Okta Identity Platform Assessment
Published 23 January 2023
Abstract
The modern digital enterprise requires a consistent, robust and adaptive Identity and Access Management (IAM) foundation. This foundation includes many capabilities as described in our IAM reference architecture, but one of the most critical decisions organizations need to make is on your primary Identity Management platform vendor. This is our second research report focusing on this topic. Our first vendor report was on Microsoft’s Entra IAM program and strategy, and this report provides an overview and critical evaluation of Okta’s IAM solution that was built “in the cloud” from its inception in 2009.
Okta is a pure Identity as a Service (IDaaS) solution providing pretty much soup-to-nuts IAM capabilities for a wide range of use cases and user bases. In this in-depth report, we’ll review Okta’s current portfolio of IAM and related products/services, then expand our discussion to look at these offerings as specific IAM capabilities within the TechVision Reference Architecture for IAM. We close with our recommendations for organizations who may be considering Okta as a foundational vendor to support the execution of their IAM strategy.
Authors:
| Doug Simmons
Principal Consulting Analyst |
Gary Rowe
CEO/ Principal Consulting Analyst |
Executive Summary
In the mid-to-late 2000’s, cloud computing made its entry into enterprise networking and data center footprint. Since that time, enterprises of all ilk have begun, are in process, or have completed migration of many types of IT infrastructure from on-premises into the cloud. This has, in large part, been facilitated by the Big Three cloud infrastructure as a service (IaaS) providers: Amazon Web Services, Google Cloud Platform and Microsoft Azure. Additionally, vendors like Salesforce, Workday, Microsoft Office and many others have made workforce productivity (e.g., sales, human resources, business productivity, etc.) solutions available as software as a service (SaaS). This roughly eighteen-year period between 2005 and now has seen the rise of hybrid IT in myriad shapes and forms, consisting of a mix of on-premises and in-cloud IT functions and services.
And around this timeframe – beginning in 2009, Okta was conceived as an Identity as a Service (IDaaS) solution and they are still leaders in this category. Initially, Okta created a cloud-resident web access management (WAM) solution that essentially off-loaded the burden of on-premises SSO and coarse-grained access control. Within a few years, Okta became a massive success and enterprises around the world began to consider migration to the Okta IDaaS in concert with their overall cloud migration strategies.
Due to this meteoric success, Okta has continued to develop IDaaS solutions and capabilities and has further cemented its legacy and leadership in the cloud identity management space. From these humble but auspicious beginnings, Okta has gone on to establish itself as a cloud centric, zero trust-enabling IAM suite of capabilities that today include the following:
- Okta Workforce Identity Cloud
- Single Sign On (SSO) – enables federated login with a network of 7,000+ pre-built integrations that facilitate access to cloud and on-prem applications, APIs, as well as critical infrastructure – regardless of the user location or device.
- Adaptive Multifactor Authentication (MFA) – supports a range of assurance factors—including knowledge factors, possession factors, inherence factors, and time-based factors that can integrate external risk signals and force step up authentication dynamically or block access requests.
- Identity Lifecycle Management – automates joiner-mover-leaver processes such as account creation and deletion using integration capabilities (e.g., SCIM, APIs) from many authoritative source systems, including Human Resources Management Systems, AD, LDAP, etc.
- Workflows – enables automation of identity-based processes with a low/no-code interface and extensible platform service.
- Identity Governance – includes a suite of products to facilitate governance, risk, and compliance via access request/fulfillment, access certifications, entitlement tasks and access reporting throughout the identity lifecycle.
- Okta Customer Identity Cloud
- Universal Login – enables social login, customizable user experiences, MFA, and passwordless authentication.
- SSO – federation with a sizeable number of applications
- Attack Protection – enables out-of-the-box bot detection, breached password detection, suspicious IP throttling, etc.
- Organizations (B2B) – Customizable authentication and authorization workflows for B2B partners
- Passwordless Authentication – enables secure authentication with the option to use biometrics or security keys.
Okta runs on Amazon Web Services (AWS) and relies on its Elastic Compute Cloud (EC2), Simple Storage Service (S3), Virtual Private Clouds (VPC’s), Cloud Front, Lambda and API Gateway. Okta is available in every region AWS is present, giving its IDaaS solution a global footprint with multi-region failover capability.
Today Okta is a pure IDaaS provider with comprehensive IAM capabilities for a wide range of use cases and user bases. The rapid advancement and uptake of Okta was led by organizations that focused on “better and faster” cloud-based solutions and were interested in executing on this cloud-first strategy. While Okta shines in a cloud-based world, organizations that are heavily entrenched in Microsoft IAM, desktop, endpoint management and Azure cloud deployments may see Okta as a redundant solution. Microsoft licensing, particularly the “E5” enterprise licensing that many large companies have acquired, includes an extensive amount of IAM functionality that is on par with Okta’s and requires no (or little) additional license fees. In some cases, the emerging Microsoft Entra IAM suite is more feature rich – depending on your organization’s requirements (see the TechVision Research report “Microsoft Entra as a Complete IAM Platform”). In general, the Okta suite is very suitable for organizations with one or more of the following characteristics:
- Cloud-first focus
- SSO prioritization
- M&A, Multi-organizational, complex domain architectures
- Not fully locked into a comprehensive Microsoft enterprise license, as just described, or does not want to use Microsoft licenses to their full extent
- Desire to limit full dependency on Microsoft for reasons that may range from avoiding vendor lock-in, mitigating risk, looking to move away from Microsoft/Azure-centricity, organizational politics, lack of confidence in Microsoft IAM solution, or a lack of Microsoft skills within the enterprise
- IGA not a top priority or using best-of-breed IGA solutions (Okta IGA is a new product offering, having debuted in the second half of 2022)
- Focusing on a Customer IAM (CIAM) solution that can be seen more as a green field than enterprise IAM
Okta SSO is a strong and proven product that enterprises are generally able to deploy quickly, at scale and is very flexible in order to meet the needs of organizations that need to be very responsive to business conditions and partnership integration/de-integration. This platform is a mega toolkit for deploying federated SSO across a broad range of SaaS and web-based applications quickly and easily. Given that the Okta IDaaS platform runs on AWS and leverages a good deal of AWS’ global data centers, it is a scalable solution that can rely on AWS reliability and failover capabilities.
Okta’s IGA is not as strong as competing vendors such as SailPoint, Saviynt, MicroFocus, Clear Skye or ForgeRock in the areas of identity lifecycle management and governance capabilities. This is why many large organizations that use Okta also deploy one of the above vendors. While Okta currently has less advanced capabilities in the IGA area, they are increasing their investments and making progress in this area. Note that Microsoft as we described in the Entra report are also working to catch up with some of the pure-play IGA vendors in this area.
We think Okta is a great fit for many organizations, but the progress that Microsoft has made in expanding their IAM capabilities combined with the inclusive licensing model has elevated the stature of Microsoft as a competitor. And Microsoft isn’t the only alternative to Okta as a primary IAM platform with Ping Identity ForgeRock, SailPoint, Microfocus, One Identity, Saviynt and many other IAM/IGA providers with viable solutions that may warrant consideration. Of particular interest and to be covered in future reports are the are the “Big 3” Thoma Bravo IAM/IGA acquisitions that include SailPoint, Ping Identity and ForgeRock. How Thoma Bravo builds, consolidates, divests or otherwise leverage these three acquisitions may change the IAM platform landscape and be factors in deciding on Okta or other vendors in the future.
