Axiomatics Aims for Access Autonomy
Publication Date: 15 April 2025
Abstract
This is the second of a series of reports on specific vendor offerings that enterprises should consider as they modernize their Identity and Access Management (IAM) foundation. In this report, we’ll review Axiomatics, a tenured company focused on externalizing user access control policy and decisions from applications in multi-cloud environments.
More and more, access decisions are being made at runtime based on the best data that can be quickly assembled. Such runtime authorization mechanisms often implement what’s called Attribute-Based Access Control (ABAC) methods for determining access rights when a user or agent is attempting to interact with specific applications and data. Using an ABAC model as its foundation, Axiomatics’ mission is to “securely connect people and information through runtime authorization” with a vision to “enable every organization in the world to enforce Zero Trust access.” Nearly 100 percent of the company’s customer base is comprised of Global 1000 organizations, showing a proclivity for helping to solve complex access issues in large enterprises across all the major market verticals.
In this report, we explore in detail the Axiomatics Authorization Hub and set of tools that bring externalized authorization to bear. We’ll then conclude with a set of pragmatic recommendations and an enterprise action plan for improving enterprise access control capabilities via Axiomatics deployment.
Authors:
| Doug Simmons Principal Consulting Analyst [email protected] |
Gary Rowe CEO / Principal Consulting Analyst [email protected] |
Executive Summary
Runtime authorization to access IT assets has always been a challenge. We know, as we’ve been working in this space for our entire careers. Applications always seem to have their “own way of doing things” when it comes to granting user (or agent) access.
TechVision Research recently had the opportunity to speak at length with David Brossard, Axiomatics’ Chief Technology Officer (CTO). The purpose of this meeting was to understand Axiomatics’ (axiomatics.com) approach to runtime authorization and how their approach differs from the many of the existing vendors in this space. We also wanted to get a sense for Axiomatics’ roadmap and vision.
Axiomatics was founded by a team of researchers at the Institute of Computer Science in Stockholm, Sweden in 2006. Headquartered in Stockholm, this 60-person company has executive and sales offices in North America (Chicago) and development offices in Athens, Greece. Numerous distributors partner with Axiomatics to support field sales and implementation, as well.
Axiomatics’ mission is to “securely connect people and information through runtime authorization” with a vision to “enable every organization in the world to enforce Zero Trust access.” Nearly 100% of the company’s customer base is Global 1000, showing proclivity for helping to solve complex access issues in large enterprises across all the major market verticals. Their 95% Net Promoter Score (NPS) indicates that they maintain a very high degree of customer satisfaction and loyalty. Axiomatics also claims to be a “100% partner-driven culture” and has an impressive list of partners that includes technology partners such as SailPoint and CrowdStrike, integration partners such as Accenture, Deloitte, KPMG, PwC and IC Consult; and several resellers including Optiv and NovaCoast. A complete partner list is provided at https://axiomatics.com/partners#partner-directory.
From its inception, Axiomatics has been a strong proponent of Attribute Based Access Control (ABAC) as the foundation for enabling granular runtime access based on identity attribute values maintained in the enterprise IAM environment and resource attribute values maintained in the target system of records. It is noteworthy that TechVision Research has long been an arch supporter of ABAC as the most effective means of access management based on identity attributes that immutably indicate a person’s (or agent or thing (i.e., “subject”)) current affiliation with the enterprise. We consistently advocate “loose coupling” of the various components of the IAM infrastructure using standards-based approaches that help eliminate vendor lock-in. Our experience of over 30 years designing and implementing IAM capabilities has led us to believe that the ability to rapidly “rip and replace” various components of the infrastructure – especially as burgeoning “as a service” (SaaS) models for authentication and authorization continue to emerge. For this reason alone, we find Axiomatics’ ABAC-centric approach to runtime authorization to be particularly interesting and promising.
