Cloud-based IoT Ecosystems fuel the AI Economy
Publication Date: September 12, 2024
Abstract
Critical to the success of any Artificial Intelligence (AI) program is the systematic collection of the vast quantities of data required to train AI models. Next-generation AI will be fueled by the data created by the expansive universe of connected Internet of Things (IoT) devices. Scaling IoT requires a well-orchestrated ecosystem and this starts with the cloud vendors and cloud-based IoT hubs to assist in this process.
A world that maps physical devices and services to individuals and enterprises has often been a missing link in maximizing the value of the modern Digital Enterprise. IoT ecosystems are tasked to better govern, manage, secure, and integrate IoT devices and IoT-generated data to support a diverse set of use cases.
The foundation for this emerging and pervasive IoT ecosystem requires scalable methods for determining how devices and data generated by these devices are identified, secured and accessed. These ecosystems are generally very large and include registration, connectivity, and IAM-centric services including zero-trust principles such as device authentication, authorization, data security and more.
In this light, we’ll describe and evaluate two primary cloud infrastructure providers – Amazon and Microsoft and their respective IoT management platforms. We’ll then conclude this review with pragmatic recommendations and an enterprise action plan for building an effective and manageable IoT program.
Authors:
Doug Simmons Gary Rowe
Principal Consulting Analyst CEO/Principal Consulting Analyst
[email protected] [email protected]
Executive Summary
While much discussion around IoT has typically centered around consumer devices such as connected (intra and inter-operable) cars, home appliances (refrigerators, thermostats, washers and dryers) garage doors, home lighting, and security systems, the impact of IoT today is being felt much more directly within the enterprise. While such consumer-oriented use cases nudge the hype meter for IoT ever higher, the realm of IoT devices isn’t just in the home automation environment. Forthcoming designs and devices will include low-cost sensors embedded in just about everything related to our business and personal lives. Coupled with rapidly evolving and expanding Artificial Intelligence (AI) capabilities surrounding the IoT environment, we can see how so many “things” will likely yield an exceedingly useful – and risky, future.
IoT is ultimately well suited for most of today’s enterprise processes currently leveraging human monitoring and control. It also has an enormous capability of capturing data at scale. Examples of IoT devices include things like pressure sensors, temperature and humidity sensors, accelerometers, etc. They capture information about a specific environment where they’re located. For example, an accelerometer could indicate whether the elevator is at rest or in motion. Often, such devices are part of a manufacturing shop floor, hospital, utility grid, or warehouse ecosystem. They span multiple vertical industries. However, because such capabilities can be augmented by and integrated with big data analytics, AI, machine learning and other emerging technologies, we must ensure that proper physical and logical security mechanisms are in place as this data proliferation escalates.
Enterprise IoT deployments may involve just about anything that can collect data via an embedded sensor with a means of communicating the collected data or measurements. These IoT devices will often be managed by a gateway or intermediary control system that processes the device-captured data, determines the desired or resultant behavior and operation, and concurrently allows for manual observation and intervention. These control systems may send instructions to the appropriate device, or group of devices. In fact, most manufacturing and distribution industries where Industrial Control Systems (ICS) are rapidly becoming IP-addressable have a plethora of use cases involving registration, communication and management with myriad devices across their environments.
For a deep dive into the Operational Technology (OT) and Industrial Control Systems (ICS) security and integration approaches, technologies and best practices, please see the recent TechVision Research document titled “OT/ICS Security”. The energy and utility industry, for example, has many early use cases for such devices, sensors and controller interactions on a very large scale. For example, smart meters on homes and businesses are a foundation for better controlling and managing energy usage and reporting. They can also be a platform for new types of applications such as variable rate energy prices to encourage usage during non-peak periods.
As demand for scalable and secure IoT capabilities increases, the introduction of cloud-based IoT “hubs” and “control centers” brings a clear ability to design and deploy secure IoT services that tie directly with the business – without developing and securing an IoT networking data center on your own. With the rapid rise of 3rd party IoT integration capabilities from smart devices that communicate using standard protocols like MQTT (i.e., Message Queuing Telemetry Transport), as well as the ability to integrate devices – whether smart, dumb, active or passive, into the IoT ecosystem with APIs that development organizations can use ‘right out of the box’, the landscape for IoT device enablement becomes in focus.
If you look carefully at your own organization and the vertical industry(ies) it addresses, there is very likely a fount of existing use cases, 3rd party IoT edge solutions and good practices for designing, deploying, securing and monitoring your IoT environment to bring your strategy to life. But be aware that with IoT deployments it becomes all about the data. This means that from the enterprise perspective, there is data streaming from sensors, actuators, industrial control systems, public utilities and so on. To be sure, there are significant risks of data exposure to nefarious actors, which introduces new concerns in terms of data privacy and intellectual property protection.
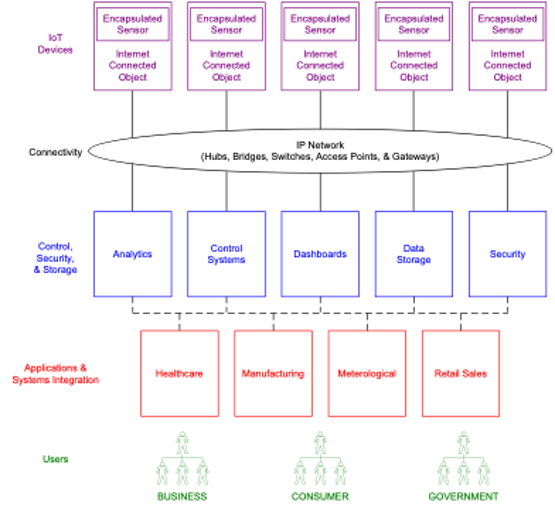
TechVision’s conceptualized overview of the elements comprising an Internet of Things ecosystem is illustrated in Figure 1 below. This ecosystem includes interconnected devices with encapsulated sensors that monitor and collect data shown across the top. These sensors can either be autonomous or governed remotely and can transmit data to other interconnected devices including analytic processing systems, automated control systems, manually operated dashboard systems, data storage systems, security (access and authentication) systems, and so forth. These types of data collection and sharing ecosystems are of considerable value to businesses, consumers and government entities.