Introduction
Some thirty years ago, the now ubiquitous world wide web was born. Riding on the success of TCP/IP networks that spawned from the U.S.’s Advanced Research Projects Agency Network (ARPANET), the forerunner of the Internet, “the web” changed the world forever. Browsers such as Mosaic were born, content was uploaded onto internet-connected servers and everyone from school kids to grandparents were soon ‘surfing the web’ to see, read and learn things in ways never before thought possible. After 10 years or so of running their IT environments in their own data centers, organizations saw cloud computing as a major step toward rapid elasticity of compute services and cloudification began.
Okta was a major part of the cloudification of IT and, in particular IAM. For those that are interested in a historical perspective on how Okta evolved to become the dominant player in the IAM market today, please refer to Appendix 1 for details.
Okta Overview
Okta emerged in the relatively nascent stage of the cloudification of the world of IT. As a startup in early 2009 it didn’t take too long for Okta to become what at the time was referred to as a “market disruptor”. Until this time, IAM was pretty much exclusively an on-premises solution set. Enterprises ran their IT infrastructure, including IAM, in their data centers or colocation facilities. The economically desirable elasticity of cloud computing hadn’t reached the world of IAM, yet and Okta was the company that changed this paradigm. Even though Microsoft at this point in time had rolled out Azure as their cloud computing environment, Azure AD was often seen as merely a cloudification of an enterprise’s on-premises AD environment. In other words, Azure AD at that time was viewed as a Microsoft solution that was primarily focused on Microsoft applications.
Okta, on the other hand, had positioned itself as a network agnostic IDaaS for SSO. Okta provides a relatively simple tool called the AD Sync Agent to synchronize on-premises AD accounts and passwords with Okta’s Universal Directory. Okta is the front-end proxy for web-based authentication and authorization, issuing OpenID Connect (OIDC), SAML or OAuth tokens that enable federated SSO to all applications that are configured behind the front-end.
From these humble but auspicious beginnings, Okta has gone on to establish itself as cloud centric IAM suite of capabilities that today include the following:
- Okta Workforce Identity Cloud
-
- Single Sign On (SSO) – enables federated login with a network of 7,000+ pre-built integrations that facilitate access to cloud and on-prem applications, APIs, as well as critical infrastructure – regardless of the user location or device.
-
- Adaptive Multifactor Authentication (MFA) – supports a range of assurance factors—including knowledge factors, possession factors, inherence factors, and time-based factors that can integrate external risk signals and force step up authentication dynamically or block access requests.
- Identity Lifecycle Management – automates joiner-mover-leaver processes such as account creation and deletion using integration capabilities (e.g., SCIM APIs) from many authoritative source systems, including Human Resources Management Systems, AD, LDAP, etc.
- Workflows – enables automation of identity-based processes with a low/no-code interface and extensible platform service.
- Identity Governance – includes a suite of products to facilitate governance, risk, and compliance via access request/ fulfillment, access certifications, and entitlement tasks throughout the identity lifecycle.
- Okta Customer Identity Cloud
- Universal Login – enables social login, customizable user experience, MFA and passwordless authentication.
- SSO – federation with a sizeable number of applications
- Attack Protection – enables out-of-the-cloud-box bot detection, password breach detection, suspicious IP throttling, etc.
- Organizations (B2B) – Customizable authentication and authorization workflows for B2B partners
- Passwordless Authentication – enables secure authentication with the option to use biometrics or security keys.
So, this is where we find Okta today: a genuine IDaaS providing pretty much soup-to-nuts IAM capabilities for a wide range of use cases and user bases. In the following sections, we’ll take a more in-depth look at Okta’s current portfolio of IAM and related products/services, then expand our discussion to look at these offerings as specific IAM capabilities within the TechVision Reference Architecture for IAM.
Product Suite Overview
At the basic level, Okta runs on Amazon Web Services (AWS) and relies on its Elastic Compute Cloud (EC2), Simple Storage Service (S3), Virtual Private Clouds (VPC’s), Cloud Front, Lambda and API Gateway. Okta is available in every region AWS is present, giving its IDaaS solution a global footprint with multi-region failover capability. Given this backdrop, we’ll now look at each of these Okta products and solutions that build out the Okta IAM platform starting with the workforce services.
Workforce Identity Cloud
It was in the enterprise space that Okta got its start as did ForgeRock, Ping, Microsoft, Micro Focus and many others. As we explained in the Introduction, the first major push into the IDaaS arena was to position itself as a cloud resident SSO security proxy. This is where we will begin our review, followed by their further advancements Okta has made as a more comprehensive IAM suite. We’ll cover key workforce identity staples for Okta including SSO, adaptive MFA, Identity Lifecycle Management and IAM workflows and Identity Governance.
SSO
Okta’s “flagship” identity management service is devised to allow organizations to present a single, integrated web application to all end users, including employees, contractors, customers, and business partners, who can navigate it with a single set of credentials. That is essentially the essence of SSO. Users need to login only once. Centralized registration can be automated so that this capability can allow users to be provisioned and de-provisioned in the target applications. Upon login, end users are routed to a single landing page and navigate to allowed applications. This is a sweet spot for Okta. The general, high-level SSO flow is illustrated in Figure 1.
Figure 1: The Okta SSO Platform (Source: Okta)
With Okta SSO, a more seamless user experience is enabled by providing SSO to all the web applications that make up an organization’s portal. To provide SSO to all applications, users first authenticate into Okta via a web-based client leveraging the user’s browser. Once this session has been established, Okta can authenticate the user to any connected application subject to the access control “rules set” within Okta. There are two primary ways that the initial Okta session can be created:
- Using the Okta “My Applications” dashboard.
- Using Service Provider Initiated SAML (SP SAML) with an existing portal.
Okta’s “My Applications” landing page provides an initial portal to all assigned applications. This option is commonly used when no central portal exists and the requirements for login screen customization are minimal.
On the other hand, many Okta enterprise customers use what is called the Service Provider (SP) SAML method, which integrates Okta SSO with the enterprise’s existing portal infrastructure. The flow for this common method is as follows:
- Users navigate to a central portal, for example, http://support.myco.com.
- If they are not already logged in, they are redirected to an Okta login widget along with a SAML request, then sent back to the portal with a SAML response after entering their correct username and password, or another such unique credential.
- The SAML federation response transparently logs the user into the portal.
- Now the user has both a portal session and an Okta session that can be used to transparently authenticate to any assigned application via SAML federation on redirection.
Once the Okta session has been established, users can transparently authenticate to any assigned application using a catalog based or “custom SSO integration”. SSO integrations can either be federated (supporting a standard such as SAML or another open authentication protocol such as OIDC or OAuth) or leverage Okta’s Secure Web Authentication (SWA) to perform a secure, form-driven post to the application login page.
