverage core company strengths. As a result, TechVision continues to recommend to our customers that Akamai be a short-list vendor in the CIAM IDaaS market.
Cloudentity
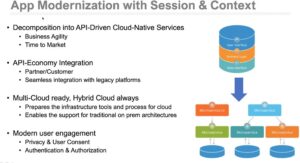
Cloudentity, based in Seattle, WA, has been in business for several years as a security and IAM consulting company and has transitioned to a product/service vendor. TechVision had the opportunity to recently interview Nathanael Coffing, their founder and Chief Strategy Officer. He described their offering as fitting into the modern DevOps model serving up microservices to support application specific security, micro-perimeter security and intelligent riskscoring. Nathaniel also stated that CIAM is continuing to grow its presence in the marketplace – focusing on marketing engagement and customer engagement, and more degrees of specialization. Modern IAM is becoming more OIDC-based and the challenge is how to bring all of our applications into this environment. IAM teams havestruggled to keep up with onboarding of traditional / legacy applications. They feel that API adoption accelerates innovation, that developers are leading the way and the challenges are around how-to onboard applications more quickly with a consistent, secure and frictionless user experience. According to Cloudentity, CIAM is centeredaround:
- Session – how authenticating and bringing users and machines into the application
- Context – meeting at the API with distributed policy decision points and distributed
The illustration below, provided by Cloudentity shows these relationships.
Figure 5: Cloudentity Model for App Modernization with Session & Context
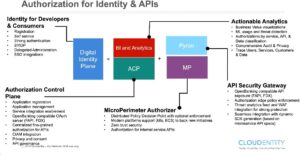
Key to their model is the Authorization Control Plane (ACP), which can leverage principal Identity Providers (IdPs)and incorporate those identities into a finer-grained authorization context for distributed policy enforcement of users, things and APIs. The functions and features of the ACP and supported Cloudentity components are shown below.
Figure 6: Cloudentity API-centric Ecosystem
In concert with ACP and Pyron, Cloudentity’s API security gateway and their MicroPerimeter Authorizer (MP) work in conjunction to apply authorization rules regardless irrespective of location. Nathanael explained that this is the fastest way to onboard an application into the IAM ecosystem, because it offloads much of the authorization decision-making from the applications themselves.
With their relationship with AWS, customers can use AWS API gateway in the same way. AWS Cognito can be incorporated in much the same way by connecting with ACP’s Identity Hub that provides the ability to normalize identities from multiple backends, such as AWS – almost like a virtual directory. The Identity Hub helps developers create simple, no-code, drag and drop customer journeys with registration trees. It can also use out-of-the-box registration trees designed for ease of use. For instance, Identity Hub and ACP can be used to create an adaptive customer journey that provides opportunities for gathering consent, ensuring that only the most necessary customer data is collected and only after the user has given consent. Azure and Azure B2C is also integratable in this manner. In fact, all of these external IdPs can be integrated and normalized within ACP.
The graphic below illustrates the integration points and flows between ACP Identity Hub and multiple authoritative identity sources, authentication and authorization frameworks.
Figure 7: Cloudentity Authoritative Sources of User Identity Data
Cloudentity’s identity security products were specifically designed to work with leading container orchestration platforms. For example, once deployed in a Kubernetes cluster, the sidecar automatically registers with the central repository to provide East/West tracking and security. Additionally, each Cloudentity product is distributed as a Docker container or an installable Linux package. Cloudentity is strong technically and has a model that fits within the next generation of microservices and DevOps programs many enterprises are moving towards. Cloudentity starts with a microservices approach with strong delegated administration, identity proofing, and provisioning, authentication and authorization services. For an enterprise with “develop first” IT principles, this modern approach and deep technical strength has positioned Cloudentity as an “up and coming” CIAM vendor.
ForgeRock
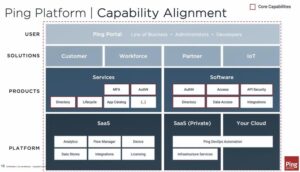
ForgeRock has a built a scalable platform. TechVision had the opportunity to recently interview Peter Barker,ForgeRock’s Chief Product Officer, who provided an overview of the soon-to-be-released (as of late June) Version 7.0 of the ForgeRock IAM platform as well as his vision for CIAM. ForgeRock’s IAM market share continues togrow substantially, as many organizations continue to modernize their IAM infrastructures – both EIAM and CIAM, migrate their IAM workloads to the public cloud and embark further on their digital transformation journeys.
Peter described ForgeRock’s strategy as including enabling brand trust by providing a centralized platform and tool sets to better manage the way customer data is used. ForgeRock envisages the future of identity management as acombination of people, services and things that are increasingly context-aware and, based on this combination of elements, allow different levels of access. ForgeRock asserts that the next generation IAM will become identity relationship management (IRM) with a focus on establishing end-to-end IoT/CIAM solutions with identity management coupled with IoT, consent and privacy controls. TechVision agrees with this relationship-centric IAMapproach.
As illustrated below, the ForgeRock Identity Platform heavily leverages AI and is intended to be comprehensive and simple-to-use. The platform includes full-suite IAM and identity governance and administration (IGA) capabilities that can be implemented across an organization for all identities (workforce, consumers, things), and offers feature parity across all delivery options, including on-premises, any cloud environment, and as a service.
