Digital Identity Wallets
Initial Publication Date: 14 February 2024
Abstract
The tech world has been striving to find an approach to the various aspects of the identity problem for several decades. There have been any number of false dawns and many lessons learnt along the way and inevitably there is a sense that we must be getting closer to a solution set that would work across many if not all vertical sectors and geographic domains.
Most recently, the potential of distributed ledgers, self-sovereign identities and decentralized identities has generated considerable excitement and expectation. Digital identity wallets are the latest approach to get widespread attention, notably in Europe where the European Union has invested large sums to make digital identity wallets available to all its citizens for use in both public and private applications by 2026.
However, digital wallets are not new and have been available from the likes of Apple, Google, and Samsung as well as numerous payments companies for over ten years, and it is an open question as to how the established players will interact with the newcomers emerging in the European market. At heart is the challenge of interoperability between providers and an agreed set of standards to support giving consumers / citizens a valid choice.
As one notable panelist at Chrysalis IV observed, the emergence of decentralized identities is going to be highly disruptive, and we can expect the identity tools we are familiar with will have to be re-imagined. In this report, we focus on digital identity wallets as one aspect of this trend.
This report covers:
- The digital identity wallet value proposition and the opportunities and challenges for the enterprise
- TechVision Research’s analysis of digital identity wallet providers
- Seven steps an enterprise should take to best leverage digital identity wallets.
Authors:
| David Goodman, D. Phil
Principal Consulting Analyst |
Executive Summary
After decades of developing solutions to capture different aspects of the identity puzzle, we are currently at the dawn of a new world that leverages much of the pioneering work that was carried out by visionaries as well as hardware and software developers during the preceding years.
Distributed ledgers, self-sovereign identities and decentralized identities have opened new horizons that in turn have led to the current buzz around the viability of digital identity wallets based on mobile devices to provide the kind of pervasive identity solution that has been much sought after.
The European Commission (EC) is investing USD 100 million from the Digital Europe Program into piloting and enhancing a European digital identity (EUDI) wallet. The EUDI Wallet will potentially revolutionize how citizens and businesses digitally identify themselves when accessing public and private services throughout Europe, using their smartphones in a secure and convenient manner. Citizens will be able to control their personal data stored within a wallet which will also be equipped with mechanisms to minimise the data shared for accessing services.
This investment is supporting four pan-European pilot projects that will develop and test the usage of the EUDI Wallet for individuals and businesses around a diverse range of everyday use cases. These use cases cover both public and private services with national and cross-border interactions.
Everyday scenarios include:
- providing identification to online and offline public and private services.
- displaying your mobile driving license.
- authorizing payments.
- signing documents electronically.
- presenting medical prescriptions.
For instance, the EUDI Wallet will make it easier for EU citizens to travel and move to a new country. It will include digital travel credentials (DTCs) and will simplify the processes of opening a bank account, registering for a SIM card, proving educational and professional qualifications, and claiming social benefits through the European Health Insurance Card (EHIC).
The large-scale pilot projects the EC is investing in will help Member States and other stakeholders prepare for the entry into force of the European Digital Identity Regulation, currently in the final stages of preparation. The target is for everybody living in the EU to have access to a secure and user-friendly eID by 2030, requiring Member States to provide their citizens with access to a EUDI Wallet on a mobile phone or another digital device.
The legislation will ensure that such digital wallets already underway in several Member States, such as Poland and Finland, are based on harmonized standards across the EU and can be used by citizens seamlessly across borders. Citizens will always have full control of the data they share, and the use of the wallet will be completely voluntary.
But the EUDI Wallet is not the only wallet available: Apple, Google, Samsung, and others have for over ten years provided their users with wallets on their smartphones and it remains to be seen how the global market opens to the new challenges and opportunities as well as the availability of the appropriate standards.
Is this another false dawn, or are we really on the threshold of solving the identity conundrum once and for all?
Introduction – How We Got to Where We Are
The quest for a universal solution to the provision of digital identities for individuals and businesses alike has been a growing burning business problem since the 1990’s and the emergence of the Internet as a platform for online transactions and interactions.
The heady early days of X.500 and LDAP were driven by the requirements associated with support for the spread of unique email addresses which went beyond the scope of the DNS. This morphed into the growth of enterprise directories and enterprise-wide identity-based applications that provided little opportunity for the individual to manage their personal information within enterprises and more significantly between organisations across the Internet. With the explosion of digital commerce, the disconnect between the two perspectives became ever more apparent:
- from the early-noughties onwards this led to numerous well-intended ‘bottom-up” initiatives to address enabling individuals to be responsible for the storage, management, and use of their personal data. In retrospect, without clear unequivocal governmental and/or big tech support and direction, most of these plans were doomed to flounder (as they inevitably did).
- during the mid-tens, a market for CIAM (customer identity and access management) products and solutions emerged, recognizing that enterprises were not managing their customer data and requirements well enough. As employees became no longer office-bound, the enterprise dividing lines between employees working remotely and customers gradually started to dissolve and became more a matter of granular access controls and permissions.
Over the last decade several factors have led us to where we are today:
- participation in online trading and social media platforms became so prevalent and an everyday aspect of most people’s lives that the cumbersome and outdated approaches to identification, verification and authentication led to intolerable frustrations and inefficiencies both by individuals as well as businesses.
- the adoption of ‘smart devices’ was universal, cross-generational, and cross-demographic and hence a natural candidate as a vehicle for future digital identity solutions.
- the groundwork for recent developments in digital identities centred around the work carried out in the noughties by Kim Cameron and others who helped define the ‘Laws of Identity’ especially from a user perspective, which in turn led to developments in the realms of self-sovereign identity (SSI) solutions and W3C standards for verifiable credentials.
- the growing public awareness of privacy concerns arising from sharing personal data over the Internet, based on the threat of identity theft, the unsolicited trading of personal data and well-publicised accounts of corporate data breaches, that has led to the re-casting of data protection regulations starting with Europe’s GDPR.
What is emerging in the market is a new environment where the focus has shifted from the provision and use of rigid digital identities to the provision and reliance on specific attributes related to those identities. There is an increased demand for electronic identity solutions, particularly in the European Union (EU) that can deliver these capabilities providing efficiency gains and a high level of trust, both in the private and the public sectors, relying on the need to identify and authenticate users with a high level of assurance.
This document examines how the trend towards digital identity wallets is emerging in Europe and elsewhere, and the dominance of the mobile wallets provided by Apple, Google and others with the iOS and Android operating systems. It also assesses the opportunities and barriers to widespread adoption and the lessons to be learned for corporates.
Digital Identity Wallets
The concepts and issues associated with digital identity are scarcely new; and neither are wallet technologies which have been around for ten years or more but are evidently gaining momentum with numerous benefits for individuals and businesses alike. The EU is demonstrating its commitment to a broad set of initiatives, ranging from regulations and policies to an investment of well over USD 100 million.
The adoption of SSI, verifiable credentials and privacy and the requirement for a truly decentralized, transparent, and cryptographically auditable environment for data transactions has also gained widespread acceptance. The attraction is that the emerging ecosystems will empower users to gain real control over their data particularly when conjoined with a consent management platform. There is no doubt that the types of envisaged collaborative ecosystems will be both ground-breaking and disruptive to users, enterprises, and service providers from the tech giants to the plethora of new start-ups.
Mobile wallets originated over ten years ago to support online payments through:
- Closed wallets, such as Amazon Pay, Walmart Pay et al. are ones which can only be used to pay for items with the issuing merchant. The funds inside the wallet are exclusively for transactions involving the owning company or its affiliates.
- Open wallets, such as Apple Pay, Google Pay, Revolut et al. can be used to pay for purchases at any card-accepting merchant location.
Each approach has its own set of benefits based on differing market priorities.
Initiatives
In this section, we look at the emergence of digital wallets in different jurisdictions and different applications. To date this space has been dominated by Apple, Google, and others but the massive initiative launched by the EU as well as the open-source Open Wallet Foundation program are challenging the status quo.
Europe
According to Margarethe Vestager, Executive Vice-President European Commission, on 6 May 2021:
Data is not oil – it is a renewable resource that can be pooled, shared, reused … we want to enable businesses to make the most of data – while securing that we can trust that we are protected from misuse.
eIDAS Regulation
The eIDAS Regulation on electronic identification and trust services [1] [2] was seen as a key enabler for secure cross-border electronic transactions in the internal market and was in its time a milestone towards creating a predictable regulatory environment to help businesses, citizens and public authorities carry out secure and seamless electronic interactions.
By providing certainty on the legal validity of identity and trust services, it was intended to:
- ensure that people and businesses could use their own national electronic identification schemes (eIDs) [2] to access public services available online in other EU Member States.