Applications in the Okta Application Network, which today consists of a very large number of commercial applications as we will discuss later, come pre-integrated for SSO using SAML or SWA. These integrations are delivered as part of the service and are continually maintained and updated by Okta. This level of “pre-integration” with popular applications such as Salesforce, ServiceNow, Microsoft 365, Workday, etc. provides a major “assist” to enterprise architects, developers, and integrators for the obvious reasons.
For custom applications that are not in the Okta Application Network, Okta provides integration toolkits to easily enable SAML to function consistently with the SWA. The SAML integration toolkits are available for .NET apps running on Microsoft’s Internet Information Service (IIS), and they support forms authentication and a variety of other languages including Java, and PHP. Again, organizations can leverage Okta’s Secure Web Authentication (SWA) to achieve SSO to these applications with a no-code approach.
For simplicity’s sake, SWA allows end users sessions to be authenticated transparently to the application by its automation of the typical local application login process. SWA only requires that the user account in the target application be provisioned with a known password that can then be managed securely in the Okta service (i.e., the Universal Directory, discussed later).
It bears mentioning here that Okta has become a popular VPN front-end, too by supporting native VPN capabilities that are built into the mobile operating system and which leverage existing VPN solutions and enable remote access. However, it is important to understand that unlike with VPN’s, Okta provides access only to specific, Okta-enabled applications and not the entire network. Okta doesn’t replace an organization’s VPN but can enhance it by providing a single point-of-entry that enforces adaptive MFA (discussed next) and is well integrated with the organization’s application SSO landscape.
Due to its relatively simplicity to implement, Okta’s SSO has by far the largest install base of the Okta IAM suite or portfolio. It is the flagship, and it is successfully deployed in thousands of enterprises of all sizes and in all industries. Once Okta SSO is in place, enterprise customers typically expand the Okta footprint (i.e., the Workforce Identity Cloud) by deploying the next critical piece: adaptive MFA.
Adaptive MFA
Okta’s Adaptive MFA feature is an extension of their SSO (cloud IAM) platform, and supports the following factors for authentication, among others:
- Okta Verify
- Google Authenticator
- SMS Authentication
- Voice Call Authentication
- Symantec VIP
- On-Prem MFA (e.g., RSA SecurID)
- DUO Security
- Yubikey
- Security Question (generally NOT recommended)
- Windows Hello for Business
- U2F keys
Okta Verify is an MFA factor type designed for end user identity verification with the Okta SSO service. Okta Verify is available for iPhone, Android, and Windows devices. Okta Verify includes the option to deploy Okta’s MFA app to enable push notifications to these mobile devices. For a much more detailed analysis of MFA approaches, technologies, and vendors, please see the TechVision Research document titled “Multi-Factor Authentication (MFA): Enterprise Strategy and Market Assessment”.
Okta Verify also supports a device biometric technology to guard against unauthorized use of Okta Verify. Administrators can configure an end-user fingerprint or FaceID request, which appears after the initial MFA challenge.
For improved security on Android, Okta customers can enable hardware key storage on Android via Okta Verify Settings. Enabling this feature allows the implementation of security protocols using access-controlled, hardware-backed keys based on the Federal Identity, Credential, and Access Management (FICAM) architecture. Okta Verify for mobile also uses FIPS 140-2 validation for all security operations when enabled in the administrative dashboard. Okta is FedRAMP certified.
For the “adaptive” part of the authentication process, Okta has introduced risk-based authentication. Configuring this feature allows organizations to inspect login context like device, location, and user behavior to take dynamic actions based on risk level. This means step-up authentication can be automatically implemented in high-risk scenarios, which may reduce some of the burden on administrators to create and manage complex authentication policies. Through machine learning, Okta can also refine login context, continually improving security as well as user experience. Some of the key features of Okta’s risk-based authentication include:
- Log and block authentication attempts from suspicious IP addresses.
- Activate the ThreatInsight tool that uses attack data from across Okta’s cloud network to identify and block malicious login attempts.
- Integrate external risk signals to provide additional context.
Detected authentication risk levels are then paired with appropriate access decisions, like allowing or denying access, prompting for MFA, or using passwordless authentication for a low-risk request. In addition to Okta Verify, the SSO platform supports these popular or emerging authentication techniques:
- Okta Fastpass – allows workers to register their devices to Universal Directory via the Okta Verify App, which establishes a unique binding between it and the user in the Okta Workforce Identity Cloud. The result is a passwordless login experience that works on any device across browsers, desktop applications, and native mobile applications.
- Email-based magic link – utilizes a simple web link embedded in a verified email to validate the request and continue the login process.
- Factor sequencing – for a higher level of assurance, factor sequencing allows end users to authenticate using one or more high assurance factors like Okta Verify with risk-based-authentication as a form of step-up authentication.
- WebAuthn – this is a standards-driven approach to password-less authentication that relies on 3rd party authenticators like YubiKey or TouchID to authenticate to applications. Many organizations now use WebAuthn to stop all password-based identity attacks.
- PIV/Smartcard – uses Federal Personal Identity Verification (PIV)/Smartcards (or any X.509 supported cards) to authenticate in Okta or any apps integrated with Okta without passwords.
- Passwordless with Device Trust – integrates with leading endpoint management systems (e.g., VMWare) to deliver a password-less login experience on desktop and mobile.
- AD-joined Desktop single sign-on – uses password-less authentication to login to Okta on machines joined on the enterprise’s Active Directory domain using the agent-based Okta Integrated Windows Authentication (IWA) or using cloud-based Kerberos approaches (agentless).
Okta Adaptive MFA also supports integration with a variety of popular VPNs, enabling a broad array of factors, straightforward end-user enrollment, and a thoughtful policy framework to improve identity assurance for remote network access.
Identity Lifecycle Management
Having been very well-received in the IAM marketplace with its relatively straightforward IDaaS SSO – further augmented with adaptive MFA, Okta began to dive seriously into the identity lifecycle management area over the past few years. Typically, identity lifecycle management is centered on provisioning and de-provisioning of user accounts on multiple applications, systems, and networks. It also includes account management and administrative capabilities such as self-service and delegated administration, access requests and workflows. In these next two sections, we’ll examine Okta’s approach.
With Okta, portal users are registered once, and then accounts are automatically created in each “target” web application. For example, to add users to the system, Okta supports initial user registration with:
- The Okta administrative interface
- Bulk import from a CSV file or from an external directory service
- Programmatic use of Okta’s RESTful user management APIs
For most enterprises, the most popular ways to integrate identity data with Okta is through the AD Sync Agent, which can run on any Windows machine with read access to the domain controller and require no changes to firewall settings. This is how Okta often supports delegated authentication, provisioning and deprovisioning, directory sync, and AD password management.
Additionally, Okta’s RESTful APIs can be used in conjunction with a custom user registration form to support self-service user provisioning, or they can support required approval workflows – described in the next section.
As a part of the user creation process, Okta is able to transform the username format to ensure there are no violations of various cloud applications’ username format requirements. For example, if a portion of an organization’s portal is based on the Salesforce.com platform, it’s possible that a customer or partner that tries to register with that portal already has an existing Salesforce.com account (for example, [email protected]). In this case, she would normally be prevented from creating an additional account or registering. Okta is able to provide a transformation for that user and would instead provision him as john@okta.myco.com to ensure there are no user namespace conflicts within Salesforce.com.