- Axiomatics has considerable “street cred” when it comes to access control externalization. Some might argue that “they wrote the book” on the topic with their foray into the world of the extensible access control markup language (XACML) almost 20 years ago.
They continue to expand and improve their offering by focusing on the simplification of policy management – an admirable undertaking, to say the least. For this year (2025), they are moving away from multiple tools toward a comprehensive control plane within the Authorization Hub. Some of the interesting product plans include the development and release of a requirements-gathering component, as well as enhanced policy testing, deployment, and policy review.
Their impressive set of capabilities should enable customers to extend their Zero Trust frameworks to include authorization policy standardization and integration. While federated SSO has become completely ubiquitous, the same level of cross-domain interoperability of access controls has not been as successful. We expect this to improve, and companies like Axiomatics, with their dogged determination to get this right and make it happen are a shining light.
While most of our review of their solution has been decidedly “enterprise-centric”, Axiomatics is also seeing growing adoption in the Customer IAM (CIAM) market. Perhaps this is in part because the CIAM space consists of more homegrown than COTS applications, and the opportunity to create a robust access control policy framework like the Authorization Hub enables is more conducive to CIAM, initially. Many of our customers start small and grow, rather than boil the ocean from the outset – thanks in part to our advice given to them.
TechVision recommends a structured approach to identifying key access control risks across this spectrum and has developed a Reference Architecture that is very useful in evaluating the set of capabilities necessary for your future state access control foundation. With over 30 years of helping our customers identify and mitigate these identity-centric risks, TechVision can help with this process.
Introduction
More and more, access decisions are being made at runtime based on the best data that can be quickly assembled. Such runtime authorization mechanisms often implement Attribute-Based Access Control (ABAC) methods for determining access rights when a user or agent attempts to interact with specific applications and data.
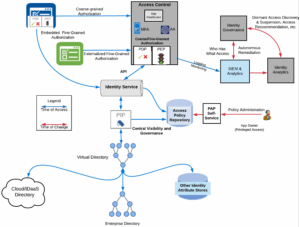
This capability relies primarily on attributes associated with a user, agent, or thing (subjects) that are inputs into the runtime decision of whether a subject may access a given resource in a particular way. Attributes of the resource are also considered in the decision-making process. Note that role-based access control (RBAC) can also be implemented as a specialization of ABAC. Fine-grained authorization systems principally involve a “PEP” and “PDP”. The PEP (Policy Enforcement Point) intercepts a user’s, application’s, or device’s access request to a resource, then makes a decision request to the PDP (Policy Decision Point) to obtain the access decision (i.e., access to the resource is approved or rejected), and acts on the received decision. The PDP evaluates access requests against authorization policies before issuing access decisions. The PDP often interfaces with the IAM directory, one of the many possible Policy Information Points (PIP), to access information about the user or device in question to inform its decision-making process. An illustration of the National Institute of Standards and Technology (NIST) Special Publication 800-162 ABAC architecture is shown below.
Figure 1: NIST ABAC Architecture (Source: Axiomatics)
Using this model to show the level of interaction between components of the runtime authorization process within TechVision Research’s Adaptive Authorization Capability Pattern is shown below.
Figure 2: TechVision Research Adaptive Authorization Capability Pattern
Adaptive authorization matches risk with request by evaluating additional environmental conditions, using risk score as a factor in dynamically determining authorization decisions. This set of capabilities is explained in detail in TechVision’s report titled, “Architecting and Managing Hybrid and Cloud-based Identity Services”.
To be clear, TechVision Research has long been an advocate of “loose coupling” of the various components of the IAM infrastructure using standards-based approaches that help eliminate vendor lock-in. Our experience of over 30 years designing and implementing IAM capabilities has led us to believe that the ability to rapidly “rip and replace” various components of the infrastructure – especially as burgeoning “as a service” (SaaS) models for authentication and authorization continue to emerge. For this reason alone, we find Axiomatics’ ABAC-centric approach to runtime authorization to be particularly interesting and promising.