Figure 8: ForgeRock’s Platform Overview
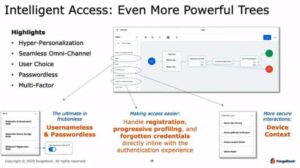
The ForgeRock Identity Platform consists of a series of modules built from open source projects, and is an identity administration and provisioning solution focused on managing relationships across users, devices and things. ForgeRock’s Intelligent Access model, based on their well-known “authentication trees” model, allows developer/ administrators integrating CIAM adaptive access (i.e., authentication and authorization) to use a visual, drag-and-drop interface to create/wire-in the adaptive flows. These adaptive flows are able to take into account myriad variables during the customer’s login process, including device, location, and so forth, as well as to wire-in the consent form, etc. Changes to the adaptive flows do not require any change to the actual client application code, making it very straightforward to modify underlying CIAM functions without impacting existing application distribution.
Some notable features in ForgeRock’s 7.0 release include:
- Username-less and password-less authentication – Supports password-less authentication leveraging biometric capabilities of the user’s registered/known device. This even allows for the omission of a user ID during authentication, and then can select the user ID / account to use after authenticating withoutproviding a user ID or This offers a more frictionless, ‘fast-lane experience’ means of authenticating. The user information is stored in OpenDJ, the backend ForgeRock directory service.
- Microsoft InTune integration to leverage mobile device management (MDM) information that can assist in user device
- Identity management functions infused directly into their Intelligent Access Trees
– user registration, progressive profiling and forgotten credentials can be handled directly in the workflow in order to maintain a more intuitive and streamlined user experience. This means that if a user forgets her password, she is not ‘dumped off’ in another code base that leaves the user ‘outside’ the initial authentication experience.
- Autonomous Identity – ForgeRock’s AI engine gives real time visibility into identity data, with a global view of identities, access review and autonomous remediation where risk-allowed and predictive provisioning. ForgeRock is increasing their use of AI and ML to “delight and protect” users (per ForgeRock), and continuously inspect and adapt real-time access based on user behavior and to orchestrate real-time response and
- Administration/Configuration UI improvements and enhancements, providing a ‘fast-lane’ for configuration and administration to streamline the overall administrative
Figure 9: ForgeRock Intelligent Access Trees
TechVision Research has assisted several large, global enterprises architect and deploy ForgeRock EIAM and CIAM components on public clouds (e.g., AWS and GCP) and on- premise. Overall, the experience has been positive and we feel that ForgeRock’s improvements in their 7.0 release will only enhance this experience. ForgeRock remains a strong CIAM and EIAM solution platform and bears consideration if your organization is embarking on a CIAM modernization program.
IBM
This is the first time IBM has made the TechVision CIAM short-list as they are in the process of modernizing many of their IAM and security services. For this report, TechVision had the opportunity to speak with Sean Brown, the Program Director for IBM’s Identity and Access Management solutions.
IBM has a long and storied past in the EIAM space and now has begun to venture into the burgeoning CIAMmarket. Do not discount IBM for being ‘late to the game’ The CIAM market is just beginning to take shape and IBMis likely to be a successful and influential contributor. Per IBM, about 50% of their customers are using their IAM platform for CIAM use cases, which is indicative of an increased focus in this area.
The existing IBM solution for both EIAM and CIAM is called IBM Cloud Identity. Their investment is focusing on the solution set known as IBM Cloud Paks, which are intended to be lightweight, enterprise-grade, modular cloud solutions, integrating a container platform, containerized IBM middleware and open source components, as well as common software services for development and management. IBM Cloud Paks are designed to run anywhere, are open and secure and consumable. Leveraging Cloud Pak foundation, the Cloud Identity IAM stack is built on top of Kubernetes infrastructure running on Docker containers so that it is dynamically scalable. The IAM platform is built on IBM’s RedHat, acquired in 2019, and this is further integrated with CloudPath on the OpenShift layer to enableZero Trust security services leveraging identity data. IBM provided the marketing overview graphic illustrated below.
Figure 10: IBM Cloud Identity Overview
IBM is investing in more cloud-native implementations of their IAM platform. The central theme of their platformis Continuous Access Control, which in a nutshell looks at the device, risk of the location, risks associated with the person/device/location/information risk level to determine access privileges during runtime. By incorporating IBM’s application gateway technology based on Docker, Cloud Identity allows applications to leverage a centralized policy framework for continuous access control.
Furthermore, by leveraging Trusteer, an acquisition by IBM in 2013, Cloud Identity identifies online fraud and determines if malware is present on the client machine. This has been integrated with the IAM platform to leverage Trusteer’s risk management capabilities. Together with the Cloud Identity access policy framework, IBM has taken a significant step forward in the area of adaptive access based on contextual awareness, AI and ML.
With Intelligent Governance – though not traditionally a CIAM set of capabilities, it bears mentioning that IBM has stepped deeply into the pool of Identity Governance and Administration (IGA) functionality.
With Identity Analytics, the Cloud Identity solution helps InfoSec understand who or what the outliers are, dormant accounts, over-provisioned accounts and so on are monitored and risk analyzed. This set of features can provide the bulkof the monitoring, analytics, reporting and remediation information an organization requires to detect and addressanomalies.