Application-specific user properties such as group membership, role, or profile can also be created or modified based on rules associated with the Okta user profile. Attributes of that profile are then pushed into the target applications as part of the provisioning process. These target web applications can be SSO-enabled using code templates provided by Okta in a variety of languages including Java, ASP. NET, and PHP.
Events that trigger a lifecycle state change – such as an employee position change, termination, or the expiration of an external application license – initiate processes to ensure that access to resources remains compliant with business and security policies. In a provisioned environment, the new user account is created in the organization’s existing user store and, based on rules set up by the organization, the profile information flows down through the Okta app integrations out to all the target applications to create the accounts that the new user needs access to. Again, users can be imported from an external application or directory service such as LDAP or AD or can be manually created in Okta. The following are some examples:
- If an employee changes jobs or roles – resulting in an update to various attributes in the authoritative source repository (e.g., HR database, LDAP, or AD), the existing user account can be updated through Okta out to the external (target) applications, changing access levels, adding or removing group membership, or synchronizing passwords for example.
- When a user no longer needs an external application or the application is no longer available to the user (such as an expired license), the user account can be updated, and the access removed.
- When a user is removed from a group that was providing them access to certain applications, the user can be automatically deprovisioned from those applications. When added as a member of a group, the user inherits access to the applications that have been granted to the group.
- When an employee leaves an organization, the HR database can trigger Okta to deactivate the user account in the Okta Universal Directory, resulting in access to removal and account de-activation to all applications integrated with Okta. This procedure can also be performed manually by an administrator. If the employee returns to the organization at a later date (for example, after a return from leave), reactivating the user in Okta Universal Directory reactivates the user’s accounts in the external applications.
Workflows
Workflows are often an important part of customizing Okta products like Lifecycle Management, in addition to enabling identity automation and orchestration for IT and Security processes. Workflows provide a no-code interface for end-users to simplify and automate complex identity processes, at scale. In this vein, Okta Workflows provides an interface-driven platform for the automation of business processes using a library of pre-built templates and connectors, in addition to enabling users to connect to third-party applications over APIs. In this way, Okta Workflows offers a number of capabilities to facilitate and automate account management, such as:
- Provision and deprovision app accounts – when a person joins the organization, HR integration trigger and workflow can automatically create their identity in the Okta-enabled target applications, as well as set entitlements, assign folder shares, and send a message to their manager. Similarly, when an employee leaves the company, Okta Workflows can freeze the account, transfer their digital assets to a manager, and then deactivate the user account some period (e.g., three days) later.
- Sequence actions with logic and timing – Okta Workflows can create deactivated accounts in all Okta-connected applications some period (e.g., one week) before a new employee’s start date, and then activate them on their first day.
- Send notifications for lifecycle events – For a lifecycle event such as an application assignment or user suspension, Okta Workflows can notify IT by email or Slack.
- Log and share lifecycle events – Okta Workflows can query Okta APIs and syslog events, run logic, and compile data into a CSV file. Then, Okta Workflows can email that file to specific IAM teams.
- Automate security operations to protect company data – Customers can use Workflows to set up security notifications for particular events, such as sending a password change notification or hardening customer verification with an email factor challenge.
- Respond to security risk signals – Workflows can automatically monitor and take action against external or internal threats, such as tracking and alerting for possible account takeovers or reporting suspicious activity to security teams.
As can be seen, the Okta Workflows feature provides a reasonable amount of customization and flexibility regarding automation of business processes related to IAM. Using RESTful APIs, IAM teams or application developers can establish a solid foundation for automating (and auditing) IAM joiner/mover/leaver (JML), in addition to automating common IT and Security tasks. This also provides the foundation for expansion of the enterprise IAM experience into identity governance and administration (IGA), as we describe next.
Identity Governance
Okta Identity Governance is a SaaS-delivered platform that can provide the tools necessary to manage identity and access lifecycles across multiple systems. As we describe in detail in the TechVision Research report titled “Establishing a Modern-Day Identity Governance and Administration (IGA) Framework”, IGA is an important set of capabilities that can improve the overall security of the organization.
To be sure, Okta Identity Governance builds upon the existing Okta Lifecycle Management products and capabilities we have just covered, such as Provisioning and Workflows, which facilitate enterprises access fulfillment and entitlement tasks during a user’s identity lifecycle.
With Okta’s Identity Governance capabilities, organizations can help the organization can:
- Create, protect, and audit access to critical resources.
- Reduce risks associated with unmanaged identities and accumulation of elevated or privileged access.
- Make access certification more meaningful with the contextual information provided by the converged IAM solution, such as sign-in frequency, a resource’s last accessed date, and so forth.
- Automatically provision new employees to birthright apps based on their user profile attributes.
- Enable users to self-service access requests to Okta-connected resources from their workplace collaboration tools.
- Automate tasks to reduce the time taken and errors associated with manual data entry and provisioning tasks.
Directly integrated into an Okta organization, Okta Access Requests automates the process of requesting access to applications and resources and can route user requests to one or more approvers for action. These Access Requests can be defined and configured to meet the needs of several different organizational roles, such as Requester, Approver and Administrator.
Using the IGA Access Certifications feature, Okta customers can also create audit campaigns to periodically review users’ access to resources and approve or revoke access automatically when required. Okta’s Identity Governance Reports let’s administrators and managers obtain a high-level overview of past certification campaigns and see details of past resource access requests and campaigns, including users involved and remediation status.
Lastly, it is important to note that Okta can integrate with an existing on premises identity management solution. For example, integration between Okta and an existing identity management solution can allow Okta to provide both SSO and even user management to all applications already integrated with that identity management solution. Additional cloud and on-premises applications can then be integrated directly with Okta and the whole collection managed within a single consistent framework. This is a useful feature for many organizations that have developed extensive integration capabilities with “legacy” tools such as Microsoft Identity Manager (MIM), SailPoint or others.
Customer Identity
Customer Identity and Access Management (CIAM) is important and highly visible as it provides organizations with a public gateway to secure external engagement and is a critical element of any Digital Enterprise program. CIAM differs from traditional (inwardly focused, enterprise) IAM because of its greater emphasis on user experience, privacy and consent management, increased scale, integration with CRM/marketing systems, and a business/sales focus. TechVision Research has dedicated a sizeable amount of research targeted specifically to Customer IAM (CIAM). For a look at some of the latest research on this topic, please consult our research document titled “Online Consumerization Booms: Recalibrating Customer IAM (CIAM)”.
Okta began offering a series of CIAM-centric capabilities several years ago as the trend toward specialized IAM offerings for customer-facing e-commerce, healthcare and financial services began to surge. Augmenting their flagship SSO foundational infrastructure with key CIAM capabilities have led to the release of the following:
- Universal Login
- Customer SSO
- Attack Protection
- Organizations (B2B)
- Passwordless Authentication
We’ll now dive into each of these below.
Universal Login
This feature was initialized principally through the acquisition of Auth0 by Okta in May 2021. The Auth0 Universal Login Capability Okta acquired lets its customers define specific login flows to do what is needed to better ensure the user’s identity.