TechVision Research recently had the opportunity to speak at length with David Brossard, Axiomatics’ Chief Technology Officer (CTO). The purpose of this meeting was to understand Axiomatics’ (axiomatics.com) approach to runtime authorization supports key customer requirements and how their approach differs from many of the existing vendors in this space. So, with this brief introduction to runtime authorization, we now look at Axiomatics and its distinctive approach.
Axiomatics Background
Axiomatics was founded by a team of researchers at the Institute of Computer Science in Stockholm, Sweden in 2006. Headquartered in Stockholm, this 60-person company has executive and sales offices in North America (Chicago) and development offices in Athens, Greece. Numerous distributors partner with Axiomatics to support field sales and implementation, as well.
Axiomatics’ mission is to “securely connect people and information through runtime authorization” with a vision to “enable every organization in the world to enforce Zero Trust access.” Thirty percent of the company’s customer base is Global 1000, showing proclivity for helping to solve complex access issues in large enterprises across all the major market verticals. Their 95% Net Promoter Score (NPS) indicates that they maintain a very high degree of customer satisfaction and loyalty. Axiomatics also claims to be a “100% partner-driven culture” and has an impressive list of partners that includes technology partners such as SailPoint and CrowdStrike, integration partners such as Accenture, Deloitte, KPMG, PwC and IC Consult; and several resellers including Optiv and NovaCoast. A complete partner list is provided at https://axiomatics.com/partners#partner-directory.
TechVision has been following the company’s journey closely when one of our most respected former colleagues from Burton Group, Gerry Gebel, joined Axiomatics as the President of Axiomatics Americas. For many years, we worked closely with Gerry in raising awareness of “federated identity” standards such as SAML (Secure Assertions Markup Language) and XACML (eXtensible Access Control Markup Language), beginning in the mid-2000s.
Since then, SAML has become the de facto standard underpinning federated single sign-on (SSO) standards like OpenID and OAuth. Today, virtually every website one traverses uses a SAML-based cross-site authentication model. It took about five years for SAML to gain root, but XACML has taken a bit longer due to issues principally centered on complexity of the standard and a slow adoption of “externalized authorization” by major application vendors. But headway is being made and as we’ll discuss in this report, a new era of cross-domain, federated authorization may be upon us at last.
We were fortunate to have an in-depth conversation with David Brossard, Axiomatics Chief Technology Officer (CTO) very recently. During this briefing, we were able to dive deep into the key capabilities of both the current product suite and the near-term roadmap. We share our findings in the next section.
Axiomatics Access Control Foundation
From its inception, Axiomatics has been a strong proponent of Attribute Based Access Control (ABAC) as the foundation for enabling granular runtime access based on identity attribute values maintained in the enterprise IAM environment. It is noteworthy that TechVision Research has long been an advocate of ABAC as the most effective means of access management based on identity attributes that immutably indicate a subject’s (person, agent or thing) current affiliation with the enterprise. The subject’s attributes, as maintained in the identity management system, become the “source of truth” and are used by runtime authorization engines to determine if access should be granted or denied. The policies that determine the subjects’ access during runtime rely on the subject’s specific attribute values to make their decisions, which we will discuss in more detail further on.
Axiomatics’ runtime authorization model is also referred to as “Orchestrated Authorization,” which is intended to enable IAM teams to establish policy guardrails while enabling developers, DevOps, and DevSecOps teams, as well as application owners, to author, test, deploy, and analyze policies.
This approach helps their customers align to a Zero Trust strategy by creating policy visibility that can accelerate application development that is adherent to access policies unique to the customer. In this regard, the company promotes itself as being attractive to both “business users” and “developers”. Consistency and granularity of access policies across multiple business domains helps their customers maintain and improve regulatory compliance, intellectual property protection, development efficiency and cost reduction, and user experience – among many other advantages.