- create a European internal market for trust services by ensuring that they would work across borders and have the same legal status as their traditional paper-based equivalents.
Since the entering into force of the eID part of the regulation in September 2018, only 14 Member States have notified at least one eID scheme. As a result, only 59% of EU residents have access to trusted and secure eID schemes across borders. Only seven schemes are entirely mobile, responding to current user expectations. As not all technical nodes to ensure the connection to the eIDAS interoperability framework are fully operational, cross-border access is limited; very few online public services accessible domestically can be reached cross-border via the eIDAS network.
The evaluation of eIDAS in 2020 [3] revealed that the current regulation fell short of addressing these new market demands, mostly due to its inherent limitations to the public sector, the limited possibilities, and the complexity for online private providers to connect to the system, its insufficient availability of notified eID solutions in all Member States and its lack of flexibility to support a variety of use cases. Furthermore, identity solutions falling outside the scope of eIDAS, such as those offered by social media providers and financial institutions, raise privacy and data protection concerns. They cannot effectively respond to new market demands and lack the cross-border outreach to address specific sectoral needs where identification is sensitive and requires a high degree of certainty.
Hence since it came into force, whilst it had limited success in providing access to public services in several EU Member States, it was recognised that eIDAS had not gone far enough and was no longer entirely fit for purpose.
A Framework for a European Digital Identity
In June 2021, the European Commission (EC) unveiled a proposal to update the existing eIDAS Regulation, formally referred to as the European Digital Identity framework (EDIF) [4] [5] but referred to throughout this report as eIDAS 2.0, as it is commonly known. This proposed update stood as a response to the ever-evolving technological landscape and the dynamic needs of the EU digital market and sought to improve the security and reliability of electronic identification and trust services.
To accomplish this, the main shift in the proposal was the creation of a unified European digital identity with a digital identity wallet as a key component.
eIDAS 2.0 expands the scope of the original regulation to include more types of electronic trust services, including electronic registered delivery services, electronic certificates for authentication, and electronic seals for digital documents. This means it regulates new services like attestation of attributes and electronic ledgers, among others.
Moreover, eIDAS 2.0 places a strong emphasis on interoperability and security, which are areas to be improved within the original eIDAS regulation. It achieves this by offering technical standards and specifications to reduce fragmentation and by imposing new security requirements for cryptographic algorithms and key management while increasing the focus on data protection.
By offering a framework for European digital identity based on the revision of eIDAS, it is hoped that at least 80% of citizens should be able to use a digital identity solution to access key public services by 2030. Furthermore, the security and control offered by eIDAS 2.0 should give citizens and residents full confidence that it will offer everyone the means to control who has access to their digital twin and to which data exactly. This will also require a high level of security with respect to all aspects of digital identity provisioning, including the issuing of a EUDI Wallet, and the infrastructure for the collection, storage, and disclosure of digital identity data.
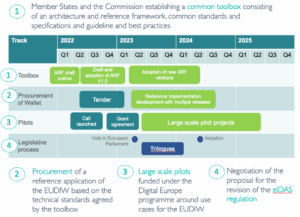
Figure 1: The timeline for Europe’s digital identity wallet initiative
Furthermore, the current eIDAS framework does not cover the provision of electronic attributes, such as medical certificates or professional qualifications, making it difficult to ensure pan-European legal recognition of such credentials in electronic form. In addition, the eIDAS Regulation does not allow users to limit the sharing of identity data to what is strictly necessary for the provision of a service.
While the evaluation of the eIDAS Regulation shows that the framework for the provision of trust services was rather successful, providing a high level of trust and ensuring the uptake and use of most trust services, more is needed to be done to reach full harmonisation and acceptance. For qualified certificates of website authentication (QWACs), citizens must be able to rely on them and benefit from the secure and trustworthy information about who is behind a web site, thus reducing fraud.
In addition, to respond to the dynamics of the markets and to technological developments, the proposal expands the current eIDAS list of trust services with three new qualified trust services, namely the provision of electronic archiving services, electronic ledgers and the management of remote electronic signature and seal creation devices.
This proposal also offers a harmonized approach to security, for citizens relying on a European digital identity representing them online, and for online service providers who will be able to fully rely on and accept digital identity solutions independently of where they have been issued. This proposal implies a shift for issuers of European digital identity solutions, providing a common technical architecture and reference framework and common standards to be developed in collaboration with the Member States. A harmonized approach is necessary to avoid that the development of new digital identity solutions in Member States create further fragmentation triggered through using divergent national solutions. A harmonized approach also strengthens the Digital Single Market as it allows citizens, other residents, and businesses to identify online in a secure, convenient, and uniform way across the EU to access both public and private services. Users would be able to rely on an improved ecosystem for electronic identity and trust services recognized and accepted everywhere in the EU.
To avoid fragmentation and barriers due to diverging standards, the EC has adopted a recommendation which sets out a process to support a common approach allowing Member States and other relevant stakeholders from the public and private sectors to work towards the development of a Common Toolbox to avoid divergent approaches and avoid endangering the future implementation of the EUDI framework.
In this respect, the proposal implements the political mandate to provide an EU-wide framework for public electronic identities which ensures that any citizen or resident can have access to a secure European e-identity, which can be used anywhere in the EU to identify and authenticate for access to services in the public and private sectors, allowing citizens to control what data is communicated and how it is used.
The key provisions of eIDAS 2.0 are explained in Table 1 below.
| Article | Topic | Description |
| 6a | EUDI wallet issuance | Member States are required to issue a EUDI Wallet under a notified eID scheme to common technical standards following compulsory compliance assessment and voluntary certification within the European cybersecurity certification framework, as established by the Cybersecurity Act.
It includes provisions to ensure that natural and legal persons shall have the possibility to securely request and obtain, store, combine and use person identification data and electronic attestations of attributes to authenticate online and offline and to allow access to goods and online public and private services under the user’s control. |
| 6b | Fraud prevention | Specific provisions are made on the requirements applicable to relying parties for the prevention of fraud and to ensure the authentication of personal identification data and electronic attestations of attributes originating from the EUDI Wallet. |
| 7 | Mandatory identification scheme | To make more eID means available for cross border use and improve the efficiency of the process of mutual recognition of notified eID schemes, the notification of at least one eID scheme by Member States is made mandatory. |
| 11a | Unique and persistent identification | Provisions to facilitate unique identification are added to ensure the unique and persistent identification of natural persons in cases where identification is legally required, such as in the areas of health or finance, to discharge anti-money laundering obligations, or for judicial use.
Member States are required to include a unique and persistent identifier in the minimum set of person identification data. The possibility for Member States to rely on certification to ensure conformity with the Regulation and so replacing the process of peer review, improves the efficiency of mutual recognition. |
| Use of strong authentication | New provisions on the cross-border reliance on the EUDI Wallet to ensure that users can rely on their use to access online services provided by public sector bodies and by private service providers requiring the use of strong user authentication. | |
| 14 | Mutual recognition agreements | International aspects allow the Commission the possibility of adopting implementing decisions attesting the equivalence of the requirements applied to trust services established in third countries and of the services they provide, in addition to the use of mutual recognition agreements. |
| 17, 18, 20, 21 & 24 | Qualified trust service providers (QTSPs) | Regarding the general provision applicable to trust services, Articles 17, 18, 20, 21 and 24 are aligned with the rules applicable to network and information security in the EU. For the methods to be used by QTSPs to verify the identity of natural or legal persons to whom qualified certificates are issued, the provisions on the use of remote means of identification have been harmonised and clarified to ensure that the same rules are applied across the EU |
| 29a | Remote electronic signature creation devices | Requirements for a qualified service for the management of remote electronic signature creation devices are defined. The new qualified trust service would be directly linked and build on measures calling for the harmonisation of supervision practices by Member States. |
| 45 | QWACs | To ensure that users can identify who is behind a website, providers of web browsers are required to facilitate the use of qualified certificates for website authentication |
| 45d, 45e, 45f | Electronic attestations of attributes | Provisions are made on the legal effects of electronic attestations of attributes, their use in defined sectors and the requirements for qualified attestations of attributes. including a provision on the verification of attributes against authentic sources and an assurance that users of the EUDI Wallet can benefit from the availability of electronic attestations of attributes as well as additional rules for the provision of electronic attestation of attribute services, including on the protection of personal data |
| 45g | Qualified electronic archiving services | The provision of qualified electronic archiving services at the EU level complements that on qualified preservation services for qualified electronic signatures and qualified electronic seals. |
| Maintenance of (qualified) electronic ledgers | A framework for trust services regarding the creation and maintenance of electronic ledgers and qualified electronic ledgers which combine time stamping of data and their sequencing with certainty about the data originator similar to e-signing, with the additional benefit of enabling a more decentralized governance that is suitable for multi-party cooperation. To prevent fragmentation, it is necessary to define a single pan-European framework that will enable the cross-border recognition of trust services supporting the operation of electronic ledgers. This pan-European standard for node operators will apply notwithstanding other EU secondary legislation. | |
| 48b | Monitoring effectiveness | Statistics on the use of the EUDI Wallet are to be collected for monitoring the effectiveness of the amended Regulation |
Table 1: Detailed explanation to specific provisions of eIDAS 2.0
Wallet Prototype
The EC is committed to providing a prototype EUDI Wallet as set out in eIDAS 2.0 to enable European citizens and business to share identity data in a secure and convenient way in order:
- to trial and inform the specifications developed by Member States as the Common Toolbox to implement the EUDI Wallet.