For example, the authentication flow can start off using a simple username and password, but also dynamically call other features such as social login and multi-factor authentication (MFA). This can be invoked in real-time without requiring application-level changes because all functionality is driven by the web pages served by the centralized authentication server
Additionally, Okta customers can create more consistent, branded login experiences by customizing the login page appearance and behavior from the Auth0 Dashboard including the logo and colors. For more advanced use cases, the code of each page can be modified as well.
Okta also introduced risk-based authentication to help take advantage of login context like device, location, and user biometrics and to take dynamic actions based on risk level. This allows step-up authentication to be automatically implemented in high-risk scenarios, reducing the burden on administrators to create and manage complex policies. Through machine learning, Okta can also refine login context, continually improving security as well as user experience. This is also a feature of Okta’s Workforce Identity Cloud – not just Customer Identity Cloud.
SSO
Like its enterprise SSO set of capabilities, Customer SSO supports enterprise federation, social login, MFA or username and password authentication and allows users to log in once and use all applications they have been granted access to.
Attack Protection
Many of the attacks targeting authentication are distributed denial of service (DDoS), credential stuffing and password spraying attacks. One of the primary ways Okta combats against DDoS and such brute force attacks is to enable rate limits on authentication and API calls to Okta services. For example, Okta sets various organization-wide and concurrent rate limits so that legitimate calls to Okta are not affected, but spikes in traffic that are often characteristic of DDoS attacks are dropped, preventing lockouts to the Okta service.
Organizations
Over the past 30 years businesses have been evolving toward managed services for their Information Technology deployment and operations. The terms ‘off-shoring’ and ‘outsourcing’ became analogous with perceived cost savings, scalability (up and down), and operational expensing (“OpEx”) for corporate tax purposes. Managing these B2B partnerships effectively and securely requires new thinking when it comes to Identity and Access Management (IAM). This dramatic sea change in how businesses manage their IT infrastructure introduces IAM challenges centered on external people/processes/things needing access to mission critical internal IT systems. Often, managed service providers (MSPs) require highly privileged access rights to deploy, configure, update, and monitor IT environments from thousands of miles away. This challenge exists for enterprise IAM enablement of a broad range of vendors – not just MSPs. Network appliance and security vendors, participants in the company’s supply chain, even Human Resources and payroll services often require access to sensitive corporate systems, often from outside the traditional enterprise network security perimeter. For a much more detailed investigation into the realm of B2B IAM, please see the TechVision Research report titled “Digital B2B Requires Updated IAM”.
Okta refers to this B2B IAM focus as Okta Organizations. An Okta organization (org) is a root object and a container for all other Okta objects. It contains resources such as users, groups, and applications, as well as policy and configurations for the enterprise Okta environment. Within every org, there are users and applications. These are the only mandatory items that must be configured for the B2B “org” to use Okta. Users can be created in Okta, imported through directory integrations, or imported through application integrations. Applications are connections to public apps (such as Office 365) or proprietary applications, such as the enterprise’s own applications.
Each Okta org exists in a specific segment (or “cell”) of Okta’s infrastructure. A cell is a conceptual grouping of Okta’s public-facing services and UI for a subset of orgs. Cells are completely independent of each other and feature redundancy to ensure availability.
Passwordless Authentication
The challenge with authentication is that traditional authentication-via-passwords has been problematic. For higher value transactions in particular, the use of simple, relatively insecure, often recycled, easily guessed or stolen passwords are no longer good enough. One of the most sought-after pieces of personally identifiable information (PII) is a username and password; this is especially threatening when individuals reuse the same username/password combinations at multiple sites. So, passwords are a problem. With passwordless authentication, enterprises can reduce or even eliminate many password-based attacks, including phishing and credential stuffing. We’ve written extensively on this topic, and you can read more in the TechVision Research report titled “Zero Passwords in a Zero Trust World”.
Okta has a few different password-less options for various use cases, such as:
- Email magic links – end users click on a link embedded in a verified email to validate the request and continue the login process. This approach can be ideal for password less authentication into applications that require infrequent authentication, access from any device, or when its needed.
- Factor sequencing – allows user authentication using one or more high assurance factors like Okta Verify with risk-based-authentication to remove the need for a second factor.
- WebAuthn – is a standards-driven approach to passwordless authentication that uses authenticators like YubiKey or TouchID to authenticate into applications. This is the optimal passwordless approach as there is no back-and-forth credential sharing needed.
Universal Directory
Okta’s service contains a native cloud user store called the Universal Directory, which allows customer, partner, and employee identities to be centralized into a single location. This native cloud user store can operate independently from, or in combination with, external directory services. User profiles and their associated properties can originate in Okta and be managed from Okta, or they can be mastered from a variety of external sources.
For example, an organization may have a set of internal employees that needs access to its portal and whose identities are managed in Active Directory (very common!) or LDAP. Okta could leverage AD or LDAP for the authentication of internal employees who access the portal applications, but customer and partner user accounts could be managed natively in Okta, eliminating the need for yet-another-directory. However, Okta can also manage customer and partner accounts in an existing corporate directory as well.
Okta Integrations Network
As IAM architects and solutions designers for more than three decades, TechVision Research knows how important robust and reliable data integration with authoritative identity source systems and target environments truly are. Without a requisite level of identity data integration that can support real-time event and batch processing, the IAM environment can be left with stale or otherwise suspect information upon which it relies to make access decisions. We discuss this at length in the TechVision Research report titled “Architecting and Managing Hybrid and Cloud-based Identity Services”.
Over the past dozen years or so, Okta has established a fairly impressive range of “integrations” with vendors that create, manage or consume identity data across a broad range of industries and scenarios. For example, Okta has “out-of-the-box” (though there is no “box”) connector with HR vendors such as Workday, ADP Workforce Now and Oracle/PeopleSoft, among several others.
These provide the integration to Okta required to import users and their attributes on an ongoing basis from say, Oracle HCM Cloud, which acts as the user system of record. This connector operates as a SOC 2 Type II audited service running in Amazon Web Services. In fact, the Okta Integration Network (OIN) is a catalog of integrations that enterprises use to give their workforce access to the technology needed to deploy and expand their IAM footprint. Some of the available integrations include.
- Salesforce
- Microsoft 365
- Google Workspace
- Workday
- Oracle HCM
- ServiceNow
- Zendesk
- CrowdStrike
- Cisco
- Check Point
- F5
- Fortinet
- Palo Alto Networks
- Zscaler
- Splunk
- Literally hundreds more…
The OIN fosters support for de facto and industry integration standards like SSO federation via OIDC or SAML, identity data integration via the System for Cross Domain Identity Management (SCIM) to manage users in cloud-based systems. Additionally, the Okta Workflows Connector Builder toolkit contains the Okta API to secure access to application endpoints using OAuth 2.0 without user association as in the typical app-to-app or service-to-service use cases.
Okta’s Pricing/Licensing Model
The basic Okta pricing model is a per user monthly subscription fee. For most large organizations there is room for negotiation and enterprises don’t need to subscribe to the full portfolio of services. To give you a sense for the “list price” which is subject to change, Okta’s flagship SSO component is priced at $2/user/month, Adaptive MFA can add another $6/user/month, Identity lifecycle management is $4/user/mo. Workflows are $6/user/mo.