The Orchestrated Authorization approach is centered on helping their customers achieve an authorization vision that can support “every application and resource in their technology environment.” Axiomatics vision for this is illustrated in their high-level visual below.
Figure 3: Axiomatics Orchestrated Authorization Overview (Source: Axiomatics)
Why ABAC?
For the better part of the “computer age” going back to the 1960’s, subject authorization has been largely based on membership in access control “groups”. Group objects are merely lists of identities that can be used to grant or deny access. If one’s identity is in a specific group that has access to a system, network or application, then access is granted. Group objects are “static lists”. Membership to existing groups is typically assigned during initial subject account provisioning or because of a specific access request to the system, network or application “owner” (if one exists). Groups are by their nature, stale – meaning, they often have subject identities in them that are no longer working for the company, have changed jobs within the organization and no longer should have access, and so forth.
There are myriad reasons that group lists get stale quickly. Many organizations do not have the capability to continually cull through the thousands – if not tens of thousands of groups that have sprung up over the course of decades. The update process is not only arduous, but also often not consistently followed in most enterprises.
ABAC, on the other hand, is often referred to as a “dynamic” grouping. Simply put, if you and I both have an attribute named “department” and we both have the value “accounting” in that attribute, we are effectively members of a group called accounting. Even there is no actual group object by that name (accounting), the fact that we both have the same value for this attribute effectively “groups us”. The dependency is on the Identity Governance and Administration (IGA) controls to ensure the attribute values are up-to-date and reflect “the current, accurate affiliation” of the subject to the enterprise. Keeping key subject attributes up to date by automating data synchronization or virtualization is a contemporary, effective means to ensure attribute accuracy. This is typically much easier to accomplish on an automated basis than static group management for tens of thousands of large enterprise groups whose purpose or ownership is often no longer understood or maintained, respectively.
A similar set of challenges to Group Based Access Control (GBAC) is apparent in the model known as Role Based Access Control (RBAC). Like groups, subjects can be assigned specific organizational roles (e.g., “accounts payable clerk,” “developer,” “HR administrator,” etc.) when first hired or transitioning to a new job within the organization. Myriad challenges with enterprise role definitions that are “consumable” by multiple systems and applications would warrant a TechVision report on this set of challenges alone. Suffice it to say, role engineering projects are often defined by significant challenges like “role explosion” (too many roles), managing complex role hierarchies, and ensuring flexibility in dynamic environments, as well as potential security risks from over-permissioning or misusing roles.
Even so, it should be recognized that a “role” is simply an attribute, just like any other attribute maintained within the IAM infrastructure. In the ABAC model we’ve been discussing, a role attribute can be used in addition to other subject attributes to make an access control decision during runtime. This means “role + other attributes” can be useful for runtime access decisions, while the role attribute by itself might not be the single access determining factor because the assigned role is (typically) not granular enough.
So, Axiomatics promotes ABAC as the “modern approach to authorization”, and we tend to agree. In summary, ABAC enables:
- Externalization – Authorization is managed outside the protected applications in a coherent and consistent way.
- Runtime implementation – Authorization decisions are evaluated at runtime when the user is attempting to access the protected resource.
- Granularity – Authorization considers the identity of subjects as well as resource and contextual data.
- ReBAC – The relationship between users and resources is used to define whether access should be granted.
Now, let’s dive into Axiomatics’ product suite, starting with the foundation: the Authorization Hub.
The Authorization Hub
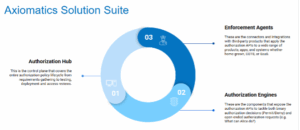
The solution suite is centered on the Authorization Hub control plane, as illustrated and described below.
Figure 4: The Axiomatics Solution Suite (Source: Axiomatics)
Axiomatics is sold as a single suite consisting of:
- Axiomatics Authorization Hub
- Control Plane (PAP) – described below
- Policy authoring
- Deployment management
- Control Plane (PAP) – described below
- Policy testing (future)
- Access reviews (future)
- Policy Testing Framework
- Policy testing
- Policy tracing
- CI/CD deployment
- Policy Companion
- AI-based policy helper
- Authorization Engines
- Decision Engines (PDP)
- Axiomatics Decision Services (ADS) – a lightweight authorization engine that delivers yes/no decisions and can be deployed centrally, locally, as a side-car, etc.