- to be tested in several large-scale pilots (LSPs) that cover different sectors, such as healthcare, financial services, education and transport.
- to be made available for re-use by Member States, LSP projects and other contributors as open source.
Architectural Reference Framework (ARF)
The purpose of the EUDI Wallet Architecture and Reference Framework (ARF) [6] is to provide a set of the specifications needed to develop an interoperable EUDI Wallet solution based on common standards and practices.
On 3 June 2021, the EC adopted a Recommendation calling on Member States to work towards the development of a Toolbox including a technical ARF, a set of common standards and technical specifications on a set of common guidelines and best practices. The document aims to describe a comprehensive ARF covering all the specifications needed to implement a EUDI Wallet solution. It is to be used by the EC in developing a reference implementation of a EUDI Wallet and by the consortia piloting its use in the context of the LSPs. The code for the EUDI Wallet reference implementation, provided in a mobile form factor, will be available as open source for re-use by implementors across Europe. The LSPs are expected to provide feedback on the ARF as they develop and interact with relying parties, qualified or non-qualified electronic attestations of attribute ((Q)EAA) providers, person identification data (PID) providers in meaningful transactions under the proposed use cases.
Large Scale Pilots (LSPs)
Prior to its roll-out in Member States, the EC is investing over USD 100 million from its Digital Europe program in four large scale projects, all of which launched on 1 April 2023, to pilot the use of the EUDI Wallet. The objective of these projects is to test digital identity wallets in real-life scenarios spanning different sectors such as travel, health, banking, education and more.
The LSPs are testing technical specifications for the Common Toolbox for the EUDI Wallet and the software prototype.
Over 600 private companies and public authorities across most Member States as well as Norway, Iceland, Switzerland, and Ukraine are participating.
POTENTIAL
 The POTENTIAL[1] ‘European Consortium for Digital Identity’ aims to promote the development and deployment of six use cases. It specifically focuses on opportunities for the new infrastructure among public and private stakeholders and interoperability and scalability of solutions. The goal is to enable Member States to build the necessary expertise and infrastructure, considering results of other EU funded projects and leveraging synergies.
The POTENTIAL[1] ‘European Consortium for Digital Identity’ aims to promote the development and deployment of six use cases. It specifically focuses on opportunities for the new infrastructure among public and private stakeholders and interoperability and scalability of solutions. The goal is to enable Member States to build the necessary expertise and infrastructure, considering results of other EU funded projects and leveraging synergies.
NOBID
 This consortium[2], originating from a set of Nordic and Baltic countries, as well as Italy and Germany, which involves several banks and is piloting the use of the EUDI Wallet for the authorisation of payments for products and services by the wallet user/holder. It aims to address the issuance of wallets, the provision of payment means by financial institutions, and the acceptance of and payment in a retail context.
This consortium[2], originating from a set of Nordic and Baltic countries, as well as Italy and Germany, which involves several banks and is piloting the use of the EUDI Wallet for the authorisation of payments for products and services by the wallet user/holder. It aims to address the issuance of wallets, the provision of payment means by financial institutions, and the acceptance of and payment in a retail context.
DC4EU
 The Digital Credential for Europe (DC4EU)[3] Consortium is to pilot the use of the EUDI Wallet in both the educational sector (educational credentials and professional qualifications) and the social security domain (PDA1 and EHIC). The pilot is aligning with ESSPASS [7] and the European Learning Model. This LSP is unique its use of the European Blockchain Services Infrastructure (EBSI) in the context of the EUDI Wallet.
The Digital Credential for Europe (DC4EU)[3] Consortium is to pilot the use of the EUDI Wallet in both the educational sector (educational credentials and professional qualifications) and the social security domain (PDA1 and EHIC). The pilot is aligning with ESSPASS [7] and the European Learning Model. This LSP is unique its use of the European Blockchain Services Infrastructure (EBSI) in the context of the EUDI Wallet.
EWC
 The EU Digital Consortium (EWC)[4] uses the EUDI Wallet to store and present digital travel credentials to enable the support of free cross-border movement in Europe. It is also focused on the development of business digital identity wallets that allow a citizen to effectively identify themselves anywhere in Europe as legitimate representatives of an organization. Lastly it is employing the EUDI Wallet to store payment credentials and authorize account-to-account based transactions, as well as card-based and possibly token based transactions.
The EU Digital Consortium (EWC)[4] uses the EUDI Wallet to store and present digital travel credentials to enable the support of free cross-border movement in Europe. It is also focused on the development of business digital identity wallets that allow a citizen to effectively identify themselves anywhere in Europe as legitimate representatives of an organization. Lastly it is employing the EUDI Wallet to store payment credentials and authorize account-to-account based transactions, as well as card-based and possibly token based transactions.
Use Cases
Between them the four LSPs are in the process of demonstrating eleven different use cases as detailed in Table 2 below:
| # | Use Case | Objective | Scenario |
| 1 | Accessing government services | Secure access to digital public services, such as applying for a passport or driver’s licence, filing taxes, or accessing social security information.
(Identify to and access a digital public service) |
Bob is posted by his employer to another Member State. He needs to register as a resident in the new country and he can use his EUDI Wallet for this purpose. Bob can also use his wallet to prove his identity for various online public services such as to register his driver’s licence, to vote in European or local elections, or to provide his fishing and hunting licence information when applying for a permit. |
| 2 | Opening a bank account | Verification of a user’s identity when opening an online bank account, eliminating the need for the user to repeatedly provide their personal information. | Alice uses a EUDI Wallet to verify her identity when opening an online bank account, eliminating the need for her to repeatedly provide their personal information. |
| 3 | SIM Registration | Proof of identity for the purpose of pre- and post-paid SIM card contracts (registration and activation), reducing fraud and costs for mobile network operators. | Bob is visiting another Member State. He can use his EUDI Wallet to apply and buy a SIM card for his mobile phone from a local provider. |
| 4 | Mobile Driving License | The storage and presentation of the mobile driving license in both online and physical interactions such as a driver providing their license on the side of the road. | Alice has installed a personal digital wallet on her mobile phone. It has been provided by her home country, ensuring that the wallet has been issued to her personally. Alices’ digital wallet allows her to download, store and use her mobile driving license, replacing the document in her physical wallet. |
| 5 | Signing Contracts | Creating secure digital signatures for signing contracts online, eliminating the need for paper documents and physical signatures. (Remote qualified electronic signature) | Alice uses her wallet when signing contracts online, as it provides a secure digital signature, eliminating the need for paper documents and physical signatures. |
| 6 | Claiming Prescriptions
|
Providing details of prescriptions to pharmacies cross-border and initiating the dispensation of medical products.
(ePrescription) |
Bob, a diabetic, needs to stock up on insulin while staying in a foreign country. Presenting his digital prescription which he received from his physician at home, he visits a local pharmacy to have the medicine dispensed. |
| 7 | Initiating payments | Verification of a user’s identity when initiating a payment online.
(Account-to-account, card-based, possibly token-based)
|
Alice, for business purposes, holds banking accounts at financial institutions in several Member States. Previously, to authorise transactions when banking electronically, she had to use different means (e.g., a fingerprint, a one-time passcode, or affirmation to transaction approval queries send to her personal device). Now all banks use her digital wallet for this purpose. |
| 8 | Education certification | Proof of possession for educational credentials, such as diplomas, degrees, and certificates making it easier to apply for jobs or further education.
(Educational credentials and professional qualifications) |
When applying for a job or further education online, Bob makes use of his EUDI Wallet to securely provide his education credentials (such as diplomas, degrees or certificates). |
| 9 | Accessing social security benefits
|
A EUDI Wallet can be used to securely access a user’s social security information and benefits, such as retirement or disability benefits. It can also be used to facilitate freedom of movement by storing documents such as the European Health Insurance Card (EHIC).