Our clients have expressed a good deal of satisfaction with Okta as of this writing, though most of them use the Okta SSO and Adaptive MFA capabilities and have not used some of the other important capabilities, including lifecycle management and identity governance. Most of our customers are also using SailPoint, Saviynt, Microsoft, Ping, ForgeRock and solutions like CyberArk or BeyondTrust/Delinea for Privileged Access Management (PAM).
Okta Developer Platform
Businesses require nimble capabilities to develop, deploy and retire myriad online applications that power their Digital Enterprises, electronic commerce initiatives and deliver significant revenue to the bottom line. Never has this been more prevalent than in the past three years, when the COVID-19 pandemic sent millions to the shelter of their own homes and spurred an unprecedented move towards online customer interaction for the acquisition of goods and services. In addition to e-commerce facing applications, the emergent work-from-home culture established an employer-employee relationship that depended as much on the efficacy of enterprise IT applications as it once did on face-to-face contact.
As TechVision Research has been emphasizing for the past several years, a combination of loose-coupling, virtualization and federation are critical characteristics for digital transformation and enterprise IT as a whole. Secure, API-enabled microservices create an ‘abstraction layer’ that can dramatically simplify application development, integration, data security, privacy, and operational support. With this comes the understanding of just how important Application Programming Interfaces (APIs) are to enabling and securing the modern Digital Enterprise. Please see the TechVision Research report titled “Architecting and Securing an API-Driven Economy” for a deeper look into this important area of IAM.
Okta’s Developer Portal has become a central utility for enterprise application developers and integrators for a range of use cases, such as adding authentication with Okta’s redirect model (opens new window) to server-side web applications. Additionally, many OIN partners (see above) build provisioning integrations (using the SCIM protocol) to automate lifecycle management use cases for their customers.
Via Okta’s API Access Management through Okta’s implementation of the OAuth 2.0 standard, developer access to APIs is integrated with Okta’s implementation of OpenID Connect for authentication. Similarly, Okta provides a client management API for onboarding, monitoring, and deprovisioning client apps. Okta’s customers can then publish their own “integrations” in the Okta Integration Network (OIN) catalog to expose the app to thousands of Okta workforce customers. In this fashion, Okta’s developer community enables a sort of secure open-source library for myriad IAM connectivity use cases.
Now that we’ve combed over the key components of Okta’s IDaaS offering, let’s see how these fit into the TechVision Research IAM Reference Architecture.
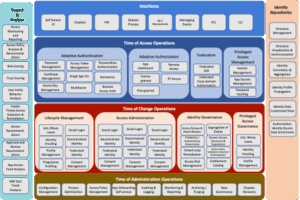
Okta and the IAM Reference Architecture
There are a lot of capabilities within the Okta IDaaS portfolio as we have just seen. In this section, we will map the Okta IAM capabilities with the TechVision Research Reference Architecture for IAM, which is a master template that identifies the IAM capabilities (rather than technologies) that can be improved or enabled, allowing business stakeholders and technical architects to achieve a common language for IAM functions. These functions can then be refined over time, and the purpose of the Reference Architecture is to maintain a “living, breathing” representation of the organization’s IAM strategy. Please note that considerably more information is available in the many TechVision Research documents that encapsulate the Reference Architecture for IAM within discussions about authentication, MFA, IGA, and Application Development. The overarching TechVision Research document titled “IAM Reference Architecture” is recommended as a good starting point to gather more information.
The following high-level template starts the IAM journey:
Figure 2: Top Level IAM Reference Architecture Template
These IAM capabilities are described at the highest level as:
Interact: Interact is a layer of user interaction (UI) and application programming interfaces (API) that simplify end user and application developer interaction with the rest of the IAM infrastructure. In this way, non-experts can follow the best practices of IAM without having to be experts in the field.
This allows the enterprise to:
- Incorporate new security capabilities without having to reengineer applications.
- Increase speed to market by removing security from the critical path of service development.
- Enhance security through the automatic adoption of best of breed security and privacy components.
- Decrease on-boarding friction by isolating complex security infrastructure through intuitive user interfaces.
From the Okta perspective, the Interact layer includes Okta SSO via Okta’s end-user dashboard, the Okta Admin Console, Developer Portal, and exposed APIs related to these functions.
Access: Access is the layer that answers the “Who has access to what?” question. It ensures customers can confidently exchange information and get the services they need to buy and use your products. It ensures employees and partners have all the digital resources they need to get the job done, nothing less and nothing more.
This allows the enterprise to:
- Ensure the right people have the right access to the right resources at the right time.
- Protect the assets of the company and its customers.
- Reduce productivity drains and costs caused when people can’t access the resources they need.
Okta supports these capabilities through the Identity Lifecycle and Okta Workflows, Identity Governance services, as well as the Authentication, MFA and SSO.
Change: Change manages the relationships between all the moving parts within the digital environment. Change establishes the connections between people, devices, applications, and data when they enter the environment, manages the connections while the relationship exists, and disconnects when access is no longer necessary.
This allows the enterprise to:
- Establish and maintain the proper rights, entitlements, and restrictions in order to reduce your attack surface, because Users and their identities are the most vulnerable link in a network.
- Orchestrate identity across device, network, and application boundaries because in the absence of the traditional security perimeter, identity is the common denominator across the entire digital environment.
- Prevent toxic combinations through transparency of entitlements across business processes.
Okta supports these capabilities through the Identity Lifecycle and Okta Workflows, Universal Directory, Identity Governance and Device Assurance services.
Manage: Manage is where the administrators of the IAM platform upgrade, configure, tune, troubleshoot, document, and audit the platform and its components.
This allows the enterprise to:
- Incorporate new security capabilities without having to reengineer applications.
- Increase speed to market by removing security from the critical path of service development.
- Enhance security through the adoption of best of breed security and privacy components.
- Increase agility through isolating security software releases and patches to the underlying infrastructure components.
These capabilities are enabled by the Okta Admin Console and Dashboard.
Measure: Measure is the lens into the digital environment. It allows live behavior observation, anomaly detection, platform health checks, and deeper analysis of usage and threats. It also provides the audit and reporting capabilities necessary to prove you are performing your duty to protect.
This allows the enterprise to:
- Understand behavior to improve the customer experience.
- Detect vulnerabilities before they are crises. The costs of prevention are much less than the costs of a breach.
- Prove compliance as required by law.
Again, these capabilities are enabled by the Okta Admin Console and Dashboard, they leverage key Okta resources such as ThreatInsight, Device Assurance, and others.
Store: Store is the shared place where the identity profiles, attributes, and relationships are kept and maintained. It may be physically centralized or distributed and contains the map which defines “who has access to what?”, often in the form of an entitlements catalog or database.
This allows the enterprise to support two important groups:
- For customers, it becomes the backbone for the entire customer experience; the customer data layer where all your interactions are captured.
- For employees, it becomes a user-centric view of entitlements across the entire digital environment.
These types of capabilities are supported via Okta’s Universal Directory.
We will now dissect these IAM capability descriptions in more detail below.