- Binary API
- Batch Binary API
- Contextual Authorization Query (CAQ) – described below.
- Open-ended RESTful API
- Enforcement Points/Agents (PEP)
- PEP APIs
- PEP SDKs for Java
- PEP for SAP (partnership)
- PEP APIs
- PEP for SharePoint (partnership)
- Of note is the fact that PEPs for large, somewhat ubiquitous application systems like SAP and SharePoint have been developed through partnerships. Also, the current version of the Authorization Hub control plane is conducive to customer organizations wanting private cloud or on-premises deployment. Axiomatics is carefully considering whether to support the Hub as a service (i.e., SaaS offering), but has not yet made the decision to do so. The reason for this, as stated by Mr. Brossard, is that customers are not requesting such an “as-a-service” solution (yet). Moreover, according to Mr. Brossard, their larger customers are fighting against a SaaS model for a range of reasons, not the least of which is security.
Policy Administration Point (PAP)
One of the reasons for slow adoption of the XACML standard for externalizing authorization is the fact that the standard is cumbersome and complex. In other words – not easy to use. Also, typical enterprise requirements straddle both the IAM team and the App/Dev-DevOps teams with no clear ownership. To address this, Axiomatics has been working extensively on the development and augmentation of their PAP control plane to make it easier for business users to define their policies using a natural language format.
ALFA
To this end, Axiomatics has been building their XACML management interface on ALFA, the Abbreviated Language for Authorization, which is a domain-specific language used for defining access control policies. ALFA has been specifically designed as a user-friendly alternative to the more complex XML-based XACML standard, often used in conjunction with Policy Administration Points (PAPs) for managing those policies. Below is a snapshot of the Authorization Hub PAP interface.
Figure 5: The Axiomatics Policy Administration Interface (Source: Axiomatics)
Within the Policy Editor of the PAP, business users, administrators or developers can create, author, and design policy workflows that serve both complex and simple enterprise use cases. It also provides developers the ability to author policies in their Integrated Development Environment (IDE) using ALFA.
This interface is where one can define attributes that describe:
- The user
- The resource
- The action
- The context
…and map attributes to underlying sources like user directories (LDAP, Entra, Graph, SCIM), databases (SQL, Graph…) and related APIs.
The Authorization Hub is also where one can:
- Combine policies and attribute connectors into a single domain
- Configure authorization services to retrieve configuration
- Manage authorization services centrally
For release in 2025, Axiomatics Development is currently working on expanding policy testing and tracing to give their customers a more comprehensive look at how policies will behave before pushing into production. The policy tracing will also be able to:
- Analyze policies and understand why a policy is executing under certain conditions
- Help users understand why the policy evaluation yielded a specific decision
- Be used during development or in production to replay an unexpected result.
Note that Axiomatics is in the process of submitting ALFA 2.0 to the Internet Engineering Task Force (IETF) for standard ratification as an RFC (Request for Comment). The IETF (like Axiomatics) is committed to cross-domain standard adoption so XACML can work with current de facto standards such as OAuth and to establish and promote the use of externalized authorization as the preferred architecture and deployment pattern.
In Axiomatics’ development roadmap for 2025, they signal the intention of providing an AI-based policy helper for customers who are getting more involved in AI deployment across their IT ecosystems. AI expertise is not required to enable this capability. We see this as being beneficial to customers in a big way, however, as AI is becoming increasingly entrenched. Policy definition and policy management has been a challenge in large-scale externalized authorization deployments, as we can attest. With AI being able to facilitate this sometimes-arduous process, we see a lot of upside.