Figure 1: Internet of Things Ecosystem
Every large enterprise can benefit from a well-thought-out IoT strategy. Some notable industries currently adopting and building out secure IoT ecosystems:
- Energy and Utilities
- Healthcare
- Logistics and Manufacturing
- Transportation
- Financial Services
- Food Services
- Government Municipalities/Military
- Retail
What is really interesting is the growing number of enterprise IoT use cases and scenarios that are appearing. Telemetry – defined as “the process of recording and transmitting the readings of an instrument” is one of the most basic and useful capabilities extended by IoT integration with a logically centralized IT infrastructure. With the establishment of cloud-based IoT connectivity hubs from AWS, Microsoft and others, the path of (adoption)resistance shrinks considerably. By embedding myriad appropriate security capabilities within the IoT ecosystem, from SDKs that contain X.509 key management to extensive monitoring and configuration management, the hundreds and even thousands of telemetric and process control-enabled devices that comprise many enterprise operational infrastructures are able to be active and secure participants in the mission-critical role of real time data gathering and processing – if done right.
Simply put, those organizations that are utmost prepared to protect their large-scale deployed applications realized through the interconnection of diverse digital assets and able to quickly recover from the entire gambit of security threats will ultimately deliver the potential benefits afforded by the IoT. There is an enormous amount of information and awareness regarding IoT integration, configuration and security being made available today. TechVision generally recommends a structured approach to such a critical infrastructure element like secure IoT integration and deployment, and has developed a Reference Architecture that may be useful in evaluating the set of capabilities necessary for your future state IoT foundation. TechVision can help our clients architect, build and manage this process.
Introduction
IoT is one of the fastest growing and most widely hyped areas in technology; perhaps only competing with artificial intelligence (AI) and before that – blockchain. That said, IoT is ultimately well suited for most of today’s enterprise processes currently leveraging human monitoring and control. It also has an enormous capability of capturing data at scale. These capabilities can be augmented by integrating with big data analytics, AI, and machine learning along with other emerging technologies, but we must ensure that as this data escalates, proper physical and logical security mechanisms are in place. Examples of IoT devices include things like pressure sensors, temperature and humidity sensors, accelerometers, etc. They capture information about a specific environment where they’re located. For example, an accelerometer could indicate whether the elevator is at rest or in motion. Often, such devices are part of a manufacturing shop floor, hospital, utility grid, or warehouse ecosystem. They span multiple vertical industries.
IoT devices can communicate with back-end services in both directions. However, many IoT devices may have limited power, and connectivity may be slow or intermittent. The back-end services receive telemetry data at scale from the devices and determine how to process and store that data. They also communicate with the device and manage the device lifecycle by controlling and monitoring the operational state of the device.
There are lots of moving parts associated with discovering, identifying, securing, provisioning, supporting and governingInternet of Things objects. Organizations need to be proactively addressing and architecting this foundation because “things” are being connected to enterprise networks at an unprecedented scale. This scale, the nascency of IoT standards, the lack of device intelligence and overall diversity of the “things” being introduced to enterprise networks makes this a particularly challenging and potentially risky endeavor.
To take full advantage of IoT, there is an evolving ‘IoT ecosystem’ to make use of the massive amount of data being collected and devices being controlled. Because there are generally too many IoT devices to individually manage, the IoT ecosystem generally connects devices to a hierarchy of control systems or gateways that ultimately combine remote monitoring and operational support/management with policy-driven levels of participation and sharing.
In the TechVision Research document titled “Identity of Things (IDoT)”, we introduced an important new category of IAM that specifically supports the scale, can integrate IoT identifiers and can handle the variety of contextual data and relationships associated with “things” that are increasingly accessible and integrated with internal and external networks. Added to this, IoT raises complex IAM-related challenges such as handling device ownership transfers, assigning identity and trust levels when a hardware ID isn’t already provided by the device manufacturer, and, of course, the massive potential scale and its potential impact on the network and connected systems.
To recap, our IDoT report outlined three basic categories of IAM support:
- Hardware/IoT Ecosystem Providers: Large IoT device manufacturers initially focused on building the mechanisms for registering and identifying devices, managing these endpoints and providing appropriate access. These are generally proprietary environments for the devices associated with the manufacturer of the connected devices.
- Major Technology Platform/Cloud Providers: This approach extends the IDoT and IoT ecosystem to the major platforms, service providers and cloud vendors extending IoT capabilities and connectivity to organizations already using these IT platforms. These ecosystems are generally proprietary (but very large) and include registration, connectivity and IAM services.
- Identity and Access Management Providers: This category represents vendors and service providers that are focused on providing IAM as a service supporting IoT. In most cases these are general purpose IAM offerings that are being adapted or extended to support IoT. The first two categories have been the easiest path towards enabling IoT services within the enterprise as they leverage early ecosystems being built by hardware manufacturers and major platform/cloud vendors. The challenge is that these categories create silos limiting access outside of the proprietary ecosystems. Long term, we see the Identity and Access Management providers expanding their offerings to more seamlessly accommodate IoT and the zero trust principles the IoT ecosystem must support.
Today, the most pervasive and potentially scalable option is through the major technology platform/cloud providers (#2 above). Therefore, we are diving into two of the primary (i.e., pre-eminent) cloud infrastructure providers – Amazon and Microsoft, each of whom offer an IoT management platform that many organizations are beginning to rely on more extensively for IoT adoption and expansion. It bears mentioning that Google Cloud Platform (GCP) had at one time been considered one of these leading, albeit nascent, cloud IoT platforms. However, in 2023, Google announced that its cloud IoT platform would be discontinued.
In conjunction, we’ll address the IAM impacts and capabilities associated with IoT integration and security. However, before we do that, let’s briefly recap the current state of the evolving “IoT ecosystem” in general.
A Look At the Evolving IoT Ecosystem
While much discussion has typically centered around consumer devices such as connected (intra and inter operable) cars, home appliances (refrigerators, thermostats, washers and dryers) garage doors, home lighting and security systems, the impact of IoT today is being felt much more directly within the enterprise. While such consumer-oriented use cases nudge the hype meter for IoT ever higher, the realm of IoT devices isn’t just in the home automation environment. Forthcoming designs and devices will include low-cost sensors embedded in just about everything related to our business and personal lives.