(Portable Document A1 (PDA1)) |
Bob has been employed in another Member State. He uses the EUDI Wallet to access to his social security information and benefits, such as retirement and disability benefits. When his current employer posts him again across border, Bob uses the wallet to store documents such as the EHIC.
|
| 10 | Travelling
|
Presenting information from travel documents (e.g. the user’s passport, visa, and other), allowing for quick and easy access when going through airport security and customs. (Digital travel credentials) | When preparing for her business trip, Alice can store her passport, visa, and other travel documents on her mobile digital wallet, allowing for quick and easy access when going through airport security and customs. |
| 11 | Organisational digital identities (ODIs)
|
Proving you are a legitimate representative of an organisation.
|
Bob and Alice together own a small hotel that has been awarded an eco-label. Storing its digital representation in their company digital identity wallet, they can prove to customers that they meet strict environmental standards. |
Table 2: Use cases demonstrated by the European large scale pilot projects
Each pilot will each make use of components of the reference implementation developed by the EC and contribute to further enhance its security, user-friendliness, and interoperability.
The four pilot projects and the corresponding use cases enumerated in Table 2 are implemented by the respective consortium bringing together public and private actors from different Member States as shown in Table 3 below.
| Country | POTENTIAL | NOBID | DC4EU | EWC |
| Austria (AT) | 1,2,3,4,5,6 | 11 | ||
| Belgium (BE) | 1,4,5 | |||
| Bulgaria (BL) | ||||
| Switzerland (CH) | 7 | |||
| Cyprus (CY) | 1,4,5,6 | |||
| Czech Republic (CZ) | 3,6 | 9 | 8 | |
| Germany (DE) | 1,2,3,4,5 | 10 | 7,8,9 | |
| Denmark (DK) | 9 | 10, 11 | ||
| Estonia (EE) | 4 | |||
| Ireland (EI) | 11 | |||
| Greece (EL) | 1,2,3,4,5,6 | 10 | 7,8 | |
| Spain (ES) | 4,6 | 10 | 7 | |
| Finland (FI) | 1,4 | 7,8 | ||
| France (FR) | 1,2,3,4,5,6 | 8,9 | ||
| Croatia (HR) | ||||
| Hungary (HU) | 6 | 7 | ||
| Iceland (IS) | 9 | |||
| Italy (IT) | 1,4,6 | 9 | 8 | |
| Lithuania (LT) | 4 | 10 | ||
| Latvia (LV) | 9 | |||
| Luxembourg (LU) | 1,2,3,4,5 | 10 | 7 | |
| Malta (MT) | 10 | |||
| Netherlands (NL) | 1,3,4 | 9 | 11 | 8 |
| Norway (NO) | 9 | 10 | 8 | |
| Poland (PL) | 1,3,4,6 | 7 | ||
| Portugal (PT) | 1,2,4,5,6 | 10,11 | ||
| Romania (RO) | 10 | 9 | ||
| Sweden (SE) | 10 | 8,9 | ||
| Slovenia (SI) | 1,2,5 | 10 | ||
| Slovakia (SK) | 1,4,5 | |||
| Ukraine (UA) | 1,2,3,4,5,6 | 9 |
Table 3: Tested use cases by the European large scale pilot projects and the country of origin of participating entities
Challenges and Open Issues
Credentials vs Identities
Digital credentials may contain any information for any purpose but are not the same as digital identities although someone wishing you prove something about yourself should be able to verify the source, integrity and validity of the data contained in the credential.
Unique identifiers
The concept of a unique and persistent identifier was changed to a more privacy-friendly record-matching, which allows verification of a person’s identity based on several personal details, by which Member States must ensure the unequivocal identity of a person in another Member State.
Trusted Lists
Member States have the obligation to establish, maintain and publish trusted lists of qualified trust service providers (QTSPs) and the services provided by them.
Person Identification Data (PID)
Member States shall, for the purposes of this Regulation, include in the minimum set of person identification data …., a unique and persistent identifier in conformity with Union law, to identify the user upon their request in those cases where identification of the user is required by law.
… a minimum set of person identification data necessary to uniquely and persistently represent a natural or legal person.
The PID is an official government (digital) document, with a mandatory data set and several optional elements, with processes in place that follow a high level of assurance that vary from one country to another. However, there is no reason why a citizen could use a digital identity wallet without a PID – it’s just that it won’t be government authenticated.
Organizational Digital Identity (ODI)
An organizational digital identity (ODI) uses digital credentials to certify company affiliation and authorization to act for people and machines. An ODI wallet is wallet software for legal entities and represents a stand-alone legal body.
On-chain and off-chain
Decentralized identities can be based on either, for example, blockchain (i.e., on-chain) or SSI (off-chain), both of which have multiple benefits. Proponents of each are trying to solve specific challenges and address some requirements for different use cases, building their concepts and technological ecosystems on interoperability and standardized approaches, although with the ambition to converge the different approaches. Having to manage multiple on-chain and off-chain digital identities with different digital wallets is an unnecessary burden for users and requires an orchestrated resolution [8].
Governance
Member States are required to designate one or more competent national authorities to enforce the EDIF and to appoint single points of contact to improve cross-border coordination.
Levels of Assurance
The various existing digital identity schemes in Europe reach different levels of assurance: low, substantial, and high. However, the aim is for all EUDI Wallets to reach “high.” This could lead to fragmentation unless mutual recognition is achieved between Member States as well as between sovereign (state) and private-sector applications and verification of specific credentials.
Qualified Website Authentication Certificate
A sensitive issue in the negotiations related to qualified website authentication certificates (QWACs), recognised systems to authenticate the identity of the person or organisation behind a website to avoid possible scams.
Web browser providers like Firefox’s Mozilla opposed a mandatory imposition of QWACs, which they saw as potentially introducing elements of state control over the internet. MEPs managed to introduce the possibility for web browsers to take preventive actions over possible breaches of user privacy.
It was observed that several subtle changes were discretely inserted into eIDAS 2.0 which it was claimed opened the door to facilitating mass surveillance [9]. The proposal granted Member States the authority to insert their keys into browsers, which in turn facilitated the interception of encrypted traffic. In addition, security checks to these keys would be restricted that would most likely result in innovative solutions offering a stronger level of protection being blocked. It was feared that the introduction of unlinkability would only remain optional, whereby citizens’ privacy protections will be dictated by the Member State with the weakest safeguards. As a result, over 350 top level scientists and multiple non-governmental organizations signed an open letter that underscored the risks and presented concrete suggestions for mitigating them [10].
Standards compliance
The EUDI Wallets are at the forefront of a revolutionary shift towards enhanced security, privacy, and user control through the seamlessly integration of a few pivotal protocols targeting better control of personal data. These include OID4VC (OpenID for verifiable credentials) [11], which in turn specifies OID4VCI (OpenID for verified credentials issuance) [12] and OID4VP (OpenID for verifiable presentations) [13] into the digital wallet ecosystem, alongside a robust suite of other cutting-edge privacy mechanisms and formats such as SD-JWT (selective disclosure JWTs) and those capable of ZKP (zero-knowledge proofs). The OID4VCI and OID4VP can be implemented in digital wallets for both organizations and individuals The use of these specifications aligns with the requirements specified in the ARF.
Open Wallet Foundation (OWF)
 On 23 February 2023, Linux Foundation Europe, an independent trusted supporter, and vendor-neutral home for open-source projects in Europe, announced the official formation of the Open Wallet Foundation (OWF). This new, collaborative effort aims to develop open-source software to support interoperability for a wide range of wallet use cases, including making payments, proving identity, storing validated credentials such as employment, education, financial standing, and entitlements.
On 23 February 2023, Linux Foundation Europe, an independent trusted supporter, and vendor-neutral home for open-source projects in Europe, announced the official formation of the Open Wallet Foundation (OWF). This new, collaborative effort aims to develop open-source software to support interoperability for a wide range of wallet use cases, including making payments, proving identity, storing validated credentials such as employment, education, financial standing, and entitlements.
The OWF aims to set best practices for digital wallet technology through collaboration on standards-based OSS components that issuers, wallet providers and relying parties can use to bootstrap implementations that preserve user choice, security, and privacy.
The OWF is an open-source community that works together to blend different skill sets to build fundamental, standards-based technologies for multipurpose wallets.
The OWF is a consortium of companies and non-profit organisations collaborating to drive global adoption of open, secure, and interoperable digital wallet solutions as well as providing access to expertise and advice through its Government Advisory Council.