Contextual Access Query (CAQ)
The CAQ has as its purpose to tackle open-ended authorization requests such as:
- What can Subject XYZ (e.g., “Alice”) do?
- Who can edit record #321?
- And more…
- As a result, the CAQ enables:
- Dynamic runtime data filtering & masking
- Dynamic entitlement provisioning to COTS & SaaS
- Dynamic user access reviews -integrate with IGA tooling
- Policy (gap) analysis
For example, in the use case described as “at runtime, in a data-centric application, retrieve only the data records a user is allowed to access”, the CAQ sets what systems the query applies to (e.g., SQL databases, Graph-based systems, etc.). The CAQ generates filter expressions that are then translated into the target system’s query language (GraphQL, SQL…)
The results are then used to perform access reviews to validate policy impact:
- Compare between different snapshots to understand evolution
- Execute “gap analysis” tests to:
- Determine if there are unused (unusable) policies
- Determine whether some policies impact others
Note that CAQ is one of several tools in the Axiomatics policy testing toolset, alongside the Policy Testing Framework (PTF), Axiomatics Decision Services (ADS), and Policy Tracing.
Access Review and Audit
Authorization Hub’s authorization service generates an audit trail of all accesses granted and denied. Each audit entry contains the entire request, response, and set of policies used during evaluation. In this way, customers can use their existing Security Information Event Management (SIEM) services (e.g., Splunk) to analyze the logs and detect patterns, threats, and attacks.
Authorization Interoperability and Development
Firstly, we want to discuss an important standardization initiative aimed at fostering authorization logic interoperability, as described below. Following that, we get into the CI/CD pipeline discussion.
OpenID AuthZEN
As we discussed earlier, the market adoption of federated authentication using the underlying SAML protocol has become essentially globally ubiquitous. Not so in terms of authorization – yet. This has been a steep hill to climb because so much authorization logic is built-in to the business applications in widespread use – and because internally developed applications haven’t typically had a standardized approach to perform authorization function. This last bit doesn’t sit well with the CI/CD DevSecOps mantra to eliminate code silos, improve cross-team code sharing and reuse, reuse and reuse wherever possible. To the rescue, at long last, is the OpenID AuthZEN initiative, partly led and supported by Axiomatics.
OpenID AuthZEN is a two-year-old initiative bringing PDP vendors like PlainID, SGNL, Okta, Ping and Axiomatics together to establish a PEP/PDP interface standard. Their aim is to spearhead development of authorization agents that can lead the industry to something akin to “the OAuth moment of authorization!”
Put simply, this is a concerted community effort to increase interoperability between existing standards and approaches to authorization by standardizing interoperable communication patterns between major authorization components (i.e., PAP, PDP, PEP, and PIP: see NIST ABAC’s architecture presented in the Introduction). It also intends to establish and promote the use of externalized authorization as the preferred pattern.
It is the hope of this group (as well as ours) that major application vendors such as SAP, Salesforce, and so on will soon leverage – and even require externalized authorization – just like today we use SAML OpenID federated authentication as basic “table stakes”. Adoption of AuthZEN could at long last herald in an era of true authorization policy interoperability, which will be a boon to both internal application developers and large system integrators.
Axiomatics Labs
In the TechVision Research report titled, “How Microservices Can Improve Your IAM Strategy”, we described how Continuous Integration and Continuous Delivery (CI/CD) can benefit from:
- Logically combining the Development, Information Security and Operations groups into a single entity referred to as DevSecOps, with a primary focus on agile development (the antithesis of the waterfall model) coupled with,
- Adopting microservices architecture and deployment strategies that break down business functions into atomic-level IT functions, or “services”, that can be reused, retrofitted and replaced with minimal disruption to the overall IT infrastructure.
One of the most significant results of such a DevSecOps model is improved accessibility of what might be considered general purpose IT services, such as user authentication and authorization, profile management, customer and employee lifecycle management, data privacy, activity monitoring, input validation, anomaly detection and so forth.