We are also encouraged that IBM Cloud Identity is building a comprehensive model for Decentralized Identity (DID). Over the past several months, TechVision has been briefed extensively on IBM’s Decentralized Identityproduct agenda, and during our briefing on their CIAM capabilities, it became even more apparent that IBM is taking the possibility (probability?) of a Bring Your Own Identity world based on DID very seriously. IBM offers a Tech Preview installation kit that allows customers to start prototyping on this platform now, making use of cryptographically secure verifiable claims to authenticate and authorize (based on claims data) both enterprise andcustomer users. From our perspective, this is one of the most advanced ‘sandboxes’ an enterprise can find to begin their DID on distributed ledgers journey.
So, it appears that this is not your grandfather’s IBM with respect to their CIAM (and EIAM) solution. The once-aging IBM Identity Management suite has been completely re-factored into a cloud-ready, currently tooled and forward-looking suite that should make most enterprise short-lists for deeper evaluation regarding meeting your CIAM requirements.
iWelcome
TechVision had the opportunity to interview Marco Venuti, VP of Product Management and Maarten Stultjens, VP Corporate Development to get an update on iWelcome’s current portfolio and roadmap. iWelcome has a strong, customer-friendly CIAM service with the primary limitation being geography: they primarily sell to and service organizations in Europe. As a European-centric CIAM provider they have a heavy emphasis on privacy, flexibility in terms of data residency and strong consent management capabilities. They also have strong marketing integration and progressive profiling capabilities.
iWelcome’s Identity as a Service (IDaaS) CIAM solution has traditionally provided a single- tenant private cloudCIAM (and B2B) infrastructure in the past, but is augmenting their value proposition by providing a multi-tenant cloud deployed on AWS. This new environment is completely “per-customer isolated”, with customer geographic region-specific data residency in support of GDPR. Of note is the fact that iWelcome will continue to support its single-tenant model for both existing customers and going forward for its customers that require a single-tenant cloud infrastructure. Also, of note is that iWelcome also provides a B2E (Enterprise IAM) IDaaS suite, which is outside the scope of this research document.
Figure 11: iWelcome High-Level Proposition Portfolio
The illustration above shows iWelcome’s high-level proposition portfolio, which provides a good level-set for where the company is focused. Of prime consideration is iWelcome’s growing relationship with AWS. With more of their own customers embarking on an AWS strategy, iWelcome is building new services on AWS to actively promote a multi-tenancy iWelcome solution offering. As illustrated above, their as-a-service product line iscomprised of:
- Customer Journey Management – this is the onboarding feature set that helps bring customers online andconvert website visitors to customers with a frictionless process. This process is supported by capabilities like social registration, account matching, identity verification and progressive profiling. These capabilities are offered via out-of-the-box templates or can be built and customized by developers using iWelcome’s
- Mobile SDK – supports secure and intelligent authentication natively into their customers’ apps via welcome’s API architecture. Using the Mobile SDK customers can add authentication to apps or update facilitates orchestration of customer journeys by changing registration, activation and progressive profiling flows.
- Consent Lifecycle Management (CLM) – All data information that is linked to consents and preferences are stored in this separate CLM module. This includesdata attributes, data values, consent information, processing purposes, the retention data and ‘consentable documents’ (documents that need consumer’s consent such as revised privacy policy documents). This information is captured and made available for self-service portals by RESTful APIs.
- eID – eIDAS is the EU-standard for electronic identification, which is implemented via domestic eIDschemes in In the Netherlands, the domestic scheme for eIDAS transactions is called eHerkenning. iWelcome supports a variety of organizations with its eHerkenning solution. As one of the founding partners of eHerkenning, iWelcome is certified by the Dutch Government since 2010
- RITM – This module is B2B-focused, supporting delegated administration, using roles and attributes. RITM provides a multi-level delegation model that allows its customers to onboard and manage business partners and applications through delegation, entitlements and customizations, according to the B2B relationship’s needs. In addition to traditional one-time-passwords (OTP) over SMS, iWelcome provides an MFA App, available for Apple and Android, which supports OTP as well as the more popular push/swipe (i.e., a push notification on the admin’s phone to accept or reject the authentication )
Core to these modules is iWelcome’s Identity Synchronization feature, which provides synchronization interfaces for users and groups:
- Inbound SCIM API to manage the intake of Identity and group information and relationship from externalsystems such as CRM, HR, AD, LDAP or any other Identity Management Systems or Master DataManagement
- Outbound Notification API to propagate user attributes and user consent changes for the integration with CRM, Marketing Automation or any other Identity Management
iWelcome has a very strong and growing European customer base. TechVision feels their IDaaS solution for CIAM is a very strong candidate that EU-centric enterprises should consider. Due to their focus on GDPR in particular and privacy in general, as well as their relatively robust set of features across their integrated modules and single-tenant and multi-tenant cloud deployment models, iWelcome should be viewed as a leader in the EU CIAM market.
Microsoft
This is the first time Microsoft is making TechVision’s vendor short-list in the CIAM area as they are ramping up their investments and adding to their core capabilities in this area. Microsoft via Active Directory (AD), Azure Active Directory (Azure AD) and Office 365 has a massive footprint in most enterprises and to a certain degree is an incumbent in many large organizations. This has resulted in Microsoft, in our consulting engagements (RFPs, RFIs, Short-lists) being considered as a CIAM provider, but historically not having enough of the core CIAM capabilities to emerge as a primary solution. So why is Microsoft now on our short-list? The short answer is that their combination of existing platform strengths, their current focus on CIAM with the Microsoft Azure Active DirectoryB2C offering, their roadmap and investments in the CIAM space and innovation in areas such as Decentralized Identity have them on our list.