Enterprise IoT deployments may involve just about anything that can collect data via an embedded sensor with a means of communicating the collected data or measurements. These IoT devices will often be managed by a gateway or intermediary control system that processes the device-captured data, determine the desired or resultant behavior and operation, and concurrently allows for manual observation and intervention. These control systems may send instructions to the appropriate device, or group of devices. In fact, most manufacturing and distribution industries where Industrial Control Systems (ICS) are rapidly becoming IP-addressable have a plethora of use cases involving registration, communication and management with myriad devices across their environments. For a deep dive into the Operational Technology (OT) and Industrial Control Systems (ICS) security and integration approaches, technologies and best practices, please see the recent TechVision Research document titled “OT/ICS Security”. The energy and utility industry, for example, has many early use cases for such devices, sensors and controller interactions on a very large scale. For example, smart meters on homes and businesses are a foundation for better controlling and managing energy usage and reporting. They can also be a platform for new types of applications such as variable rate energy prices to encourage usage during non-peak periods.
Today, RFID tags and smart communication “chips” are being integrated into equipment and individual components during the manufacturing process. For instance, as products are manufactured details surrounding each step in their production may be observed and recorded in real-time including subassemblies and piece-parts. Analytics may be applied to this rich set of business data and potentially yield improved insight into operations and processes that can lead to improved business performance. In an inventory management setting, this data will provide the ability to optimize purchase rates and pricing during procurement based on current quantities and anticipated demand.
This ability to tag components early on is a breakthrough technology for asset management, inventory management, delivery tracking and many other applications. While these types of systems work today, the ability to scale these solutions to enable better automation, management, auditing, and tracking via the development of a managed ecosystem can dramatically improve the efficiency and effectiveness of even such straightforward use cases.
TechVision’s conceptualized overview of the elements comprising an Internet of Things ecosystem is illustrated in Figure 2, below. This ecosystem includes interconnected devices with encapsulated sensors that monitor and collect data shown across the top. These sensors can either be autonomous or governed remotely and can transmit data to other interconnected devices including analytic processing systems, automated control systems, manually operated dashboard systems, data storage systems, security (access and authentication) systems, and so forth. These types of data collection and sharing ecosystems are of considerable value to businesses, consumers and government entities.
Figure 2: Internet of Things Ecosystem
Every large enterprise can benefit from a well thought out IoT strategy. Some notable early industries adopting building out IoT ecosystems:
- Energy and Utilities
- Healthcare
- Logistics and Manufacturing
- Transportation
- Financial Services
- Food Services
- Government Municipalities and Military
- Retail
While most industries have a wide range of use cases, there is a consistent opportunity for most enterprises to automate, replace, optimize or in some way augment repetitive human actions with the use of smart interconnected devices. For example, in a hospital setting (e.g., healthcare) the automated monitoring of blood pressure, oxygen saturation, respiration, electrocardiograph and life-sustaining vital indications is becoming standardized and increasingly connected.
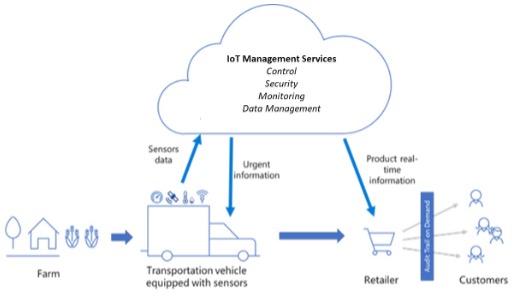
Another simple but very common example involves a logistics company responsible for transporting perishable food products from the growers to the retailers. In the process of transportation, the food needs to be maintained at the correct temperature, humidity, and light exposure.
Figure 3: IoT in Logistics Management Example
As illustrated above, the trucks each have individual sensors that track temperature, humidity, and light exposure. In this scenario, IoT solutions ensure the fruit is fresh and untampered with over the journey. In the simplest case, the food status (e.g., temperature) is tracked using sensors throughout the journey: from Farm to Table. In summary, everything becomes interconnected: objects can be identified and recognized, controlled and managed based on the devices inherent sensing, actuating, and processing capabilities ranging from simple RFID tags to sophisticated control and logistics systems. Now, let’s take a look at some of the main classes of IoT devices.
Active and Passive Devices
In Figure 4 below, we show there being two basic classes of IoT devices:
- Passive – these types of devices communicate data to a control system in a one-way data flow (from device to control system). Typical devices in this class are sensors, RFID tags, data collection/ingestion modules, telemetry devices, utility meters and so on.
- Active – devices in this class are largely communicating in a bi-directional, two-way manner such as actuators, cellular/Bluetooth/wi-fi technology, micro-controllers, near-field communication (NFC) devices, etc.
Figure 4: Classifying Active vs. Passive Devices
In classifying devices that make up the IoT landscape in this way, we can apply a more risk-informed lens to the degree of the authentication and access control functionality that should be extended to any given device. For example, passivedevices will typically require less security capabilities because these devices are communicating only from “device-to-mothership”. The level of authentication and authorization required to communicate with the device will be less, because the risk associated with a device hack is theoretically lower. An example is a sensor that communicates one-way only – such a device cannot be commandeered by a hacker to become a malicious bot on your network. Likewise, the operations associated with device registration, provisioning and life-cycle management are necessary but also typically less of a risk.
On the other hand, an active device theoretically enables a richer attack surface. The device’s identity, credential(s), access privileges/entitlements, ownership and so forth are necessary aspects of its lifecycle management and authentication/authorization capabilities. Continuing with an example similar to passive devices, active devices can be hacked and turned into malicious, two-way communications agents on your network if these important security operations are not managed in accordance with your enterprise risk profile.
Lifecycle Management of Things
Device management is comprised of a critical set of capabilities that determine how an active or passive device participates in the IoT ecosystem. Similar to Identity and Access Management (IAM) functionality related to people (i.e., employees, contractors, business partners, customers), devices need to be uniquely identified, registered, maintained, and in many cases, authenticated and authorized for specific functions.
In the TechVision Research document titled “Identity of Things (IDoT)”, we deep dive into the specific IAM capabilities such as these that an IoT ecosystem may require and ultimately support. In summary, key IAM requirements include the ability to:
- Uniquely identify every device
- Register the device within the IoT platform
- Assign authentication credentials
- Grant access privileges to send or receive data
- Monitor device usage, characteristics, anomalies, etc.