Delivering IT functionality via self-contained services/microservices involves the identification of discrete application functions within a compact, single-purpose code set. Such a specific purpose microservice can then be easily and securely integrated into multiple, disparate in-house developed or COTS applications. This approach provides an environment for further integration of a related set of microservices as needed by a set of related, callable services. These related services can include specific IAM services such as ‘create identity’; ‘authenticate identity’; ‘authorize identity’, and so forth.
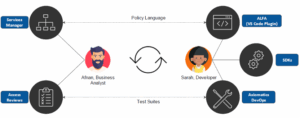
Key to Axiomatics adoption within the enterprise is the product’s ability to flourish in such an application development environment. We can attest that Axiomatics has spent several years making this one of their strongest suits. The company’s intention has long been to “put the Developer” at the heart of the Axiomatics suite. An illustrative example of this is shown below.
Figure 6: The Axiomatics Developer Focus (Source: Axiomatics)
Axiomatics’ landing page for developers of all stripes is here https://labs.axiomatics.com/ Here, you can see a suite of tools for developers that:
- Is available open source as a Github repository: https://github.com/axiomatics/policy-testing-framework
- Provides test integrations for Java developers
- Provides fine-grained tracing of policy evaluation
- Builds into your CI/CD pipeline by helping assemble authorization domains for deployment
- This set of development capabilities is an enormous boon to enterprises developing business applications in that it affords the ability to standardize access policies across the spectrum. TechVision knows firsthand how important it is to have such a capable set of policy definition and integration tools available, because we have personally worked on several large organizations’ application modernization programs. The work involves a strong governance backbone to gather multi-disciplinary, business application access control requirements and translate them into a workable (read: understandable) policies and schemas. Axiomatics has paid their dues in getting this aspect of modernized access control externalization particularly attractive.
Summary
- In summary, Axiomatics has considerable “street cred” regarding access control externalization. Some might argue that “they wrote the book” on the topic with their foray into the world of XACML almost 20 years ago.
They continue to expand and improve their offering by focusing on the simplification of policy management – an admirable undertaking to say the least. For this year (2025), they are moving away from multiple tools toward a comprehensive control plane within the Authorization Hub. Some of the interesting product plans include the development and release of a requirements-gathering component, as well as enhanced policy testing, deployment, and policy review.
Their impressive capabilities should enable customers to extend their Zero Trust frameworks to include authorization policy standardization and integration. As we have said – authentication is the “easy part”. We’re just kidding, of course, but while federated SSO has become completely ubiquitous, the same level of cross-domain interoperability of access controls has not been as successful. We expect this to improve, and companies like Axiomatics, with their dogged determination to get this right and make it happen are a shining light. And, while most of our review of their solution has been decidedly “enterprise-centric”, Axiomatics is also seeing growing adoption in the Customer IAM (CIAM) market. Perhaps this is in part because the CIAM space consists of more homegrown than COTS applications, and the opportunity to create a robust access control policy framework like the Authorization Hub enables is more conducive to CIAM, initially. We’re not saying CIAM is their sweet spot, but rather, it can be a viable “proving ground” for much of what we have reviewed here. Many of our customers start small and grow, rather than boil the ocean from the outset – thanks in part to our advice given to them.
Recommendations
We hope you have found this report useful. TechVision Research feels that access control is one of the more critical elements of an enterprise security posture. Zero Trust architecture cannot exist without solid access controls that genuinely reflect the risk tolerance of the organization – whether for enterprise users or customer users.
As more and more of our customers embark on their massive IT modernization programs, it is crucial to remember that this becomes the perfect time to comprehensively capture system and application requirements across the spectrum or domain being modernized. These requirements are the seeds for the access control policies that must be defined and implemented to achieve the risk management and go-to-market objectives. Having the capability to translate common language policy definitions into something like XACML without having to become an eXACML guru is very helpful. We mean, very helpful.