Microsoft will certainly continue to partner with other organizations (or enterprises will simply integrate other services with their Microsoft portfolio) to address some of the gaps in their service offerings. For example, certain areas such as IGA may be more heavily relegated to partners at least for a while. Microsoft may also be attractive to organizations with large Microsoft bases that may benefit from the economics of licensing agreements supporting IAM services with a relatively modest (or no) incremental licensing investment.
Microsoft, like several of the vendors we interviewed, are increasing their investments in B2C scenarios and the overall ease of use and core set of IAM services. TechVision had the opportunity to interview Microsoft Identity and Security experts Pam Dingle, Director of Identity Standards and Alex Weinert, Partner Director of Identity Security earlier this year to better understand Microsoft’s Identity and Security strategy and roadmap. They described Microsoft’s 5 areas of focus for 2020 as being:
- Connect all applications and cloud resources to improve access controls and the user experience
- Enable boundary-less collaboration and automated access lifecycle for all users
- Go password-less to make security effortless for users
- Empower developers to integrate Identity into their applications and improve security
- Start your Zero Trust journey to protect your organization as you digitally transform
TechVision then had a Customer-centric IAM discussion with Robin Goldstein, the Principal Group PM Manager of Microsoft Identity in June, 2020. Robin was upfront in stating that Microsoft’s core focus (like many vendors) has been on the employee and partner side, but she highlighted that Azure AD B2C builds upon the core Identity platform with support for extensibility, branding, more consumer friendly and more mobile device friendly than the traditional offerings. She described that where Microsoft wants to be is with a “single technology stack”. She also described Identity as the “new control plane for security in the cloud” which TechVision certainly agrees with. The following chart summarizes Microsoft’s portfolio of current, preview and general investment areas for IAMcapabilities. This gives us a sense for the single technology stack Robin was highlighting.
Figure 12: Microsoft Critical Capabilities Summary
Note that while Customer IAM is a specific capability category within the overall Microsoft Identity and AccessManagement model, it also leverages the portfolio of core capabilities in their IAM suite. Areas like adaptive access, user and device authentication, SSO and other functions critical to Customer IAM users are within the Microsoft platform offering.
Microsoft’s increasing investment in CIAM is also evidenced by their new External Identities preview that offers self-service sign-on using social IDs such as Google and Facebook, the ability to customize user attributes and applylight branding, and API connectors that enable identity proofing, verification, and plug-in support for Decentralized Identifiers (DIDs). External Identities expands on the B2B collaboration capabilities in Azure AD by enabling self-service sign-up and greater flexibility to customize the user experience.
In summary, Microsoft is making significant progress in the CIAM space and is an option to consider for organizations that already have a large investment in Microsoft platform services. Microsoft may also be attractive to organizations with large Microsoft bases that may benefit from the economics of licensing agreements supporting IAM services with a relatively modest (or no) incremental licensing investment. While you may still use partner products and services, Microsoft continues to fill in the gaps in their CIAM portfolio.
Okta
Okta is a strong, scalable IDaaS solution. Okta has placed a major emphasis on supporting develops subsequent to their acquisition of Stormpath in 2017 with most technical/ APIs/federation capabilities addressed. Okta is a traditional Enterprise IAM vendor successfully moving to the CIAM space with an enterprise IDaaS-centric modelthat has been transformed to support CIAM. Okta continues to move towards a full portfolio of CIAM capabilitiesand intends to leverage as much as commonality as possible between enterprise user and customer use cases. Duringour recent interview with Okta’s Product Marketing Leader, Swaroop Sham, it was disclosed that CIAM account for approximately 25% of their revenue with a 70% YoY growth. These figures indicate that Okta is making an impact on the CIAM market and will likely garner a place on many enterprises’ vendor short-lists, especially if they are already deploying Okta for their B2E IAM. Okta’s CIAM platform overview is illustrated below
Figure 13: Okta CIAM Platform Overview
As illustrated above, some of the important capabilities that the Okta CIAM platform supports include:
- Adaptive MFA – Leverages a range of password-less authentication options for customers using email magic links, WebAuthN or factor
- Lifecycle Management – enables the customer onboarding journey including progressive profiling and consent
- Access Gateway – enforces location, device and network
- API Access Management – Controls which apps and APIs users and developers have access to using attribute-based policies enforced through SAML and OAuth 2 protocols. This module can be integrated with many of the leading API gateways, including Apigee, AWS, Google Cloud, MuleSoft, NGNIX and more.