A significant component of this set of procedures is one of initial ‘discovery’ of IoT devices that exist or ‘show up’ in the OT/IT infrastructure. We discuss the various discovery processes in more detail in the TechVision Research report titled “OT/ICS Security”, but in summary, the best way to discover (I)OT assets is to start with passive monitoring of the network by spanning the network traffic.
This form of “dynamic IoT device discovery and profiling” automates device lifecycle management processes that allow specific devices on the network. IoT integration and security solutions can provide the IoT device discovery capability that forms the critical foundation for establishing security. Both device discovery and profiling can be included as modules within routers, gateways, threat management utilities, and other similar devices that allow inbound and outbound network traffic because these tools are backed by a knowledge base, which helps detect new devices even without any foreknowledge of them. Then, the beginnings of lifecycle management in the form of device registration and access provisioning can take place.
Once devices are registered and provisioned (i.e., lifecycle management), devices must be capable of providing identifiers and credentials when connecting to data collection or monitoring services (i.e., the IoT management platform). These identifiers will then be correlated with appropriate entitlements and access privileges in determining appropriate access. In a manner similar to authorizing access to networks and services to end users, devices must have risk-appropriate access privileges assigned to them.
Current IT security and IAM infrastructure typically supports group membership, role or attribute based access control (e.g., RBAC and ABAC, respectively), but may need be extended to consider a variety of IoT devices, relationships and enterprise security policies. In some cases, the enterprise IoT infrastructure will need to facilitate simple-but-safe means of managing device access privileges on par with what we have become accustomed to providing for human users.
All of this sounds daunting, but in the following section we’ll outline “what good looks like” from an IoT integration and security standpoint.
IoT Integration Reference Architecture
At the heart of the IoT Integration Reference Architecture are the mechanisms by which devices – whether dumb, smart, active or passive are discovered, securely identified, and integrated from a tamper-proof data transmission and controls surface standpoint. In the next sections, we’ll look at these key mechanisms and capabilities in more depth.
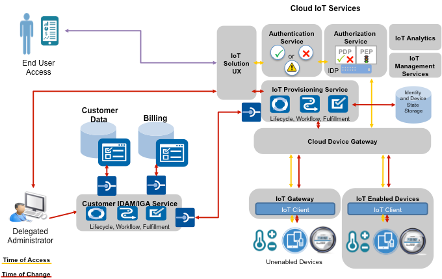
APIs, Gateways and Wrappers
As shown in the illustration below, a variety of devices will be connected to the enterprise; some via edge gatewayssupporting “dumb” (unenabled) devices and more sophisticated IoT-enabled devices that can directly connect. Note that “dumb” device does not imply “passive”, it simply means the device does not have IoT integration capabilities built-in. Active devices may be “dumb” because they do not natively connect to the network and interact with IoT management and monitoring capabilities.
Whether natively unenabled or enabled (dumb or smart, respectively), these devices and edge gateways will generally tie into a cloud-based ecosystem that supports a variety of IAM, security and auditing services including provisioning, deprovisioning, authentication, authorization, management and analytics. A variety of user types (individuals, devices and applications) will access these services and they will be supported by a set of administration, lifecycle management and other back-end services. These back-end services may also support connections to customer and internal databases.
For such purposes, APIs and gateways can function as the “abstraction layer” between dumb or passive devices. An IoT gateway is a centralized hub that connects IoT devices and sensors to cloud-based computing and data processing. Modern IoT gateways often allow bidirectional data flow between the cloud and IoT devices. Similarly, IoT ecosystem APIs can provide a more direct way to interface with edge devices and the IoT management system or specific IoT-enabled applications. At a high level, both APIs and gateway provide some glue between the edge devices and the IT systems that depend on the data they provide.
In the illustration below, we show how an IoT ecosystem functions in the form of a TechVision Research Reference Architecture pattern:
Figure 5: Reference Architecture for IoT Ecosystem
A major challenge in architecting and deploying such modern capabilities for IoT devices is simply focused on properly and securely identifying these devices (e.g., authentication, “Time of Access”). It can be difficult in that most sensors and monitoring devices will generally communicate using a proprietary protocol and may not have a media access control (MAC) address or standard way of identifying the device. This is often managed by pointing the IoT devices towards a gateway positioned to aggregate data from and manage multiple sensors.
IoT/Security Considerations
As TechVision described in our recent reports titled “OT/ICS Security”, “Multi Cloud Cybersecurity Reference Architecture”, “Zero Trust Networking”, “Zero Passwords in a Zero Trust World” and “The Future of Identity Management 2023+”, the security attack surface is growing exponentially and IoT is a major part of this vulnerability. The IoT landscape provides a variety of entry points across all layers for hackers to exploit, including attacks such as:
- Silicon – tampering with device identification
- IoT Objects – redirection and token/password snooping
- Local Networks – command injection and man-in-the-middle spoofing
- Gateways – data manipulation
- Global Networks – snooping
- Cloud Services – DDoS attacks
- Cloud Applications – data manipulation and software application repurposing.
In order to ensure privacy and security, traditional digital security tenets must be re-examined in the era of IoT with these specific considerations:
- Device identity: The IoT requires strong device identity and Root of Trust at its foundation. Hardware-based security, where appropriate, is a key ingredient for enabling this functionality.
- Secure network scale: For many IoT deployments, the number of IoT endpoints will dwarf those in traditional IT projects. Securely managing the network connections and data across these devices requires a scalable solution. Today, public key infrastructure (PKI) is often used to enable trust between systems based on digital certificates. PKI has been proven to scale; however, the device and environmental characteristics of IoT create a challenge for the secure issuance and processing of certificates. Coupling PKI with a strong device identity is needed.
- Data security and physical security: Building security into the data itself, whether it is in transit (data communication) or at rest (data storage), is valuable in the IoT, given the lack of physical security that resists tampering for most devices. Therefore, tamper-resistant physical security — which can be addressed with hardware security — becomes critical. Key control data and sensor data are now accessible, which can also be addressed with hardware security.
In the following section, we’ll look at the future state for IoT integration and security.