Currently there are over 300 entities that have expressed interest in joining the Open Wallet Foundation and are working collaboratively to establish governance and scope.
| Premier members | General members | |
| Accenture | American Express | IndyKite |
| Gen | Deutsche Telekom / T-Systems | Intesi Group |
| Futurewei | esatus AG | Ping Identity |
| Visa | Fynbos | SmartMedia Technologies (SMT) |
| Hopae | Spruce | |
| IAMX | Swisscom | |
| IDnow | ||
Table 4: Some of the sponsors and general members of the OWF
| Non-profits, academic and government entities | |
| Customer Commons | ID2020 |
| Decentralized Identity Foundation (DIF) | IDunion SCE |
| Digital Identification and Authentication Council of Canada (DIACC) | Mifos Initiative |
| Digital Dollar Project | MIT Connection Science |
| Digital Identity New Zealand (DINZ) | Modular Open-Source Identity Platform (MOSIP) |
| Digital Identity and Data Sovereignty Association (DIDAS) | OpenID Foundation |
| DizmeID Foundation (DIZME) | Open Identity Exchange (OIX) |
| Hyperledger Foundation | Secure Identity Alliance (SIA) |
| Information Technologies ics and Telematics Institute / Centre for Research and Technology Hellas (CERTH/ITI) | Universitat Rovira i Virgili |
| Johannes Kepler University Linz | Trust Over IP Foundation (ToIP) |
Table 5: Some of the other members of the OWF
The OWF does not intend to publish a wallet itself, nor offer credentials or create new standards. Instead, its open-source software engine aims to become the core that other organizations and companies leverage to develop their own digital wallets. The wallets will seek feature parity with the best available wallets and interoperability with major cross-border projects such as the EUDI Wallet.
According to Daniel Goldscheider, Founder of the OWF:
Wallets are critical infrastructure for payments, for identity, and for secure access. Open source – driven by collaboration among for-profits large and small, non-profits, and government leaders – is a great role model for infrastructure that is vital for digital societies and benefits everyone.
With open source at the core of wallets, like it is at the core of web browsers, anyone can build a digital wallet that works with others and gives consumers the freedom to maintain their identity and verifiable credentials and share relevant data when, where, and with whom they choose.
With such a consequential and diverse group of members, OWF underscores how important it is to have an open foundation to support a plurality of digital wallets to ensure consistency, interoperability, and portability while protecting consumer privacy.
Gabriele Columbro, general manager of Linux Foundation Europe, said:
The world needs a place to store digital assets that matter, and the work of this foundation has the potential to redefine the credentials landscape globally, creating in turn much better digital experiences for people everywhere and new market opportunities.
The EU has been a leading force in data privacy and consumer protection, and efforts like OWF offer a concrete opportunity for policy makers to “shift left” their engagement, enabling a continuous and transparent feedback cycle between regulations and regulated technology. That’s why we are honoured to bring such a relevant group of cross-industry players together in OWF under Linux Foundation Europe.
Launching in tandem with OWF is a report, Why the World Needs an Open-Source Digital Wallet Right Now, from the OWF in partnership with Linux Foundation Research. The report notes:
- Digital wallets are the world’s leading payment method for e-commerce and point-of-sale retail. In 2021, the value of digital wallet transactions came to USD 15.9 trillion.
- Hundreds of digital wallets exist, but suffer from a host of problems, including vendor lock in, no interoperability, questionable security, and limited capabilities.
- New wallets are underway, too, but without them all staying in sync, every country or organization that issues credentials could become a walled garden. IDs and wallets from elsewhere won’t work, disrupting travel, international students, and mobile workforces.
- The future will include multiple wallets, which is why there is a need for a world-class wallet engine to ensure that interoperability is built in.
Interoperability
To support different member-proposed standard credential types the OWF plans to develop a common core that lays the foundation for interoperability and inclusivity. The level required for OWF-based wallets to be accepted by governments and regulatory regimes around the world is high and requires the common core to solve for interop at four different layers.
| Layer | Description |
| Legal | Governance for the interoperability of credentials, systems and the management of identity and access rights across multiple applications and services to meet regulatory and security requirements |
| Business | Alignment of business processes, responsibilities, and expectations to achieve commonly agreed and mutually beneficial goals |
| Semantic and syntactic | The ability of two or more systems to exchange data even if the interface and programming languages are different |
| Protocol | The ability of different systems devices, applications, or products to connect and communicate in a coordinated way without effort from the end user |
Table 6: Interoperability requirements
Proposed Initial Building Blocks
Members have already expressed interest in contributing resources for the following initial building blocks/credential types (based on the EUDI Wallet as reference point):
- Payment Tokenisation (EMV Tokenisation Specification)
- ISO mDL (ISO/IEC 18013-X — Mobile Driving License)
- W3C Verifiable Credentials (W3C Verifiable Credentials Data Model v1.1)
- Anonymous Credentials (AnonCreds Specification v1.0 Draft)
- ICAO DTC (Digital Travel Credentials Technical Report v1.2)
TechVision Research Wallet Provider Shortlist
Vendor Selection Criteria
Although some of the major technology companies have been offering wallet services for several years, the market for digital identity wallet is nascent and far from mature. At present the market is dominated by mobile device manufacturers and payments companies: however, these solutions fall far short of providing the digital identity wallets as described, for example, in the initiatives taking place in Europe. As such, for some time, we will be looking at hybrid solutions until the infrastructure and the appropriate standards are in place, either at a national level or globally, to support fully functional digital identity wallets.
Several of the emerging players are making their wallets open source which allows enterprises to construct their own in-house solution or to simply extend an existing solution. While this may initially appear to be an attractive way forward and one that might require the least initial capital outlay, it is TechVision Research’s opinion that it is fraught with risk and would eventually become a logistical and commercial liability. Amongst the potential pitfalls going forward would be achieving the right levels of access and security, managing data protection and passwords, supporting API standards, and keeping up with demands for increases in speed and scale as the system grows.
Below is the TechVision Research recommended checklist based on our observations in the marketplace from both vendors and user organizations. As this is a specific area of focus within the identity management market, it doesn’t necessarily mean that the vendors selected on our shortlist are the best overall digital identity wallet providers, but it does mean that these are the vendors that we believe have strong offerings specific to consumer-oriented identity services.
Big Tech Wallets
Whilst the EU is aiming to have 80% of its citizens in the possession of a digital identity wallet by 2030 – and making use of it on a daily basis for a wide range of applications – Apple, Google and others can claim that all users of iOS and Android devices have already had for a number of years a digital wallet that integrates relatively seamlessly with a range of third parties including payments, boarding passes etc. Although these vendors dominate the wallet market, at present (and for the foreseeable future), they only provide a limited set of attributes and credentials.
Apple
Apple Wallet, originally Apple Passbook announced in 2012 then renamed in 2015, is a digital wallet included with iOS and watchOS that allows users to store Wallet passes such as coupons, boarding passes, student ID cards, government ID cards, business credentials, resort passes, car keys, home keys, event tickets, public transportation passes, store cards, as well as credit cards, and debit cards for use via Apple Pay.
The original Google Wallet was introduced in 2011 supported Mastercard cards issued by Citibank. Four years later Android Pay was launched and in 2018 Google Wallet and Android Pay were re-branded as Google Pay with an API for merchants to add the payment service to their respective platforms. Then in 2022, Google Pay was transformed back into Google Wallet, available as an app on Android devices.
The Google Wallet allows users to store items such as payment cards for use via Google Pay, as well as passes such as loyalty cards, digital keys, digital identification cards, bus or train passes, event tickets and health passes.
Others
Samsung Wallet was introduced in 2013 before being migrated into a new app called Samsung Pay in 2015. Samsung Wallet now contains the Samsung Pay service for payment cards, alongside other features such as cryptocurrency assets and digital credentials. Samsung Wallet supports memberships (loyalty cards), gift cards, health passes, and boarding passes.
Huawei Wallet, available on Android and Harmony OS, also stores boarding passes, loyalty cards, and gift vouchers.
There are a variety of digital wallets, including the Singaporean Singpass[5], the Malaysian Touch ‘n Go eWallet[6] and the eCNY wallet in China[7], that enable transactions among various retail vendors in the form of mobile payments and have widespread usage in East Africa and among Asian countries.
Digital Identity Wallet Providers
From a TechVision Research perspective, the companies listed below are thought and market leaders in this space but will be joined by numerous others over the coming two-three years.
Bank.Id
BankID is used for identification or digital signatures with thousands of companies and authorities across Sweden. It also allows users to activate a digital ID card in their BankID app. On average, 18 million identifications and signatures are done with BankID every day which makes BankID an important part of the Swedish digital ecosystem.
BankID was first available in 2003 on computers before it was launched on a card in 2005 and then on mobile devices in 2011.