Capabilities of the IAM Functional and Technical Landscape
Now, let’s look at the next level of the architecture, which we subtly tailor to identify the functional capabilities that are the foundation for a best-in-class IAM Reference Architecture. Each category is broken up into multiple capabilities at a level of greater detail. For example, interfaces can be for applications / developers (APIs, messaging services), lines of business/LOBs, self-service, or even robotic processes. This applies to each category and, based on stakeholder input, use cases and priorities can be further developed into Reference Architecture patterns or templates for specific services.
Remember, at this level the Reference Architecture is not focused on the actual implementation of things that carry out these controls. Rather it is a model of what the controls are, how they work, and how they interact to assure the utility of content.
It is important to understand that these functional capabilities consider all type of objects and use cases within the IAM foundation. As ultimately implemented, different enterprises enable different IAM capabilities in different ways to meet different protection needs. And they do so differently for different content and business functions because of the different risks and potential consequences associated with failures and costs associated with protection. And they may do so with hybrid solutions that simultaneously run on-premises and in the cloud. One size does not fit all.
The next layer of the TechVision Research Reference Architecture for IAM (see below) allows us to identify the IAM capabilities that are to be supported in the hybrid IAM infrastructure.
Figure 3: IAM Capabilities Within Reference Architecture
With this information, technical architects can rapidly zero-in on the current options (technology and process) their IAM architecture should encompass to achieve the required capabilities for the business. In the form of architecture considerations, each of the options available is then described in more detail to help identify the right approach for an optimal IAM architecture and deployment strategy. In the subsequent section, we’ll look at sample IAM Reference Architecture patterns and map them to some of the key capabilities enabled by Okta.
Sample Okta IAM Reference Architecture Patterns
Now let’s look at some examples where our customers have deployed various IAM services. We will take a look at Okta’s authentication, SSO, runtime access management, IGA and workflow capabilities in the context of the Reference Architecture for IAM. Generically, the IAM capabilities are used as input to the development of the Reference Architecture pattern illustrated below:
Figure 4: Typical IAM Service Pattern
It is important to note that much of the overall IAM infrastructure supports or consumes the provisioning, workflow and IGA processing output. For example, the “login service” in the upper left corner relies on the IGA policies, birthright access provisioning, workflow, and approvals and so on to be able to function appropriately and securely through the “App Dashboard” (PEP, for policy enforcement point) – which interacts during runtime with the access policy repository (PDP, for policy decision point), the enterprise Active Directory and/or Enterprise LDAP and the entitlements catalog.
Now, let’s take a look at this IAM architecture pattern when the enterprise determines that it wants to leverage Okta.
Okta Pattern Example
Below is an illustration the Okta solution functions at a high level:
Figure 5: IAM Reference Architecture Using Okta IAM Capabilities
As this modified pattern shows, just about all the standard, required IAM capabilities as defined by our Reference Architecture are supported across Okta. The administrative and self-service interfaces along with the associated service request/response workflows are supported natively by the Okta platform.
It should be noted that one very important piece of a comprehensive IAM puzzle is Privileged Access Management (PAM), which manages privileged account credentials, such as systems administrator and application service accounts, and puts them inside a secure repository typically called a ‘vault.’ Once inside the vault, system administrators and application service accounts need to go through the PAM system to access the credentials in the vault, at which point they may authenticate to the target system and their access is monitored and logged. When the credential is checked back into the vault, it is reset to ensure administrators must go through the PAM system next time they want to use a credential from the vault. This method of vaulting credentials (or ‘secrets’) and checking credentials in and out on a real-time, as-needed basis accounts for most PAM approaches today. Okta does not yet have a PAM solution, although they can support “least privilege access” and centrally manage sudo privileges across server fleets (i.e., elastic stacks and agents). However, Okta has stated their intention to offer a comprehensive PAM solution in 2023, with limited early access starting in Q2/23 that is integrated with the product family reviewed here.
Hopefully, going through this exercise gives us increased confidence that Okta is evolving to a much more complete IAM platform that provides a basis for using it as the primary enterprise IAM foundation.
Summary and Recommendations
Okta took the IAM industry by storm a dozen years ago and has firmly established itself at the leader in the IDaaS market. Their meteoric rise is due to many factors including the inherent cloud-centric nature of the overall platform, strong marketing and early positioning as the modern cloud-based IAM solution. The timing couldn’t have been better as the IT world was rapidly moving from on-premises data centers to shared infrastructure in the cloud, the market was exceedingly ripe for an IDaaS that was (and still is) simple to implement and integrate and for many, cost effective as well.
This report on Okta (and our previous report on Microsoft Entra) comes at a time where most large enterprises are at an inflection point with respect to their future-state IAM foundation. The challenge is that there is no one vendor that meets all large enterprise requirements but having too many vendors creates tremendous complexity and rapidly escalating costs. There is further pressure to shore up enterprise IAM given its importance in building a secure, scalable and manageable digital capability.
We think Okta is a great fit for a number of organizations. There appears to be no doubt that Okta SSO is able to be deployed quickly, at scale and is very flexible in order to meet the needs of organizations that need to be very responsive to business conditions and partnership integration/de-integration. This platform is a mega toolkit for deploying federated SSO across a broad range of SaaS and web-based applications (in the cloud or on-prem) quickly and easily. Given that the Okta IDaaS platform runs on AWS and leverages a good deal of AWS’ global data centers, it is a scalable solution that can rely on AWS reliability and failover capabilities.
Okta has a very strong overall IAM solution and is addressing capabilities in areas they are not quite as strong such as Identity Lifecycle Management, IGA, PAM while continuing to add to its core IDaaS strengths. The challenge in fully consolidating around Okta (with a similar challenge for Microsoft Entra) is that vendors such as SailPoint, Saviynt, MicroFocus, CyberArk, Delinea and others have a long lead on developing identity lifecycle management, PAM and governance capabilities, whereas Okta has less mature offerings in these areas, but is ramping up their investment. Okta may also be a good fit for a CIAM strategy in that the needed capabilities (scalability, federation, ease of use…) are generally at a higher priority. It could also be perfect for your Enterprise IAM strategy, but that is typically a much more complex environment with legacy processes and technologies that require attention.
There is additional pressure to assess organizations are heavily entrenched in Microsoft IAM, desktop, endpoint management and Azure cloud deployments. Microsoft licensing, particularly the “E5” enterprise licensing that many large companies have acquired, includes an extensive amount of IAM functionality that is on par with Okta’s. In some cases, the emerging Microsoft Entra IAM suite is more feature rich – depending on your organization’s requirements.
In summary, our first in-depth look at Okta shows that their solid IDaaS SSO foundation is scalable, effective, and secure. For many organizations, this may fit the bill and the per user per month pricing is a good economic investment. Expanding this to include identity lifecycle management, workflows, identity governance and so forth should be undertaken in a thoughtful manner, realizing that incremental improvement to the organization’s overall IAM strategy should be deliberate and not hasty.
TechVision firmly believes that the future of IAM is in the cloud, and Okta exemplifies this pure play better than anyone today from a capability standpoint. However, you must take your own organization’s requirements for cost effectiveness into account. TechVision generally recommends a structured approach to such a critical infrastructure element like IAM and has developed a reference architecture that may be useful in evaluating the set of capabilities necessary for your future state IAM foundation. TechVision can help with this process.