Future State of IoT
It isn’t just connecting the devices – rather, it is analyzing and securing the massive amounts of data that is generated from these connected devices. This data will drive AI use cases. IoT-enabled big data will really reap benefits from data fusion: the combinatorial effect resulting from the ability to mine, correlate, integrate, and map, or fuse, IoT device-generated sensor and other data to provide insights into projecting simulations. These advancements in business intelligence can help enterprises achieve real business outcomes previously unattainable.
For example, the continuous integration of applications with sensors allows for smart systems to become increasingly smarter as they learn based on greater quantities and improved analysis of the data collected and measured. Entire business models beginning with the sales agreement, during manufacture and delivery, through the warranty and maintenance period and until retirement can be considered in a single integrated approach. Moving from streamlining processes that only consider an intradepartmental data view to encapsulating sales with supply, manufacturing and operations data provides new opportunities for efficiencies to become realized and capitalize on opportunities as they arise.
In summary, the combination of IoT devices with data analytics and such will enable:
- Centralized functions to become self-monitoring allowing for real-time allocation
- Cost reductions via improved utilization and productivity gains
- Data fusion between context, location and state of related objects
- IT designs where everything is connected
- Real time analysis and application of feedback according to current conditions
- Better research data, better predictive analytics and better decision metrics
So, we see continuing momentum between IT and OT and the resulting need for IAM technology and techniques to help them integrate securely and effectively. That being said, what are some of the main solutions being developed and deployed to bring this vision to fruition? The sections that follow provide an overview of two of the top cloud infrastructure providers’ IoT ecosystem offerings:
- Microsoft Azure IoT
- Amazon AWS IoT Core
What about Google? Well, Google Cloud Platform (GCP) had at one time been considered one of these leading, albeit nascent, cloud IoT platforms. However, in 2023 Google announced that its cloud IoT platform would be discontinued. According to Google, the decision was made in order to “focus their efforts on a limited number of products that will have the biggest impact.” This means that they will no longer be supporting IoT devices and applications. This is certainly an interesting development in that it leaves enterprise customers that have invested heavily in the GCP ecosystem wanting, and may ultimately lead them to consider another, competitive platform (e.g., Microsoft or Amazon). However, it is also important to note that as of this writing, there a number of vendors offering IoT platforms for integration. This includes names like Software AG, ABB, Hitachi and many others who are in many ways ‘niche’ players focused on specific vertical industries, geographies and use cases. Many of these may run on GCP. However, from the perspective of a multi-purpose, cloud-centric IoT ecosystem, Microsoft and Amazon lead the market – at least for the time being.
Top IoT Cloud Vendors
Microsoft Azure IoT Hub
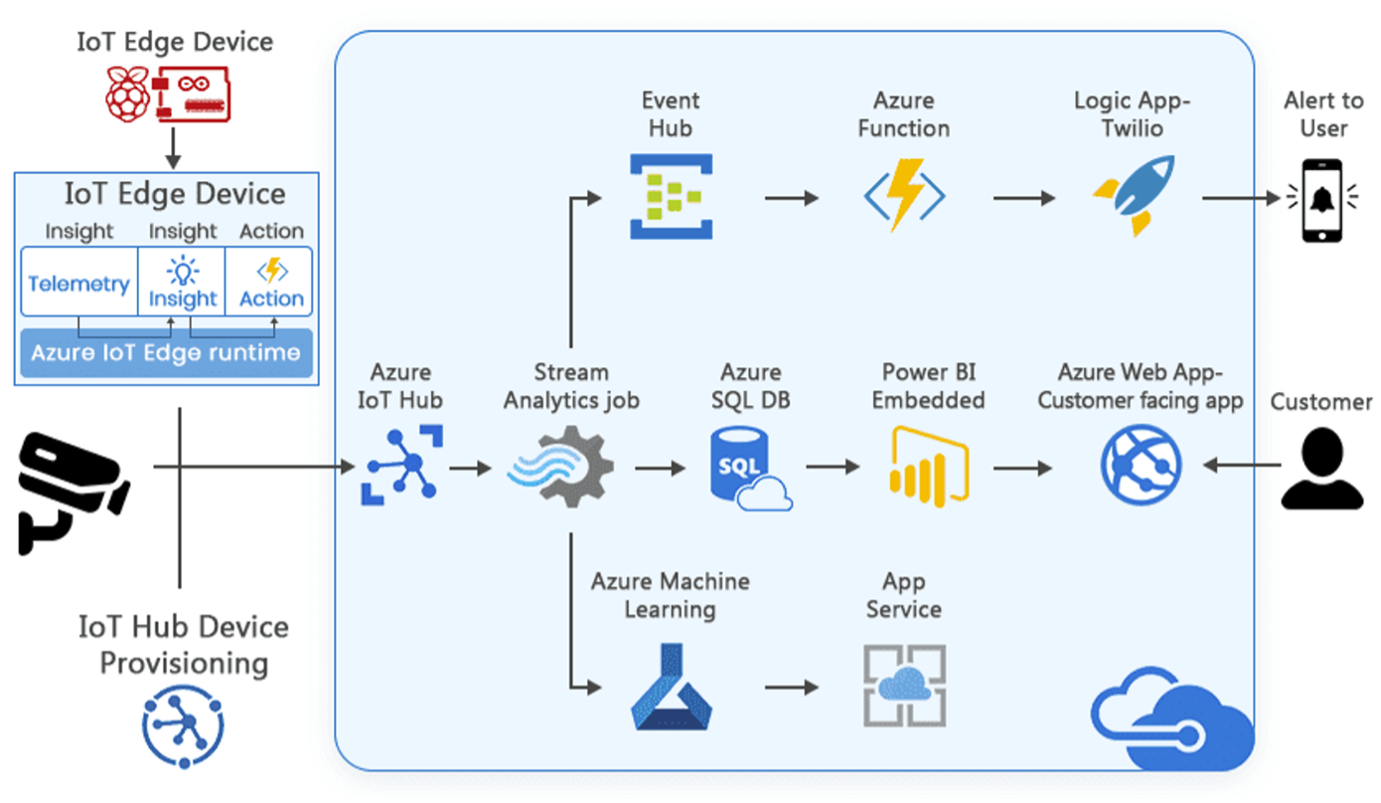
As described by Microsoft, the Azure Internet of Things (IoT) Hub is a collection of Microsoft-managed cloud services that connect, monitor, and control up to millions of IoT assets.