BankID is the single largest such service with a usage rate of 94% among smartphone users. It is administered by Finansiell ID-Teknik BID AB that is owned by several Swedish and Scandinavian banks. In 2022, BankID had about 8.4 million active users and was supported by over 6,000 web services. Only individuals with a Swedish personal identity number can acquire BankID, which is an issue for any non-Swedish citizens living in Sweden.
Dock
Dock was established in 2017 in Switzerland to solve the problems inherent in existing data solutions. It is a verifiable credentials company that provides Dock Certs, a user-friendly, no-code platform, a developer solution that enable organizations to issue, manage and verify fraud-proof credentials efficiently, securely, and at a lower cost.
Dock allows organizations in diverse sectors including health and safety, governments, workforce, education, supply chain and Web 3.0 as well as individuals to create and share verified data.
Dock provides a Wallet SDK, enabling users to build ID Wallet capabilities inside an existing app, to store, manage and share reusable Digital ID credentials without having to download an extra app.
Gataca
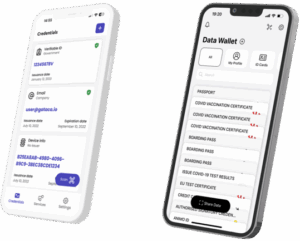
Founded in 2018, Gataca is a cybersecurity company that provides decentralized digital identity management technology. It was conceived as an academic research project at MIT in 2017 to mitigate the risks of conducting business online and is now based in Madrid.
Gataca Wallet is a phone-based ID wallet that can store tamper-proof identity credentials securely. Its advanced features include:
- Multi-identity: Create different profiles in your wallet.
- Multi-device: Manage your wallet from different devices.
- Backup and recovery.
- Aligned with European specifications for verifiable credentials.
- Electronic signature of documents.
The company also provides Gataca Studio, an all-in-one platform to facilitate the integration of SSI into a website or application. Gataca works in the areas of government, education, finance, travel and healthcare.
IDnow
The company was founded in 2010 and is headquartered in Munich with offices in Dubai, France, Spain, and the United Kingdom. It pioneered work in identity verification that led to a suite of identity products including the IDnow Wallet which represents the future of digital identity verification. It focuses on Fintech and other banking solutions, notably know your customer (KYC) and anti-money laundering (AML), as well as travel and telecommunications.
iGrant.io
Founded in 2017 and headquartered in Stockholm, with offices in Finland and India, iGrant.io provides an infrastructure for data exchange and verification services with digital wallets. Its solution unifies SSI, verifiable credentials, X.509, pods and digital wallets. The company emphasizes the importance of consent through a suite of automated data agreements in support of its data exchange platform that is also compliant with data protection and privacy regulations using centralised and decentralised Web 3.0 technologies. Every personal data transaction is based on a signed data agreement, making it trustworthy, immutable, and auditable. iGrant.io has to date primarily focussed on the healthcare, government, and travel sectors. It is a participant in EWC as well as the EBSI-VECTOR program[8].
Thales
Drawing on extensive feedback from pilot projects, such as the US Digital Driver’s Licenses (DDL) program[9], and active participation in the ISO standardization process[10], Thales, a global cybersecurity and data protection company headquartered in France, has designed its citizen-centric solution, Digital ID Wallet. It is supported by Gemalto’s Mobile Security Core[11] to provide protection against advanced threats and malware attacks and fulfilling the highest and most stringent security requirements of governments. Thales is a participant in the POTENTIAL and NOBID pilots.
Figure 2: Gataca and iGrant.io Wallets
Challenges and Open Issues
US Government IDs
Four US states (Arizona, Colorado, Georgia, and Maryland) permit their residents to save their government-issued identification credentials in both Apple and Google Wallets (only Arizona for Samsung Wallet). Mobile IDs in Google Wallet support three personal identification standards: ISO 18013-5, ISO 23220-4, and NIST 800-63, whereas Apple Wallet supports ISO 18013-5. Google and Samsung users have a choice whether to present their ID via NFC or QR, whereas Apple users can only present via NFC. Once the credential is read, the ID holder must confirm the personal information they wish to share (full name, age, etc.)
Mobile Driving Licenses (mDLs)
Although not an official identity document a driving license is used extensively worldwide, particularly in the US, as a form of identity verification, which both Apple and Google already support (i.e., ISO 18013-5 [14]).
According to Article 5 of eIDAS 2.0
Member States shall issue mobile driving licences based on the Union standard specifications laid down in Annex I, Part C.
And further:
Member States shall ensure that electronic applications established for mobile driving licences, in order to enable verification of the existence of the driving rights of the holder of the driving licence, are available to persons having their normal residence in their territory, or to persons who are otherwise entitled to hold mobile driving licences issued by them, free of charge. These applications shall be based on the European Digital Identity Wallets issued in accordance with Regulation (EU) No 910/2014 of the European Parliament and of the Council.
Whilst it is clear that EU countries are required to issue mobile driving licences, assuming that these mDLs are based on the ISO 18013-5 specification, there is still some ambiguity as to whether it mandates the use solely in EUDI Wallets or whether other wallets (e.g., Apple, Google etc) would be acceptable.
If this were the case, it would be much easier for European citizens to insert their mDL into their existing Apple/Google wallet. And consequently, EUDI Wallets would become far less attractive and useful, and would be relegated to occasional use on governmental websites; and Big Tech would effectively own digital ID in Europe.
Decentralized ID Travel
Digital Travel Credentials
SITA[12], a specialist in air transport communications and information technology, are collaborating with decentralized identity start-up Indicio[13] for verifiable digital travel credentials (DTC) that will enable passengers to store a digital version of their passport in a mobile wallet in line with standards from the International Civil Aviation Organization (ICAO) which is run by the United Nations (UN) [15]. Indicio’s offering is an SSI solution based on Hyperledger Indy. A separate identifier (DID) is created for each data sharing event making it harder to link too much of a person’s private information. The decentralized identity can be verified using blockchain, without storing personal data.
In March 2023, SITA and Indicio announced a pilot DTC scheme for travel to the island of Aruba. Beyond the Aruba pilot, the goal is for passengers to arrive at an airport with all document checks completed with only a photo cross check but no scanning of passports at the gate [16].
According to SITA AT BORDERS Senior Vice President Jeremy Springall:
“The adoption of digital identities will be the biggest technology breakthrough in the travel industry in decades. It will simplify the identification process at every step of the journey and open up opportunities for the air transport industry to fully embrace the benefits of seamless travel and the digital economy.”
In October 2023, SITA announced a collaboration with three Arab Air Carriers Organization (AACO) member airlines around its Travel Digital Identity Solution enables airlines, airports, and governments to verify a passenger’s identity and travel documents digitally by matching the biometrics data on their documents to an ICAO-compliant digital identity held on their mobile device thereby consolidating all travel documents into a single identity.
Digital Passports
Finland became the first country to offer its citizens a fully digital passport enabling passengers to use them when they both leave the country and return [17]. Supported by the EU, a six-month pilot program, started at the end of August 2023, was available only to Finnish citizens from Helsinki Airport as a partnership between Finnair, airport operator Finavia, and the Finnish police. Through the end of February 2024, Finnair passengers flying to and from three United Kingdom airports can pass through border control using new voluntary DTCs, with plans to extend to other routes. The EU is also planning similar pilot programs for Zagreb Airport in Croatia and Schiphol Airport in the Netherlands.
India, which already offers digital identity and boarding services for travellers on domestic flights, plans to extend the offer to international flights. Singapore, the United Arab Emirates (UAE), Qatar and Saudi Arabia, which boast the most modern airports in the world, also want to introduce the technology.
Digital passports are not the same as the introduction of biometrics, primarily facial recognition, used to create a single token of authentication for passing through an airport as is in use at Singapore’s Chiangi airport and at Dubai’s airport and like Global Entry, the US’s Trusted Traveller programme.
The ICAO is leading the effort to develop a universal digital identity and to get airports to standardize and coordinate customs and immigration processes and share passengers’ facial recognition and passport data.
Today biometrics are attached to a physical document but soon with biometrics and other key verifiable credentials, as well as visas, medical certificates, and boarding passes, stored on their mobile devices, physical passports will become completely redundant and a thing of the past [18].
“Open” vs “Closed” Wallets
On the one hand, wallets provide a simple exchange or presentation of verifiable credentials, and in contrast wallets are a way of exchanging and combining types of verified information as part of a complex transaction between two anonymised persons (legal, natural, automated, or manual) which might be governed by smart contracts etc.
What can be confusing are the different models and applications associated with the use of wallets.