Appendix 1: Historical Perspective on IDaaS
By the mid-1990’s – soon after the web began to grow exponentially in popularity, it became apparent that there needed to be a way manage users access to specific web content. This momentum was largely triggered by the e-commerce boom that the web intrinsically enabled. Mechanisms for creating and maintaining user identities (user IDs) and passwords were integrated with web servers, largely via the Lightweight Directory Access Protocol (LDAPv3), which not so ironically was also become table stakes for the growing internet industry. E-Commerce “portals” became more popular, customer identity management was born, credit card information was obtained and stored – and cybersecurity never looked the same again.
On the enterprise side, organizations of all shapes and sizes were deploying initial or augmenting existing TCP/IP networks to connect to the internet. Employee portals became a standard service within each enterprise that allowed employees to direct their browsers to a specific, internet-addressable front-end that would give them access to numerous business, productivity, manufacturing, supply chain and other such applications that comprised enterprise’s digital landscape. As in the e-commerce space with consumer identities, these corporate IP networks needed a viable means for managing employee (and contractor!) identities, passwords and just as importantly information access rights.
Around this time, network operating system (NOS) directories were becoming very commonplace within most enterprises. Chief among these directory services were Novell’s NetWare Directory Service (NDS), Microsoft Active Directory and Banyan Vines. NOS directories were largely responsible for managing users’ access to the corporate IP network, managing access to file and print services as well as managing machine (PCs, printers) identification. Also becoming more ubiquitous within many enterprises were what were termed “enterprise directories”, which were almost always but not exclusively LDAPv3 directories implemented to house a superset of employee and contractor identity data over and above the information typically stored in the NOS directories. A new industry was born around the concept of enterprise directories and authoritative source identity data integration with various HR systems and other relational database environments. Vendors such as Netscape, iPlanet, Sun Microsystems, Zoomit, Metamerge, SoftSwitch, ISOCOR enjoyed substantial demand for their directory integration solutions – at the time referred to as “meta directories”.
But that wasn’t the end of it. It soon became apparent that more sophisticated means for managing “run time access control” – including user authentication was necessary. At this point, web access management (WAM) entered the stage. Web access management systems act as control points over user and application interaction with Web-accessible resources. These systems typically run in the operational environment but rely on authoritative directory services and other repositories to obtain information about users and policies.
Access management systems have enabled enterprises to provide common authentication and authorization services to web-based applications (whether internally and externally facing). A key capability enabled by WAMs is that users are able access many applications with a single sign-on. Access management systems also improve the ease of administration, using rules and delegated administration to create scalability in policy management, even with fine-grained access controls.
Organizations integrate WAM systems with web portals and support access policy management functions in coordination with enterprise identity management and directory services. When the WAM era began, the industry leaders in this space were vendors like Netegrity SiteMinder (now owned by CA), Oblix NetPoint (now owned by Oracle and called Oracle Access Manager (OAM)), and IBM/Tivoli Access Manager (TAM) (now called WebSeal). Those were the leading on-premises solutions twenty-two years ago and many are still in use today. WAMs would sit behind network load balancers and receive user authentication requests, query the enterprise directory to validate username and password, look up access control policy and if these steps passed muster, create a header-resident security token that would be passed along on the web re-direction to tell the target application that the user had authenticated successfully. These are the basics of SSO that are still largely in use today.
In the mid-to-late 2000’s, cloud computing made its entre into enterprise networking and data center footprint. Since that time, enterprises of all ilk have begun, are in process or have completed migration of many types of IT infrastructure from on-premises into the cloud, in large part facilitated by the Big Three cloud infrastructure as a service (i.e., IaaS) providers: Amazon Web Services, Google Cloud Platform and Microsoft Azure. Additionally, vendors like Salesforce, Workday, Microsoft Office and many, many others have made workforce productivity (e.g., sales, human resources, business productivity, etc.) solutions available as software as a service (SaaS). This roughly eighteen-year period between 2005 and now has seen the rise of hybrid IT in myriad shapes and forms, consisting of a mix of on-premises and in-cloud IT functions and services.
And, around this timeframe – beginning in 2009, Okta was conceived as what was then and still is referred to as an Identity as a Service (IDaaS) solution. Initially, Okta created a cloud-resident WAM solution that essentially off-loaded the burden of on-premises SSO and access control. Within a few years, Okta became a massive success and enterprises around the world began to consider migration to the Okta IDaaS in concert with their overall cloud migration strategies.
Due to this meteoric success, Okta has continued to develop IDaaS solutions and capabilities and has further cemented its legacy and leadership in the cloud identity management space.
About TechVision
World-class research requires world-class consulting analysts, and our team is just that. Gaining value from research also means having access to research. All TechVision Research licenses are enterprise licenses; this means everyone that needs access to content can have access to content. We know major technology initiatives involve many different skillsets across an organization and limiting content to a few can compromise the effectiveness of the team and the success of the initiative. Our research leverages our team’s in-depth knowledge as well as their real-world consulting experience. We combine great analyst skills with real world client experiences to provide a deep and balanced perspective.
TechVision Consulting builds off our research with specific projects to help organizations better understand, architect, select, build, and deploy infrastructure technologies. Our well-rounded experience and strong analytical skills help us separate the “hype” from the reality. This provides organizations with a deeper understanding of the full scope of vendor capabilities, product life cycles, and a basis for making more informed decisions. We also support vendors in areas such as product and strategy reviews and assessments, requirement analysis, target market assessment, technology trend analysis, go-to-market plan assessment, and gap analysis.
TechVision Updates will provide regular updates on the latest developments with respect to the issues addressed in this report.
About the Authors
 Doug Simmons brings more than 25 years of experience in IT security, risk management and identity and access management (IAM). He focuses on IT security, risk management and IAM. Doug holds a double major in Computer Science and Business Administration.
Doug Simmons brings more than 25 years of experience in IT security, risk management and identity and access management (IAM). He focuses on IT security, risk management and IAM. Doug holds a double major in Computer Science and Business Administration.
While leading consulting at Burton Group for 10 years and security, and leading global identity management/security consulting at Gartner for 5 years, Doug has performed hundreds of engagements for large enterprise clients in multiple vertical industries including financial services, health care, higher education, federal and state government, manufacturing, aerospace, energy, utilities and critical infrastructure.
 Gary Rowe is a seasoned technology analyst, consultant, advisor, executive and entrepreneur. Mr. Rowe helped architect, build and sell two companies and has been on the forefront the standardization and business application of core infrastructure technologies over the past 35 years. Core areas of focus include:
Gary Rowe is a seasoned technology analyst, consultant, advisor, executive and entrepreneur. Mr. Rowe helped architect, build and sell two companies and has been on the forefront the standardization and business application of core infrastructure technologies over the past 35 years. Core areas of focus include:
Identity and Access Management, business/technology trends, cloud computing, security/risk management, privacy, innovation, AI, new IT/business models and organizational strategies.
Prior to starting TechVision Research he was President of Burton Group from 1999 to 2010, the leading technology infrastructure research and consulting firm. Mr. Rowe grew Burton to over $30+ million in revenue on a self-funded basis, sold Burton to Gartner in 2010 and supported the acquisition as Burton Co-President (now Gartner for Technical Professionals) at Gartner.