Figure 6: Azure IoT Hub (Source: Microsoft)
The Azure IoT product portfolio presents two paths for creating solutions: Platform as a Service (PaaS) and Software as a Service (SaaS).
- Platform as a Service solutions – this approach contains Azure IoT solution accelerators that are customizable PaaS solutions for specific industry verticals. Microsoft’s/partners’ IoT solution accelerators provide pre-built solutions that provide more granular options within a vertical. Examples of IoT solution accelerators include Remote Monitoring, Connected Factory, Predictive Maintenance, and Device Simulation.
- Software as a Solution solutions – these are suited for organizations with fewer device models, more predictable scenarios, and limited IoT device integration capabilities. Azure IoT Central is a managed SaaS solution and is typically more suitable when the IoT needs are straightforward and relatively little cloud development expertise is required.
In this report, we focus on Azure IoT Hub PaaS technologies, which are categorized as follows:
- Device support
- IoT
- Data and Analytics
- Visualization and Integration
We describe each of these four categories and their subcomponents briefly below.
Device Support
Azure IoT provides numerous capabilities to support a range of devices, including Azure IoT Device SDK, Azure IoT certified devices, Security Program for Azure IoT and Windows 10 & 11 IoT.
IoT
The suite of IoT technologies include:
- Azure IoT Hub:Azure IoT Hub is a managed service that enables bidirectional communications between large numbers (e.g., millions) of IoT devices and a solution back end to connect, manage, and scale IoT devices from the edge to the cloud.
- Azure Time Series Insights:Azure Time Series Insights lets enterprises store, visualize, and query large amounts of time series data generated by IoT devices to gain actionable insights.
- Azure Sphere:Azure Sphere is an end-to-end solution for securing Microcontroller Unit (MCU) powered devices. Azure Sphere comprises three parts:
- Azure Sphere Operating System is a secure OS that creates a secured platform for IoT devices.
- Azure Sphere Certified MCUs provide connectivity and a dependable hardware root of trust.
- Azure Sphere Security Service brokers trust for device-to-device and device-to-cloud communication. It detects emerging threats and renews device security.
This is how enterprises can build new devices and connect existing equipment securely using end-to-end security features that are layered across the device stack.
- Azure IoT Edge:IoT Edge is built on top of IoT Hub and enables enterprises to move parts of their workloads to the edge devices to offload/share processing capabilities.
- IoT Hub Device Provisioning Service:The Azure IoT Hub Device Provisioning Service is a helper service for IoT Hub, enabling enterprises to provision large numbers of devices in a secure and scalable manner.
- Azure Digital Twins:Azure Digital Twins helps enterprises model the relationships and interactions between people, spaces, and devices. This ability helps create models of a physical environment for IoT monitoring and analysis. Once the environment has been modeled, enterprises can run predictive algorithms to anticipate the behavior of the entire system.
- Azure Maps:Azure Maps is a collection of geospatial services that use mapping data to provide accurate geographic context to web and mobile applications. Enterprises can then add spatial analytics, mapping services and mobility services to their IoT apps using APIs.
Data and Analytics
Azure Machine Learning: Azure machine learning represents a suite of products to build, train, and deploy machine learning models in Azure. Data and analytics solutions from Azure represent a set of solutions to store and analyze IoT data. These include Azure Stream Analytics, Azure HDInsight, Azure Data Lake, Azure Cosmos DB, and Azure Data Fabric.
Enterprises can also build systems using Azure Functions to enable a serverless application that can run small pieces of code, or “functions,” in the cloud. These functions can then be combined to create more comprehensive applications. Enterprises pay only for the time their code runs in Azure (serverless application).
Visualization and Integration
Visualization and Integration solutions for IoT solutions include Microsoft Flow, Azure Logic Apps, Azure Web App, Notification Hubs, Azure Active Directory, Microsoft Power BI, Azure Monitor, and Power Apps.
Now, let’s contrast Microsoft’s offering to Amazon’s, described below.
Amazon AWS IoT Core
AWS IoT provides the services that support the devices that are usually located in close proximity to the real-world interfaces they monitor and control – and the data that passes between them and AWS IoT. To enable this, AWS IoT provides device software that facilitate integration of IoT devices into AWS IoT-based solutions. A high-level depiction of this set of capabilities appears below.
Figure 7: AWS IoT Ecosystem (Source: Amazon)
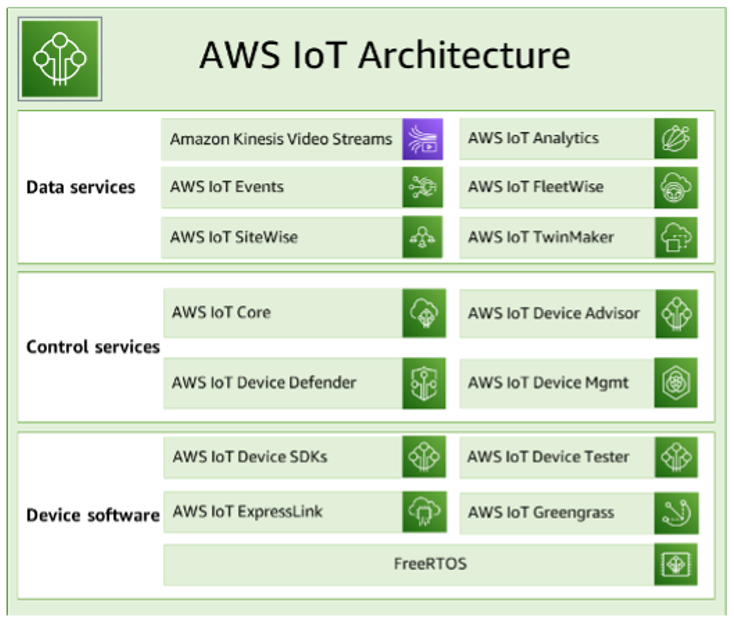
AWS IoT is made up of the services illustrated below.
Figure 8: AWS IoT Architecture Components (Source: Amazon)
Let’s inspect of each of these separately below.