In one business model, like that used by Apple, all parties agree to a centralized ruleset and governance. It does not matter if languages or semantics are different in their original form, but all attestations, values, formats etc are ‘normalized’ to a common agreed standard, no matter where or by whom they are executed. Most issues are determined by the operator of the application and accepted by all the relying parties and actors. The actual terms of the transaction are clear to read and see before entering the transaction. Issues like the question of liability, performance penalties, and jurisdiction are pre agreed to apply across each transaction using the application.
Mediation between parties is not computationally heavy on the wallet device, with most of the effort at each credential or attestation provider in the back-office.
The other business model is one in which there are no preorganised applications. The transaction type, rules and actors are all ad hoc and negotiation/mediation are decided at the time of transaction, although some pre-designed templates could be created and used. This could be very computationally heavy and possibly prone to error regarding semantics and lack of oversight regarding correct procedures, safeguards, and business cash flows towards operation of the system.
As there are other models between these two extremes, it becomes important to be able to differentiate between them, applying the right transparent terminology to avoid any ambiguity or false expectations.
Opportunities and Benefits
One of the challenges facing the EU and the Member States is how to make the adoption of the EUDI Wallet attractive enough to download and manage.
There has been to date a slow awareness raising campaigns, which is not surprising as there is nothing tangible to back up the EU’s ambition.
Figure 3: Early awareness graphics on the benefits of the EUDI Wallet
In Europe, the anticipated introduction of eIDAS 2.0 and the EUDI Wallet presents a mix of challenges and opportunities for citizens, governments, and both public and private sector service providers.
Although organizations are faced with a set of apparently daunting challenges, from investing in the integration of new technology, building user awareness to navigating new regulations and putting safeguards in place for if and when something goes awry, the anticipated benefits far outweigh the initial obstacles.
The adoption of the EUDI Wallet offers several advantages that benefit both organizations and citizens:
- Increased security: With EUDI Wallets, data is less susceptible to large scale breaches by using biometrics, strong encryption, and distributed storage. This ensures data integrity and reduces the likelihood of identity theft.
- Enhanced user experience: Managing multiple digital identities has become a considerable burden for both businesses and their users, who may be asked to create a digital identity for each service they want to access. With a digital identity wallet, users have password-less access to online services by simply scanning a QR code to share their credentials, reducing onboarding abandonment rates and increasing retention.
According to recent statistics on cart abandonment in the eCommerce sector [19], 25% of users mentioned as the second most important reason for dropping out the fact that the site requested them to use a specific account.
- Cost cutting: In addition to an improved user experience and hopefully more satisfied customers, a key benefit for a business is the potential for efficiency gains, achieved through reduced operational expenses related to customer identity verification processes, decreased expenditures on fraud prevention and lowered storage costs for attributes and attestations.
According to a European Commission impact assessment study [3], the estimated savings from more efficient onboarding procedures for financial services in the EU would range between USD 860 million and USD 1.7 billion per year and the estimated savings from reduced fraud could range between EUR 1.1 billion and EUR 4.3 billion.
- Reduced identity fraud: Credentials are issued and cryptographically signed by trusted authorities, facilitating automatic identity verification. This ensures that only verified individuals access your organization’s services, mitigating losses from fraud, errors, and fines linked to inaccurate customer identification and verification of transactions.
- Enhanced privacy and control: Individuals gain greater control over their personal information using an EUDI Wallet. They can choose what data to share and with whom, increasing data protection and reducing the risk of privacy breaches.
- Cross-border interoperability: The EUDI Wallet is designed to work seamlessly across different industries and countries, not limited to the EU.
Corporate Readiness and Next Steps
The adoption of digital identities is in different stages of implementation around the globe, from countries like Norway and Sweden close to full digital ID adoption to countries just embarking on the digital ID journey.
Although the impetus for the introduction of digital identity wallets is most apparent in Europe, enterprises worldwide should be getting ready to accept digital identities from their customers and employees and understand the crucial role that wallets are set to play.
As with the implementation of any (and all) identity and access management systems, preparing for eIDAS 2.0 in Europe and implementing authentication through digital identity wallets is a multifaceted process that requires a whole enterprise approach to addressing data privacy, security, and user experience. And as ever, anyone familiar with TechVision Research will know that this is not a job for one department or the faint-hearted: a successful implementation and ongoing compliance requires the involvement of legal, HR, IT and product teams, driven by the commitment of the senior executive team.
Step 1: Understanding requirements.
To get your project off the ground, it is important first to assess the feasibility and gather insights from all the relevant stakeholders before implementing decentralized identity technology across the enterprise. With an outline objective in mind, the first step is to involve and get commitment from all impacted stakeholders, including internal teams, decision-makers, customers, employees, and partners. Currently, it is a worthwhile exercise to liaise with the appropriate national or regional authorities and, particularly in Europe, regulators and to understand the roles that they are expected to play going forward.
Step 2: Choose a technology provider.
In selecting a technology solution that aligns with your high-level set of requirements and complies with the appropriate standards and regulations, you are choosing a key partner to work closely with.
Given that the realization of decentralized identities are relatively new, important factors to consider are a strong track record and expertise, deployment options (on-prem versus cloud strategies), industry expertise, implementation times, scalability, customization, user-friendliness, and support quality.
Step 3: Identifying initial use cases.
Realistically, you will not want to boil the ocean straight off. With that in mind, the next step is to identify several potential use cases and evaluate their complexity who the necessary stakeholders would be, and what the expected impact would be.
Helping to make this decision will be to choose one that allows you to demonstrate the benefits to your management team and your users. It is important to start small and gradually expand to a larger user base as you gain experience.
- Beyond identity verification and authentication processes, explore the possibility to issue credentials to your users.
- Create user stories and journey maps to visualize how users interact with the digital identity wallet in the selected use case.
- Estimate volumes for active users and issued credentials.
Step 4: Pilot preparation.
Once you have assembled the right set of teams and points of contact, you are ready to take the practical steps to get your initiative up and running. First off, if there isn’t a procedure in place already, it’s time to assess and review your current IAM systems and processes and by evaluating the existing identity verification and authentication processes. In addition, it is important to identify what personal data is collected from customers, employees, suppliers and partners and their sources of trust i.e., who it is who issues or attests to the veracity of the information provided. Finally, you will want to understand the current systems and processes in use for customer onboarding, authentication, and data storage management.
Step 5: Plan and design.
Working with your technology supplier and the internal teams, you are ready to create further develop your high-level plan including architectural designs, technical specifications and integration requirements with clear deadlines, milestones, and service levels for pilot users.
Step 6: Lessons learnt.
Once the pilot is up and running, it is important to carry out an ongoing assessment of how the initiative is progressing from a technical, regulatory compliance and, most importantly, user experience perspectives. This will provide you with the opportunity, where appropriate, to refine the user experience and address any other issues before full-scale implementation.
Step 7: Incremental scaling.
Once you, your stakeholders and users are confident of the working of the pilot, the final phase is to expand the use of decentralized identity technology to different and more complex use cases and/or to a larger user base by repeating the steps already taken.
Above all, to maintain the momentum created by the pilot as well as to ensure its long-term success across the whole enterprise, it is vital to promote and educate all employees, especially those directly impacted, about the new solution and the use of digital identity wallets.
For compliance with evolving regulations and to maintain user satisfaction, you should continue with ongoing monitoring and auditing procedures, with regular review milestones.
Conclusion
Worldwide there are major initiatives underway to establish the parameters and frameworks for the safe and secure interoperability of digital identities across borders. An increasing number of countries have already made or are in the process of making a digital identity a primary option for access to both public and private sector services, either led by the government or by the private sector – or a combination of the two. It is becoming increasingly evident that a mobile phone-based identity wallet is the preferred vehicle for storing, securing, and managing digital identities.
According to Thales from their involvement in pilots in the US, 87% of participants said they were highly interested in a digital identity wallet integrating all their credentials, an appetite that is evident worldwide. Likewise, a Thales survey across 11 countries in 2018 found that 70% of citizens would like their identity document on their smartphone, with the crucial proviso that the app was adequately secured.
There are still several questions, challenges and misconceptions stopping organisations from moving forward with the adoption of digital identities which need to be addressed and clarified. There are also issues around liability for data stored on individuals’ own devices as well as inclusivity and the verification of credentials for those who struggle to identify themselves at present.
Nonetheless, there is abundant evidence that digital identity ecosystems supported by digital identity wallets are growing very rapidly across the planet auguring the real dawn that we have been anticipating for decades.