Increasing developer speed and consistency in terms of access control coding and re-use in the CI/CD pipeline will bring rewards in many areas. On one hand, you get lower overall development and integration costs. On the other, you get consistent policy implementation that lowers your risk.
Action Plan
No matter how far along you are (or aren’t) in your deployment, don’t delay moving the needle forward. Business applications need to support better, faster, data-driven decisions and the stakes are higher than ever. Again, if you’re behind the IT modernization curve, don’t boil the ocean – start with the highest risk environments, solve the most pressing problems and keep moving forward. Axiomatics’ Authorization Hub can improve your multi-cloud cybersecurity, DevOps, automation capabilities and subject access to your IT assets.
Those organizations that strive to be prepared to protect their broad range of critical information assets in a secure-but-user-friendly ecosystem will be able to do this by developing a comprehensive IAM architecture and deployment strategy. TechVision recommends a structured approach to identifying key access control risks across this spectrum and has developed a Reference Architecture that is very useful in evaluating the set of capabilities necessary for your future state access control foundation. With over 30 years of helping our customers identify and mitigate these identity-centric risks, TechVision can help with this process.
About TechVision
World-class research requires world-class consulting analysts, and our team is just that. Gaining value from research also means having access to research. All TechVision Research licenses are enterprise licenses; this means everyone that needs access to content can have access to content. We know major technology initiatives involve many different skillsets across an organization and limiting content to a few can compromise the effectiveness of the team and the success of the initiative. Our research leverages our team’s in-depth knowledge as well as their real-world consulting experience. We combine great analyst skills with real world client experiences to provide a deep and balanced perspective.
TechVision Consulting builds off our research with specific projects to help organizations better understand, architect, select, build, and deploy infrastructure technologies. Our well-rounded experience and strong analytical skills help us separate the “hype” from the reality. This provides organizations with a deeper understanding of the full scope of vendor capabilities, product life cycles, and a basis for making more informed decisions. We also support vendors in areas such as product and strategy reviews and assessments, requirement analysis, target market assessment, technology trend analysis, go-to-market plan assessment, and gap analysis.
TechVision Updates will provide regular updates on the latest developments with respect to the issues addressed in this report.
About the Authors
 Doug Simmons brings more than 25 years of experience in IT security, risk management and identity and access management (IAM). He focuses on IT security, risk management and IAM. Doug holds a double major in Computer Science and Business Administration.
Doug Simmons brings more than 25 years of experience in IT security, risk management and identity and access management (IAM). He focuses on IT security, risk management and IAM. Doug holds a double major in Computer Science and Business Administration.
While leading consulting at Burton Group for 10 years and security, and identity management consulting at Gartner for 5 years, Doug has performed hundreds of engagements for large enterprise clients in multiple vertical industries including financial services, health care, higher education, federal and state government, manufacturing, aerospace, energy, utilities and critical infrastructure.
 Gary Rowe is a seasoned technology analyst, consultant, advisor, executive and entrepreneur. Mr. Rowe helped architect, build and sell two companies and has been on the forefront the standardization and business application of core infrastructure technologies over the past 35 years. Core areas of focus include identity and access management, blockchain, Internet of Things, cloud computing, security/risk management, privacy, innovation, AI, new IT/business models and organizational strategies.
Gary Rowe is a seasoned technology analyst, consultant, advisor, executive and entrepreneur. Mr. Rowe helped architect, build and sell two companies and has been on the forefront the standardization and business application of core infrastructure technologies over the past 35 years. Core areas of focus include identity and access management, blockchain, Internet of Things, cloud computing, security/risk management, privacy, innovation, AI, new IT/business models and organizational strategies.
He was President of Burton Group from 1999 to 2010, the leading technology infrastructure research and consulting firm. Mr. Rowe grew Burton to over $30+ million in revenue on a self-funded basis, sold Burton to Gartner in 2010 and supported the acquisition as Burton President at Gartner.