Data Services
The Data Services component of AWS IoT helps organizations analyze the data from the devices within their mission centric IoT solutions and take appropriate action by using the following AWS IoT services:
- Amazon Kinesis Video Streams is a service that enables the streaming of live video from devices to the AWS Cloud, where it is durably stored, encrypted, and indexed, allowing access to this data through APIs. Amazon Kinesis Video Streams can be used to capture large amounts of live video data from millions of sources, including smartphones, security cameras, webcams, cameras embedded in cars, drones, and other sources – enabling playback of video for live and on-demand viewing, and building applications that take advantage of computer vision and video analytics through integration with Amazon Rekognition Video, and libraries for ML frameworks. This service can also send non-video time-serialized data such as audio data, thermal imagery, depth data, RADAR data, and more.
- Amazon Kinesis Video Streams with WebRTC provides a standards-compliant WebRTC implementation as a fully managed capability to securely live stream media or perform two-way audio or video interaction between any camera IoT device and WebRTC-compliant mobile or web players. This capability can help customers build applications for live peer-to-peer media streaming, or real-time audio or video interactivity between camera IoT devices, web browsers, and mobile devices for a variety of use cases.
- AWS IoT Analytics facilitates operationalization of sophisticated analytics on large volumes of unstructured IoT data. This service filters, transforms, and enriches IoT data before storing it in a time-series data store for analysis. Enterprises can analyze data by running one-time or scheduled queries using the built-in SQL query engine or Machine Learning.
- AWS IoT Events detects and responds to events from IoT sensors and applications. Events are patterns of data that identify more complicated circumstances than expected, such as motion detectors using movement signals to activate lights and security cameras. AWS IoT Events continuously monitors data from multiple IoT sensors and applications, and integrates with other services, such as AWS IoT Core, IoT SiteWise, DynamoDB, and others to enable early detection and tailored insights.
- AWS IoT FleetWise is a managed service that can collect and transfer vehicle data to the cloud in near-real time. This service supports vehicles that use different protocols and data formats and can be used to help transform low-level messages into human-readable values and standardize the data format in the cloud for data analyses.
- AWS IoT SiteWise collects, stores, organizes, and monitors data passed from industrial equipment by MQTT messages or APIs at scale by providing software that runs on a gateway in your facilities. The gateway securely connects to enterprise on-premises data servers and automates the process of collecting and organizing the data and sending it to the AWS Cloud.
- AWS IoT TwinMaker builds operational digital twins of physical and digital systems, supporting the creation of digital visualizations using measurements and analysis from a variety of sensors, cameras, and enterprise applications. It is chiefly used to help enterprises keep track of physical factory, building, or industrial plant environments.
Control Services
The following AWS IoT Control Services are used to manage the devices within enterprise-specific IoT solutions:
- AWS IoT Core is a managed cloud service that enables connected devices to securely interact with cloud applications and other devices. AWS IoT Core can support many devices and messages, and it can process and route those messages to AWS IoT endpoints and other devices.
Figure 9: AWS IoT Core Services (Source: Amazon)
The AWS IoT Core connectivity services provide secure communication with the IoT devices and manage the messages that pass between them and AWS IoT.
- Device gateway enables devices to securely and efficiently communicate with AWS IoT. Device communication is secured by secure protocols that use X.509 certificates.
- Message broker provides a secure mechanism for devices and AWS IoT applications to publish and receive messages from each other. Devices can use either the MQTT protocol directly or MQTT over WebSocket to publish and subscribe. Devices and clients can also use the HTTP REST interface to publish data to the message broker. The message broker distributes device data to devices that have subscribed to it and to other AWS IoT Core services, such as the Device Shadow service and the rules engine.
- AWS IoT Core for LoRaWAN makes it possible to set up a private LoRaWAN network by connecting LoRaWAN devices and gateways to AWS without the need to develop and operate a LoRaWAN Network Server (LNS). Messages received from LoRaWAN devices are sent to the rules engine where they can be formatted and sent to other AWS IoT services.
- Rules engine connects data from the message broker to other AWS IoT services for storage and additional processing. For example, an enterprise can insert, update, or query a DynamoDB table or invoke a Lambda function based on an expression that it defined in the Rules engine. The enterprise can use an SQL-based language to select data from message payloads, and then process and send the data to other services, such as Amazon Simple Storage Service (Amazon S3), Amazon DynamoDB, and AWS Lambda. Enterprises can also create rules that republish messages to the message broker and on to other subscribers.
- AWS IoT Core Device Advisor is a cloud-based, fully managed test capability for validating IoT devices during device software development. Device Advisor provides pre-built tests that can be used to validate IoT devices for reliable and secure connectivity with AWS IoT Core, before deploying devices to Production.
- AWS IoT Device Defenderhelps secure an enterprise’s collection (or “fleet”) of IoT devices by continuously auditing the IoT configurations to ensure that they aren’t deviating from security best practices. This service sends an alert when it detects any gaps in the IoT configuration that might create a security risk, such as identity certificates being shared across multiple devices or a device with a revoked identity certificate trying to connect to AWS IoT Core.
- AWS IoT Device Management services helps track, monitor, and manage the plethora of connected devices that make up device fleets and helps ensure that IoT devices work properly and securely after they have been deployed. They also provide secure tunneling to access IoT devices, monitor their health, detect and remotely troubleshoot problems, as well as services to manage device software and firmware updates.
Device Software
AWS IoT provides the following software to support enterprise IoT devices:
- AWS IoT Device SDKs facilitates connection of devices to AWS IoT via open-source libraries, developer guides with samples, and porting guides to build IoT products or solutions on various hardware platforms.
- AWS IoT Device Testerfor FreeRTOS and AWS IoT Greengrass is a test automation tool for microcontrollers.
- AWS IoT ExpressLink powers a range of hardware modules developed and offered by AWS Partners. The connectivity modules include AWS-validated software, which can facilitate securely connecting devices to the cloud and thus integrating with a range of AWS services.
- AWS IoT Greengrassextends AWS IoT to edge devices so they can act locally on the data they generate and use the cloud for management, analytics, and durable storage. Using this service, connected devices can run AWS Lambda functions, Docker containers, or both, execute predictions based on machine learning models, keep device data in sync, and communicate with other devices securely – whether or not the devices are connected to the Internet.