Glossary
AACO Arab Air Carriers Organization
ARF Architecture and Reference Framework
CIAM Customer/Consumer Identity and Access Management
DID Decentralized Identifiers
DNS Domain Name Server
DTC Digital Travel Credentials
EAA Electronic Attestation of Attributes
EBSI European Blockchain Service Infrastructure
EC European Commission
EDIF Framework for a European Digital Identity
EHIC European Health Insurance Card
eID electronic IDentification
eIDAS electronic IDentification and Authentication Services
EMV Europay, Mastercard and Visa
EU European Union
EUDIW European Union Digital Identity Wallet
EWC European Wallet Consortium
ICAO International Civil Aviation Organization
IEC International Electrotechnical Commission
ISO International Standards Organization
LDAP Lightweight Directory Access Protocol
LSP Large Scale Pilot
mDL mobile Driving Licence
MEP Minister of the European Parliament
NFC Near Field Communication
ODI Organizational Digital Identity
OWF Open Wallet Foundation
PDA1 Portable Document A1
PID Personal Identification Data
QEAA Qualified Electronic Attestation of Attributes
QR Quick Response
QTSP Qualified Trust Service Provider
QWAC Qualified Web Authentication Certificates
SIM Subscriber Identity Module
SSI Self-Sovereign Identity
W3C World Wide Web Consortium
About TechVision
World-class research requires world-class consulting analysts, and our team is just that. Gaining value from research also means having access to research. All TechVision Research licenses are enterprise licenses; this means everyone that needs access to content can have it. We know major technology initiatives involve many different skills across an organization and limiting content to a few can compromise the effectiveness of the team and the success of the initiative. Our research leverages our team’s in-depth knowledge as well as their real-world consulting experience. We combine great analyst skills with real world client experiences to provide a deep and balanced perspective.
TechVision Consulting builds off our research with specific projects to help organizations better understand, architect, select, build, and deploy infrastructure technologies. Our well- rounded experience and strong analytical skills help us separate the hype from the reality. This provides organizations with a deeper understanding of the full scope of vendor capabilities, product life cycles, and a basis for making more informed decisions. We also support vendors when they carry out a product and strategy review and assessment, a requirement analysis, a target market assessment, a technology trend analysis, a go-to- market plan assessment, or a gap analysis.
TechVision Updates will provide regular updates on the latest developments with respect to the issues addressed in this report.
About the Author
 David has over 30 years of experience in senior identity management positions in Europe and the US. He led two prominent pioneering EC-funded projects then worked for IBM, firstly with Lotus and later Tivoli. He has led several start-ups in the identity space and spent eight years in senior product management roles for telecom providers Apertio, Nokia Siemens Networks and Ericsson. He has worked as a technology analyst and consulted with some of the largest companies in Europe and the US. He has broad insights across the European privacy/regulatory environment, European clients, and vendors. David is currently based in Scotland.
David has over 30 years of experience in senior identity management positions in Europe and the US. He led two prominent pioneering EC-funded projects then worked for IBM, firstly with Lotus and later Tivoli. He has led several start-ups in the identity space and spent eight years in senior product management roles for telecom providers Apertio, Nokia Siemens Networks and Ericsson. He has worked as a technology analyst and consulted with some of the largest companies in Europe and the US. He has broad insights across the European privacy/regulatory environment, European clients, and vendors. David is currently based in Scotland.
References
| Source | URL |
| [1] European Commission (2014) Regulation (EU) No 910/2014 of the European Parliament and of the Council, Official Journal of the European Union, L 257/73. | https://eur-lex.europa.eu/legal-content/EN/TXT/HTML/?uri=CELEX:32014R0910 |
| [2] European Commission (2016) eIDAS Technical Specifications, based on Opinion No. 1/2016 and CIR (EU) 2015/1501 (2016-01-26, v1.0) | https://ec.europa.eu/digital-building-blocks/wikis/display/DIGITAL/eIDAS+eID+Profile |
| [3] Study to support the impact assessment for the revision of the eIDAS regulation, European Commission, 9 June 2021 | https://digital-strategy.ec.europa.eu/en/library/study-support-impact-assessment-revision-eidas-regulation |
| [4] European Commission, 2021. Proposal for a Regulation of the European Parliament and of the Council of amending Regulation (EU) No 910/2014 as regards establishing a framework for a European Digital Identity. [Online] | https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=CELEX%3A52021PC0281 |
| [5] European Commission (2023) eIDAS Technical Specifications, based on Opinion No. 3/2023 and CIR (EU) 2015/1501 (2023-04-24, v1.3) | https://ec.europa.eu/digital-building-blocks/wikis/display/DIGITAL/eIDAS+eID+Profile |
| [6] European Commission (2023) The European Digital Identity Wallet Architecture and Reference Framework (2023-04, v1.1.0) | https://github.com/eu-digital-identity-wallet/eudi-doc-architecture-and-reference-framework/releases |
| [7] European Commission (2022) ‘European Social Security Pass’ | https://ec.europa.eu/social/main.jsp?catId=1545&langId=en |
| [8] Vid Kersic, Urban Vidovic, Andraz Vrecko, Martin Domajnko, Muhamed Turkanov, ‘Orchestrating Digital Wallets for On- and Off-Chain Decentralized Identity Management’, IEEE Access, 1 August 2023 | https://ieeexplore.ieee.org/document/10194951 |
| [9] Last Chance to fix eIDAS: Secret EU law threatens Internet security | https://last-chance-for-eidas.org/ |
| [10]Open letter on the position of scientists and NGOs on the EU’s proposed digital identity reform | https://nce.mpi-sp.org/index.php/s/cG88cptFdaDNyRr |
| [11]OpenID Foundation (2022), ‘OpenID for Verifiable Credentials – Overview’, | https://openid.net/sg/openid4vc/ |
| [12]OpenID Foundation (2023), ‘OpenID for Verifiable Credential Issuance (OID4VCI)’, | https://openid.net/specs/openid-4-verifiable-credential-issuance-1_0-11.html |
| [13]OpenID Foundation (2023) ‘OpenID for Verifiable Presentation (OIDC4VP)’, | https://openid.net/specs/openid-4-verifiable-presentations-1_0.html |
| [14]ISO/IEC 18013-5:2021 Personal identification, ISO-compliant driving licence, Part 5: Mobile driving licence (mDL) application | https://www.iso.org/standard/69084.html |
| [15]SITA plans roll out of decentralized ID passports for travel sector with Indicio | https://www.ledgerinsights.com/sita-decentralized-id-passports-travel-indicio/ |
| [16]SITA, Indicio start piloting decentralized identity passports for Aruba travel | https://www.ledgerinsights.com/sita-indicio-decentralized-identity-passports-aruba/ |
| [17]Like it or not, digital passports are coming to an airport near you: Mobile passports, currently being trialled in Finland, will make travel easier. But what about data security? | https://www.telegraph.co.uk/travel/news/digital-passports-finland-europe-airport-technology/ |
| [18]The Future of International Travel Is Passport-Free. | https://www.cntraveler.com/story/passport-free-travel-biometrics |
| [19]49 Cart Abandonment Rate Statistics 2024, Baymard Institute | https://baymard.com/lists/cart-abandonment-rate |
Related Reports
The following reports might be helpful in your continued exploration of this domain:
Reports that explore Identity and Access Management:
- Putting Identity into Context – Next Generation IAM, by David Goodman.
- The Future of Identity Management, by Gary Rowe, Doug Simmons, David Goodman, and Bill Bonney.
- Blockchain-based Identity Management, by Doug Simmons and Gary Rowe.
- Reports that explore data, its categorization, management, technical handling, and use:
- Fixing the Fundamentals: The Business Blueprint, by Noreen Kendle.
- IoT as a Security Risk Amplifier and Mitigation Strategies, by Bill Bonney and Scott David.
- New European Privacy and Data Protection Regulations – Compliance or Consequences, by David Goodman.
- Opportunities in Europe with Electronic Identification and Trust Services, by
[1] digital-identity-wallet.eu
[2] nobidconsortium.com
[3] dc4eu.eu
[4] eudiwalletconsortium.org
[5] singpass.gov.sg/main/
[6] touchngo.com.my/
[7] scmp.com/tech/big-tech/article/3237735/china-digital-currency-beijing-forum-promotes-sim-based-e-cny-hard-wallet-alternative-mobile.
[8] ebsi-vector.eu
[9] thalesgroup.com/en/markets/digital-identity-and-security/press-release/gemalto-wins-us-government-grant-for-digital-driver-s-license-pilot-in-four-jurisdictions in partnership with Colorado, Idaho, Maryland, and Washington D.C. as well as NIST.
[10] Primarily to support the ISO/IEC 18013-5 Standard for mDL applications.
[11] thalesgroup.com/en/markets/digital-identity-and-security/government/identity/digital-identity-services/mobile-software-security
[12] sita.aero
[13] indicio.tech