- Authentication – Granular user, group, app and contextual sign-on policies that can be paired with password complexity and logout experience requirements. Authentication can be embedded into customer apps with open standards such as SAML and OIDC. This can also be used to connect users to 3rd party cloud apps using over 6,000 pre-built SaaS integrations. Additionally, password-less authentication using an email-based “magic link” is supported. From a user behavior analytics standpoint, Okta establishes a baseline login behavior for each individual user, and responds to anomalous activity with the appropriate set of strong factors for both high and low risk login
- Authorization – Assign granular application-level access controls using easy-to- administer application entitlement policies that can be assigned to groups of users without having to write
- User Management – Create and manage customer profiles and assign access rights via the Okta User Admin Console or via
- User Content – Allows downstream 3rd-party applications to prompt users for permission to access a set of entitlement scopes. User consent remains valid until users choose to revoke these
- Advanced Server Access – this is Okta’s privileged access management (PAM)
solution for administering and configuring the Okta environment, supporting MFA.
- Universal Directory – Marketed as a highly scalable cloud-based user store to manage all customer users, groups and devices, mastered in Okta or from authoritative sources.
Swaroop shared the figure below as he described a typical CIAM journey.
Figure 14: Okta’s CIAM Customer Journey
As shown above, Okta’s partnership with OneTrust and DataGrail enables the CIAM platform to manage customer privacy and consent much more granularly and can automatically propagate updated consent preferences across all relevant apps in real time
As illustrated above, there is a good deal of functionality that Okta views as being shared across customer-centric use cases. With Okta the proverbial 800-pound gorilla in the IDaaS enterprise market coupled with the significant investment they are making in the CIAM market, they are sure to be on many enterprise vendor short-lists.
Ping Identity
As TechVision reported in our CIAM report 18 months ago; Ping Identity has a viable CIAM solution that leverages their traditional IAM capabilities paired with their developer- friendly, API-oriented platform from their acquisitions of UnboundID and Elastic Beam. The challenge 18 months ago was the capabilities gap between their on-premiseand cloud-based CIAM offerings. Ping has traditionally provided strong integration and federation capabilities, but has expanded their cloud and hybrid capabilities over the past few years.
For an enterprise that has Ping-centric IAM services (and there are many) this is a solid offering and should beconsidered. As Ping continues to build out its core platform to support CIAM-centric services, it should also be considered for customers without an existing Ping base. Ping has clearly elevated their offerings over the past 18months.
TechVision had the opportunity to have a briefing with Loren Russon, Vice President of Product Management at Ping Identity. As a public company, Ping has shown good growth, which we feel bodes well for its customers, given that a strengthening revenue stream is an important metric for long-term vendor viability. Ping currently has over60% of the Fortune 100 within their customer base and they have a strong footprint in the largest US banks, pharmas and retail organizations.
The CIAM market share for Ping is growing around their PingOne and PingCloud services, which offer both public and private SaaS models. They have a sizeable number of channel partnerships, including Accenture, PwC, Deloitte, Optiv – reporting over 300 such partnerships worldwide.
Customer360 is their CIAM authentication solution package, which is meant to address broader business problemswhile providing a lower overall price point. The solution package includes authentication, directory, multi-factor authentication, and delegated administration functionality, alongside professional services, 3rd party integrations and more. Ping’s solutions are a templatized means of offering core underlying code that enables a CIAM solution that is built on a uniform, core set of IAM services offered by Ping. This differentiation is important as Ping isoffering a core platform that supports CIAM as opposed to a CIAM-specific platform.
Figure 15: Ping Product Roadmap Themes
The in-cloud or on-premise models can be deployed selectively, in a hybrid manner. The key takeaway fromPing’s strategy is the ability for their customers to selectively deploy software and services in an architecture that best fits their customers’ organizations (i.e., cloud, on- premise, SaaS, etc.) It is apparent that Ping is continually investing in developing their cloud platform on PingOne in order to better meet their customers’requirements for a flexible and effective CIAM platform
Figure 16: Ping Platform/Capability Alignment
While still a leading enterprise IAM solution vendor, Ping is focusing more heavily on CIAM. They have described the “customer journey” to facilitate:
- Customer acquisition and retention – The CIAM focus across the industry is “user experience”, and Ping appears to have received that memo, too, with an increased emphasis on simplification of the user registration and login processes that they believe attracts and retains
- Loyalty and revenue – A big part of the user experience improvements occur after sign-on and center onincreased personalization across multiple access channels that assist in building longer-term brand
- Trust – Ping’s CIAM services aim for giving customers as much control as possible of their data to adhere to privacy regulations and build trust via fine-grained access controls.
The foundational CIAM customer database resides within Ping Directory—the PingOne for Customers cloud data store can also be leveraged—intended to enable centralized user profile management. Taking an “API first” approach, the platform supports microservices and DevOps automation in driving modern application development. They offer APIs for all services to make it relatively straightforward to embed CIAM functionality into applications, including MFA, continuous and adaptive authentication, consent management and self- service.
Adaptive authentication features allow customers to link and manage trusted devices so they can securely login to applications using a face scan, fingerprint and other authentication methods. Using their mobile SDK, Ping’s customers can use their own branded mobile applications to enable password-less sign-on without having to download or use a third- party MFA application.
Expanding their vision of customer centricity, Ping, who acquired ShoCard in early 2020, will be investing in the Decentralized Identity model. We’ve covered ShoCard in several of our reports examining this disruptive model. While details of how this will look are not yet available, TechVision will be watching these developments closely and will keep you apprised of Ping’s direction and offerings in the Decentralized Identity space.