- FreeRTOS FreeRTOS is an open source, real-time operating system for microcontrollers that lets enterprises include small, low-power edge devices in their custom IoT solutions. The service includes a kernel and a growing set of software libraries that support many applications.
With this review of both Microsoft and Amazon cloud-based IoT infrastructure offerings, we offer our conclusions and recommendations in the next section.
Conclusions and Recommendations
There are so many existing and emerging use cases for integrating things with the broad expanse of IT capabilities. This starts with the automated collection of diverse data that fuels AI. There are also many use cases surrounding Industrial Control Systems, Intelligent Shop Floor Control / Management Systems, energy management and control, healthcare / hospital floor, remote equipment management, transportation management, inventory management and so on. There is no doubt that there are many devices that can transmit and receive data in ways that dramatically automate processes, provide efficiency, deliver services and offer customization that directly impact business’ bottom lines.
With the onset of cloud-based IoT hubs and control centers, there comes a clear ability to design and deploy secure IoT services that tie directly with the business – without developing and securing a networking data center on your own. With the rapid rise of 3rd party IoT integration capabilities from smart devices that communicate using standard protocols like MQTT, as well as the ability to integrate devices – whether smart, dumb, active or passive, into the IoT ecosystem with APIs that development organizations can use ‘right out of the box’, the landscape for IoT becomes in focus.
If you look carefully at your own organization and the vertical industry(ies) it addresses, there is very likely a fount of existing use cases, 3rd party IoT edge solutions and good practices for designing, deploying, securing and monitoring your IoT environment to bring your strategy to life.
But be aware that with IoT deployments it becomes all about the data. From the enterprise perspective, there is data streaming from sensors, actuators, industrial control systems, public utilities and so on. From this perspective, there are significant risks of data exposure to nefarious actors, which introduces new concerns in terms of data privacy and intellectual property protection. For these reasons, it is imperative to think of IAM as not just your grandfather’s “people management and access solution”. Just like people, things need to be registered, provisioned, authenticated, authorized, change-managed, audited and so forth. The capabilities in these important areas enabled by expansive cloud ecosystems such as Microsoft IoT Hub and AWS IoT Core are capable of identifying and enabling the universe of uniquely identifiable things that communicate over networks.
What is really interesting is the growing number of enterprise IoT use cases and scenarios that are appearing. Telemetry – defined as “the process of recording and transmitting the readings of an instrument” is one of the most basic and useful capabilities extended by IoT integration with a logically centralized IT infrastructure. With the establishment of cloud-based IoT connectivity hubs from AWS, Microsoft and others, the path of resistance shrinks considerably. By embedding myriad appropriate security capabilities within the IoT ecosystem, from SDKs that contain X.509 key management to extensive monitoring and configuration management, the hundreds and even thousands of telemetric and process control-enabled devices that comprise many enterprise operational infrastructures are able to be active and secure participants in the mission critical role of real time data gathering and processing.
Action Plan
Simply put, those organizations that are utmost prepared to protect their large-scale deployed applications realized through the interconnection of diverse digital assets and able to quickly recover from the entire spectrum of security threats will ultimately deliver the potential benefits afforded by the IoT. Those organizations building AI capabilities will also largely benefit from a strong and secure IoT ecosystem.
There is an enormous amount of information and awareness regarding IoT integration, configuration and security being made available today. TechVision recommends a structured approach to such a critical infrastructure element like secure IoT integration and deployment and has developed a Reference Architecture that may be useful in evaluating the set of capabilities necessary for your future state IoT foundation. TechVision can help with this process.
About TechVision
World-class research requires world-class consulting analysts, and our team is just that. Gaining value from research also means having access to research. All TechVision Research licenses are enterprise licenses; this means everyone that needs access to content can have access to content. We know major technology initiatives involve many different skillsets across an organization and limiting content to a few can compromise the effectiveness of the team and the success of the initiative. Our research leverages our team’s in-depth knowledge as well as their real-world consulting experience. We combine great analyst skills with real world client experiences to provide a deep and balanced perspective.
TechVision Consulting builds off our research with specific projects to help organizations better understand, architect, select, build, and deploy infrastructure technologies. Our well-rounded experience and strong analytical skills help us separate the “hype” from the reality. This provides organizations with a deeper understanding of the full scope of vendor capabilities, product life cycles, and a basis for making more informed decisions. We also support vendors in areas such as product and strategy reviews and assessments, requirement analysis, target market assessment, technology trend analysis, go-to-market plan assessment, and gap analysis.
TechVision Updates will provide regular updates on the latest developments with respect to the issues addressed in this report.
About the Authors
 Doug Simmons brings more than 25 years of experience in IT security, risk management and identity and access management (IAM). He focuses on IT security, risk management and IAM. Doug holds a double major in Computer Science and Business Administration.
Doug Simmons brings more than 25 years of experience in IT security, risk management and identity and access management (IAM). He focuses on IT security, risk management and IAM. Doug holds a double major in Computer Science and Business Administration.
While leading consulting at Burton Group for 10 years and security, and identity management consulting at Gartner for 5 years, Doug has performed hundreds of engagements for large enterprise clients in multiple vertical industries including financial services, health care, higher education, federal and state government, manufacturing, aerospace, energy, utilities and critical infrastructure.
 Gary Rowe is a seasoned technology analyst, consultant, advisor, executive and entrepreneur. Mr. Rowe helped architect, build and sell two companies and has been on the forefront the standardization and business application of core infrastructure technologies over the past 35 years. Core areas of focus include identity and access management, blockchain, Internet of Things, cloud computing, security/risk management, privacy, innovation, AI, new IT/business models and organizational strategies.
Gary Rowe is a seasoned technology analyst, consultant, advisor, executive and entrepreneur. Mr. Rowe helped architect, build and sell two companies and has been on the forefront the standardization and business application of core infrastructure technologies over the past 35 years. Core areas of focus include identity and access management, blockchain, Internet of Things, cloud computing, security/risk management, privacy, innovation, AI, new IT/business models and organizational strategies.
He was President of Burton Group from 1999 to 2010, the leading technology infrastructure research and consulting firm. Mr. Rowe grew Burton to over $30+ million in revenue on a self-funded basis, sold Burton to Gartner in 2010 and supported the acquisition as Burton President at Gartner.