While Ping has had challenges over the past few years in expanding on their base strengths in the EIAM/federation areas while building out their CIAM offering, moving to an annuity contract service model and migrating services tothe cloud, we feel much more positive about their strategy and execution going forward. We feel that Ping has achieved solid footing in 2020 with their hybrid deployment model and much improved focus on key CIAM requirements. We now have seen that Ping is clearly focused in the right direction, their solutions have matured to better meet the needs of the industry and their channel partnerships have grown and strengthened to the point that we feel Ping is a viable option for many organizations CIAM and EIAM needs.
SAP
The SAP Customer Data Cloud (former Gigya platform) is a well-proven CIAM solution and SAP’s acquisition hashelped SAP/Gigya remain a leader in the IDaaS CIAM market with a few caveats. SAP’s CIAM offering is called SAP Customer Data Cloud (CDC), a cloud-based IDaaS service offering. TechVision had the opportunity to speak with SAP’s Adrian Nash, Head of Product for Customer Data Cloud, Sonny Dasgupta, Head of Product Marketing and Ratul Shah, Senior Director of Product Marketing. Certainly, for an enterprise that runs the majority of its back-office IT infrastructure on SAP software and wants to integrate its customer-facing e-commerce or support platforms with that SAP environment, SAP Customer Data Cloud should be one of the first CIAM solutions considered. To further support this, our recent briefing highlighted the trend that SAP has a new vision that bundlesCDC with SAP’s commerce, marketing, sales and service offerings to foster a more complete journey for CIAM relationships, in all four corners of the globe.
Figure 17: SAP’s Key Differentiators
As shown in the graphic above, SAP has invested in developing “global access”, which harnesses the increased scope, intelligence and modularization that can provide a low- latency, single identity that is accessible globally. Their UI is focused on enabling multi- channel registration and login to improve the customer experience. Integration with SAP- supported end-to-end business processes extends CIAM out to multiple customer experience solutions and services. In addition to investing in global access, SAP has improved several key capabilities driven by their customers’ requests, including:
- Native push authentication in support of MFA, as well as support for phone number login
- Enrichment extensions to better enable progressive profiling of customer data
- Consent documents and support for CCPA, in addition to GDPR
- More out-of-the-box connectors to source and target customer-centric systems to ease integration wherever
This level of focus has begun to help SAP improve the large-scale, end-to-end customer experience for SAP’s largest customers. As example, SAP mentioned a large, global CPG company, who has over 23,000 web sites and digital properties that they collect customer data from. Already a sizeable customer of SAP’s products and services, the company makes an excellent example of how the SAP Customer Data Cloud extends the CIAM environment in an integrated multi-product and customer data management way. That said, SAP is still early in its quest to fullyintegrate the CDC and overarching SAP worlds. We’ll continue to monitor progress in this area and keep our clientsadvised.
Even though the initial push is for SAP-centric clients (based on our direct observation since several of our large consulting clients also being SAP shops), it is important that we stress that CDC may also be a good fit forenterprises that are not so SAP-centric, or run little or no SAP at all. With Gigya’s pedigree as a bona fide technology agnostic CIAM platform, CDC can be a good candidate, as well. We have assisted in the design and deployment of CDC in organizations that are not running their business on SAP, and the user experience on multi- channel interfaces has been good.
Nevertheless, as we have stated previously in our research, there are often pitfalls when a larger, established company acquires a successful smaller company in that the original heterogeneity begins to suffer as the acquired platform gets swallowed up within the big vendor’s homogenous ambition. Time will only tell if that is whathappens to Gigya, but as of this writing, the level of autonomy of the Gigya platform is still strong and has not been diluted by the acquirer.
Salesforce
TechVision had the opportunity to speak with Ian Glazer, Vice President, Identity, Privacy and Data Governance Product Management at Salesforce in order to gain a current understanding of Salesforce’s CIAM capability and strategy. Given the strategy, direction, standards support and integration capabilities Salesforce has made our short-list.
Salesforce.com is a premier SaaS-based CRM solution, and in concert with this solution they offer Salesforce Identity is an IDaaS platform, competing with Gigya/SAP, Janrain/Akamai and iWelcome. That said, with the largest repository of customer data already residing in their platform, Salesforce has the opportunity to provide a rich set of integrated CIAM services that will be hard for others to match. Their overall platform structure is illustrated below.
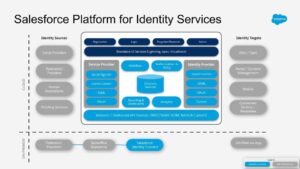
Figure 18: The Salesforce Platform
The biggest question we had in assessing Salesforce was how serious they are in building out an integrated CIAM service and Ian described a comprehensive and well thought out plan and program. They are positively answering our questions. Salesforce Identity provides a deep and rich set of core identity services including the followingfeatures.
- Cloud-based user directories, so user accounts and information are stored and maintained in one place, while available to other services or
- Authentication services to verify users and keep granular control over user access. Organizations can requiretwo-factor authentication, select which apps users can use, and set how often individual users log in to maintain their
- Access management and authorization for third-party apps, including UI integration,
so, a user’s apps and services are readily available.
- Application user provisioning, which streamlines the process for providing and removing access to apps to multiple users
- An API for viewing and managing Identity
- Identity event logs for creating reports and dashboards on single sign-on (SSO) and connected app
- Salesforce Identity Connect for integrating Microsoft Active Directory (AD) with Salesforce. Identity Connect allows you to manage AD users and Salesforce users simultaneously. You can configure Identity Connect to give AD users access to their Salesforce orgs without logging in
To implement Salesforce Identity, enterprises can use any of the following standards and other means of interfacing with their services:
Security Assertion Markup Language (SAML) – SAML is an XML-based protocol that allows you to transfer userinformation between services, for example, from Salesforce to Microsoft 365. Note that often Microsoft is an IDP to Salesforce. Apps use this information to authorize users and enable SSO. Salesforce supports SAML for SSO into Salesforce from a corporate portal or identity provider.
OAuth 2.0 – OAuth 2.0 is an open protocol used to allow secure authorization between apps. OAuth authorization flows describe the options for implementing OAuth in Salesforce orgs.
OpenID Connect – Open ID Connect is an authentication protocol based on OAuth 2.0 that sends identity information between services. With OpenID Connect, users can log in to another service, like Gmail, and then access their Salesforce org without logging in again.
My Domain – My Domain allows enterprises to define their own domain name within the Salesforce domain (for example, https://companyname.my.salesforce.com). My Domain makes it easier to manage login and authentication and allows for the customization of the consumer login page.
Connected Apps – A connected app is a framework that enables an external application to integrate with Salesforce using APIs and standard protocols, such as SAML, OAuth, and OpenID Connect. Connected apps use theseprotocols to authenticate, authorize, and provide single sign-on (SSO) for external apps. The external apps that areintegrated with Salesforce can run on the customer success platform, other platforms, devices, or SaaS subscriptions.
App Launcher – The App Launcher gives customer users straightforward access to apps that they use most often. Users go to the App Launcher to launch Salesforce, on-premises, and connected (third-party) apps without logging in again (e.g., single sign-on). The App Launcher displays tiles that link to the available apps.
Salesforce Identity Connect – Identity Connect integrates Microsoft Active Directory (AD) with Salesforce. User information entered in AD is shared with Salesforce instantaneously. Companies that use AD for user managementcan use Identity Connect to manage Salesforce accounts.
Two-Factor Authentication – When two-factor authentication is enabled, users are required to log in with two piecesof information, such as a username and a one-time password (OTP). Admins enable two-factor authentication through permissions or profile settings. Users register for two-factor authentication through their own personal settings or they can use an OTP generator app, such as Salesforce Authenticator or Google Authenticator. They also offer support for hardware devices, such as U2F security keys. With two-factor authentication enabled, users are required to log in with two pieces of information, such as a username and a one-time password (OTP). Salesforce supports user-defined OTPs and OTPs generated from software or hardware devices. Their goal, per Ian, is to have everyone using multi-factor authentication.
TechVision believes Salesforce Identity is a robust IDaaS that would bring CIAM capabilities to bear quite readily for enterprises who already run their CRM on Salesforce. Ian Glazer is clearly a thought-leader in IAM identerati circles, and has been at the helm of the Salesforce Identity product management group for several years. It is clear that Salesforce Identity is a well-designed platform and its ability to readily integrate with the CRM solution is a key differentiator.
Other CIAM and partnering vendors to be considered
In addition to the previously mentioned short-list vendors there are other quality offerings to consider to support your CIAM program that may rise to the top for your organization based on your current environment and business priorities. These vendors include Google, Amazon, and Radiant Logic. All of these vendors can be a viable part of an organization’s CIAM program (and an extension of our short list) under certain conditions.
Google and Amazon also seem to be logical candidates for any customer-facing program given their world-class scale and pervasive cloud-based services. Building CIAM services within these platforms is a viable solution, but again this won’t be a full-featured CIAM service without a lot of custom development and/or partnerships.Organizations with heavy DevOps and cloud-first strategies may still build their CIAM programs on top of the Google Identity Platform or Amazon Cognito services, but this will generally take a lot of work. Other vendors worth consideration are LoginRadius, Auth0 and Micro Focus.
Radiant Logic is vendor that can support identity integration capabilities as organizations build out their CIAMprogram, but is not a stand-alone CIAM solution. Radiant Logic boasts a strong virtual directory platform and identity data integration solution enabled by their Identity Correlation Service (ICS), which provides a plethora ofout-of-the-box connectors to authoritative source and target systems through a combination of virtual (real-time) integration between authoritative source systems. Their solution can also add to the relationship management and correlation capabilities that may not be as robust within the selected CIAM vendor’s portfolio.
We’ll close with some final thoughts about vendor selection and how TechVision can further support our clients in this area. First, the CIAM space is moving at Internet speed and updated vendor information is always available from TechVision for our clients via dialogues/inquires. We develop the vendor short-list summary to provide a summary assessment of the vendors as a starting point, but we have deep information and additional perspectives on virtually every vendor in this space. TechVision is also available for more detailed consulting including the development of RFIs/RFPs, supporting the collection of cross-functional requirements and to support the development of your CIAM reference architecture. Our team has done over 1,000 enterprise consultingengagements in the IAM space and we are happy to further support our clients in all areas related to CIAM and IAM in general.
Conclusions/Action Plan
The Digital Enterprise requires consistent, clear, and secure identity management for every user, device, process andasset across all lines of business. Identity management is the ability to set up and manage the relationships between users and things and to enforce rules for access and security. At its simplest, identity management must answer two questions: who/what are you, and what can you do?
These sound simple but have never been more complicated. Nor have the stakes ever been higher. For enterprises,the ability to manage the digital identities of every contributor, every customer, and every prospect is a fundamental requirement to realize the full benefits of cloud computing, mobility, and the Internet of Things (IoT)…and to do it securely for your enterprise and for your customers.
The bottom line is that every person (or “thing”) of interest to the business must be able to be identified, access the resources they need to produce, buy, use, and recommend the products and services of the company. And the business must be able to leverage the data generated by these customer interactions to help build customer relationships and grow revenue.
CIAM is a foundational capability to achieve transformation and is a major priority for most of our clients. While there are several vendors that can help support this foundation, there are some recommendations TechVision highlights for all of our clients.
So, what should you be focusing on as you build out your CIAM program? Remember not making a decision is making a decision and investments in the CIAM space are highly encouraged for most of our clients. We’ll concludethis report with 7 next steps to get the ball rolling with your CIAM program:
- Start with a clear understanding of requirements – Customer engagement requires that the CIAM platform supports a responsive customer experience across various digital business The people closest tothe customers should be the conduit to this knowledge and should be engaged in the process.
- Progressive profiling not “all or nothing” – Customers are willing to give more information as the relationship deepens and value increases. Think of the customer profile as a representation of the state of the relationship; the more the customer willingly shares, the deeper the
- Inclusion vs exclusion – Traditional IAM is about protection – keeping the bad guys at bay. CIAM is about inviting people in. While security is important, it cannot be a barrier to
- Enterprise IAM should be on the team, but shouldn’t be leading the project – As the
old saying goes, “When all you have is a hammer, everything looks like a nail”. While the identity processes look similar for employees and customers, they are different and should be led by the businesses with a customer focus, not the technical people who may have a tendency to try to fit the customer into a familiar model.
- Customer and employee relationships are different – The enterprise can define and enforce the relationship between the enterprise and the employee. The enterprise enforces the rules. Customers are increasingly in charge of not only the relationship, but the rules as well. Regulations such as GDPR are redefining the roles by putting the customer in
- Pay attention to privacy – Privacy and proper handling of customer data is an expectation, not an option. Not only is the company liable, but customer trust can be lost in an instant and take years to
- Correlation and context are important – Understanding the various connections the customer has with your enterprise are keys to customer engagement. How they prefer to communicate, how they are represented in various business functions, and how valuable they are to the business are all connected through a proper CIAM infrastructure.
As always, we encourage your feedback and are available to discuss any of these topics and how they apply to your organization. Good luck in this critical area.
About TechVision
World-class research requires world-class consulting analysts and our team is just that. Gaining value from research also means having access to research. All TechVision Research licenses are enterprise licenses; this means everyone that needs access to content can have access to content. We know major technology initiatives involve many different skill sets across an organization and limiting content to a few can compromise the effectiveness of the teamand the success of the initiative. Our research leverages our team’s in-depth knowledge as well as their real-world consulting experience. We combine great analyst skills with real world client experiences to provide a deep and balanced perspective.
TechVision Consulting builds off our research with specific projects to help organizations better understand, architect, select, build, and deploy infrastructure technologies. Our well- rounded experience and strong analyticalskills help us separate the “hype” from the reality. This provides organizations with a deeper understanding of the full scope of vendor capabilities, product life cycles, and a basis for making more informed decisions. We also support vendors in areas such as product and strategy reviews and assessments, requirement analysis, target market assessment, technology trend analysis, go-to-market plan assessment, and gap analysis.
TechVision Updates will provide regular updates on the latest developments with respect to the issues addressed in this report.
About the Authors
 Gary Rowe is a seasoned technology analyst, consultant, advisor, executive and entrepreneur. Mr. Rowe helped architect, build and sell two companies and has been on the forefront the standardization and business application of core infrastructure technologies over the past 35 years. Core areas of focus include
Gary Rowe is a seasoned technology analyst, consultant, advisor, executive and entrepreneur. Mr. Rowe helped architect, build and sell two companies and has been on the forefront the standardization and business application of core infrastructure technologies over the past 35 years. Core areas of focus include
identity and access management, blockchain, Internet of Things, cloud computing, security/risk management, privacy, innovation, AI, new IT/business models and organizational strategies.
He was President of Burton Group from 1999 to 2010, the leading technology infrastructure research and consulting firm. Mr. Rowe grew Burton to over $30+ million in revenue on a self-funded basis, sold Burton to Gartner in 2010 and supported the acquisition as Burton President (now Gartner for Technical Professionals) at Gartner.
 Doug Simmons brings more than 25 years of experience in IT security, risk management and identity and access management (IAM). He focuses on IT security, risk management and IAM. Doug holds a double major in Computer Science and Business Administration.
Doug Simmons brings more than 25 years of experience in IT security, risk management and identity and access management (IAM). He focuses on IT security, risk management and IAM. Doug holds a double major in Computer Science and Business Administration.
While leading consulting at Burton Group for 10 years and security, and identity management consulting at Gartner for 5 years, Doug has performed hundreds of engagements for large enterprise clients in multiple vertical industries including financial services, health care, higher education, federal and state government, manufacturing, aerospace, energy, utilities and critical infrastructure.